Most C2C connectors have a **Forward to SIEM** option in the configuration UI. If a C2C connector lacks that option, you can achieve the same effect by assigning a field named `_siemforward`, set to *true*, to the connector.
For information about what C2C sources are available, see Cloud-to-Cloud Integration Framework. 1. **Use a Sumo Logic Source and parser**. If there isn’t a C2C connector for your data source, your next best option is to use a Sumo Logic Source (running on an Installed Collector or a Hosted Collector, depending on the data source)—and a Sumo Logic parser, if we have one for the data source. - To check if there’s a parser for your data source, go to the **Manage Data > Logs > Parsers** page in the Sumo Logic UI. If there is a parser for your data source, but you find it doesn’t completely meet your needs–for instance if the parser doesn’t support the particular log format you use–consider customizing the parser with a [local configuration](/docs/cse/schema/parser-editor#create-a-local-configuration-for-a-system-parser). If that’s not practical, you can submit a request for a new parser by filing a ticket at [https://support.sumologic.com](https://support.sumologic.com/). + Check if there’s a parser for your data source. In the main Sumo Logic menu, select **Manage Data > Logs > Parsers**. If there is a parser for your data source, but you find it doesn’t completely meet your needs–for instance if the parser doesn’t support the particular log format you use–consider customizing the parser with a [local configuration](/docs/cse/schema/parser-editor#create-a-local-configuration-for-a-system-parser). If that’s not practical, you can submit a request for a new parser by filing a ticket at [https://support.sumologic.com](https://support.sumologic.com/). When you forward logs to Cloud SIEM for parser processing, there are two bits of important configuration: @@ -52,13 +46,10 @@ We recommend the following ingestion processes, starting with the most preferred ::: 2. Configure the source with the path to the appropriate parser, by assigning a field named `_parser`, whose value is the path to parser, for example: - ``` _parser=/Parsers/System/AWS/AWS Network Firewall ``` - :::note - You can get the path to a parser on the **Manage Data > Logs > Parsers** page in Sumo Logic. Click the three-dot kebab menu in the row for a parser, and select **Copy Path**. - ::: + You can get the path to a parser on the **Parsers** page in Sumo Logic. Click the three-dot kebab menu in the row for a parser, and select **Copy Path**. 1. **Use a Sumo Logic Source and Cloud SIEM Ingest mapping**. This is the least recommended method, as you have to manually configure the mapping hints in an ingestion mapping. For more information, see [Configure a Sumo Logic Ingest Mapping](/docs/cse/ingestion/sumo-logic-ingest-mapping/). diff --git a/docs/integrations/containers-orchestration/kubernetes.md b/docs/integrations/containers-orchestration/kubernetes.md index ac072a0de7..f3648062b9 100644 --- a/docs/integrations/containers-orchestration/kubernetes.md +++ b/docs/integrations/containers-orchestration/kubernetes.md @@ -113,8 +113,8 @@ For details on the individual alerts, see [Kubernetes Alerts](/docs/observabilit 1. Download the [JSON file](https://raw.githubusercontent.com/SumoLogic/terraform-sumologic-sumo-logic-monitor/main/monitor_packages/kubernetes/kubernetes.json) describing all the monitors. 2. The alerts should be restricted to specific clusters and/or namespaces to prevent the monitors hitting the cardinality limits. To limit the alerts, update the JSON file by replacing the text `$$kubernetes_data_source` with `
 +3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**. +4. Click **Add**. 5. Click **Import** to import monitors from the JSON above. :::note diff --git a/docs/integrations/containers-orchestration/opentelemetry/rabbitmq-opentelemetry.md b/docs/integrations/containers-orchestration/opentelemetry/rabbitmq-opentelemetry.md index 9761804934..9e5152b4b1 100644 --- a/docs/integrations/containers-orchestration/opentelemetry/rabbitmq-opentelemetry.md +++ b/docs/integrations/containers-orchestration/opentelemetry/rabbitmq-opentelemetry.md @@ -11,7 +11,7 @@ import TabItem from '@theme/TabItem';
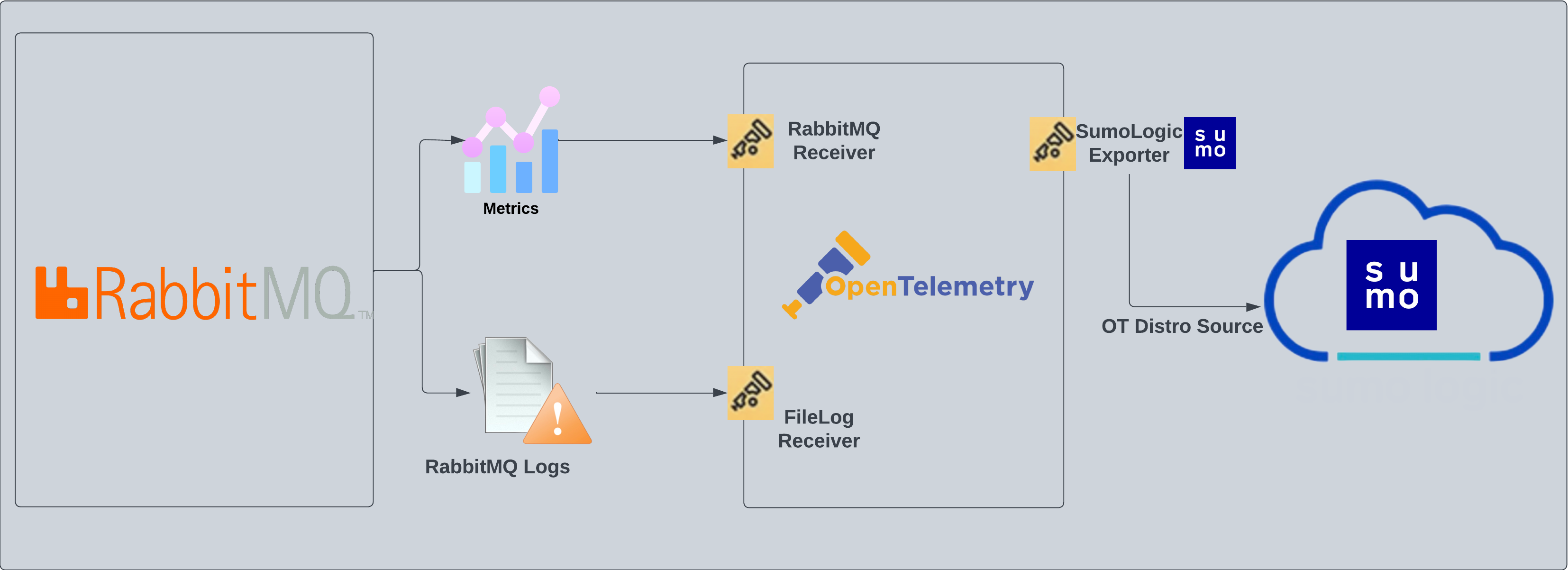 @@ -19,17 +19,32 @@ The [RabbitMQ](https://www.rabbitmq.com/getstarted.html) app is a unified log ap
Following are the [Fields](/docs/manage/fields/) which will be created as part of RabbitMQ App install if not already present.
-* `messaging.cluster.name`. User configured. Specify the user-friendly cluster name which RabbitMQ belongs to.
-* `sumo.datasource`. Has fixed value of **rabbitmq**.
+* **`sumo.datasource`**. Fixed value of **rabbitmq**.
+* **`messaging.system`**. Fixed value of **rabbitmq**.
+* **`deployment.environment`**. This is a user-configured field set at the time of collector installation. It identifies the environment where the rabbitmq env resides, such as `dev`, `prod`, or `qa`.
+* **`messaging.cluster.name`**. User configured. Enter a name to uniquely identify your RabbitMQ cluster. This cluster name will be shown in the Sumo Logic dashboards.
+* **`messaging.node.name`**. Includes the value of the hostname of the machine which is being monitored.
## Prerequisites
+### For metrics collection
+
+:::note
+The RabbitMQ receiver supports RabbitMQ versions `3.8` and `3.9`.
+:::
+
+Enable the RabbitMQ management plugin by following the instructions in the [RabbitMQ documentation](https://www.rabbitmq.com/management.html#getting-started). Also, make sure you at least have the [monitoring](https://www.rabbitmq.com/management.html#permissions) level permissions to monitor the metrics.
+
+
+### For logs collection
+
This section provides instructions for configuring log collection for RabbitMQ running on a non-Kubernetes environment for the Sumo Logic App for RabbitMQ. By default, RabbitMQ logs are stored in a log file.
Follow the instructions to set up log collection:
-1. **Configure logging in RabbitMQ**. RabbitMQ supports logging via the following methods: local text log files, syslog and stdout. RabbitMQ logs have six levels of verbosity: debug, info, warning, error, critical, none. For details please visit this [page](https://www.rabbitmq.com/logging.html#log-levels). For the dashboards to work properly, log level needs to be set to **debug**. Default log level is **info**. All logging settings are located in [RabbitMQ.conf](https://www.rabbitmq.com/logging.html).
-2. **Configure RabbitMQ to write log lines to a local file**. By default, RabbitMQ logs are stored in `/var/log/rabbitmq/rabbit@
@@ -19,17 +19,32 @@ The [RabbitMQ](https://www.rabbitmq.com/getstarted.html) app is a unified log ap
Following are the [Fields](/docs/manage/fields/) which will be created as part of RabbitMQ App install if not already present.
-* `messaging.cluster.name`. User configured. Specify the user-friendly cluster name which RabbitMQ belongs to.
-* `sumo.datasource`. Has fixed value of **rabbitmq**.
+* **`sumo.datasource`**. Fixed value of **rabbitmq**.
+* **`messaging.system`**. Fixed value of **rabbitmq**.
+* **`deployment.environment`**. This is a user-configured field set at the time of collector installation. It identifies the environment where the rabbitmq env resides, such as `dev`, `prod`, or `qa`.
+* **`messaging.cluster.name`**. User configured. Enter a name to uniquely identify your RabbitMQ cluster. This cluster name will be shown in the Sumo Logic dashboards.
+* **`messaging.node.name`**. Includes the value of the hostname of the machine which is being monitored.
## Prerequisites
+### For metrics collection
+
+:::note
+The RabbitMQ receiver supports RabbitMQ versions `3.8` and `3.9`.
+:::
+
+Enable the RabbitMQ management plugin by following the instructions in the [RabbitMQ documentation](https://www.rabbitmq.com/management.html#getting-started). Also, make sure you at least have the [monitoring](https://www.rabbitmq.com/management.html#permissions) level permissions to monitor the metrics.
+
+
+### For logs collection
+
This section provides instructions for configuring log collection for RabbitMQ running on a non-Kubernetes environment for the Sumo Logic App for RabbitMQ. By default, RabbitMQ logs are stored in a log file.
Follow the instructions to set up log collection:
-1. **Configure logging in RabbitMQ**. RabbitMQ supports logging via the following methods: local text log files, syslog and stdout. RabbitMQ logs have six levels of verbosity: debug, info, warning, error, critical, none. For details please visit this [page](https://www.rabbitmq.com/logging.html#log-levels). For the dashboards to work properly, log level needs to be set to **debug**. Default log level is **info**. All logging settings are located in [RabbitMQ.conf](https://www.rabbitmq.com/logging.html).
-2. **Configure RabbitMQ to write log lines to a local file**. By default, RabbitMQ logs are stored in `/var/log/rabbitmq/rabbit@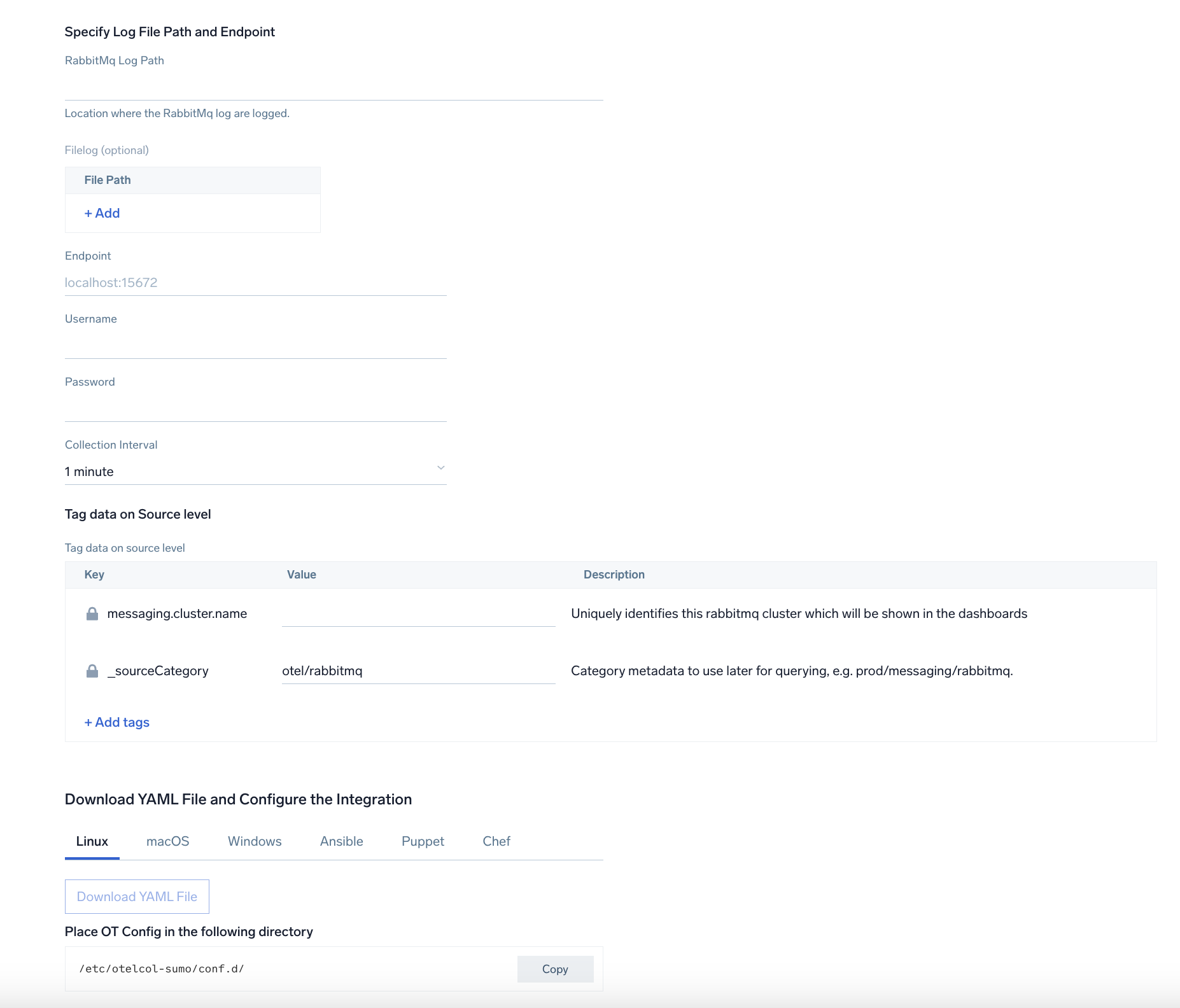 @@ -164,6 +192,8 @@ Here's a sample log message you'd find in Non-Kubernetes environments.
## Sample queries
+### Logs
+
This sample Query is from the **RabbitMQ - Logs dashboard** > **Events** by Severity panel.
```sql title="Query String"
@@ -173,10 +203,26 @@ This sample Query is from the **RabbitMQ - Logs dashboard** > **Events** by Seve
| parse "* * [*]" as date,time,severity | count by severity
```
+### Metrics
+
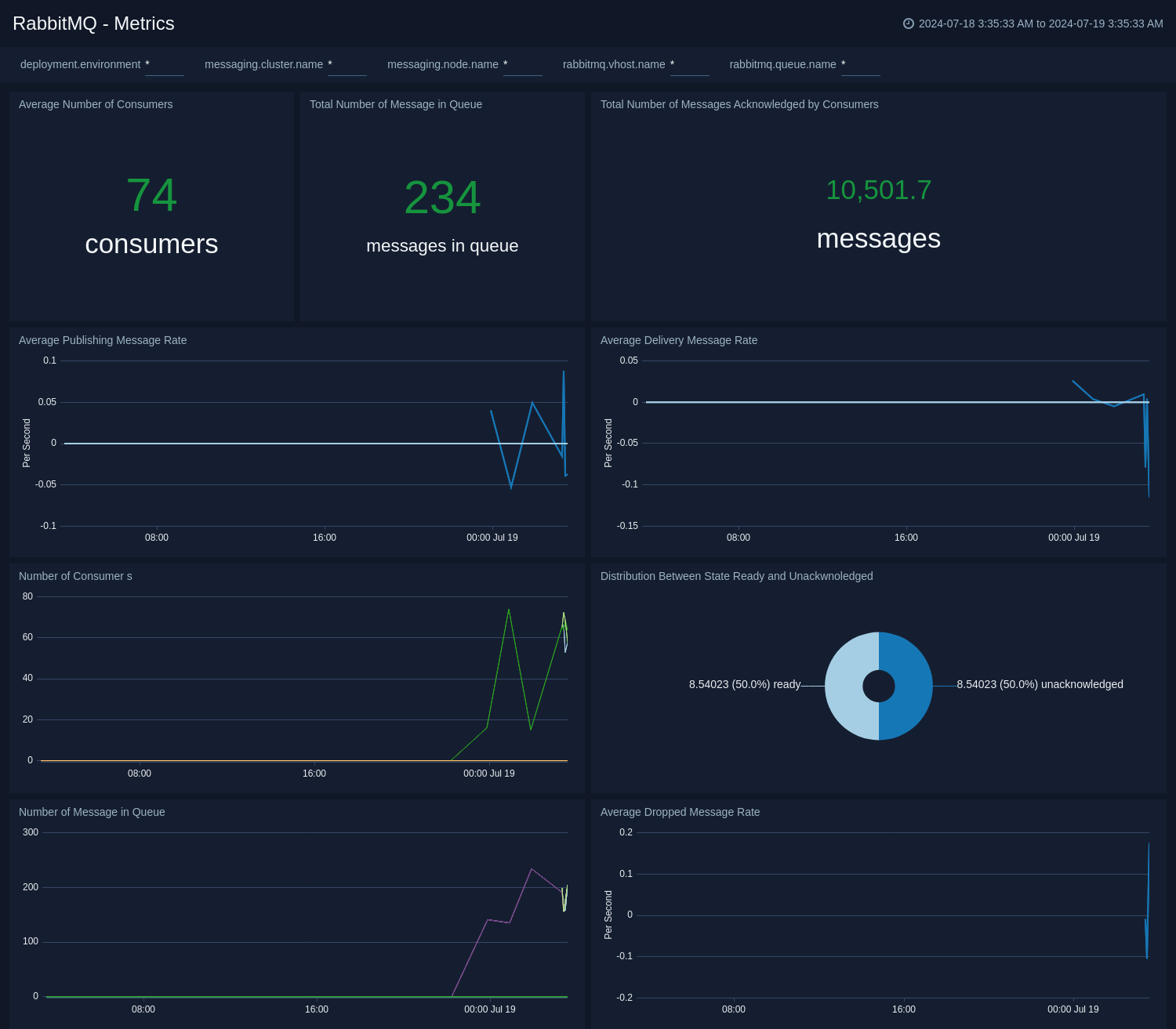
+This sample query is from the **Average Number of Consumers** panel in **RabbitMQ - Metrics** dashboard.
+
+```sql sumo.datasource=rabbitmq metric=rabbitmq.consumer.count deployment.environment=* messaging.cluster.name=* messaging.node.name=* rabbitmq.queue.name=* rabbitmq.vhost.name=*
+| avg by messaging.cluster.name
+| sum
+```
+
+
## Viewing RabbitMQ Dashboards
-### Overview
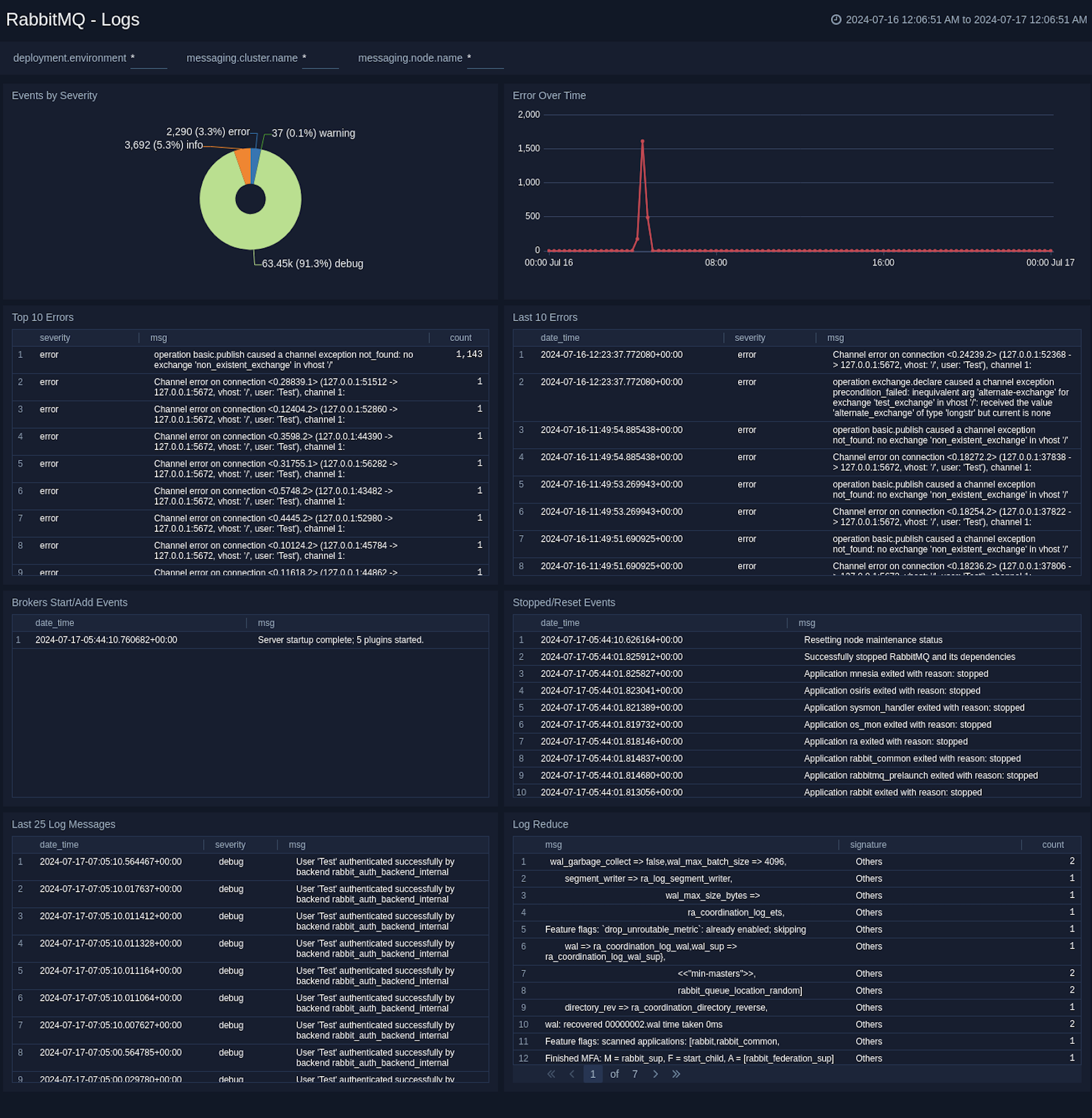
+### Logs
+
+The **RabbitMQ - Logs** dashboard gives you an at-a-glance view of error messages, error by severity, top and last 10 errors, broker, and Event Start/Add log messages.
+
+
@@ -164,6 +192,8 @@ Here's a sample log message you'd find in Non-Kubernetes environments.
## Sample queries
+### Logs
+
This sample Query is from the **RabbitMQ - Logs dashboard** > **Events** by Severity panel.
```sql title="Query String"
@@ -173,10 +203,26 @@ This sample Query is from the **RabbitMQ - Logs dashboard** > **Events** by Seve
| parse "* * [*]" as date,time,severity | count by severity
```
+### Metrics
+
+This sample query is from the **Average Number of Consumers** panel in **RabbitMQ - Metrics** dashboard.
+
+```sql sumo.datasource=rabbitmq metric=rabbitmq.consumer.count deployment.environment=* messaging.cluster.name=* messaging.node.name=* rabbitmq.queue.name=* rabbitmq.vhost.name=*
+| avg by messaging.cluster.name
+| sum
+```
+
+
## Viewing RabbitMQ Dashboards
-### Overview
+### Logs
+
+The **RabbitMQ - Logs** dashboard gives you an at-a-glance view of error messages, error by severity, top and last 10 errors, broker, and Event Start/Add log messages.
+
+ +
+### Metrics
-The **RabbitMQ - Overview** dashboard gives you an at-a-glance view of Error messages, error by severity, top and last 10 errors, Broker and Event Start/Add log messages.
+The **RabbitMQ - Metrics** dashboard gives you an at-a-glance view of your RabbitMQ deployment across brokers, queue, exchange, consumer, and messages.
-
+
+### Metrics
-The **RabbitMQ - Overview** dashboard gives you an at-a-glance view of Error messages, error by severity, top and last 10 errors, Broker and Event Start/Add log messages.
+The **RabbitMQ - Metrics** dashboard gives you an at-a-glance view of your RabbitMQ deployment across brokers, queue, exchange, consumer, and messages.
-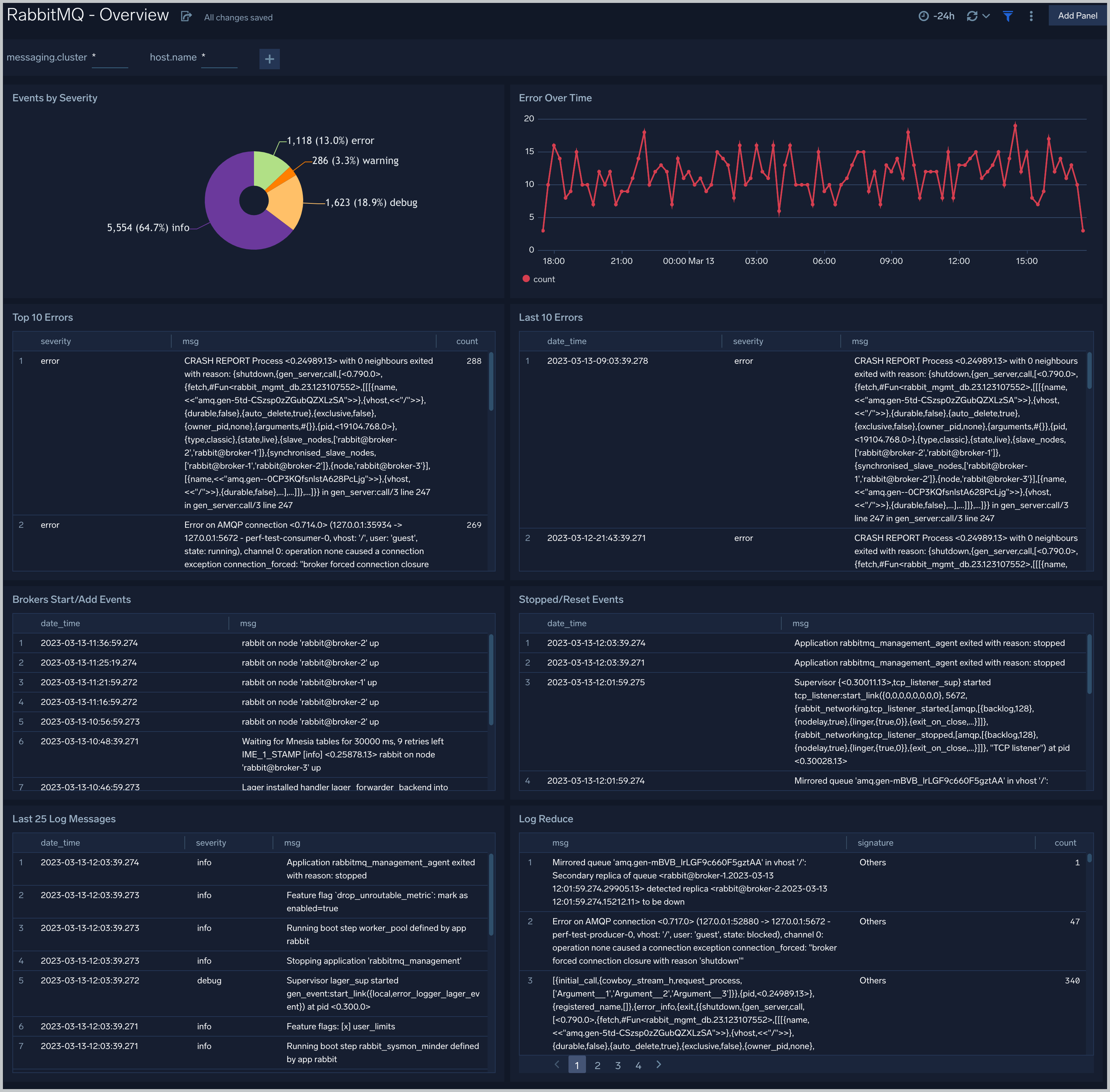 +
+ diff --git a/docs/integrations/containers-orchestration/rabbitmq.md b/docs/integrations/containers-orchestration/rabbitmq.md
index 80cfa7ba9e..a35468371d 100644
--- a/docs/integrations/containers-orchestration/rabbitmq.md
+++ b/docs/integrations/containers-orchestration/rabbitmq.md
@@ -463,7 +463,7 @@ This section demonstrates how to install the RabbitMQ App.
Version selection is not available for all apps.
:::
3. To install the app, complete the following fields.
- 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
+ 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
2. **Data Source.** Choose **Enter a Custom Data Filter**, and enter a custom RabbitMQ cluster filter. Examples:
1. For all RabbitMQ clusters: `messaging_cluster=*`
2. For a specific cluster: `messaging_cluster=rabbitmq.dev.01`
diff --git a/docs/integrations/databases/couchbase.md b/docs/integrations/databases/couchbase.md
index 9db4720cd3..fe4a125cb5 100644
--- a/docs/integrations/databases/couchbase.md
+++ b/docs/integrations/databases/couchbase.md
@@ -200,8 +200,8 @@ This section explains the steps to collect Couchbase logs from a Kubernetes envi
5. Sumo Logic Kubernetes collection will automatically start collecting logs from the pods having the annotations defined above.
6. Verify logs in Sumo Logic.
3. **Add a FER to normalize the fields in Kubernetes environments**. This step is not needed if using application components solution terraform script. Labels created in Kubernetes environments automatically are prefixed with pod_labels. To normalize these for our app to work, we need to create a Field Extraction Rule if not already created for Proxy Application Components. To do so:
- 1. Go to Manage Data > Logs > Field Extraction Rules.
- 2. Click the + Add button on the top right of the table.
+ 1. In the main Sumo Logic menu, select **Manage Data > Logs > Field Extraction Rules**.
+ 2. Click the **+ Add Rule** button on the top right of the table.
3. The **Add Field Extraction Rule** form will appear:
4. Enter the following options:
* **Rule Name**. Enter the name as **App Observability - Proxy**.
@@ -401,7 +401,7 @@ There are limits to how many alerts can be enabled - see the [Alerts FAQ](/docs/
1. For alerts applicable only to a specific cluster, your custom filter would be `'db_cluster=couchbase-standalone.01'`.
2. For alerts applicable to all cluster that start with couchbase-standalone, your custom filter would be,`db_cluster=couchbase-standalone*`.
3. For alerts applicable to a specific cluster within a production environment, your custom filter would be `db_cluster=couchbase-1` and `environment=standalone` (This assumes you have set the optional environment tag while configuring collection).
-3. Go to Manage Data > Alerts > Monitors.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**:
5. Click **Import** and then copy-paste the above JSON to import monitors.
6. The monitors are disabled by default. Once you have installed the alerts using this method, navigate to the Couchbase folder under **Monitors** to configure them. See [Monitor Settings](/docs/alerts/monitors/settings) to learn how to enable monitors to send notifications to teams or connections. See the instructions detailed in [Create a Monitor](/docs/alerts/monitors/create-monitor).
@@ -485,7 +485,7 @@ Locate and install the app you need from the **App Catalog**. If you want to see
Version selection is not available for all apps.
:::
3. To install the app, complete the following fields.
- 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
+ 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
2. **Data Source.**
* Choose **Enter a Custom Data Filter**, and enter a custom Couchbase cluster filter. Examples:
1. For all Couchbase clusters `db_cluster=*`
diff --git a/docs/integrations/databases/mariadb.md b/docs/integrations/databases/mariadb.md
index 48c06d4cb7..efad874a5f 100644
--- a/docs/integrations/databases/mariadb.md
+++ b/docs/integrations/databases/mariadb.md
@@ -448,7 +448,7 @@ Sumo Logic has provided out-of-the-box alerts available through [Sumo Logic moni
* For alerts applicable only to a specific cluster, your custom filter would be `db_cluster=mariadb-prod.01`.
* For alerts applicable to all clusters that start with Kafka-prod, your custom filter would be `db_cluster=mariadb-prod*`.
* For alerts applicable to a specific cluster within a production environment, your custom filter would be `db_cluster=mariadb-1` and `environment=prod`. This assumes you have set the optional environment tag while configuring collection.
-3. Go to Manage Data > Alerts > Monitors.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**.
5. Click Import and then copy-paste the above JSON to import monitors.
6. The monitors are disabled by default. Once you have installed the alerts using this method, navigate to the MariaDB folder under **Monitors** to configure them. See [this](/docs/alerts/monitors) document to enable monitors to send notifications to teams or connections. See the instructions detailed in [Add a Monitor](/docs/alerts/monitors/create-monitor).
@@ -526,7 +526,7 @@ Locate and install the app you need from the **App Catalog**. If you want to see
Version selection is not available for all apps.
:::
3. To install the app, complete the following fields.
- 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
+ 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
2. **Data Source.**
* Choose **Enter a Custom Data Filter**, and enter a custom MariaDB cluster filter. Examples;
1. For all MariaDB clusters, `db_cluster=*`.
diff --git a/docs/integrations/databases/memcached.md b/docs/integrations/databases/memcached.md
index 9b51f5c9f9..576f5f3218 100644
--- a/docs/integrations/databases/memcached.md
+++ b/docs/integrations/databases/memcached.md
@@ -218,7 +218,7 @@ This section explains the steps to collect Memcached logs from a Kubernetes envi
```
4. Sumo Logic Kubernetes collection will automatically start collecting logs from the pods having the annotations defined above.
3. **Add a FER to normalize the fields in Kubernetes environments**. This step is not needed if one is using application components solution terraform script. Labels created in Kubernetes environments automatically are prefixed with pod_labels. To normalize these for our app to work, we need to create a Field Extraction Rule if not already created for Proxy Application Components. To do so:
- 1. Go to **Manage Data > Logs > Field Extraction Rules**.
+ 1. In the main Sumo Logic menu, select **Manage Data > Logs > Field Extraction Rules**.
2. Click the + Add button on the top right of the table.
3. The **Add Field Extraction Rule** form will appear:
4. Enter the following options:
@@ -372,7 +372,7 @@ There are limits to how many alerts can be enabled. For more information, see [M
* For alerts applicable only to a specific cluster, your custom filter would be: `db_cluster=dev-memcached-01`
* For alerts applicable to all clusters that start with `memcached-prod`, your custom filter would be: `db_cluster=memcachedt-prod*`
* For alerts applicable to specific clusters within a production environment, your custom filter would be: `db_cluster=dev-memcached-01` AND `environment=prod`. This assumes you have set the optional environment tag while configuring collection.
-3. Go to **Manage Data > Alerts > Monitors**.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**.
4. Click **Import**.
6. On the **Import Content popup**, enter **Memcached** in the Name field, paste the JSON into the popup, and click **Import**.
diff --git a/docs/integrations/databases/mongodb.md b/docs/integrations/databases/mongodb.md
index ca047d0541..d742891716 100644
--- a/docs/integrations/databases/mongodb.md
+++ b/docs/integrations/databases/mongodb.md
@@ -235,7 +235,7 @@ Pivoting to Tracing data from Entity Inspector is possible only for “MongoDB a
```
5. Sumo Logic Kubernetes collection will automatically start collecting logs from the pods having the annotations defined above.
3. **Add an FER to normalize the fields in Kubernetes environments**. This step is not needed if one is using application components solution terraform script. Labels created in Kubernetes environments automatically are prefixed with `pod_labels`. To normalize these for our app to work, we need to create a Field Extraction Rule if not already created for Database Application Components. To do so:
- 1. Go to **Manage Data > Logs > Field Extraction Rules**.
+ 1. In the main Sumo Logic menu, select **Manage Data > Logs > Field Extraction Rules**.
2. Click the + Add button on the top right of the table.
3. The **Add Field Extraction Rule** form will appear:
4. Enter the following options:
@@ -427,7 +427,7 @@ There are limits to how many alerts can be enabled. For more information, see [M
1. Download the [JSON file](https://github.com/SumoLogic/terraform-sumologic-sumo-logic-monitor/blob/main/monitor_packages/MongoDB/MongoDB.json) that describes the monitors.
2. Replace `$$mongodb_data_source` with a custom source filter. To configure alerts for a specific database cluster, use a filter like `db_system=mongodb` or `db_cluster=dev-mongodb`. To configure the alerts for all of your clusters, set `$$mongodb_data_source` to blank (`""`).
-3. Go to **Manage Data > Alerts > Monitors**.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**.
5. Click **Import**.
6. On the **Import Content popup**, enter `MongoDB` in the Name field, paste in the JSON into the the popup, and click **Import**.
diff --git a/docs/integrations/databases/mysql.md b/docs/integrations/databases/mysql.md
index cdd76ee6c1..7b6cecf94d 100644
--- a/docs/integrations/databases/mysql.md
+++ b/docs/integrations/databases/mysql.md
@@ -346,7 +346,7 @@ Sumo Logic Kubernetes collection will automatically start collecting logs from t
2. **Add an FER to normalize the fields in Kubernetes environments**. This step is not needed if using application components solution terraform script. Labels created in Kubernetes environments are automatically prefixed with pod_labels. To normalize these for our app to work, we'll create a [Field Extraction Rule](/docs/manage/field-extractions/create-field-extraction-rule), Database Application Components, assuming it does not already exist:
- 1. Go to **Manage Data > Logs > Field Extraction Rules**.
+ 1. In the main Sumo Logic menu, select **Manage Data > Logs > Field Extraction Rules**.
2. Click the **+ Add**.
3. The **Add Field Extraction** pane appears.
4. **Rule Name.** Enter "App Observability - Database".
@@ -574,7 +574,7 @@ There are limits to how many alerts can be enabled. For more information, see [M
1. Download the [JSON file](https://github.com/SumoLogic/terraform-sumologic-sumo-logic-monitor/blob/main/monitor_packages/mysql/mysql.json) that describes the monitors.
2. Replace `$$mysql_data_source` with a custom source filter. To configure alerts for a specific database cluster, use a filter like `db_system=mysql` or `db_cluster=dev-mysql`. To configure the alerts for all of your clusters, set `$$mysql_data_source` to blank (`""`).
-3. Go to **Manage Data > Alerts > Monitors**.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**.
5. Click **Import.**
6. On the **Import Content popup**, enter "MySQL" in the Name field, paste in the JSON into the the popup, and click **Import**.
diff --git a/docs/integrations/databases/opentelemetry/cassandra-opentelemetry.md b/docs/integrations/databases/opentelemetry/cassandra-opentelemetry.md
index bad7a0d63e..3fcb226a94 100644
--- a/docs/integrations/databases/opentelemetry/cassandra-opentelemetry.md
+++ b/docs/integrations/databases/opentelemetry/cassandra-opentelemetry.md
@@ -11,9 +11,11 @@ import TabItem from '@theme/TabItem';
diff --git a/docs/integrations/containers-orchestration/rabbitmq.md b/docs/integrations/containers-orchestration/rabbitmq.md
index 80cfa7ba9e..a35468371d 100644
--- a/docs/integrations/containers-orchestration/rabbitmq.md
+++ b/docs/integrations/containers-orchestration/rabbitmq.md
@@ -463,7 +463,7 @@ This section demonstrates how to install the RabbitMQ App.
Version selection is not available for all apps.
:::
3. To install the app, complete the following fields.
- 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
+ 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
2. **Data Source.** Choose **Enter a Custom Data Filter**, and enter a custom RabbitMQ cluster filter. Examples:
1. For all RabbitMQ clusters: `messaging_cluster=*`
2. For a specific cluster: `messaging_cluster=rabbitmq.dev.01`
diff --git a/docs/integrations/databases/couchbase.md b/docs/integrations/databases/couchbase.md
index 9db4720cd3..fe4a125cb5 100644
--- a/docs/integrations/databases/couchbase.md
+++ b/docs/integrations/databases/couchbase.md
@@ -200,8 +200,8 @@ This section explains the steps to collect Couchbase logs from a Kubernetes envi
5. Sumo Logic Kubernetes collection will automatically start collecting logs from the pods having the annotations defined above.
6. Verify logs in Sumo Logic.
3. **Add a FER to normalize the fields in Kubernetes environments**. This step is not needed if using application components solution terraform script. Labels created in Kubernetes environments automatically are prefixed with pod_labels. To normalize these for our app to work, we need to create a Field Extraction Rule if not already created for Proxy Application Components. To do so:
- 1. Go to Manage Data > Logs > Field Extraction Rules.
- 2. Click the + Add button on the top right of the table.
+ 1. In the main Sumo Logic menu, select **Manage Data > Logs > Field Extraction Rules**.
+ 2. Click the **+ Add Rule** button on the top right of the table.
3. The **Add Field Extraction Rule** form will appear:
4. Enter the following options:
* **Rule Name**. Enter the name as **App Observability - Proxy**.
@@ -401,7 +401,7 @@ There are limits to how many alerts can be enabled - see the [Alerts FAQ](/docs/
1. For alerts applicable only to a specific cluster, your custom filter would be `'db_cluster=couchbase-standalone.01'`.
2. For alerts applicable to all cluster that start with couchbase-standalone, your custom filter would be,`db_cluster=couchbase-standalone*`.
3. For alerts applicable to a specific cluster within a production environment, your custom filter would be `db_cluster=couchbase-1` and `environment=standalone` (This assumes you have set the optional environment tag while configuring collection).
-3. Go to Manage Data > Alerts > Monitors.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**:
5. Click **Import** and then copy-paste the above JSON to import monitors.
6. The monitors are disabled by default. Once you have installed the alerts using this method, navigate to the Couchbase folder under **Monitors** to configure them. See [Monitor Settings](/docs/alerts/monitors/settings) to learn how to enable monitors to send notifications to teams or connections. See the instructions detailed in [Create a Monitor](/docs/alerts/monitors/create-monitor).
@@ -485,7 +485,7 @@ Locate and install the app you need from the **App Catalog**. If you want to see
Version selection is not available for all apps.
:::
3. To install the app, complete the following fields.
- 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
+ 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
2. **Data Source.**
* Choose **Enter a Custom Data Filter**, and enter a custom Couchbase cluster filter. Examples:
1. For all Couchbase clusters `db_cluster=*`
diff --git a/docs/integrations/databases/mariadb.md b/docs/integrations/databases/mariadb.md
index 48c06d4cb7..efad874a5f 100644
--- a/docs/integrations/databases/mariadb.md
+++ b/docs/integrations/databases/mariadb.md
@@ -448,7 +448,7 @@ Sumo Logic has provided out-of-the-box alerts available through [Sumo Logic moni
* For alerts applicable only to a specific cluster, your custom filter would be `db_cluster=mariadb-prod.01`.
* For alerts applicable to all clusters that start with Kafka-prod, your custom filter would be `db_cluster=mariadb-prod*`.
* For alerts applicable to a specific cluster within a production environment, your custom filter would be `db_cluster=mariadb-1` and `environment=prod`. This assumes you have set the optional environment tag while configuring collection.
-3. Go to Manage Data > Alerts > Monitors.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**.
5. Click Import and then copy-paste the above JSON to import monitors.
6. The monitors are disabled by default. Once you have installed the alerts using this method, navigate to the MariaDB folder under **Monitors** to configure them. See [this](/docs/alerts/monitors) document to enable monitors to send notifications to teams or connections. See the instructions detailed in [Add a Monitor](/docs/alerts/monitors/create-monitor).
@@ -526,7 +526,7 @@ Locate and install the app you need from the **App Catalog**. If you want to see
Version selection is not available for all apps.
:::
3. To install the app, complete the following fields.
- 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
+ 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
2. **Data Source.**
* Choose **Enter a Custom Data Filter**, and enter a custom MariaDB cluster filter. Examples;
1. For all MariaDB clusters, `db_cluster=*`.
diff --git a/docs/integrations/databases/memcached.md b/docs/integrations/databases/memcached.md
index 9b51f5c9f9..576f5f3218 100644
--- a/docs/integrations/databases/memcached.md
+++ b/docs/integrations/databases/memcached.md
@@ -218,7 +218,7 @@ This section explains the steps to collect Memcached logs from a Kubernetes envi
```
4. Sumo Logic Kubernetes collection will automatically start collecting logs from the pods having the annotations defined above.
3. **Add a FER to normalize the fields in Kubernetes environments**. This step is not needed if one is using application components solution terraform script. Labels created in Kubernetes environments automatically are prefixed with pod_labels. To normalize these for our app to work, we need to create a Field Extraction Rule if not already created for Proxy Application Components. To do so:
- 1. Go to **Manage Data > Logs > Field Extraction Rules**.
+ 1. In the main Sumo Logic menu, select **Manage Data > Logs > Field Extraction Rules**.
2. Click the + Add button on the top right of the table.
3. The **Add Field Extraction Rule** form will appear:
4. Enter the following options:
@@ -372,7 +372,7 @@ There are limits to how many alerts can be enabled. For more information, see [M
* For alerts applicable only to a specific cluster, your custom filter would be: `db_cluster=dev-memcached-01`
* For alerts applicable to all clusters that start with `memcached-prod`, your custom filter would be: `db_cluster=memcachedt-prod*`
* For alerts applicable to specific clusters within a production environment, your custom filter would be: `db_cluster=dev-memcached-01` AND `environment=prod`. This assumes you have set the optional environment tag while configuring collection.
-3. Go to **Manage Data > Alerts > Monitors**.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**.
4. Click **Import**.
6. On the **Import Content popup**, enter **Memcached** in the Name field, paste the JSON into the popup, and click **Import**.
diff --git a/docs/integrations/databases/mongodb.md b/docs/integrations/databases/mongodb.md
index ca047d0541..d742891716 100644
--- a/docs/integrations/databases/mongodb.md
+++ b/docs/integrations/databases/mongodb.md
@@ -235,7 +235,7 @@ Pivoting to Tracing data from Entity Inspector is possible only for “MongoDB a
```
5. Sumo Logic Kubernetes collection will automatically start collecting logs from the pods having the annotations defined above.
3. **Add an FER to normalize the fields in Kubernetes environments**. This step is not needed if one is using application components solution terraform script. Labels created in Kubernetes environments automatically are prefixed with `pod_labels`. To normalize these for our app to work, we need to create a Field Extraction Rule if not already created for Database Application Components. To do so:
- 1. Go to **Manage Data > Logs > Field Extraction Rules**.
+ 1. In the main Sumo Logic menu, select **Manage Data > Logs > Field Extraction Rules**.
2. Click the + Add button on the top right of the table.
3. The **Add Field Extraction Rule** form will appear:
4. Enter the following options:
@@ -427,7 +427,7 @@ There are limits to how many alerts can be enabled. For more information, see [M
1. Download the [JSON file](https://github.com/SumoLogic/terraform-sumologic-sumo-logic-monitor/blob/main/monitor_packages/MongoDB/MongoDB.json) that describes the monitors.
2. Replace `$$mongodb_data_source` with a custom source filter. To configure alerts for a specific database cluster, use a filter like `db_system=mongodb` or `db_cluster=dev-mongodb`. To configure the alerts for all of your clusters, set `$$mongodb_data_source` to blank (`""`).
-3. Go to **Manage Data > Alerts > Monitors**.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**.
5. Click **Import**.
6. On the **Import Content popup**, enter `MongoDB` in the Name field, paste in the JSON into the the popup, and click **Import**.
diff --git a/docs/integrations/databases/mysql.md b/docs/integrations/databases/mysql.md
index cdd76ee6c1..7b6cecf94d 100644
--- a/docs/integrations/databases/mysql.md
+++ b/docs/integrations/databases/mysql.md
@@ -346,7 +346,7 @@ Sumo Logic Kubernetes collection will automatically start collecting logs from t
2. **Add an FER to normalize the fields in Kubernetes environments**. This step is not needed if using application components solution terraform script. Labels created in Kubernetes environments are automatically prefixed with pod_labels. To normalize these for our app to work, we'll create a [Field Extraction Rule](/docs/manage/field-extractions/create-field-extraction-rule), Database Application Components, assuming it does not already exist:
- 1. Go to **Manage Data > Logs > Field Extraction Rules**.
+ 1. In the main Sumo Logic menu, select **Manage Data > Logs > Field Extraction Rules**.
2. Click the **+ Add**.
3. The **Add Field Extraction** pane appears.
4. **Rule Name.** Enter "App Observability - Database".
@@ -574,7 +574,7 @@ There are limits to how many alerts can be enabled. For more information, see [M
1. Download the [JSON file](https://github.com/SumoLogic/terraform-sumologic-sumo-logic-monitor/blob/main/monitor_packages/mysql/mysql.json) that describes the monitors.
2. Replace `$$mysql_data_source` with a custom source filter. To configure alerts for a specific database cluster, use a filter like `db_system=mysql` or `db_cluster=dev-mysql`. To configure the alerts for all of your clusters, set `$$mysql_data_source` to blank (`""`).
-3. Go to **Manage Data > Alerts > Monitors**.
+3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
4. Click **Add**.
5. Click **Import.**
6. On the **Import Content popup**, enter "MySQL" in the Name field, paste in the JSON into the the popup, and click **Import**.
diff --git a/docs/integrations/databases/opentelemetry/cassandra-opentelemetry.md b/docs/integrations/databases/opentelemetry/cassandra-opentelemetry.md
index bad7a0d63e..3fcb226a94 100644
--- a/docs/integrations/databases/opentelemetry/cassandra-opentelemetry.md
+++ b/docs/integrations/databases/opentelemetry/cassandra-opentelemetry.md
@@ -11,9 +11,11 @@ import TabItem from '@theme/TabItem';
})
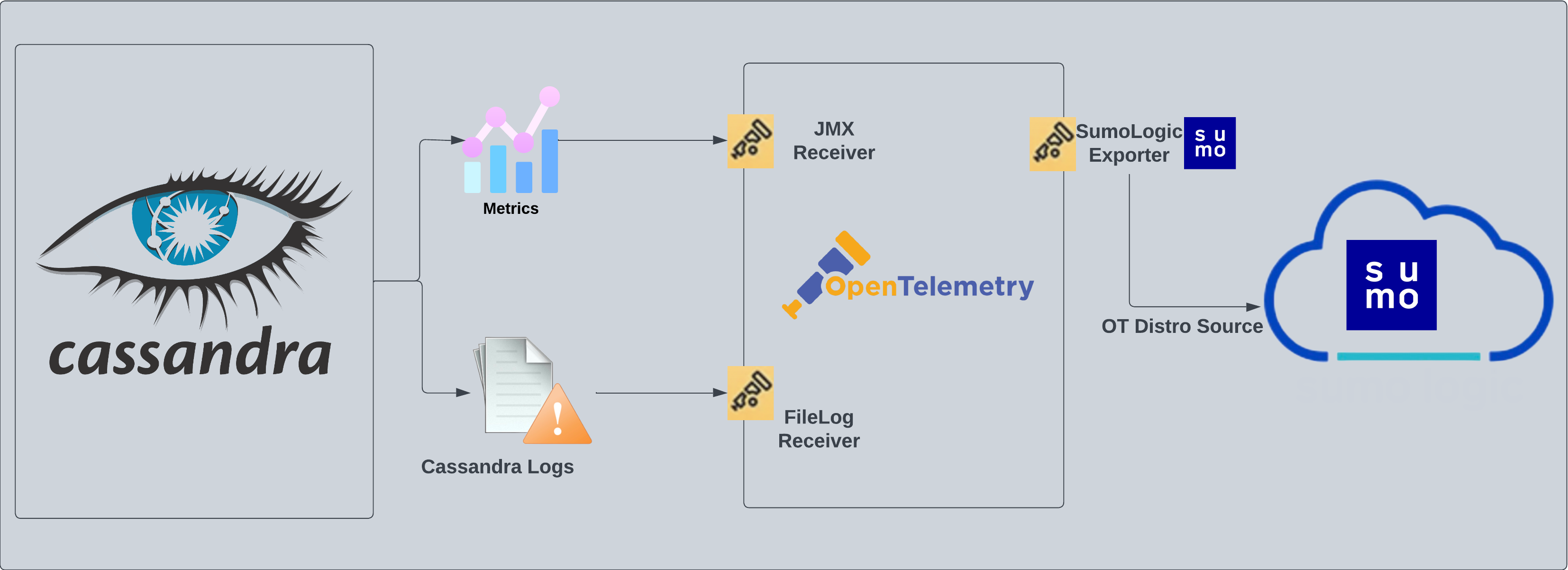 @@ -21,13 +23,27 @@ The app supports Logs from the open-source version of Cassandra. The App is test
Following are the [Fields](/docs/manage/fields/) which will be created as part of Cassandra App install if not already present:
+- `deployment.environment`. User configured. Through this Cassandra cluster is identified by the environment where it resides. For example: dev, prod, or qa.
- `db.cluster.name`. User configured. Enter a name to identify this Cassandra cluster. This cluster name will be shown in the Sumo Logic dashboards.
- `db.system`. Has fixed value of **cassandra**.
-- `deployment.environment`. User configured. Through this Cassandra cluster is identified by the environment where it resides. For example: dev, prod or qa.
+- `db.node.name`. Holds the value of the Fully Qualified Domain Name (FQDN) of the machine from which the OpenTelemetry collector is collecting logs and metrics.
- `sumo.datasource`. Has fixed value of **cassandra**.
## Prerequisites
+#### For metric collection
+
+JMX receiver collects Cassandra metrics from Cassandra server as part of the OpenTelemetry Collector (OTC).
+
+ 1. Follow the instructions in [JMX - OpenTelemetry's prerequisites section](/docs/integrations/app-development/opentelemetry/jmx-opentelemetry/#prerequisites) to download the [JMX Metric Gatherer](https://github.com/open-telemetry/opentelemetry-java-contrib/blob/main/jmx-metrics/README.md). This gatherer is used by the [JMX Receiver](https://github.com/open-telemetry/opentelemetry-collector-contrib/tree/main/receiver/jmxreceiver#details).
+
+ 2. Set the JMX port as part of `JAVA_OPTS` for Tomcat startup. Usually, it is set in the `/etc/systemd/system/cassandra.service` or `C:\Program Files\apache-tomcat\bin\tomcat.bat` file.
+
+ ```json
+ JAVA_OPTS="$JAVA_OPTS -Dcom.sun.management.jmxremote -Dcom.sun.management.jmxremote.port=11099 -Dcom.sun.management.jmxremote.authenticate=true -Dcom.sun.management.jmxremote.ssl=false -Dcom.sun.management.jmxremote.password.file=${CASSANDRA_CONF_DIR}/jmx.password -Dcom.sun.management.jmxremote.access.file=${CASSANDRA_CONF_DIR}/jmx.access"
+ ```
+
+#### For log collection
Cassandra has three main logs: system.log, debug.log, and gc.log which hold general logging messages, debugging logging messages, and java garbage collection logs respectively.
These logs by default live in `${CASSANDRA_HOME}/logs`, but most Linux distributions relocate logs to `/var/log/cassandra`. Operators can tune this location as well as what levels are logged using the provided logback.xml file. For more details on Cassandra logs, see[ this](https://cassandra.apache.org/doc/latest/troubleshooting/reading_logs.html) link.
@@ -56,6 +72,7 @@ In this step, you will configure the yaml required for Cassandra Collection. Pat
Below are the inputs required:
- The path to system.log is required here. This file is typically located in `/var/log/cassandra`. If you're using a customized path, check the respective conf file for this information.
+- For metrics, you're required to provide the JMX endpoint (default is `localhost:7199`) along with the `collection_interval` (default is 1 minute).
You can add any custom fields which you want to be tagged with the data ingested in Sumo. Click on the **Download YAML File** button to get the yaml file.
@@ -122,7 +139,44 @@ import LogsOutro from '../../../reuse/apps/opentelemetry/send-logs-outro.md';
INFO [ScheduledTasks:1] 2023-01-08 09:18:47,347 StatusLogger.java:101 - system.schema_aggregates
```
-## Sample queries
+## Sample metrics message
+
+```json
+{
+ "queryId": "A",
+ "_source": "cassandra-otel",
+ "_metricId": "dasIFS6RvCVxEcsljWGpnQ",
+ "_sourceName": "Http Input",
+ "host.id": "i-071ade75d03650657",
+ "host.group": "cassandraHostGrp",
+ "telemetry.sdk.version": "1.38.0",
+ "os.type": "linux",
+ "sumo.datasource": "cassandra",
+ "db.system": "cassandra",
+ "db.node.name": "ip-54-163-607-30.ec2.internal",
+ "_sourceCategory": "Labs/cassandra-otel",
+ "deployment.environment": "dev",
+ "_contentType": "Carbon2",
+ "host.name": "ip-54-163-607-30.ec2.internal",
+ "metric": "cassandra.client.request.write.latency.50p",
+ "_collectorId": "000000000FB3B451",
+ "_sourceId": "000000005A60F624",
+ "unit": "us",
+ "db.cluster.name": "cassandra_cluster",
+ "telemetry.sdk.language": "java",
+ "telemetry.sdk.name": "opentelemetry",
+ "service.name": "unknown_service:java",
+ "_collector": "Labs - cassandra-otel",
+ "max": 229,
+ "min": 0,
+ "avg": 131.25,
+ "sum": 525,
+ "latest": 67,
+ "count": 4
+}
+```
+
+## Sample log queries
Following is the query from Cassandra App's overview Dashboard's Nodes Up Panel:
@@ -136,7 +190,14 @@ Following is the query from Cassandra App's overview Dashboard's Nodes Up Panel:
| sort by _timeslice asc
```
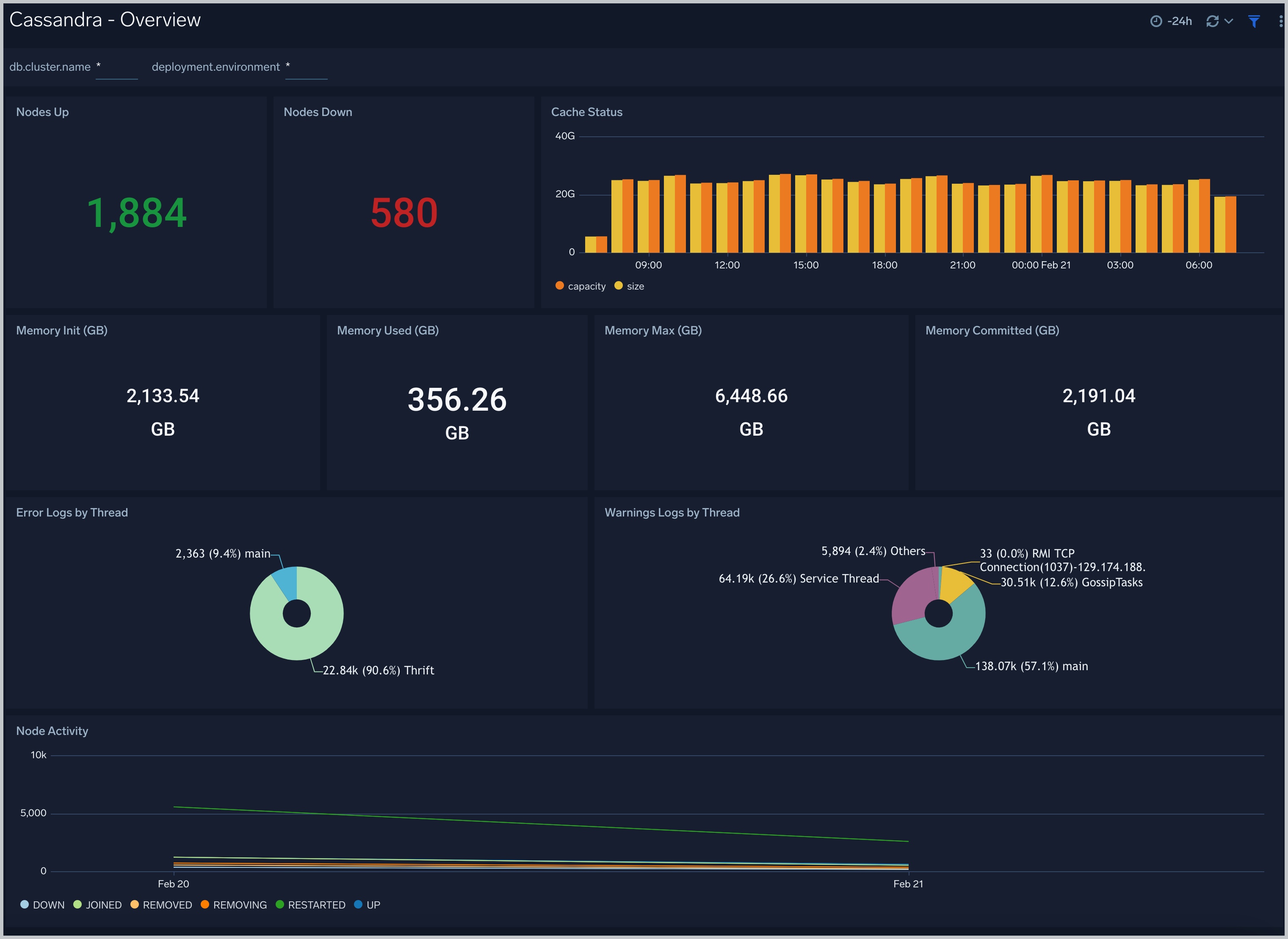
-## Viewing Cassandra Dashboards
+## Sample metrics query
+Following is the query from Cassandra App's overview Dashboard's Number of Requests Panel:
+
+```sql
+sumo.datasource=cassandra deployment.environment=* db.cluster.name=* db.node.name=* metric=cassandra.client.request.count | sum
+```
+
+## Viewing Cassandra dashboards
### Overview
@@ -148,7 +209,7 @@ Use this dashboard to:
- Gain insights into Memory - Init, used, Max and committed
- Gain insights into the error and warning logs by thread and Node activity
-
@@ -21,13 +23,27 @@ The app supports Logs from the open-source version of Cassandra. The App is test
Following are the [Fields](/docs/manage/fields/) which will be created as part of Cassandra App install if not already present:
+- `deployment.environment`. User configured. Through this Cassandra cluster is identified by the environment where it resides. For example: dev, prod, or qa.
- `db.cluster.name`. User configured. Enter a name to identify this Cassandra cluster. This cluster name will be shown in the Sumo Logic dashboards.
- `db.system`. Has fixed value of **cassandra**.
-- `deployment.environment`. User configured. Through this Cassandra cluster is identified by the environment where it resides. For example: dev, prod or qa.
+- `db.node.name`. Holds the value of the Fully Qualified Domain Name (FQDN) of the machine from which the OpenTelemetry collector is collecting logs and metrics.
- `sumo.datasource`. Has fixed value of **cassandra**.
## Prerequisites
+#### For metric collection
+
+JMX receiver collects Cassandra metrics from Cassandra server as part of the OpenTelemetry Collector (OTC).
+
+ 1. Follow the instructions in [JMX - OpenTelemetry's prerequisites section](/docs/integrations/app-development/opentelemetry/jmx-opentelemetry/#prerequisites) to download the [JMX Metric Gatherer](https://github.com/open-telemetry/opentelemetry-java-contrib/blob/main/jmx-metrics/README.md). This gatherer is used by the [JMX Receiver](https://github.com/open-telemetry/opentelemetry-collector-contrib/tree/main/receiver/jmxreceiver#details).
+
+ 2. Set the JMX port as part of `JAVA_OPTS` for Tomcat startup. Usually, it is set in the `/etc/systemd/system/cassandra.service` or `C:\Program Files\apache-tomcat\bin\tomcat.bat` file.
+
+ ```json
+ JAVA_OPTS="$JAVA_OPTS -Dcom.sun.management.jmxremote -Dcom.sun.management.jmxremote.port=11099 -Dcom.sun.management.jmxremote.authenticate=true -Dcom.sun.management.jmxremote.ssl=false -Dcom.sun.management.jmxremote.password.file=${CASSANDRA_CONF_DIR}/jmx.password -Dcom.sun.management.jmxremote.access.file=${CASSANDRA_CONF_DIR}/jmx.access"
+ ```
+
+#### For log collection
Cassandra has three main logs: system.log, debug.log, and gc.log which hold general logging messages, debugging logging messages, and java garbage collection logs respectively.
These logs by default live in `${CASSANDRA_HOME}/logs`, but most Linux distributions relocate logs to `/var/log/cassandra`. Operators can tune this location as well as what levels are logged using the provided logback.xml file. For more details on Cassandra logs, see[ this](https://cassandra.apache.org/doc/latest/troubleshooting/reading_logs.html) link.
@@ -56,6 +72,7 @@ In this step, you will configure the yaml required for Cassandra Collection. Pat
Below are the inputs required:
- The path to system.log is required here. This file is typically located in `/var/log/cassandra`. If you're using a customized path, check the respective conf file for this information.
+- For metrics, you're required to provide the JMX endpoint (default is `localhost:7199`) along with the `collection_interval` (default is 1 minute).
You can add any custom fields which you want to be tagged with the data ingested in Sumo. Click on the **Download YAML File** button to get the yaml file.
@@ -122,7 +139,44 @@ import LogsOutro from '../../../reuse/apps/opentelemetry/send-logs-outro.md';
INFO [ScheduledTasks:1] 2023-01-08 09:18:47,347 StatusLogger.java:101 - system.schema_aggregates
```
-## Sample queries
+## Sample metrics message
+
+```json
+{
+ "queryId": "A",
+ "_source": "cassandra-otel",
+ "_metricId": "dasIFS6RvCVxEcsljWGpnQ",
+ "_sourceName": "Http Input",
+ "host.id": "i-071ade75d03650657",
+ "host.group": "cassandraHostGrp",
+ "telemetry.sdk.version": "1.38.0",
+ "os.type": "linux",
+ "sumo.datasource": "cassandra",
+ "db.system": "cassandra",
+ "db.node.name": "ip-54-163-607-30.ec2.internal",
+ "_sourceCategory": "Labs/cassandra-otel",
+ "deployment.environment": "dev",
+ "_contentType": "Carbon2",
+ "host.name": "ip-54-163-607-30.ec2.internal",
+ "metric": "cassandra.client.request.write.latency.50p",
+ "_collectorId": "000000000FB3B451",
+ "_sourceId": "000000005A60F624",
+ "unit": "us",
+ "db.cluster.name": "cassandra_cluster",
+ "telemetry.sdk.language": "java",
+ "telemetry.sdk.name": "opentelemetry",
+ "service.name": "unknown_service:java",
+ "_collector": "Labs - cassandra-otel",
+ "max": 229,
+ "min": 0,
+ "avg": 131.25,
+ "sum": 525,
+ "latest": 67,
+ "count": 4
+}
+```
+
+## Sample log queries
Following is the query from Cassandra App's overview Dashboard's Nodes Up Panel:
@@ -136,7 +190,14 @@ Following is the query from Cassandra App's overview Dashboard's Nodes Up Panel:
| sort by _timeslice asc
```
-## Viewing Cassandra Dashboards
+## Sample metrics query
+Following is the query from Cassandra App's overview Dashboard's Number of Requests Panel:
+
+```sql
+sumo.datasource=cassandra deployment.environment=* db.cluster.name=* db.node.name=* metric=cassandra.client.request.count | sum
+```
+
+## Viewing Cassandra dashboards
### Overview
@@ -148,7 +209,7 @@ Use this dashboard to:
- Gain insights into Memory - Init, used, Max and committed
- Gain insights into the error and warning logs by thread and Node activity
- +
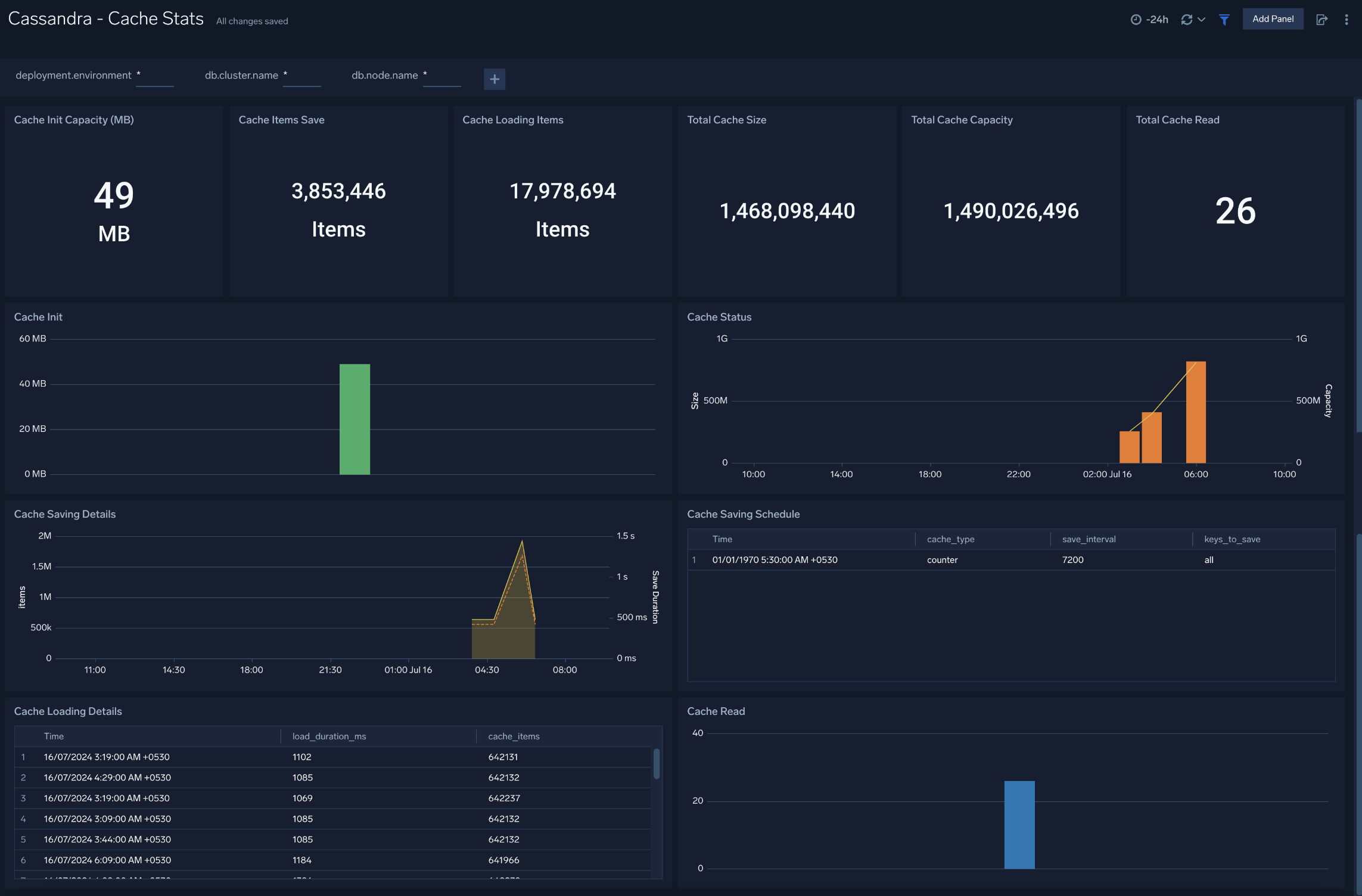
+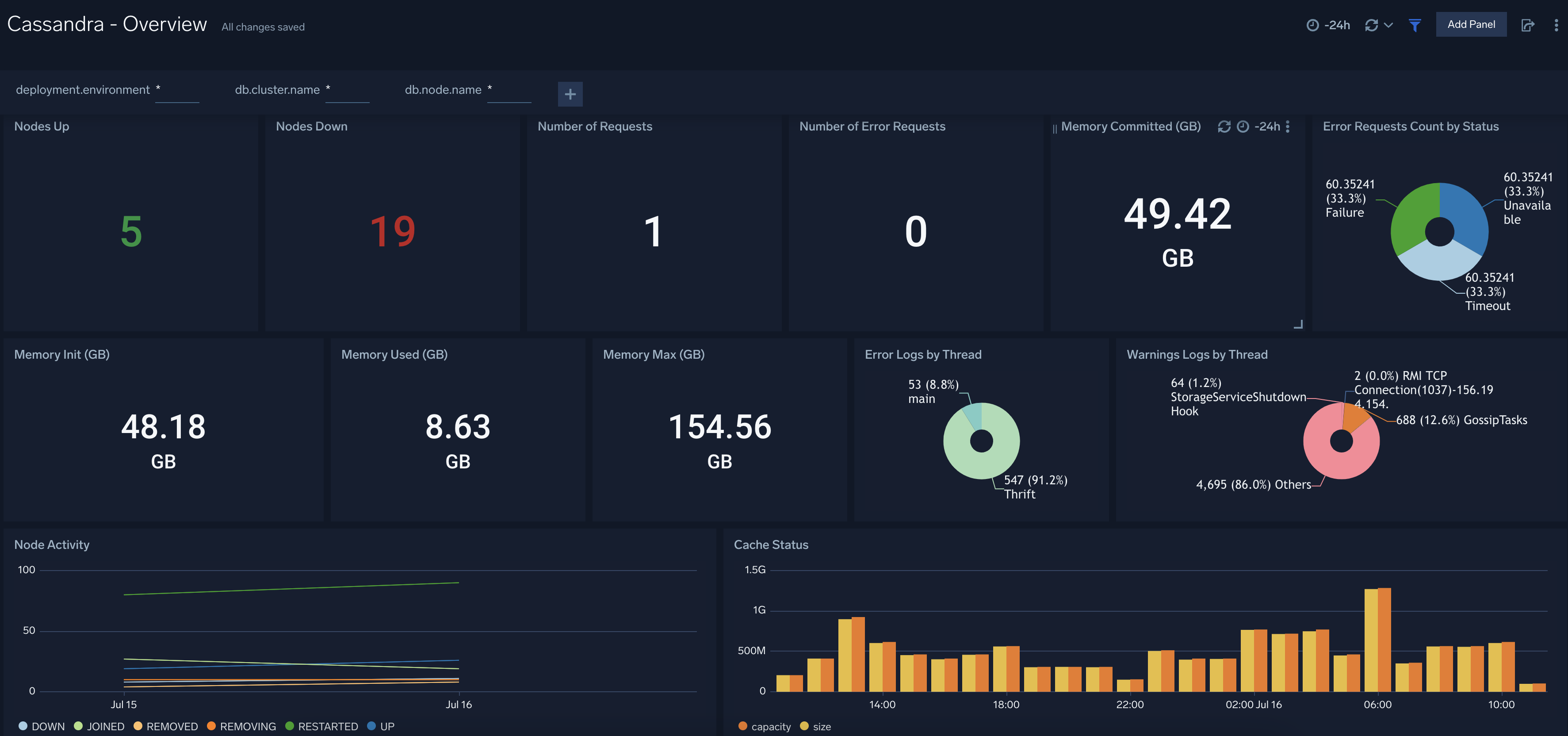 ### Cache Stats
@@ -159,7 +220,7 @@ Use this dashboard to:
- Monitor Cache performance.
- Identify Cache usage statistics.
-
### Cache Stats
@@ -159,7 +220,7 @@ Use this dashboard to:
- Monitor Cache performance.
- Identify Cache usage statistics.
-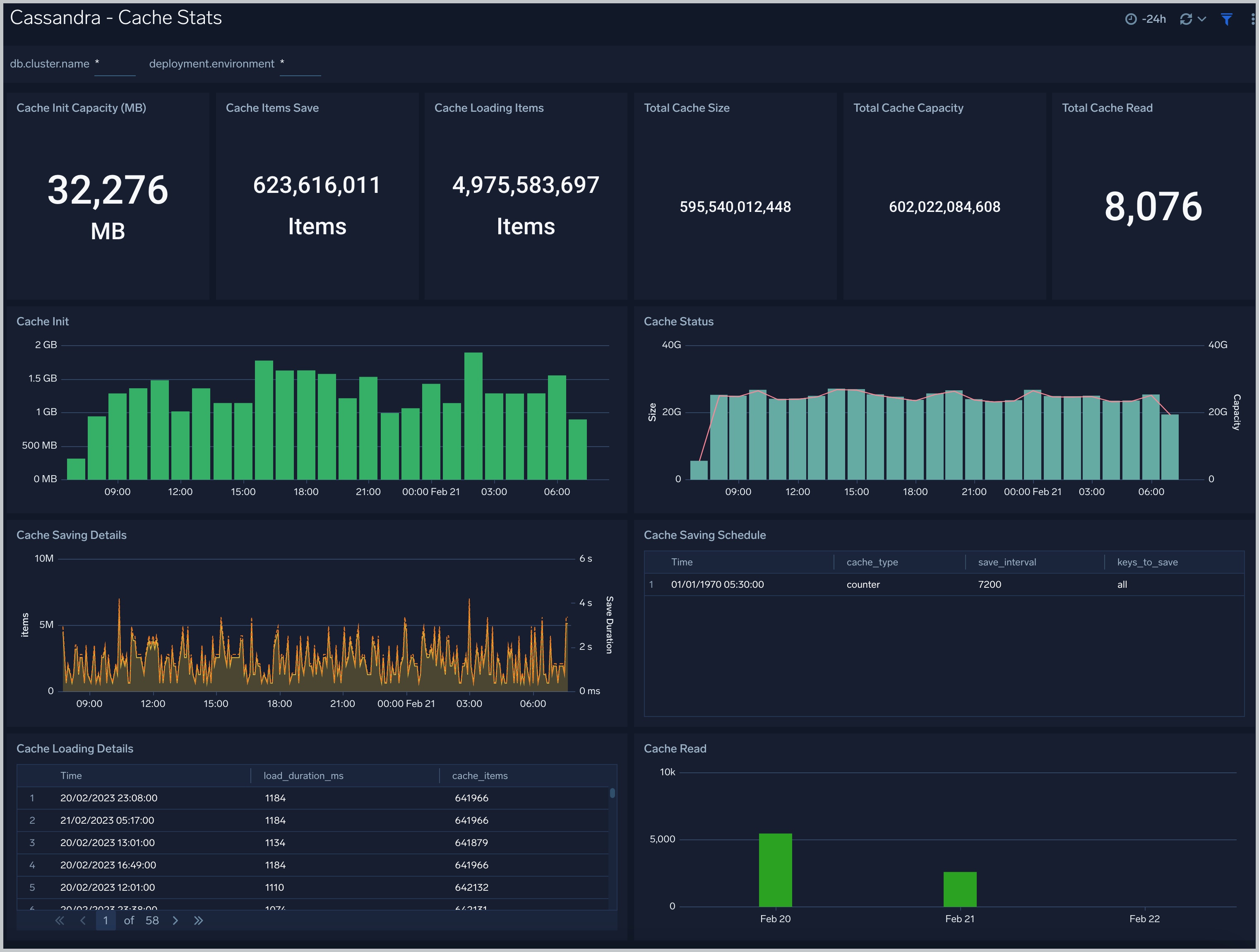 +
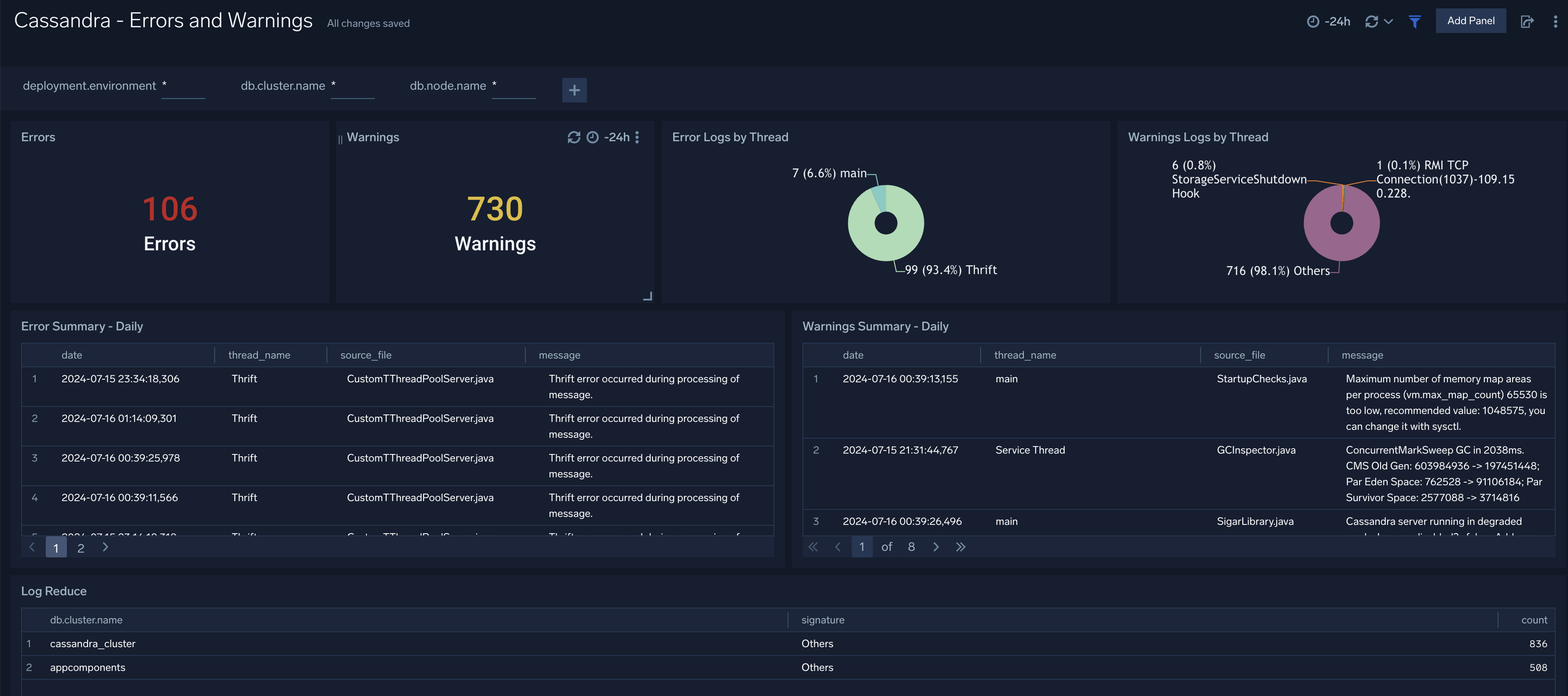
+ ### Errors and Warnings
@@ -170,7 +231,7 @@ Use this dashboard to:
- Review errors and warnings generated by the server.
- Review the Threads errors and warning events.
-
### Errors and Warnings
@@ -170,7 +231,7 @@ Use this dashboard to:
- Review errors and warnings generated by the server.
- Review the Threads errors and warning events.
-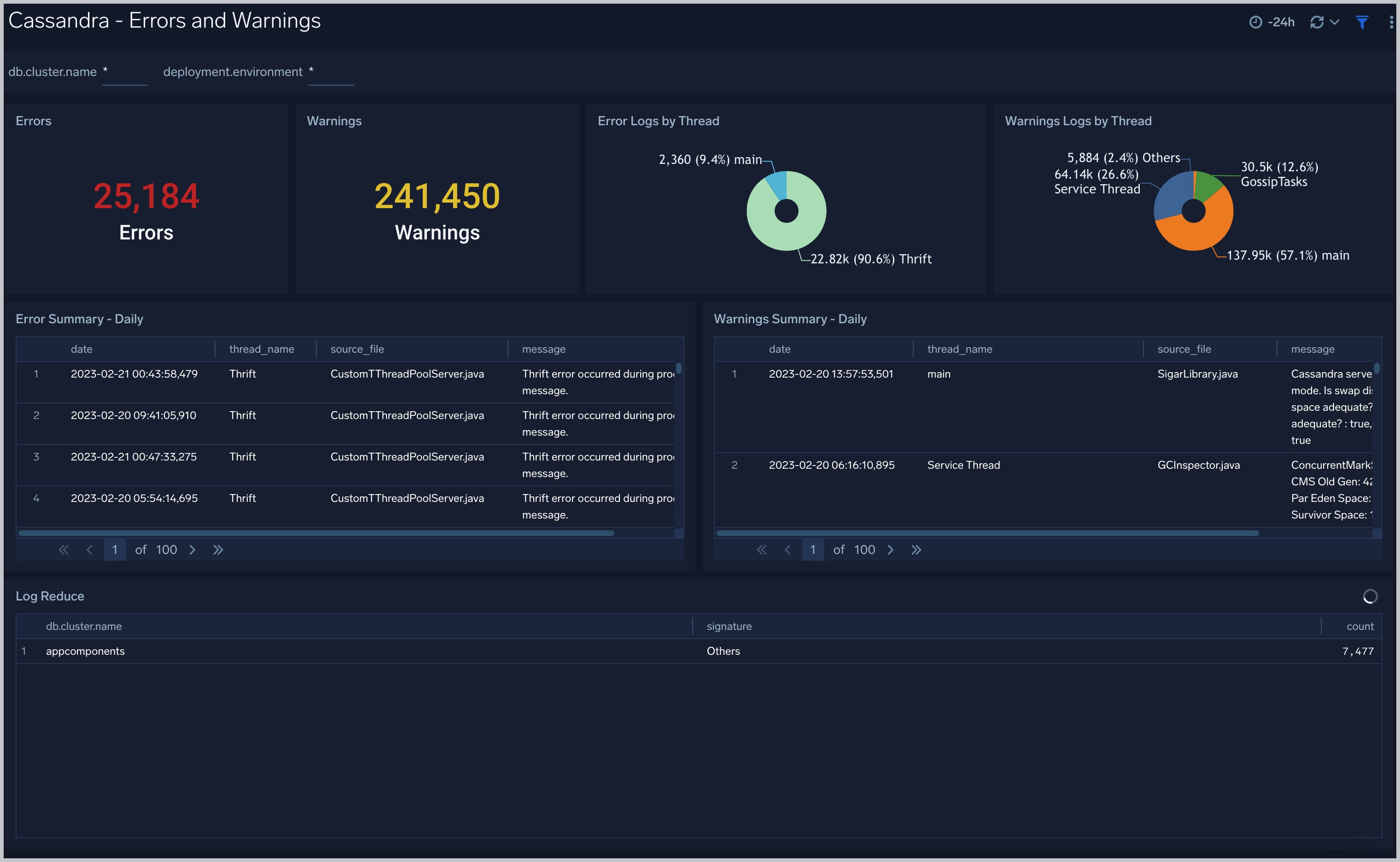 +
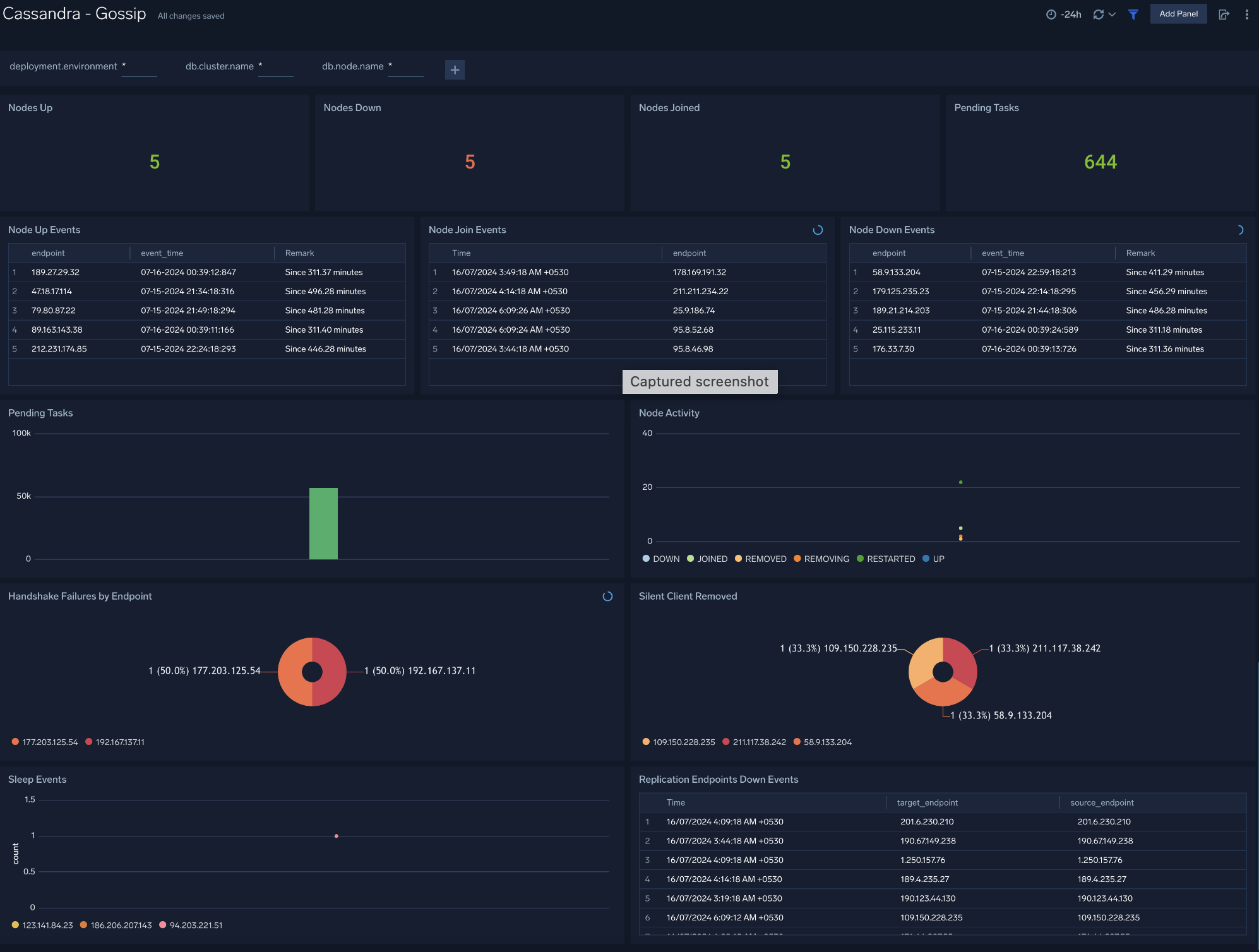
+ ### Gossip
@@ -181,7 +242,7 @@ Use this dashboard to:
- Determine nodes with errors resulting in failures.
- Review the node activity and pending tasks.
-
### Gossip
@@ -181,7 +242,7 @@ Use this dashboard to:
- Determine nodes with errors resulting in failures.
- Review the node activity and pending tasks.
-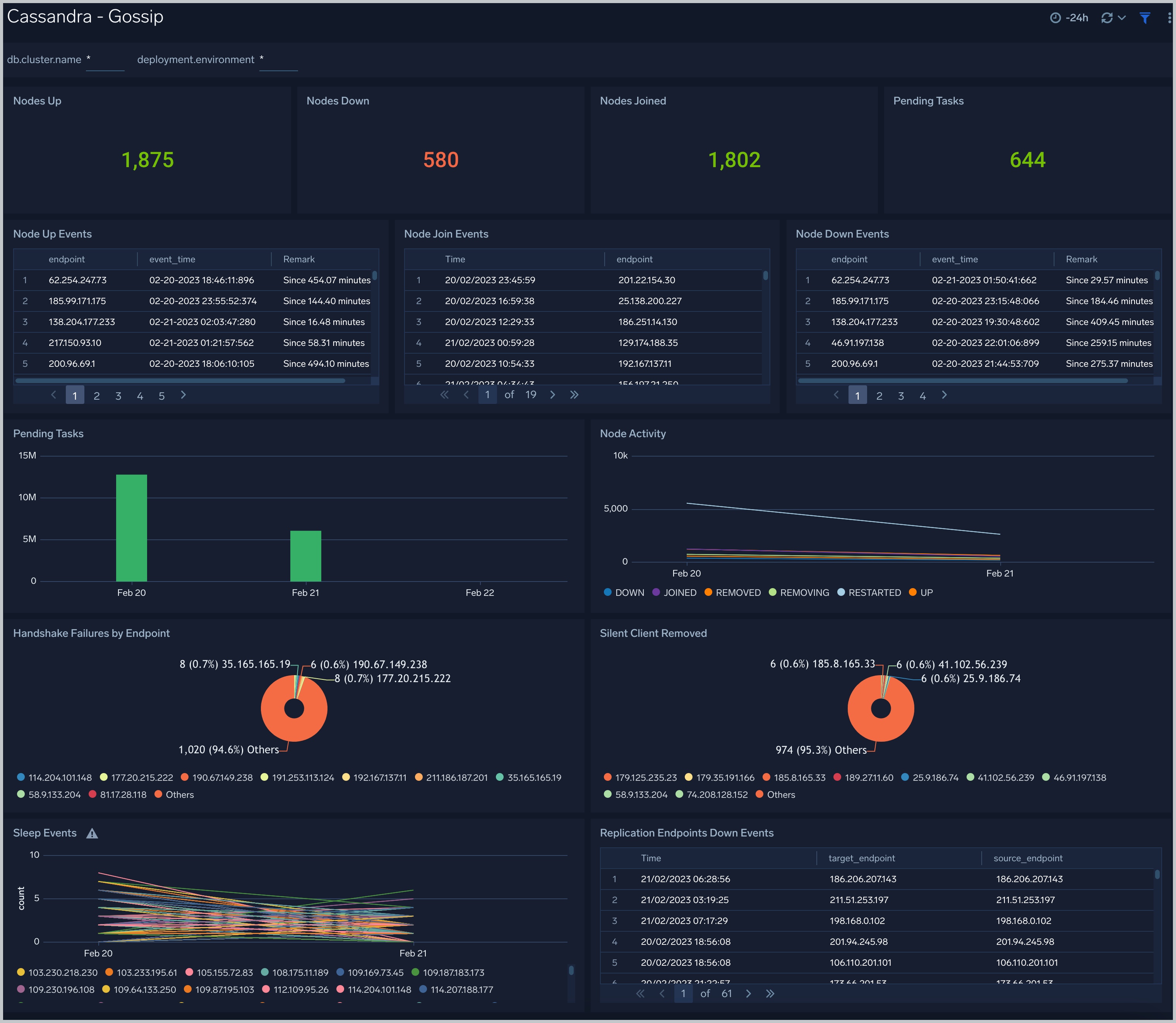 +
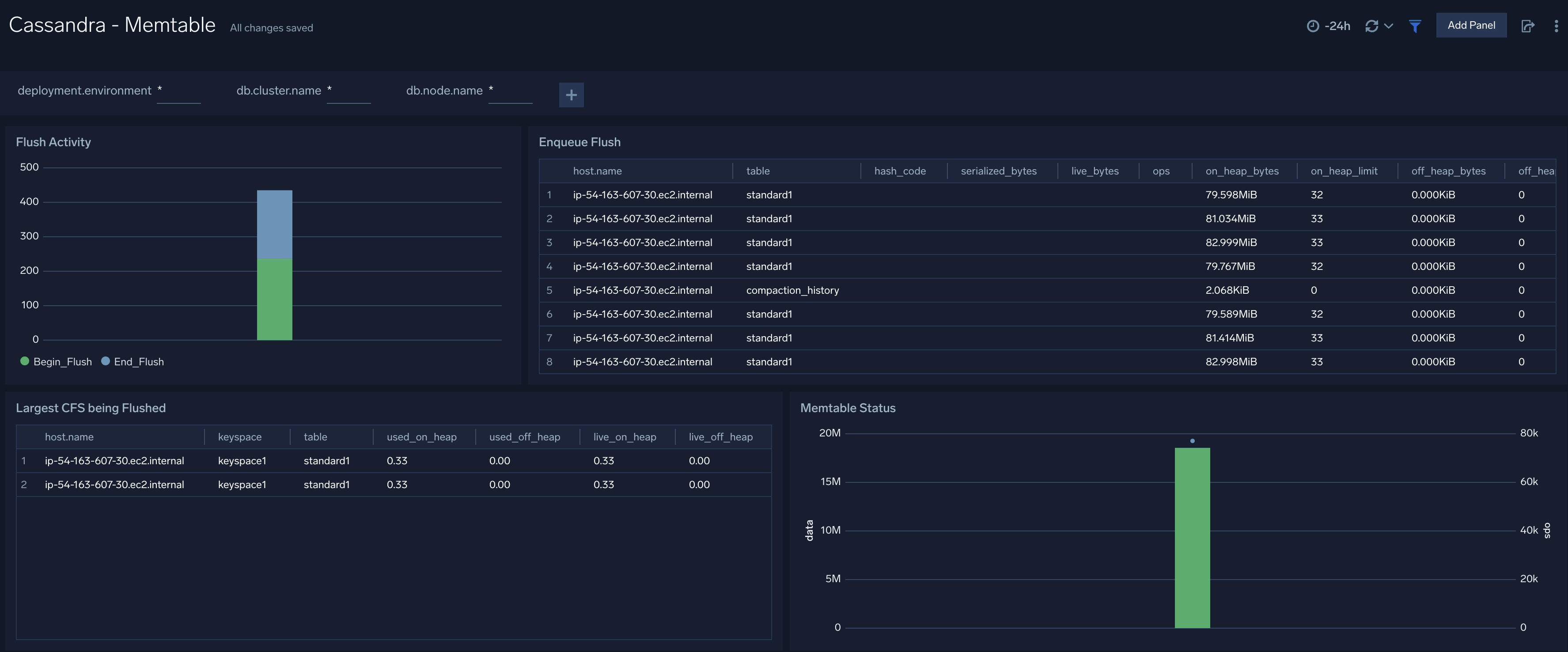
+ ### Memtable
@@ -191,7 +252,7 @@ Use this dashboard to:
- Review flush activity and memtable status.
-
### Memtable
@@ -191,7 +252,7 @@ Use this dashboard to:
- Review flush activity and memtable status.
-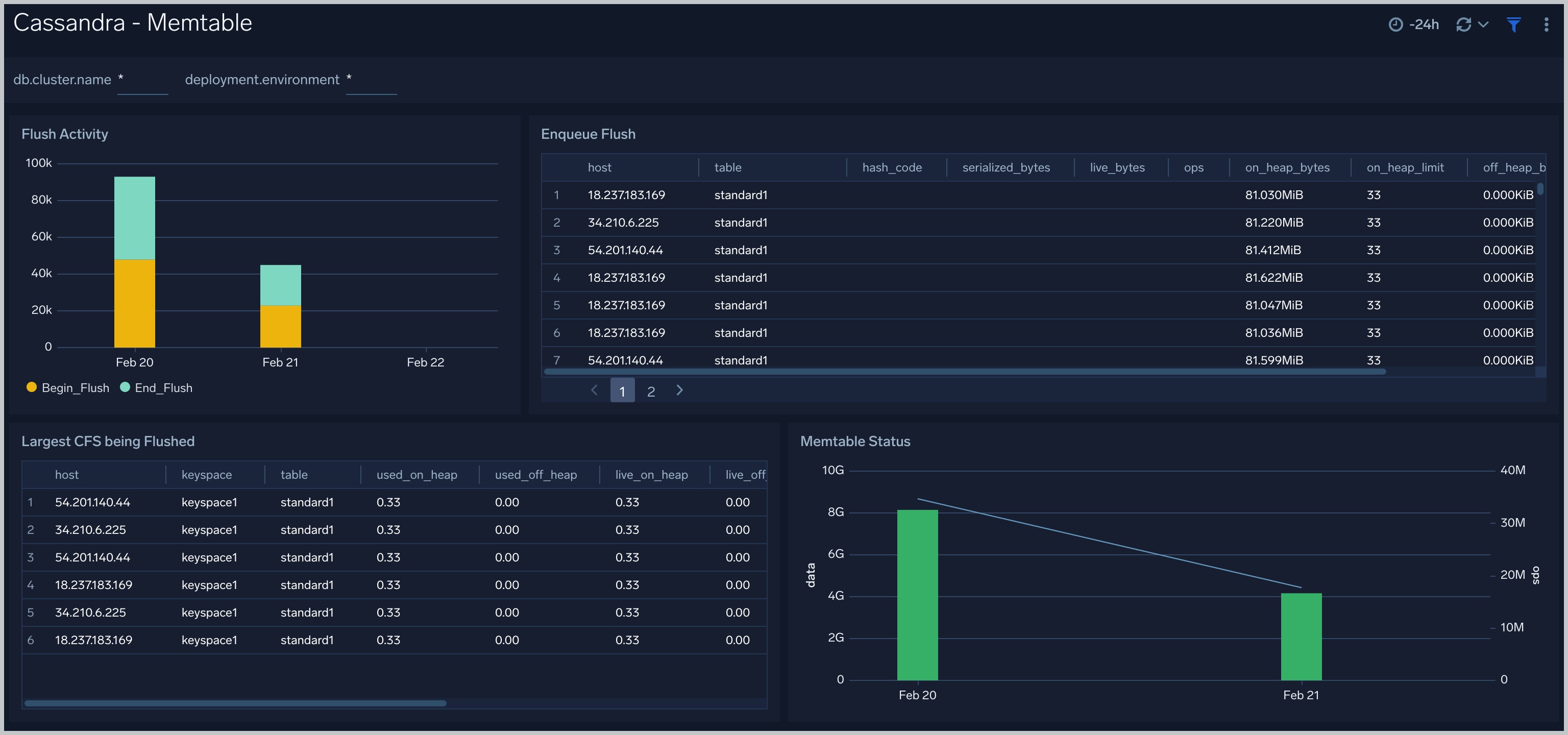 +
+ ### Resource Usage
@@ -201,4 +262,20 @@ Use this dashboard to:
- Identify resource utilization. This can help you to determine whether resources are over-allocated or under-allocated.
-
### Resource Usage
@@ -201,4 +262,20 @@ Use this dashboard to:
- Identify resource utilization. This can help you to determine whether resources are over-allocated or under-allocated.
- +
+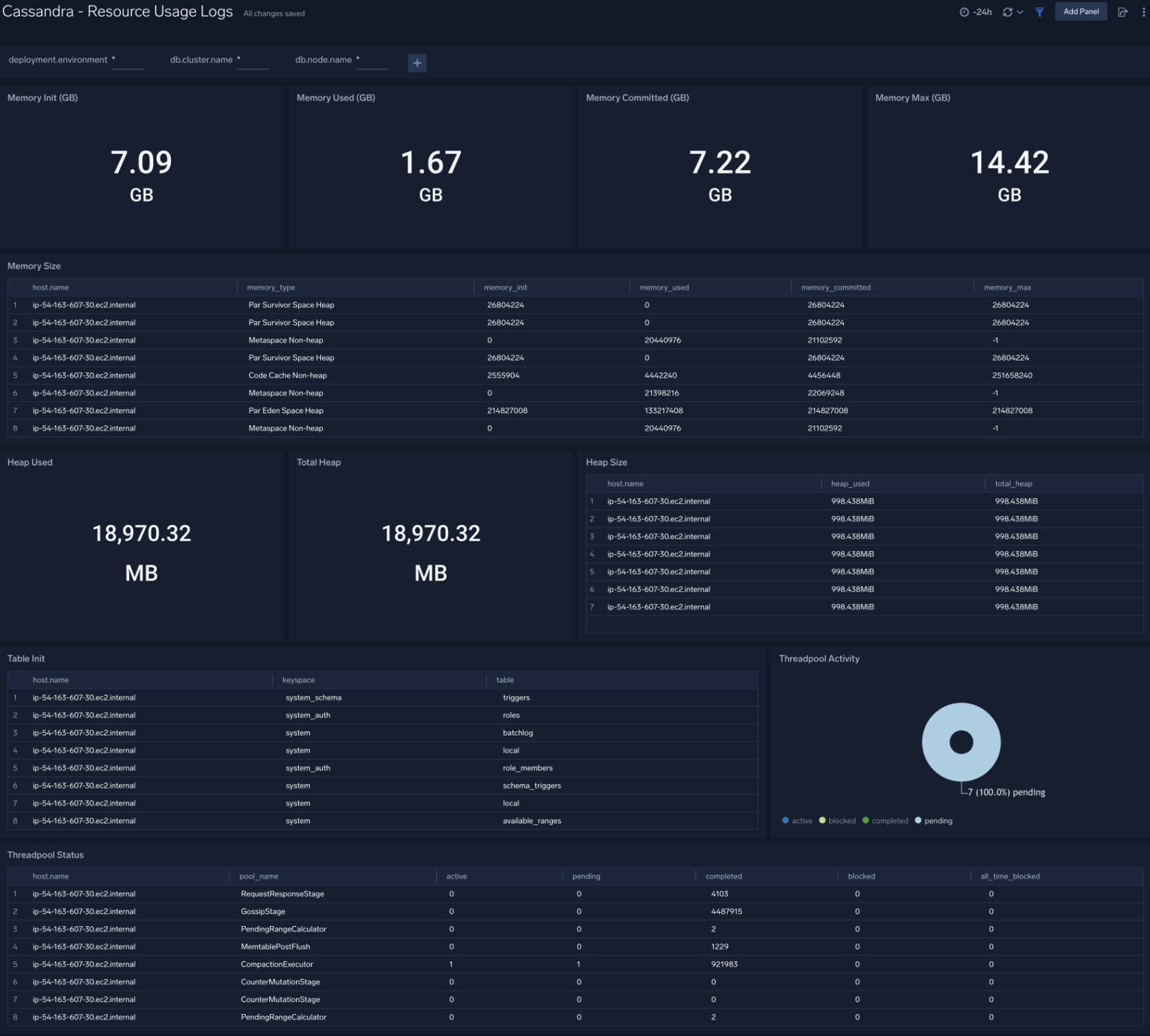 +
+### Compaction
+
+The **Cassandra - Compactions** dashboard provides insight into the completed and pending compaction tasks.
+
+
+### Compaction
+
+The **Cassandra - Compactions** dashboard provides insight into the completed and pending compaction tasks.
+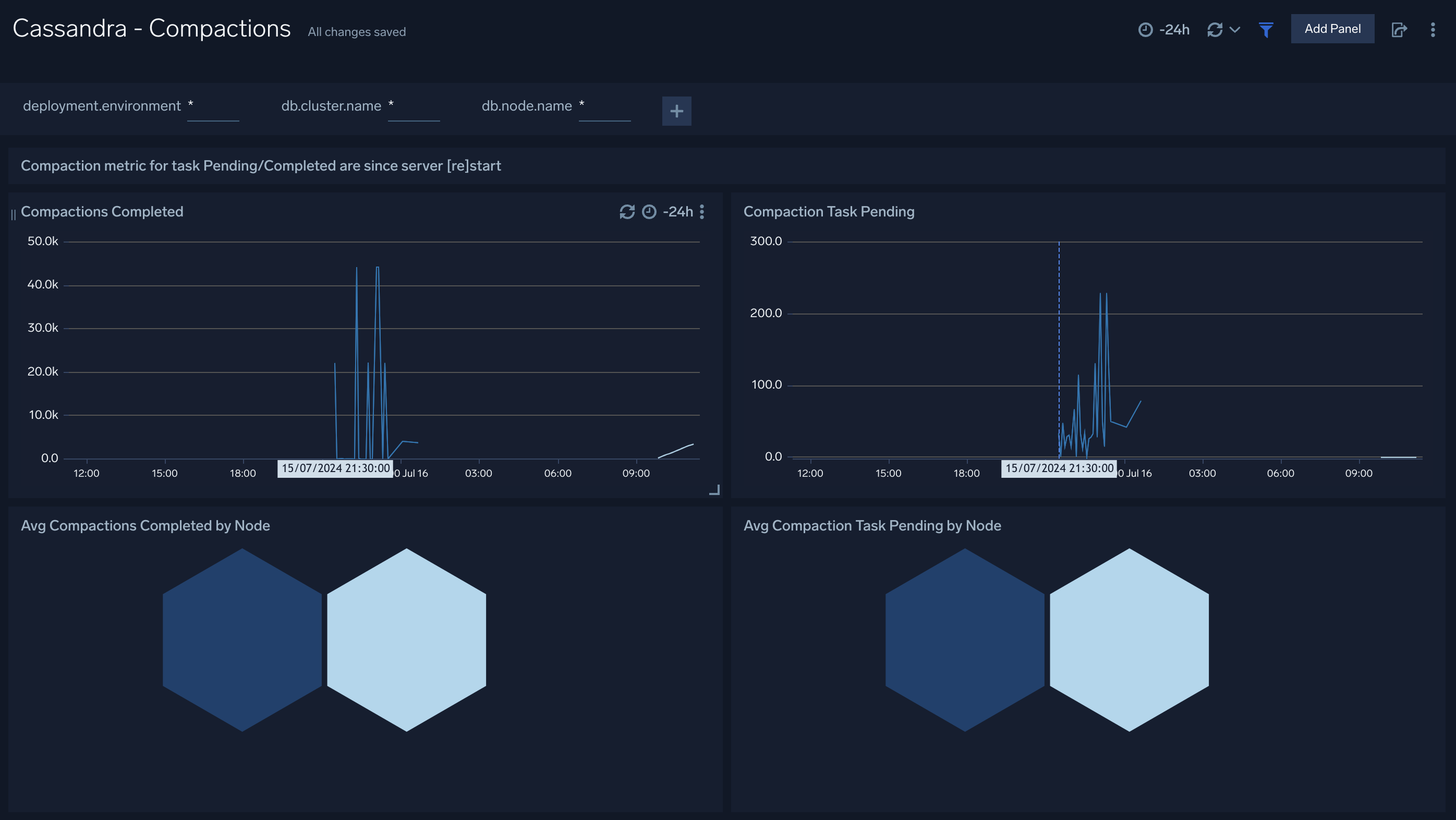 +
+### Requests
+
+The **Cassandra - Requests** dashboard provides insight into the number of request served, number of error request, and their distribution by status and operation. Also you can monitor the read and write latency of the cluster instance using this dashboard.
+
+
+### Requests
+
+The **Cassandra - Requests** dashboard provides insight into the number of request served, number of error request, and their distribution by status and operation. Also you can monitor the read and write latency of the cluster instance using this dashboard.
+ +
+### Storage
+
+The **Cassandra - Storage** dashboard provides insight into the current value of total hints of your Cassandra cluster along with storage managed by the cluster.
+
+
+
+### Storage
+
+The **Cassandra - Storage** dashboard provides insight into the current value of total hints of your Cassandra cluster along with storage managed by the cluster.
+
+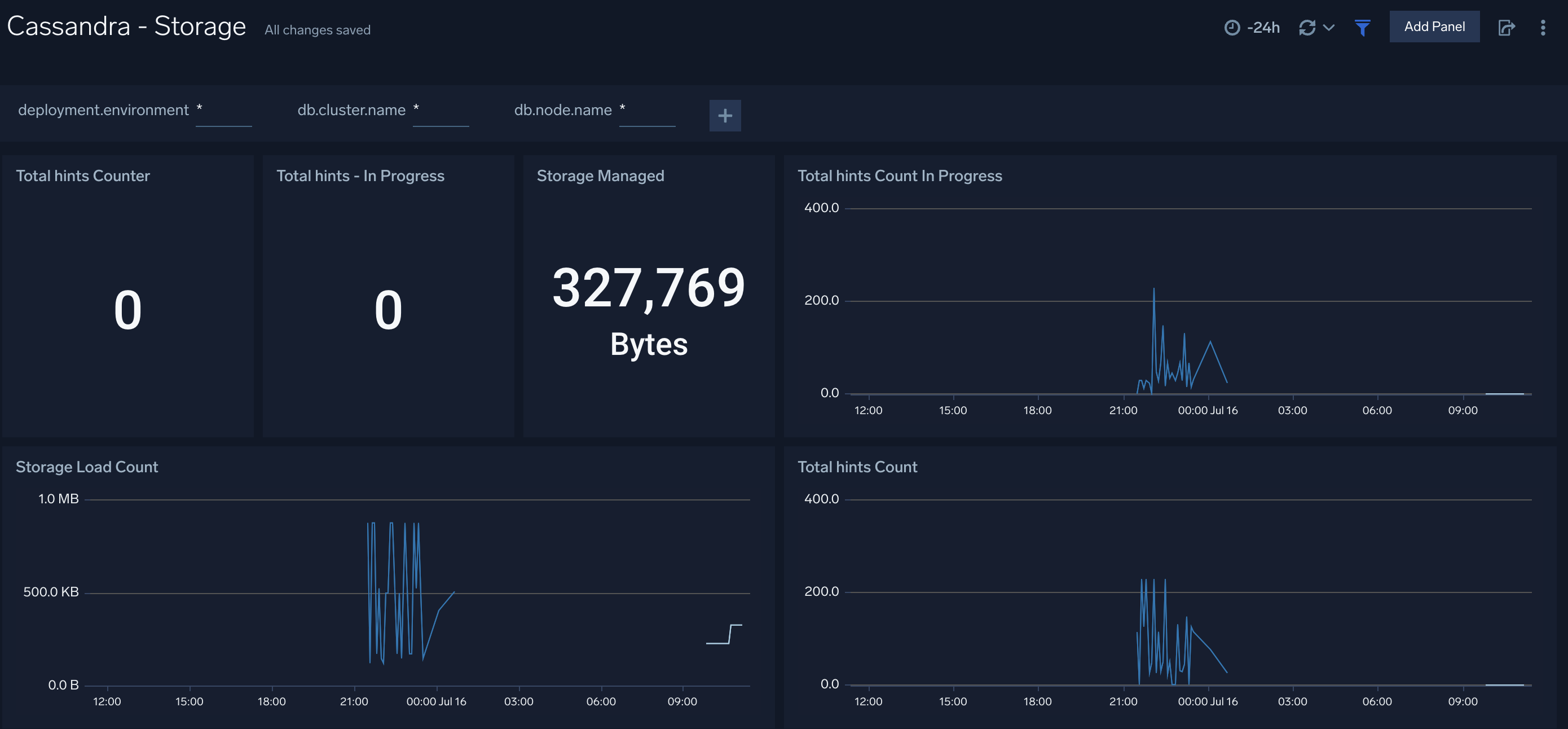 \ No newline at end of file
diff --git a/docs/integrations/databases/redis.md b/docs/integrations/databases/redis.md
index 3fa28f8c3d..997c42bc67 100644
--- a/docs/integrations/databases/redis.md
+++ b/docs/integrations/databases/redis.md
@@ -454,9 +454,9 @@ There are limits for how many alerts can be enabled - please see the [Alerts FAQ
* For alerts applicable only to a specific cluster, your custom filter would be: `db_cluster=redis-.prod.01`.
* For alerts applicable to all clusters that start with `redis-prod`, your custom filter would be: `db_cluster=redis-prod*`.
* For alerts applicable to a specific cluster within a production environment, your custom filter would be: `db_cluster=redis-1 and environment=prod`. This assumes you have set the optional environment tag while configuring collection.
-2. Go to Manage Data > Alerts > Monitors.
+2. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
3. Click **Add**.
-4. Click Import to import monitors from the JSON above.
+4. Click **Import** to import monitors from the JSON above.
:::note
Monitors are disabled by default. Once you have installed the alerts via this method, navigate to the Redis folder under **Monitors** to configure them. See [Monitor Settings](/docs/alerts/monitors/settings/#edit-disable-more-actions) to enable monitors. To send notifications to teams or connections, see the instructions detailed in Step 4 of [Create a Monitor](/docs/alerts/monitors/create-monitor).
@@ -539,8 +539,8 @@ This section demonstrates how to install the Redis ULM app.
Version selection is not available for all apps.
:::
3. To install the app, complete the following fields.
- 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
- 2. **Data Source.**
Choose **Enter a Custom Data Filter** and enter a custom Redis cluster filter. Examples:
+ 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
+ 2. **Data Source.** Choose **Enter a Custom Data Filter** and enter a custom Redis cluster filter. Examples:
* For all Redis clusters: `db_cluster=*`
* For a specific cluster: `db_cluster=redis.dev.01`
* Clusters within a specific environment: `db_cluster=redis-1 and environment=prod`. (This assumes you have set the optional environment tag while configuring collection).
diff --git a/docs/integrations/hosts-operating-systems/host-process-metrics.md b/docs/integrations/hosts-operating-systems/host-process-metrics.md
index c50b85687a..ec7e40245c 100644
--- a/docs/integrations/hosts-operating-systems/host-process-metrics.md
+++ b/docs/integrations/hosts-operating-systems/host-process-metrics.md
@@ -190,9 +190,9 @@ There are limits to how many alerts can be enabled - please see the [Alerts FAQ]
* For alerts applicable only to a specific cluster of hosts, your custom filter could be: `'_sourceCategory=yourclustername/metrics'`.
* For alerts applicable to all hosts that start with ec2hosts-prod, your custom filter could be: `'_sourceCategory=ec2hosts-prod*/metrics'`.
* For alerts applicable to a specific cluster within a production environment, your custom filter could be: `'_sourceCategory=prod/yourclustername/metrics'`
-2. Go to Manage Data > Alerts > Monitors.
-3. Click Add.
-4. Click Import to import monitors from the JSON above.
+2. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
+3. Click **Add**.
+4. Click **Import** to import monitors from the JSON above.
The monitors are disabled by default. Once you have installed the alerts using this method, navigate to the Host and Process Metrics folder under Monitors to configure them. See [this](/docs/alerts/monitors/settings) document to enable monitors, to configure each monitor, to send notifications to teams or connections, see the instructions detailed in [Create a Monitor](/docs/alerts/monitors/create-monitor).
diff --git a/docs/integrations/microsoft-azure/sql-server.md b/docs/integrations/microsoft-azure/sql-server.md
index 0c14a56f00..da6f134e8c 100644
--- a/docs/integrations/microsoft-azure/sql-server.md
+++ b/docs/integrations/microsoft-azure/sql-server.md
@@ -227,8 +227,8 @@ kubectl describe pod
\ No newline at end of file
diff --git a/docs/integrations/databases/redis.md b/docs/integrations/databases/redis.md
index 3fa28f8c3d..997c42bc67 100644
--- a/docs/integrations/databases/redis.md
+++ b/docs/integrations/databases/redis.md
@@ -454,9 +454,9 @@ There are limits for how many alerts can be enabled - please see the [Alerts FAQ
* For alerts applicable only to a specific cluster, your custom filter would be: `db_cluster=redis-.prod.01`.
* For alerts applicable to all clusters that start with `redis-prod`, your custom filter would be: `db_cluster=redis-prod*`.
* For alerts applicable to a specific cluster within a production environment, your custom filter would be: `db_cluster=redis-1 and environment=prod`. This assumes you have set the optional environment tag while configuring collection.
-2. Go to Manage Data > Alerts > Monitors.
+2. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
3. Click **Add**.
-4. Click Import to import monitors from the JSON above.
+4. Click **Import** to import monitors from the JSON above.
:::note
Monitors are disabled by default. Once you have installed the alerts via this method, navigate to the Redis folder under **Monitors** to configure them. See [Monitor Settings](/docs/alerts/monitors/settings/#edit-disable-more-actions) to enable monitors. To send notifications to teams or connections, see the instructions detailed in Step 4 of [Create a Monitor](/docs/alerts/monitors/create-monitor).
@@ -539,8 +539,8 @@ This section demonstrates how to install the Redis ULM app.
Version selection is not available for all apps.
:::
3. To install the app, complete the following fields.
- 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
- 2. **Data Source.**
Choose **Enter a Custom Data Filter** and enter a custom Redis cluster filter. Examples:
+ 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app.
+ 2. **Data Source.** Choose **Enter a Custom Data Filter** and enter a custom Redis cluster filter. Examples:
* For all Redis clusters: `db_cluster=*`
* For a specific cluster: `db_cluster=redis.dev.01`
* Clusters within a specific environment: `db_cluster=redis-1 and environment=prod`. (This assumes you have set the optional environment tag while configuring collection).
diff --git a/docs/integrations/hosts-operating-systems/host-process-metrics.md b/docs/integrations/hosts-operating-systems/host-process-metrics.md
index c50b85687a..ec7e40245c 100644
--- a/docs/integrations/hosts-operating-systems/host-process-metrics.md
+++ b/docs/integrations/hosts-operating-systems/host-process-metrics.md
@@ -190,9 +190,9 @@ There are limits to how many alerts can be enabled - please see the [Alerts FAQ]
* For alerts applicable only to a specific cluster of hosts, your custom filter could be: `'_sourceCategory=yourclustername/metrics'`.
* For alerts applicable to all hosts that start with ec2hosts-prod, your custom filter could be: `'_sourceCategory=ec2hosts-prod*/metrics'`.
* For alerts applicable to a specific cluster within a production environment, your custom filter could be: `'_sourceCategory=prod/yourclustername/metrics'`
-2. Go to Manage Data > Alerts > Monitors.
-3. Click Add.
-4. Click Import to import monitors from the JSON above.
+2. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**.
+3. Click **Add**.
+4. Click **Import** to import monitors from the JSON above.
The monitors are disabled by default. Once you have installed the alerts using this method, navigate to the Host and Process Metrics folder under Monitors to configure them. See [this](/docs/alerts/monitors/settings) document to enable monitors, to configure each monitor, to send notifications to teams or connections, see the instructions detailed in [Create a Monitor](/docs/alerts/monitors/create-monitor).
diff --git a/docs/integrations/microsoft-azure/sql-server.md b/docs/integrations/microsoft-azure/sql-server.md
index 0c14a56f00..da6f134e8c 100644
--- a/docs/integrations/microsoft-azure/sql-server.md
+++ b/docs/integrations/microsoft-azure/sql-server.md
@@ -227,8 +227,8 @@ kubectl describe pod
+
\ No newline at end of file
diff --git a/docs/integrations/product-list.md b/docs/integrations/product-list/product-list-a-l.md
similarity index 62%
rename from docs/integrations/product-list.md
rename to docs/integrations/product-list/product-list-a-l.md
index 42683cf31d..ec2799ee7b 100644
--- a/docs/integrations/product-list.md
+++ b/docs/integrations/product-list/product-list-a-l.md
@@ -1,21 +1,14 @@
---
-id: product-list
-title: Product List
-description: This article lists all the products that Sumo Logic integrates with.
+id: product-list-a-l
+title: Product List A-L
+description: This article lists all the products A-L that Sumo Logic integrates with.
---
import useBaseUrl from '@docusaurus/useBaseUrl';
-This article lists all the vendors and products that Sumo Logic integrates with, including the types of integrations we offer.
+Following are the vendors and products that Sumo Logic integrates with, listed A-L. We've divided the list into two articles to make the list easier to navigate. For the remainder, see [Product List M-Z](/docs/integrations/product-list/product-list-m-z/).
-Types of integrations:
-* **Apps**. Pre-built applications with dashboards that provide robust analytics about the product. To [install apps](/docs/get-started/apps-integrations/), select **App Catalog** from the main menu. See [Apps and Integrations](/docs/integrations/) for more information.
-* **Automation integrations**. Integrations for use in the Automation Service and Cloud SOAR. For more information, see [Integrations in App Central](/docs/platform-services/automation-service/app-central/integrations/).
-* **Cloud SIEM integrations**. Rules, mappers, parsers, and normalization schema in Cloud SIEM for integrating with external products. See [Cloud SIEM Content Catalog](/docs/cse/cloud-siem-content-catalog) for more information.
-* **Collectors**. Agents that collect data from the product. See [Send Data](/docs/send-data/) for documentation about collectors.
-* **Community apps**. Apps provided by internal and external users and our creator community. See [Sumo Logic Community Ecosystem Apps](/docs/integrations/community-ecosystem-apps/) for more information.
-* **Partner integrations**. Apps and integrations that are provided by members of our partner network. See [Partner Ecosystem Apps](/docs/integrations/partner-ecosystem-apps/) and [Partner Integrations for Sumo Logic](/docs/integrations/partner-integrations/) for more information.
-* **Webhooks**. Automated connections from the product to Sumo Logic. See [Webhooks](/docs/integrations/webhooks/buddy/) and [Webhook Connections](/docs/alerts/webhook-connections/) for available webhooks.
+For descriptions of the different types of integrations Sumo Logic offers, see [Product List](/docs/integrations/product-list/).
## A
@@ -341,218 +334,3 @@ Types of integrations:
|
+
+
+ })
+Product List A-L
+List of vendors and products A-L that Sumo Logic integrates with.
+
+
+
+ })
+Product List M-Z
+List of vendors and products M-Z that Sumo Logic integrates with.
+}) | [LogPoint](https://www.logpoint.com/en/) | Automation integration: [LogPoint](/docs/platform-services/automation-service/app-central/integrations/logpoint/) |
|
| [LogPoint](https://www.logpoint.com/en/) | Automation integration: [LogPoint](/docs/platform-services/automation-service/app-central/integrations/logpoint/) |
| }) | [LogRhythm](https://logrhythm.com/) | Automation integration: [LogRhythm](/docs/platform-services/automation-service/app-central/integrations/logrhythm/) |
|
| [LogRhythm](https://logrhythm.com/) | Automation integration: [LogRhythm](/docs/platform-services/automation-service/app-central/integrations/logrhythm/) |
| }) | [Lucidum](https://lucidum.io/) | Partner integration: [Lucidum](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Lucidum) |
-
-## M
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-|
| [Lucidum](https://lucidum.io/) | Partner integration: [Lucidum](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Lucidum) |
-
-## M
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-| Collectors:
- [Install a Collector on macOS](/docs/send-data/installed-collectors/macos/)
- [Install OpenTelemetry Collector on macOS](/docs/send-data/opentelemetry-collector/install-collector/macos/) | -|
}) | [Mailgun](https://www.mailgun.com/) | Webhook: [Mailgun](/docs/integrations/webhooks/mailgun/) |
-|
| [Mailgun](https://www.mailgun.com/) | Webhook: [Mailgun](/docs/integrations/webhooks/mailgun/) |
-| }) | [Malwarebytes](https://www.malwarebytes.com/) | Automation integration: [Malwarebytes Nebula](/docs/platform-services/automation-service/app-central/integrations/malwarebytes-nebula/)
| [Malwarebytes](https://www.malwarebytes.com/) | Automation integration: [Malwarebytes Nebula](/docs/platform-services/automation-service/app-central/integrations/malwarebytes-nebula/) Cloud SIEM integration: [Malwarebytes](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/2e08dea2-4048-4f0f-9af8-aa85881151ad.md) | -|
}) | [ManageEngine](https://www.manageengine.com/) | Automation integration: [ManageEngine Desktop Central](/docs/platform-services/automation-service/app-central/integrations/manage-engine-desktop-central/)
| [ManageEngine](https://www.manageengine.com/) | Automation integration: [ManageEngine Desktop Central](/docs/platform-services/automation-service/app-central/integrations/manage-engine-desktop-central/) Cloud SIEM integration: [ManageEngine](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/e6417fdd-1aa1-436e-a659-38d71e51599f.md) | -|
}) | [MariaDB](https://mariadb.org/) | Apps:
| [MariaDB](https://mariadb.org/) | Apps: - [MariaDB](/docs/integrations/databases/mariadb/)
- [MariaDB - OpenTelemetry](/docs/integrations/databases/opentelemetry/mariadb-opentelemetry/) | -|
}) | [Material Security](https://material.security/) | Automation integration: [Material Security](/docs/platform-services/automation-service/app-central/integrations/material-security/) |
-|
| [Material Security](https://material.security/) | Automation integration: [Material Security](/docs/platform-services/automation-service/app-central/integrations/material-security/) |
-| }) | [Mattermost](https://mattermost.com/) | Automation integration: [Mattermost](/docs/platform-services/automation-service/app-central/integrations/mattermost/) |
-|
| [Mattermost](https://mattermost.com/) | Automation integration: [Mattermost](/docs/platform-services/automation-service/app-central/integrations/mattermost/) |
-| }) | [MaxMind](https://www.maxmind.com/en/home) | Automation integration: [MaxMind V2](/docs/platform-services/automation-service/app-central/integrations/maxmind-v2/) |
-|
| [MaxMind](https://www.maxmind.com/en/home) | Automation integration: [MaxMind V2](/docs/platform-services/automation-service/app-central/integrations/maxmind-v2/) |
-| }) | [McAfee](https://www.mcafee.com/) | Automation integrations:
| [McAfee](https://www.mcafee.com/) | Automation integrations: - [McAfee ATD](/docs/platform-services/automation-service/app-central/integrations/mcafee-atd/)
- [McAfee ESM](/docs/platform-services/automation-service/app-central/integrations/mcafee-esm/)
- [McAfee MVISION](/docs/platform-services/automation-service/app-central/integrations/mcafee-mvision/)
- [McAfee Network Security Platform Manager (NSM)](/docs/platform-services/automation-service/app-central/integrations/mcafee-network-security-platform-manager-nsm/)
- [McAfee Web Gateway](/docs/platform-services/automation-service/app-central/integrations/mcafee-web-gateway/)
Cloud SIEM integration: [McAfee](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/20dec895-f649-4959-9717-104fb68bb5b4.md) | -|
}) | [Memcached](https://memcached.org/) | Apps:
| [Memcached](https://memcached.org/) | Apps: - [Memcached](/docs/integrations/databases/memcached/)
- [Memcached - OpenTelemetry](/docs/integrations/databases/opentelemetry/memcached-opentelemetry/) | -|
}) | [Microsoft](https://www.microsoft.com/) | Apps:
| [Microsoft](https://www.microsoft.com/) | Apps: - [Azure Active Directory](/docs/integrations/microsoft-azure/active-directory-azure/)
- [Microsoft Dynamics 365](/docs/integrations/microsoft-azure/microsoft-dynamics365-customer-insights/)
- [Microsoft Exchange Trace Logs](/docs/integrations/saas-cloud/microsoft-exchange-trace-logs/)
- [Microsoft Graph Azure AD Reporting](/docs/integrations/saas-cloud/microsoft-graph-azure-ad-reporting/)
- [Microsoft Graph Identity Protection](/docs/integrations/microsoft-azure/microsoft-graph-identity-protection/)
- [Microsoft Graph Security V1](/docs/integrations/saas-cloud/microsoft-graph-security-v1/)
- [Microsoft Graph Security V2](/docs/integrations/saas-cloud/microsoft-graph-security-v2/)
- [Microsoft Office 365](/docs/integrations/microsoft-azure/office-365/)
- [Microsoft SQL Server](/docs/integrations/microsoft-azure/sql-server/)
- [Microsoft SQL Server - OpenTelemetry](/docs/integrations/microsoft-azure/opentelemetry/sql-server-opentelemetry)
- [Microsoft SQL Server for Linux - OpenTelemetry](/docs/integrations/microsoft-azure/opentelemetry/sql-server-linux-opentelemetry)
- [Microsoft Teams](/docs/integrations/microsoft-azure/teams/)
Automation integrations:
- [Microsoft 365 Defender](/docs/platform-services/automation-service/app-central/integrations/microsoft-365-defender/)
- [Microsoft Azure Log Analytics](/docs/platform-services/automation-service/app-central/integrations/microsoft-azure-log-analytics/)
- [Microsoft Azure Security Center](/docs/platform-services/automation-service/app-central/integrations/microsoft-azure-security-center/)
- [Microsoft Defender ATP](/docs/platform-services/automation-service/app-central/integrations/microsoft-defender-atp/)
- [Microsoft EWS](/docs/platform-services/automation-service/app-central/integrations/microsoft-ews/)
- [Microsoft EWS Daemon](/docs/platform-services/automation-service/app-central/integrations/microsoft-ews-daemon/)
- [Microsoft EWS Extension](/docs/platform-services/automation-service/app-central/integrations/microsoft-ews-extension/)
- [Microsoft Graph Security](/docs/platform-services/automation-service/app-central/integrations/microsoft-graph-security/)
- [Microsoft OneDrive](/docs/platform-services/automation-service/app-central/integrations/microsoft-onedrive/)
- [Microsoft Sharepoint](/docs/platform-services/automation-service/app-central/integrations/microsoft-sharepoint/)
- [Microsoft Sentinel](/docs/platform-services/automation-service/app-central/integrations/microsoft-sentinel/)
- [MSSQL](/docs/platform-services/automation-service/app-central/integrations/mssql/)
- [Microsoft Teams](/docs/platform-services/automation-service/app-central/integrations/microsoft-teams/)
Cloud SIEM integration: [Microsoft](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/2b002817-fd14-49b3-a3fe-c9761275b931.md)
Collectors:
- [Microsoft 365 Audit (Office 365 Audit) - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/microsoft-audit-office/)
- [Microsoft Exchange Trace Logs](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-exchange-trace-logs/)
- [Microsoft Office 365 Audit Source](/docs/send-data/hosted-collectors/microsoft-source/ms-office-audit-source/)
- [Microsoft Graph Azure AD Reporting Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-azure-ad-reporting-source/)
- [Microsoft Graph Identity Protection Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-identity-protection-source/)
- [Microsoft Graph Security API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-security-api-source/)
Community app: [Sumo Logic Microsoft Defender for EndPoint](https://github.com/SumoLogic/sumologic-content/tree/master/Microsoft/Defender_4_EndPoint)
Webhook: [Webhook Connection for Microsoft Teams](/docs/alerts/webhook-connections/microsoft-teams/) | -|
}) | [Mimecast](https://www.mimecast.com/) | App: [Mimecast](/docs/integrations/saas-cloud/mimecast/)
| [Mimecast](https://www.mimecast.com/) | App: [Mimecast](/docs/integrations/saas-cloud/mimecast/) Automation integration: [Mimecast](/docs/platform-services/automation-service/app-central/integrations/mimecast/)
Cloud SIEM integration: [Mimecast](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/7BC43DFE-C5DD-4766-88E7-C163D82BBBF8.md)
Collector: [Mimecast Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/mimecast-source/)
Partner integration: [Mimecast app for Sumo Logic](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Mimecast) | -|
}) | [Miro](https://miro.com/) | App: [Miro](/docs/integrations/saas-cloud/miro/)
| [Miro](https://miro.com/) | App: [Miro](/docs/integrations/saas-cloud/miro/) Cloud SIEM integration: [Miro](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9f149da1-2831-465f-8bb1-a5950ccaec0c.md)
Collector: [Miro Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/miro-source/) | -|
}) | [MISP](https://www.misp-project.org/) | Automation integration: [MISP](/docs/platform-services/automation-service/app-central/integrations/misp/)
| [MISP](https://www.misp-project.org/) | Automation integration: [MISP](/docs/platform-services/automation-service/app-central/integrations/misp/)Community app: [Sumo Logic for MISP](https://github.com/SumoLogic/sumologic-content/tree/master/MISP) | -|
}) | [MITRE ATT&CK](https://attack.mitre.org/) | Automation integration: [Mitre Matrix](/docs/platform-services/automation-service/app-central/integrations/mitre-matrix/) |
-|
| [MITRE ATT&CK](https://attack.mitre.org/) | Automation integration: [Mitre Matrix](/docs/platform-services/automation-service/app-central/integrations/mitre-matrix/) |
-| }) | [MongoDB](https://www.mongodb.com/) | Apps:
| [MongoDB](https://www.mongodb.com/) | Apps: - [MongoDB](/docs/integrations/databases/mongodb/)
- [MongoDB - OpenTelementry](/docs/integrations/databases/opentelemetry/mongodb-opentelemetry/) | -|
}) | [MongoDB Atlas](https://www.mongodb.com/atlas) | App: [MongoDB Atlas](/docs/integrations/databases/mongodb-atlas/) |
-|
| [MongoDB Atlas](https://www.mongodb.com/atlas) | App: [MongoDB Atlas](/docs/integrations/databases/mongodb-atlas/) |
-| }) | [mParticle](https://www.mparticle.com/) | Webhook: [mParticle](/docs/integrations/webhooks/mparticle/) |
-|
| [mParticle](https://www.mparticle.com/) | Webhook: [mParticle](/docs/integrations/webhooks/mparticle/) |
-| }) | [MxToolbox](https://mxtoolbox.com/) | Automation integration: [MxToolbox](/docs/platform-services/automation-service/app-central/integrations/mxtoolbox/) |
-|
| [MxToolbox](https://mxtoolbox.com/) | Automation integration: [MxToolbox](/docs/platform-services/automation-service/app-central/integrations/mxtoolbox/) |
-| }) | [MySQL](https://www.mysql.com/) | Apps:
| [MySQL](https://www.mysql.com/) | Apps: - [MySQL](/docs/integrations/databases/mysql/)
- [MySQL - OpenTelemetry](/docs/integrations/databases/opentelemetry/mysql-opentelemetry/) | - -## N - -| Logo | Vendors and Products | Integrations | -| :-- | :-- | :-- | -|
}) | [Netlify](https://www.netlify.com/) | Webhook: [Netlify](/docs/integrations/webhooks/netlify/) |
-|
| [Netlify](https://www.netlify.com/) | Webhook: [Netlify](/docs/integrations/webhooks/netlify/) |
-| }) | [NETSCOUT](https://www.netscout.com/) | Automation integration: [Arbor (NETSCOUT)](/docs/platform-services/automation-service/app-central/integrations/arbor/) |
-|
| [NETSCOUT](https://www.netscout.com/) | Automation integration: [Arbor (NETSCOUT)](/docs/platform-services/automation-service/app-central/integrations/arbor/) |
-| }) | [Netskope](https://www.netskope.com/) | Apps:
| [Netskope](https://www.netskope.com/) | Apps: - [Netskope](/docs/integrations/security-threat-detection/netskope/)
- [Netskope Legacy](/docs/integrations/security-threat-detection/netskope-legacy-collection/)
Automation integrations:
- [Netskope](/docs/platform-services/automation-service/app-central/integrations/netskope/)
- [Netskope V2](/docs/platform-services/automation-service/app-central/integrations/netskope-v2/)
Cloud SIEM integration: [Netskope](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/E9BF4F45-AB91-40F6-9EA0-21B48D69FF1F.md)
Collectors:
- [Netskope Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/netskope-source/)
- [Netskope WebTx Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/netskope-webtx-source/) | -|
}) | [Neustar](https://www.home.neustar/) | Automation integration: [Neustar IP GeoPoint](/docs/platform-services/automation-service/app-central/integrations/neustar-ip-geopoint/) |
-|
| [Neustar](https://www.home.neustar/) | Automation integration: [Neustar IP GeoPoint](/docs/platform-services/automation-service/app-central/integrations/neustar-ip-geopoint/) |
-| }) | [New Relic](https://newrelic.com/) | Webhook: [Webhook Connection for New Relic](/docs/alerts/webhook-connections/new-relic/) |
-|
| [New Relic](https://newrelic.com/) | Webhook: [Webhook Connection for New Relic](/docs/alerts/webhook-connections/new-relic/) |
-| }) | [Nmap](https://nmap.org/) | Automation integration: [Nmap](/docs/platform-services/automation-service/app-central/integrations/nmap/) |
-|
| [Nmap](https://nmap.org/) | Automation integration: [Nmap](/docs/platform-services/automation-service/app-central/integrations/nmap/) |
-| }) | [Nobl9](https://www.nobl9.com/) | Webhook: [Nobl9](/docs/integrations/webhooks/nobl9/) |
-|
| [Nobl9](https://www.nobl9.com/) | Webhook: [Nobl9](/docs/integrations/webhooks/nobl9/) |
-| }) | [Nozomi Networks](https://www.nozominetworks.com/) | Automation integration: [Nozomi Networks](/docs/platform-services/automation-service/app-central/integrations/nozomi-networks/) |
-|
| [Nozomi Networks](https://www.nozominetworks.com/) | Automation integration: [Nozomi Networks](/docs/platform-services/automation-service/app-central/integrations/nozomi-networks/) |
-| }) | [Nucleon](https://nucleoncyber.com/) | Automation integration: [Nucleon Cyber](/docs/platform-services/automation-service/app-central/integrations/nucleon-cyber/)
| [Nucleon](https://nucleoncyber.com/) | Automation integration: [Nucleon Cyber](/docs/platform-services/automation-service/app-central/integrations/nucleon-cyber/) Partner integration: [Nucleon](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Nucleon) | -|
}) | [NXLog](https://nxlog.co/) | Partner integration: [NXLog](https://nxlog.co/technology-ecosystem) |
-
-## O
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-|
| [NXLog](https://nxlog.co/) | Partner integration: [NXLog](https://nxlog.co/technology-ecosystem) |
-
-## O
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-| }) | [Observable Networks](https://www.cisco.com/c/en/us/services/acquisitions/observable-networks.html) | App: [Observable Networks](/docs/integrations/security-threat-detection/observable-networks/) |
-|
| [Observable Networks](https://www.cisco.com/c/en/us/services/acquisitions/observable-networks.html) | App: [Observable Networks](/docs/integrations/security-threat-detection/observable-networks/) |
-| }) | [OISF](https://oisf.net/) | Cloud SIEM integration: [OISF](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9c138edd-dc14-43a6-b751-52e41a8bd105.md) |
-|
| [OISF](https://oisf.net/) | Cloud SIEM integration: [OISF](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9c138edd-dc14-43a6-b751-52e41a8bd105.md) |
-| }) | [Okta](https://www.okta.com/) | App: [Okta](/docs/integrations/saml/okta/)
| [Okta](https://www.okta.com/) | App: [Okta](/docs/integrations/saml/okta/) Automation integration: [Okta](/docs/platform-services/automation-service/app-central/integrations/okta/)
Cloud SIEM integration: [Okta](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/d8d14556-180c-4463-90da-d8b8600f7362.md)
Collectors:
- [Okta Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/okta-source/)
- [Okta - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/okta/) | -|
}) | [OneLogin](https://www.onelogin.com/) | App: [OneLogin](/docs/integrations/saml/onelogin/)
| [OneLogin](https://www.onelogin.com/) | App: [OneLogin](/docs/integrations/saml/onelogin/) Automation integration: [OneLogin](/docs/platform-services/automation-service/app-central/integrations/onelogin/)
Cloud SIEM integration: [OneLogin](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/e34a3430-613f-47c0-9ddd-a320bc3e5c4d.md)
Collector: [OneLogin - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/onelogin/) | -|
}) | [1Password](https://1password.com/) | App: [1Password](/docs/integrations/1password/)
| [1Password](https://1password.com/) | App: [1Password](/docs/integrations/1password/) Cloud SIEM integration: [1Password](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/d0455ea1-e901-4999-b047-0533d16adfdc.md)
Collector: [1Password Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/1password-source/) | -|
}) | [OneTrust](https://www.onetrust.com/) | Automation integration: [OneTrust](/docs/platform-services/automation-service/app-central/integrations/onetrust/) |
-|
| [OneTrust](https://www.onetrust.com/) | Automation integration: [OneTrust](/docs/platform-services/automation-service/app-central/integrations/onetrust/) |
-| }) | [OpenAI](https://openai.com/) | Automation integration: [OpenAI ChatGPT](/docs/platform-services/automation-service/app-central/integrations/openai-chatgpt/) |
-|
| [OpenAI](https://openai.com/) | Automation integration: [OpenAI ChatGPT](/docs/platform-services/automation-service/app-central/integrations/openai-chatgpt/) |
-| }) | [OpenLDAP](https://www.openldap.org/) | Automation integration: [OpenLDAP](/docs/platform-services/automation-service/app-central/integrations/openldap/) |
-|
| [OpenLDAP](https://www.openldap.org/) | Automation integration: [OpenLDAP](/docs/platform-services/automation-service/app-central/integrations/openldap/) |
-| }) | [OpenSSH](https://www.openssh.com/) | Cloud SIEM integration: [OpenSSH](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/d0bf0b9f-162e-4d1e-9b89-38e8d526a434.md) |
-|
| [OpenSSH](https://www.openssh.com/) | Cloud SIEM integration: [OpenSSH](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/d0bf0b9f-162e-4d1e-9b89-38e8d526a434.md) |
-| }) | [OpenText](https://www.opentext.com/) | Automation integrations:
| [OpenText](https://www.opentext.com/) | Automation integrations: - [Arcsight ESM](/docs/platform-services/automation-service/app-central/integrations/arcsight-esm/)
- [Arcsight Logger](/docs/platform-services/automation-service/app-central/integrations/arcsight-logger/)
- [HP Universal CMDB](/docs/platform-services/automation-service/app-central/integrations/hp-universal-cmdb/)
- [Micro Focus Service Management](/docs/platform-services/automation-service/app-central/integrations/micro-focus-service-management/)
- [OpenText EnCase Endpoint Security](/docs/platform-services/automation-service/app-central/integrations/opentext-encase-endpoint-security/)
Cloud SIEM integration: [Micro Focus](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/23850303-a1da-4c95-83f1-bd9d3b5104b8.md) | -|
}) | [OpenVPN](https://openvpn.net/) | Cloud SIEM integration: [OpenVPN](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/8e5a85b3-a95e-47d9-adcf-bb543e6580c0.md) |
-|
| [OpenVPN](https://openvpn.net/) | Cloud SIEM integration: [OpenVPN](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/8e5a85b3-a95e-47d9-adcf-bb543e6580c0.md) |
-| }) | [Opsgenie](https://www.atlassian.com/software/opsgenie) | App: [Opsgenie](/docs/integrations/saas-cloud/opsgenie/)
| [Opsgenie](https://www.atlassian.com/software/opsgenie) | App: [Opsgenie](/docs/integrations/saas-cloud/opsgenie/)Automation integration: [Atlassian Opsgenie](/docs/platform-services/automation-service/app-central/integrations/atlassian-opsgenie/)
Webhooks:
- [Webhook Connection for Opsgenie](/docs/alerts/webhook-connections/opsgenie/)
- [Webhook Connection for Opsgenie (Legacy)](/docs/alerts/webhook-connections/opsgenie-legacy/) | -|
}) | [OpsRamp](https://www.opsramp.com/) | Partner integration: [OpsRamp](https://docs.opsramp.com/integrations/a2r/3rd-party/sumologic/) |
-|
| [OpsRamp](https://www.opsramp.com/) | Partner integration: [OpsRamp](https://docs.opsramp.com/integrations/a2r/3rd-party/sumologic/) |
-| }) | [Opswat](https://www.opswat.com/) | Automation integration: [Opswat Metadefender](/docs/platform-services/automation-service/app-central/integrations/opswat-metadefender/) |
-|
| [Opswat](https://www.opswat.com/) | Automation integration: [Opswat Metadefender](/docs/platform-services/automation-service/app-central/integrations/opswat-metadefender/) |
-| }) | [Oracle Database](https://www.oracle.com/database/) | Apps:
| [Oracle Database](https://www.oracle.com/database/) | Apps: - [Oracle](/docs/integrations/databases/oracle/)
- [Oracle - OpenTelemetry](/docs/integrations/databases/opentelemetry/oracle-opentelemetry/)
Collector: [Collect Logs from Oracle Cloud Infrastructure](/docs/send-data/collect-from-other-data-sources/collect-logs-oracle-cloud-infrastructure/) | -|
}) | [Orca Security](https://orca.security/) | Cloud SIEM integration: [Orca Security](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/ab5b4909-20f7-4cf7-b8de-24f4a5b2ba57.md) |
-|
| [Orca Security](https://orca.security/) | Cloud SIEM integration: [Orca Security](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/ab5b4909-20f7-4cf7-b8de-24f4a5b2ba57.md) |
-| }) | [osquery](https://osquery.io/) | Cloud SIEM integration: [Osquery](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/eca511e4-0daa-41f7-919e-ec4d0ac1558f.md)
| [osquery](https://osquery.io/) | Cloud SIEM integration: [Osquery](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/eca511e4-0daa-41f7-919e-ec4d0ac1558f.md) Collector: [Osquery - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/osquery/) | -|
}) | [Ossec](https://www.ossec.net/) | Cloud SIEM integration: [Ossec](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/1eceb40f-85d7-45ea-b341-864a38ea0775.md) |
-
-## P
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-|
| [Ossec](https://www.ossec.net/) | Cloud SIEM integration: [Ossec](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/1eceb40f-85d7-45ea-b341-864a38ea0775.md) |
-
-## P
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-| }) | [PagerDuty](https://www.pagerduty.com/) | Apps:
| [PagerDuty](https://www.pagerduty.com/) | Apps: - [PagerDuty V2](/docs/integrations/saas-cloud/pagerduty-v2/)
- [PagerDuty V3](/docs/integrations/saas-cloud/pagerduty-v3/)
Automation integration: [PagerDuty](/docs/platform-services/automation-service/app-central/integrations/pagerduty/)
Webhook: [Webhook Connection for PagerDuty](/docs/alerts/webhook-connections/pagerduty/) | -|
}) | [Palo Alto Networks](https://www.paloaltonetworks.com/) | Apps:
| [Palo Alto Networks](https://www.paloaltonetworks.com/) | Apps: - [Evident.io ESP](/docs/integrations/security-threat-detection/evident-security-platform/)
- [Palo Alto Firewall 9](/docs/integrations/cloud-security-monitoring-analytics/palo-alto-firewall-9/)
- [Palo Alto Firewall 10](/docs/integrations/cloud-security-monitoring-analytics/palo-alto-firewall-10/)
- [Palo Alto Networks 9](/docs/integrations/security-threat-detection/palo-alto-networks-9/)
- [PCI Compliance for Palo Alto Networks 9](/docs/integrations/pci-compliance/palo-alto-networks-9/)
- [PCI Compliance for Palo Alto Networks 10](/docs/integrations/pci-compliance/palo-alto-networks-10/)
- [Palo Alto Cortex XDR](/docs/integrations/saas-cloud/palo-alto-cortex-xdr/)
- [Twistlock](/docs/integrations/security-threat-detection/twistlock/)
Automation integrations:
- [Cortex XDR](/docs/platform-services/automation-service/app-central/integrations/cortex-xdr/)
- [Palo Alto AutoFocus](/docs/platform-services/automation-service/app-central/integrations/palo-alto-autofocus/)
- [Palo Alto Networks NGFW](/docs/platform-services/automation-service/app-central/integrations/palo-alto-networks-ngfw/)
- [Palo Alto Networks Panorama V2](/docs/platform-services/automation-service/app-central/integrations/palo-alto-networks-panorama-v2/)
- [Prisma Cloud](/docs/platform-services/automation-service/app-central/integrations/prisma-cloud/)
Cloud SIEM integrations:
- [Demisto](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/C279B799-AD59-4B49-9582-5F9FD106079F.md)
- [Palo Alto Networks](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/938210de-ab6c-46fb-89d7-8530682581c6.md)
- [Redlock](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/94c035a7-d8ba-4c66-bda6-2fe19db458d6.md)
- [Twistlock](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/97C36046-B516-41F8-9751-4C788AA33785.md)
Collectors:
- [Collect Logs from Palo Alto Networks Cortex Data Lake](/docs/send-data/collect-from-other-data-sources/collect-logs-palo-alto-networks-cortex/)
- [Palo Alto Cortex XDR Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/palo-alto-cortex-xdr-source/)
- [Palo Alto Firewall - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/palo-alto-firewall/)
Community app: [Sumo Logic for Palo Alto Cortex XDR](https://github.com/SumoLogic/sumologic-content/tree/master/Palo_Alto_Networks/Cortex_XDR)
Partner integration: [Cortex XSOAR](https://xsoar.pan.dev/docs/reference/integrations/sumo-logic) | -|
}) | [PaperTrail](https://www.papertrail.com/) | Webhook: [PaperTrail](/docs/integrations/webhooks/papertrail/) |
-|
| [PaperTrail](https://www.papertrail.com/) | Webhook: [PaperTrail](/docs/integrations/webhooks/papertrail/) |
-| }) | [Phantombuster](https://phantombuster.com/) | Automation integration: [Phantombuster](/docs/platform-services/automation-service/app-central/integrations/phantombuster/) |
-|
| [Phantombuster](https://phantombuster.com/) | Automation integration: [Phantombuster](/docs/platform-services/automation-service/app-central/integrations/phantombuster/) |
-| }) | [PhishTank](https://phishtank.org/) | Automation integration: [PhishTank](/docs/platform-services/automation-service/app-central/integrations/phishtank/) |
-|
| [PhishTank](https://phishtank.org/) | Automation integration: [PhishTank](/docs/platform-services/automation-service/app-central/integrations/phishtank/) |
-| }) | [PostgreSQL](https://www.postgresql.org/) | Apps:
| [PostgreSQL](https://www.postgresql.org/) | Apps: - [PostgreSQL](/docs/integrations/databases/postgresql/)
- [PostgreSQL - OpenTelemetry](/docs/integrations/databases/opentelemetry/postgresql-opentelemetry/) | -|
}) | [Postman](https://www.postman.com/) | Webhook: [Postman](/docs/integrations/webhooks/postman/) |
-|
| [Postman](https://www.postman.com/) | Webhook: [Postman](/docs/integrations/webhooks/postman/) |
-| }) | [Pritunl](https://pritunl.com/) | Cloud SIEM integration: [Pritunl](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/598b6820-feff-4169-89da-77211493a91d.md) |
-|
| [Pritunl](https://pritunl.com/) | Cloud SIEM integration: [Pritunl](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/598b6820-feff-4169-89da-77211493a91d.md) |
-| }) | [Prometheus](https://prometheus.io/) | Collector: [Collect Prometheus Metrics](/docs/send-data/collect-from-other-data-sources/collect-prometheus-metrics/) |
-|
| [Prometheus](https://prometheus.io/) | Collector: [Collect Prometheus Metrics](/docs/send-data/collect-from-other-data-sources/collect-prometheus-metrics/) |
-| }) | [Proofpoint](https://www.proofpoint.com/us) | Apps:
| [Proofpoint](https://www.proofpoint.com/us) | Apps: - [Proofpoint on Demand](/docs/integrations/saas-cloud/proofpoint-on-demand/)
- [Proofpoint TAP](/docs/integrations/saas-cloud/proofpoint-tap/)
Automation integration: [Proofpoint TAP](/docs/platform-services/automation-service/app-central/integrations/proofpoint-tap/)
Cloud SIEM integrations:
- [ObserveIT](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/BBBEB05C-6CFE-4BF8-8AA6-73CD73DF2464.md)
- [Proofpoint](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/e0bbbae5-9a03-48f4-b138-9c3b49522f1a.md)
Collectors:
- [Proofpoint On Demand Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/proofpoint-on-demand-source/)
- [Proofpoint TAP Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/proofpoint-tap-source/)
Community app: [Sumo Logic for Proofpoint TAP](https://github.com/SumoLogic/sumologic-content/tree/master/Proofpoint/Proofpoint_TAP) | -|
}) | [ProtectOnce](https://protectonce.com/) | Automation integration: [ProtectOnce](/docs/platform-services/automation-service/app-central/integrations/protectonce/) |
-|
| [ProtectOnce](https://protectonce.com/) | Automation integration: [ProtectOnce](/docs/platform-services/automation-service/app-central/integrations/protectonce/) |
-| }) | [Pulsedive](https://pulsedive.com/) | Automation integration: [Pulsedive](/docs/platform-services/automation-service/app-central/integrations/pulsedive/) |
-|
| [Pulsedive](https://pulsedive.com/) | Automation integration: [Pulsedive](/docs/platform-services/automation-service/app-central/integrations/pulsedive/) |
-| }) | [Puppet](https://www.puppet.com/) | Apps:
| [Puppet](https://www.puppet.com/) | Apps: - [Puppet](/docs/integrations/app-development/puppet/)
- [Puppet - OpenTelemetry](/docs/integrations/app-development/opentelemetry/puppet-opentelemetry/)
Collector: [Install OpenTelemetry Collector on Puppet](/docs/send-data/opentelemetry-collector/install-collector/puppet/) | -|
}) | [Pusher](https://pusher.com/) | Webhook: [Pusher](/docs/integrations/webhooks/pusher/) |
-
-## Q
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-|
| [Pusher](https://pusher.com/) | Webhook: [Pusher](/docs/integrations/webhooks/pusher/) |
-
-## Q
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-| Automation integrations:
- [Qualys](/docs/platform-services/automation-service/app-central/integrations/qualys/)
- [Qualys EDR](/docs/platform-services/automation-service/app-central/integrations/qualys-edr/)
- [Qualys WAS](/docs/platform-services/automation-service/app-central/integrations/qualys-was/)
Cloud SIEM integration: [Qualys](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/fb83d074-c6cf-4fc7-9020-5d3e364acd17.md)
Collector: [Qualys VMDR Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/qualys-vmdr-source/)
Community app: [Sumo Logic for Qualys VMDR and Inventory](https://github.com/SumoLogic/sumologic-content/tree/master/Qualys) | - -## R - -| Logo | Vendors and Products | Integrations | -| :-- | :-- | :-- | -|
}) | [RabbitMQ](https://www.rabbitmq.com/) | Apps:
| [RabbitMQ](https://www.rabbitmq.com/) | Apps: - [RabbitMQ](/docs/integrations/containers-orchestration/rabbitmq/)
- [RabbitMQ - OpenTelemetry](/docs/integrations/containers-orchestration/opentelemetry/rabbitmq-opentelemetry/) | -|
}) | [Rapid7](https://www.rapid7.com/) | App: [Rapid7](/docs/integrations/saas-cloud/rapid7/)
| [Rapid7](https://www.rapid7.com/) | App: [Rapid7](/docs/integrations/saas-cloud/rapid7/) Automation integrations:
- [Rapid 7 InsightVM](/docs/platform-services/automation-service/app-central/integrations/rapid-7-insightvm/)
- [Rapid7 Nexpose](/docs/platform-services/automation-service/app-central/integrations/rapid7-nexpose/) | -|
}) | [RapidAPI](https://rapidapi.com/) | Automation integration: [RapidAPI](/docs/platform-services/automation-service/app-central/integrations/rapidapi/) |
-|
| [RapidAPI](https://rapidapi.com/) | Automation integration: [RapidAPI](/docs/platform-services/automation-service/app-central/integrations/rapidapi/) |
-| }) | [Recorded Future](https://www.recordedfuture.com/) | Automation integration: [Recorded Future](/docs/platform-services/automation-service/app-central/integrations/recorded-future/) |
-|
| [Recorded Future](https://www.recordedfuture.com/) | Automation integration: [Recorded Future](/docs/platform-services/automation-service/app-central/integrations/recorded-future/) |
-| }) | [Red Hat OpenShift](https://www.redhat.com/en/technologies/cloud-computing/openshift) | Partner integration: [Red Hat OpenShift](https://docs.openshift.com/acs/3.74/integration/integrate-with-sumologic.html)
| [Red Hat OpenShift](https://www.redhat.com/en/technologies/cloud-computing/openshift) | Partner integration: [Red Hat OpenShift](https://docs.openshift.com/acs/3.74/integration/integrate-with-sumologic.html) Collector: [Rapid7 Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/rapid7-source/) | -|
}) | [Redis](https://redis.io/) | Apps:
| [Redis](https://redis.io/) | Apps: - [Redis](/docs/integrations/databases/redis/)
- [Redis - OpenTelemetry](/docs/integrations/databases/opentelemetry/redis-opentelemetry/) | -|
}) | [RiskIQ](https://community.riskiq.com/) | Automation integration: [Passive Total](/docs/platform-services/automation-service/app-central/integrations/passive-total/) |
-|
| [RiskIQ](https://community.riskiq.com/) | Automation integration: [Passive Total](/docs/platform-services/automation-service/app-central/integrations/passive-total/) |
-| }) | [Rollbar](https://rollbar.com/) | Webhook: [Rollbar](/docs/integrations/webhooks/rollbar/) |
-|
| [Rollbar](https://rollbar.com/) | Webhook: [Rollbar](/docs/integrations/webhooks/rollbar/) |
-| }) | [RSA](https://www.rsa.com/) | Automation integrations:
| [RSA](https://www.rsa.com/) | Automation integrations: - [RSA NetWitness Logs](/docs/platform-services/automation-service/app-central/integrations/rsa-netwitness-logs/)
- [RSA NetWitness](/docs/platform-services/automation-service/app-central/integrations/rsa-netwitness/)
Cloud SIEM integration: [RSA](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/8c02f96f-60b2-48d6-bfe6-1605adaf4d51.md) | -|
}) | [rsyslog](https://www.rsyslog.com/) | Collector: [rsyslog](/docs/send-data/hosted-collectors/cloud-syslog-source/rsyslog/) |
-|
| [rsyslog](https://www.rsyslog.com/) | Collector: [rsyslog](/docs/send-data/hosted-collectors/cloud-syslog-source/rsyslog/) |
-| }) | [Ruby on Rails](https://rubyonrails.org/) | Collector: [Collect Ruby on Rails Logs](/docs/send-data/collect-from-other-data-sources/collect-ruby-on-rails-logs/) |
-
-
-## S
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-|
| [Ruby on Rails](https://rubyonrails.org/) | Collector: [Collect Ruby on Rails Logs](/docs/send-data/collect-from-other-data-sources/collect-ruby-on-rails-logs/) |
-
-
-## S
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-| Automation integration: [SailPoint](/docs/platform-services/automation-service/app-central/integrations/sailpoint/)
Cloud SIEM integration: [SailPoint](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/965fe719-5d9f-4100-b0b6-684191925884.md)
Collector: [SailPoint Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/sailpoint-source/) | -|
Automation integration: [Salesforce](/docs/platform-services/automation-service/app-central/integrations/salesforce/)
Cloud SIEM integration: [Salesforce](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/02cab927-d7d7-4be6-bd59-18522f741544.md)
Collector: [Salesforce Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/salesforce-source/) | -|
}) | [Sauce Labs](https://saucelabs.com/) | Partner integration: [Sauce Labs](https://docs.saucelabs.com/basics/integrations/sumo/) |
-|
| [Sauce Labs](https://saucelabs.com/) | Partner integration: [Sauce Labs](https://docs.saucelabs.com/basics/integrations/sumo/) |
-| }) | [Screenshot Machine](https://www.screenshotmachine.com/) | Automation integration: [Screenshot Machine](/docs/platform-services/automation-service/app-central/integrations/screenshot-machine/) |
-|
| [Screenshot Machine](https://www.screenshotmachine.com/) | Automation integration: [Screenshot Machine](/docs/platform-services/automation-service/app-central/integrations/screenshot-machine/) |
-| }) | [SecureAuth](https://www.secureauth.com/) | Cloud SIEM integration: [SecureAuth](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/72744d1c-ddff-4ead-b76e-60430704f945.md) |
-|
| [SecureAuth](https://www.secureauth.com/) | Cloud SIEM integration: [SecureAuth](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/72744d1c-ddff-4ead-b76e-60430704f945.md) |
-| }) | [Security Scorecard](https://securityscorecard.com/) | Automation integration: [Security Scorecard](/docs/platform-services/automation-service/app-central/integrations/security-scorecard/) |
-|
| [Security Scorecard](https://securityscorecard.com/) | Automation integration: [Security Scorecard](/docs/platform-services/automation-service/app-central/integrations/security-scorecard/) |
-| }) | [SecurityTrails](https://securitytrails.com/) | Automation integration: [SecurityTrails](/docs/platform-services/automation-service/app-central/integrations/securitytrails/) |
-|
| [SecurityTrails](https://securitytrails.com/) | Automation integration: [SecurityTrails](/docs/platform-services/automation-service/app-central/integrations/securitytrails/) |
-| }) | [Securonix](https://www.securonix.com/) | Automation integrations:
| [Securonix](https://www.securonix.com/) | Automation integrations: - [Securonix](/docs/platform-services/automation-service/app-central/integrations/securonix/)
- [Securonix V2](/docs/platform-services/automation-service/app-central/integrations/securonix-v2/) | -|
}) | [SendGrid](https://sendgrid.com/) | Webhook: [SendGrid](/docs/integrations/webhooks/sendgrid/) |
-|
| [SendGrid](https://sendgrid.com/) | Webhook: [SendGrid](/docs/integrations/webhooks/sendgrid/) |
-| Automation integration: [SentinelOne](/docs/platform-services/automation-service/app-central/integrations/sentinelone/)
Cloud SIEM integration: [SentinelOne](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/20617100-01e3-409a-8918-fd665fc31c88.md)
Collectors:
- [Collect Logs for SentinelOne](/docs/send-data/collect-from-other-data-sources/collect-logs-sentinelone/)
- [SentinelOne Mgmt API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/sentinelone-mgmt-api-source/)
- [SentinelOne - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/sentinelone/) | -|
}) | [Sensu](https://sensu.io/) | Partner integration: [Send data to Sumo Logic with Sensu](https://docs.sensu.io/sensu-go/latest/observability-pipeline/observe-process/send-data-sumo-logic/) |
-|
| [Sensu](https://sensu.io/) | Partner integration: [Send data to Sumo Logic with Sensu](https://docs.sensu.io/sensu-go/latest/observability-pipeline/observe-process/send-data-sumo-logic/) |
-| }) | [SIGNL4](https://www.signl4.com/) | Webhooks:
| [SIGNL4](https://www.signl4.com/) | Webhooks: - [SIGNL4](/docs/integrations/webhooks/signl4/)
- [Webhook Connection for SIGNL4](/docs/alerts/webhook-connections/signl4/) | -|
}) | [Sentry](https://sentry.io/welcome/) | Webhook: [Sentry](/docs/integrations/webhooks/sentry/) |
-|
| [Sentry](https://sentry.io/welcome/) | Webhook: [Sentry](/docs/integrations/webhooks/sentry/) |
-| }) | [ServiceNow](https://www.servicenow.com/) | Automation integration: [ServiceNow V2](/docs/platform-services/automation-service/app-central/integrations/servicenow-v2/)
| [ServiceNow](https://www.servicenow.com/) | Automation integration: [ServiceNow V2](/docs/platform-services/automation-service/app-central/integrations/servicenow-v2/) Webhook: [ServiceNow](/docs/alerts/webhook-connections/servicenow/) | -|
}) | [Shodan](https://www.shodan.io/) | Automation integration: [Shodan](/docs/platform-services/automation-service/app-central/integrations/shodan/) |
-|
| [Shodan](https://www.shodan.io/) | Automation integration: [Shodan](/docs/platform-services/automation-service/app-central/integrations/shodan/) |
-| }) | [Silent Push](https://www.silentpush.com/) | Automation integration: [Silent Push](/docs/platform-services/automation-service/app-central/integrations/silent-push) |
-|
| [Silent Push](https://www.silentpush.com/) | Automation integration: [Silent Push](/docs/platform-services/automation-service/app-central/integrations/silent-push) |
-| }) | [Slack](https://slack.com/) | App: [Slack](/docs/integrations/saas-cloud/slack/)
| [Slack](https://slack.com/) | App: [Slack](/docs/integrations/saas-cloud/slack/) Automation integration: [Slack](/docs/platform-services/automation-service/app-central/integrations/slack/)
Cloud SIEM integration: [Slack](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c93d9bf6-0a88-49fc-aebb-ac7b2ea6792c.md)
Collector: [Slack Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/slack-source/)
Webhook: [Webhook Connection for Slack](/docs/alerts/webhook-connections/slack/) | -|
}) | [Snare](https://www.snaresolutions.com/) | Cloud SIEM integration: [Intersect Alliance](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/005c835d-f067-4147-9da9-fe4d2691247e.md) |
-|
| [Snare](https://www.snaresolutions.com/) | Cloud SIEM integration: [Intersect Alliance](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/005c835d-f067-4147-9da9-fe4d2691247e.md) |
-| }) | [Snowflake](https://www.snowflake.com/en/) | Cloud SIEM integration: [Snowflake](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/5541f59d-e27d-48e6-a35c-34fb75e9cf13.md) |
-|
| [Snowflake](https://www.snowflake.com/en/) | Cloud SIEM integration: [Snowflake](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/5541f59d-e27d-48e6-a35c-34fb75e9cf13.md) |
-| }) | [Snyk](https://snyk.io/) | Automation integration: [Snyk](/docs/platform-services/automation-service/app-central/integrations/snyk/) |
-|
| [Snyk](https://snyk.io/) | Automation integration: [Snyk](/docs/platform-services/automation-service/app-central/integrations/snyk/) |
-| }) | [SOCRadar](https://socradar.io/) | Automation integration: [SOCRadar](/docs/platform-services/automation-service/app-central/integrations/socradar/) |
-|
| [SOCRadar](https://socradar.io/) | Automation integration: [SOCRadar](/docs/platform-services/automation-service/app-central/integrations/socradar/) |
-| }) | [SonicWall](https://www.sonicwall.com/) | Automation integration: [SonicWall](/docs/platform-services/automation-service/app-central/integrations/sonicwall/) |
-|
| [SonicWall](https://www.sonicwall.com/) | Automation integration: [SonicWall](/docs/platform-services/automation-service/app-central/integrations/sonicwall/) |
-| }) | [Sophos](https://www.sophos.com/en-us) | Automation integrations:
| [Sophos](https://www.sophos.com/en-us) | Automation integrations: - [Sophos Central](/docs/platform-services/automation-service/app-central/integrations/sophos-central/)
- [Sophos Central V3](/docs/platform-services/automation-service/app-central/integrations/sophos-central-v3/)
Cloud SIEM integration: [Sophos](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/dc8564e3-6c44-463a-8bad-36618a688d57.md)
Collector: [Sophos Central Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/sophos-central-source/)
Community app: [Sumo Logic for Sophos Central](https://github.com/SumoLogic/sumologic-content/tree/master/Sophos/Sophos-Central) | -|
}) | [SpiderFoot HX](https://login.hx.spiderfoot.net/) | Automation integration: [SpiderFoot HX](/docs/platform-services/automation-service/app-central/integrations/spiderfoot-hx/) |
-|
| [SpiderFoot HX](https://login.hx.spiderfoot.net/) | Automation integration: [SpiderFoot HX](/docs/platform-services/automation-service/app-central/integrations/spiderfoot-hx/) |
-| }) | [Spinnaker](https://spinnaker.io/) | Partner integration: [Spinnaker](https://docs.armory.io/continuous-deployment/armory-admin/observe/integrations-sumologic/) |
-|
| [Spinnaker](https://spinnaker.io/) | Partner integration: [Spinnaker](https://docs.armory.io/continuous-deployment/armory-admin/observe/integrations-sumologic/) |
-| }) | [Split](https://www.split.io/) | Webhook: [Split](/docs/integrations/webhooks/split/) |
-|
| [Split](https://www.split.io/) | Webhook: [Split](/docs/integrations/webhooks/split/) |
-| }) | [Splunk](https://www.splunk.com/) | Automation integration: [Splunk](/docs/platform-services/automation-service/app-central/integrations/splunk/)
| [Splunk](https://www.splunk.com/) | Automation integration: [Splunk](/docs/platform-services/automation-service/app-central/integrations/splunk/) Collector: [Import Raw Data from Splunk](/docs/send-data/collect-from-other-data-sources/import-raw-data-splunk/) | -|
}) | [Squadcast](https://www.squadcast.com/) | Webhook: [Squadcast](/docs/integrations/webhooks/squadcast/) |
-|
| [Squadcast](https://www.squadcast.com/) | Webhook: [Squadcast](/docs/integrations/webhooks/squadcast/) |
-| }) | [Squid Cache](http://www.squid-cache.org/) | Apps:
| [Squid Cache](http://www.squid-cache.org/) | Apps: - [Squid Proxy](/docs/integrations/web-servers/squid-proxy/)
- [Squid Proxy - OpenTelemetry](/docs/integrations/web-servers/opentelemetry/squid-proxy-opentelemetry/)
Cloud SIEM integration: [Squid](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/470cb4ad-ac19-442b-9b3a-28b979d47d8e.md) | -|
}) | [StackRox](https://www.stackrox.io/) | Collector: [StackRox](https://cdn.stackrox.io/integrations/sumologic-stackrox-app.pdf)
| [StackRox](https://www.stackrox.io/) | Collector: [StackRox](https://cdn.stackrox.io/integrations/sumologic-stackrox-app.pdf) Partner integration: [StackRox app](https://cdn.stackrox.io/integrations/sumologic-stackrox-app.pdf) | -|
}) | [StatsD](https://www.datadoghq.com/blog/statsd/) | Collector: [Collect StatsD Metrics](/docs/send-data/collect-from-other-data-sources/collect-statsd-metrics/) |
-|
| [StatsD](https://www.datadoghq.com/blog/statsd/) | Collector: [Collect StatsD Metrics](/docs/send-data/collect-from-other-data-sources/collect-statsd-metrics/) |
-| }) | [Stellar Cyber](https://stellarcyber.ai/) | [Stellar Cyber Starlight](/docs/platform-services/automation-service/app-central/integrations/stellar-cyber-starlight/) |
-|
| [Stellar Cyber](https://stellarcyber.ai/) | [Stellar Cyber Starlight](/docs/platform-services/automation-service/app-central/integrations/stellar-cyber-starlight/) |
-| }) | [Strimzi](https://strimzi.io/) | App: [Strimzi Kafka](/docs/integrations/containers-orchestration/strimzi-kafka/) |
-|
| [Strimzi](https://strimzi.io/) | App: [Strimzi Kafka](/docs/integrations/containers-orchestration/strimzi-kafka/) |
-| }) | [Stripe](https://stripe.com/) | Webhook: [Stripe](/docs/integrations/webhooks/stripe/) |
-|
| [Stripe](https://stripe.com/) | Webhook: [Stripe](/docs/integrations/webhooks/stripe/) |
-| }) | [Sucuri](https://sucuri.net/) | Cloud SIEM integration: [Sucuri](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/cdfd2ba0-77eb-4e11-b071-6f4d01fda607.md) |
-|
| [Sucuri](https://sucuri.net/) | Cloud SIEM integration: [Sucuri](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/cdfd2ba0-77eb-4e11-b071-6f4d01fda607.md) |
-| }) | [Sumo Logic](https://www.sumologic.com/) | Apps:
| [Sumo Logic](https://www.sumologic.com/) | Apps: - [Enterprise Audit - Cloud SIEM](/docs/integrations/sumo-apps/cse/)
- [Sumo Logic Audit App](/docs/integrations/sumo-apps/audit/)
- [Sumo Logic Data Volume App](/docs/integrations/sumo-apps/data-volume/)
- [Sumo Logic Enterprise Audit Apps](/docs/integrations/sumo-apps/enterprise-audit/) (multiple apps)
- [Sumo Logic Enterprise Search Audit App](/docs/integrations/sumo-apps/enterprise-search-audit/)
- [Sumo Logic Infrequent Data Tier App](/docs/integrations/sumo-apps/infrequent-data-tier/)
- [Sumo Logic Log Analysis QuickStart App](/docs/integrations/sumo-apps/log-analysis-quickstart/)
- [Sumo Logic Security Analytics App](/docs/integrations/sumo-apps/security-analytics/)
Automation integrations:
- [Basic Tools](/docs/platform-services/automation-service/app-central/integrations/basic-tools/)
- [ESMTP](/docs/platform-services/automation-service/app-central/integrations/esmtp/)
- [HTTP Tools](/docs/platform-services/automation-service/app-central/integrations/http-tools/)
- [Incident Tools](/docs/platform-services/automation-service/app-central/integrations/incident-tools/)
- [IMAP](/docs/platform-services/automation-service/app-central/integrations/imap/)
- [Mail Tools](/docs/platform-services/automation-service/app-central/integrations/mail-tools/)
- [POP3](/docs/platform-services/automation-service/app-central/integrations/pop3/)
- [SMTP V3](/docs/platform-services/automation-service/app-central/integrations/smtp-v3/)
- [Sumo Logic Cloud SIEM](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-cloud-siem/)
- [Sumo Logic Cloud SIEM Internal](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-cloud-siem-internal/)
- [Sumo Logic Log Analytics](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-log-analytics/)
- [Sumo Logic Log Analytics Internal](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-log-analytics-internal/)
- [Sumo Logic Notifications](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-notifications/)
- [Triage Tools](/docs/platform-services/automation-service/app-central/integrations/triage-tools/)
- [ZIP Tools](/docs/platform-services/automation-service/app-central/integrations/zip-tools/)
Cloud SIEM integration: [Sumo Logic](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/34A5019C-7BEC-4BF8-A3B7-C38D567126C6.md)
Community app: [Cloud Security Posture Management (CSPM) for Sumo Logic](https://github.com/SumoLogic/sumologic-content/tree/master/CSPM) | -|
}) | [Superwise](https://superwise.ai/) | Webhook: [Superwise](/docs/integrations/webhooks/superwise/) |
-|
| [Superwise](https://superwise.ai/) | Webhook: [Superwise](/docs/integrations/webhooks/superwise/) |
-| }) | [Symantec](https://sep.securitycloud.symantec.com/v2/landing) | App: [Symantec Web Security Service](/docs/integrations/saas-cloud/symantec-web-security-service/)
| [Symantec](https://sep.securitycloud.symantec.com/v2/landing) | App: [Symantec Web Security Service](/docs/integrations/saas-cloud/symantec-web-security-service/) Automation integrations:
- [Javelin AD Protect](/docs/platform-services/automation-service/app-central/integrations/javelin-ad-protect/)
- [Symantec DeepSight](/docs/platform-services/automation-service/app-central/integrations/symantec-deepsight/)
- [Symantec EDR](/docs/platform-services/automation-service/app-central/integrations/symantec-edr/)
- [Symantec Endpoint Protection](/docs/platform-services/automation-service/app-central/integrations/symantec-endpoint-protection/)
- [Symantec Endpoint Protection Cloud](/docs/platform-services/automation-service/app-central/integrations/symantec-endpoint-protection-cloud/)
- [Symantec Secure Web Gateway (Bluecoat)](/docs/platform-services/automation-service/app-central/integrations/symantec-secure-web-gateway-bluecoat/)
- [Symantec WebPulse](/docs/platform-services/automation-service/app-central/integrations/symantec-webpulse/)
Collectors:
- [Symantec Web Security Service Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/symantec-web-security-service-source/)
- [Symantec Proxy Secure Gateway - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/symantec-proxy-secure-gateway/)
- [Symantec Proxy Secure Gateway (Blue Coat Proxy) - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/symantec-proxy-secure-gateway-blue-coat-proxy/)
Cloud SIEM integration: [Symantec](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/64c7f49c-f95a-4f4a-8540-56ec5fb1d96b.md)
Community app: [Sumo Logic for Symantec WSS](https://github.com/SumoLogic/sumologic-content/tree/master/Symantec/WSS) | -|
}) | [Sysdig](https://sysdig.com/) | Cloud SIEM integration: [Sysdig](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c4de0854-e718-45e1-a4c8-63623755aa43.md) |
-|
| [Sysdig](https://sysdig.com/) | Cloud SIEM integration: [Sysdig](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c4de0854-e718-45e1-a4c8-63623755aa43.md) |
-| }) | [syslog-ng](https://www.syslog-ng.com/) | Automation integration: [Syslog-NG](/docs/platform-services/automation-service/app-central/integrations/syslog-ng/)
| [syslog-ng](https://www.syslog-ng.com/) | Automation integration: [Syslog-NG](/docs/platform-services/automation-service/app-central/integrations/syslog-ng/) Collector: [syslog-ng](/docs/send-data/hosted-collectors/cloud-syslog-source/syslog-ng/) | - -## T - -| Logo | Vendors and Products | Integrations | -| :-- | :-- | :-- | -|
}) | [Tanium](https://www.tanium.com/) | Cloud SIEM integration: [Tanium](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c7a342e6-5621-401a-ac5c-80ea3f2db23c.md)
| [Tanium](https://www.tanium.com/) | Cloud SIEM integration: [Tanium](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c7a342e6-5621-401a-ac5c-80ea3f2db23c.md) Collector: [Tanium](https://community.tanium.com/s/article/How-can-I-send-Tanium-data-to-Sumo-Logic) | -|
}) | [Telegraf](https://www.influxdata.com/time-series-platform/telegraf/) | Collector: [Telegraf](/docs/send-data/collect-from-other-data-sources/collect-metrics-telegraf/) |
-|
| [Telegraf](https://www.influxdata.com/time-series-platform/telegraf/) | Collector: [Telegraf](/docs/send-data/collect-from-other-data-sources/collect-metrics-telegraf/) |
-| }) | [Telegram](https://telegram.org/) | Automation integration: [Telegram V2](/docs/platform-services/automation-service/app-central/integrations/telegram-v2/) |
-|
| [Telegram](https://telegram.org/) | Automation integration: [Telegram V2](/docs/platform-services/automation-service/app-central/integrations/telegram-v2/) |
-| }) | [Tenable](https://www.tenable.com/) | App: [Tenable](/docs/integrations/saas-cloud/tenable/)
| [Tenable](https://www.tenable.com/) | App: [Tenable](/docs/integrations/saas-cloud/tenable/) Automation integrations:
- [Tenable.io](/docs/platform-services/automation-service/app-central/integrations/tenable.io/)
- [Tenable.sc](/docs/platform-services/automation-service/app-central/integrations/tenable.sc/)
Cloud SIEM integration: [Tenable](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/600BEF8F-BE81-4767-8322-72116C16DB20.md)
Collector: [Tenable Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/tenable-source/)
Community app: [Sumo Logic for Tenable IO](https://github.com/SumoLogic/sumologic-content/tree/master/Tenable/Tenable_IO) | -|
}) | [Tessian](https://www.tessian.com/) | Partner integration: [Tessian for Sumo Logic](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Tessian#tessian-for-sumo-logic) |
-|
| [Tessian](https://www.tessian.com/) | Partner integration: [Tessian for Sumo Logic](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Tessian#tessian-for-sumo-logic) |
-| }) | [TheHive](https://thehive-project.org/) | Automation integration: [TheHive](/docs/platform-services/automation-service/app-central/integrations/thehive/) |
-|
| [TheHive](https://thehive-project.org/) | Automation integration: [TheHive](/docs/platform-services/automation-service/app-central/integrations/thehive/) |
-| }) | [Thinkst Canary](https://canary.tools/) | [Thinkst Canary](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/0152e233-fce6-4cbf-9edc-721d7bef94f8.md) |
-|
| [Thinkst Canary](https://canary.tools/) | [Thinkst Canary](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/0152e233-fce6-4cbf-9edc-721d7bef94f8.md) |
-| }) | [ThreatConnect](https://threatconnect.com/) | Automation integration: [ThreatConnect](/docs/platform-services/automation-service/app-central/integrations/threatconnect/) |
-|
| [ThreatConnect](https://threatconnect.com/) | Automation integration: [ThreatConnect](/docs/platform-services/automation-service/app-central/integrations/threatconnect/) |
-| }) | [Threat Crowd](https://otx.alienvault.com/) | Automation integration: [Threat Crowd](/docs/platform-services/automation-service/app-central/integrations/threat-crowd/) |
-|
| [Threat Crowd](https://otx.alienvault.com/) | Automation integration: [Threat Crowd](/docs/platform-services/automation-service/app-central/integrations/threat-crowd/) |
-| }) | [Threater](https://www.threater.com/) | Cloud SIEM integration: [Bandura](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/ec354a4c-a761-4e18-8ceb-194d6e8692e2.md) |
-|
| [Threater](https://www.threater.com/) | Cloud SIEM integration: [Bandura](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/ec354a4c-a761-4e18-8ceb-194d6e8692e2.md) |
-| }) | [ThreatMiner](https://www.threatminer.org/) | Automation integration: [ThreatMiner](/docs/platform-services/automation-service/app-central/integrations/threatminer/) |
-|
| [ThreatMiner](https://www.threatminer.org/) | Automation integration: [ThreatMiner](/docs/platform-services/automation-service/app-central/integrations/threatminer/) |
-| }) | [ThreatQ](https://www.threatq.com/) | Automation integration: [ThreatQ](/docs/platform-services/automation-service/app-central/integrations/threatq/) |
-|
| [ThreatQ](https://www.threatq.com/) | Automation integration: [ThreatQ](/docs/platform-services/automation-service/app-central/integrations/threatq/) |
-| }) | [Trellix](https://www.trellix.com/en-us/index.html) | Automation integrations:
| [Trellix](https://www.trellix.com/en-us/index.html) | Automation integrations: - [FireEye AX](/docs/platform-services/automation-service/app-central/integrations/fireeye-ax/)
- [FireEye Central Management (CM)](/docs/platform-services/automation-service/app-central/integrations/fireeye-central-management-cm/)
- [FireEye Email Security (EX)](/docs/platform-services/automation-service/app-central/integrations/fireeye-email-security-ex/)
- [FireEye Endpoint Security (HX)](/docs/platform-services/automation-service/app-central/integrations/fireeye-endpoint-security-hx/)
- [FireEye Helix](/docs/platform-services/automation-service/app-central/integrations/fireeye-helix/)
- [FireEye Network Security (NX)](/docs/platform-services/automation-service/app-central/integrations/fireeye-network-security-nx/)
Cloud SIEM integrations:
- [FireEye](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/1430ab5c-7b8b-44e9-a8ec-83076fa374eb.md)
- [Trellix](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9bec8407-4182-46ec-99dd-2adfade15652.md)
Collector: [Trellix mVision ePO Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/trellix-mvisio-epo-source/) | -|
Automation integrations:
- [Trend Micro Deep Security](/docs/platform-services/automation-service/app-central/integrations/trend-micro-deep-security/)
- [Trend Micro Vision ONE](/docs/platform-services/automation-service/app-central/integrations/trend-micro-vision-one/)
Cloud SIEM integration: [Trend Micro](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/8af48b83-18bf-4233-ad51-db37baca0313.md) | -|
}) | [Tufin](https://www.tufin.com/) | Automation integrations:
| [Tufin](https://www.tufin.com/) | Automation integrations: - [Tufin SecureChange](/docs/platform-services/automation-service/app-central/integrations/tufin-securechange/)
- [Tufin SecureTrack V2](/docs/platform-services/automation-service/app-central/integrations/tufin-securetrack-v2/) | - -## U - -| Logo | Vendors and Products | Integrations | -| :-- | :-- | :-- | -|
}) | [Uptime](https://uptime.com/) | Webhook: [Uptime](/docs/integrations/webhooks/uptime/) |
-|
| [Uptime](https://uptime.com/) | Webhook: [Uptime](/docs/integrations/webhooks/uptime/) |
-| }) | [URLScan.io](https://urlscan.io/) | Automation integration: [URLScan.io](/docs/platform-services/automation-service/app-central/integrations/urlscan.io/) |
-
-## V
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-|
| [URLScan.io](https://urlscan.io/) | Automation integration: [URLScan.io](/docs/platform-services/automation-service/app-central/integrations/urlscan.io/) |
-
-## V
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-| }) | [Varnish](https://www.varnish-software.com/) | Apps:
| [Varnish](https://www.varnish-software.com/) | Apps: - [Varnish](/docs/integrations/web-servers/varnish/)
- [Varnish - OpenTelemetry](/docs/integrations/web-servers/opentelemetry/varnish-opentelemetry/) | -|
}) | [Varonis](https://www.varonis.com/) | Cloud SIEM integration: [Varonis](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/20270f89-127e-4055-96ec-56045e67e163.md) |
-|
| [Varonis](https://www.varonis.com/) | Cloud SIEM integration: [Varonis](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/20270f89-127e-4055-96ec-56045e67e163.md) |
-| }) | [Vectra](https://www.vectra.ai/) | Automation integration: [Vectra](/docs/platform-services/automation-service/app-central/integrations/vectra/)
| [Vectra](https://www.vectra.ai/) | Automation integration: [Vectra](/docs/platform-services/automation-service/app-central/integrations/vectra/) Cloud SIEM integration: [Vectra](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/7a3d1a5c-ba67-4597-971f-7057e8f6c8bb.md) | -|
}) | [VirusTotal](https://www.virustotal.com/) | Automation integration: [VirusTotal](/docs/platform-services/automation-service/app-central/integrations/virustotal/) |
-|
| [VirusTotal](https://www.virustotal.com/) | Automation integration: [VirusTotal](/docs/platform-services/automation-service/app-central/integrations/virustotal/) |
-| }) | [VMRay](https://www.vmray.com/) | Automation integration: [VMRay](/docs/platform-services/automation-service/app-central/integrations/vmray/) |
-|
| [VMRay](https://www.vmray.com/) | Automation integration: [VMRay](/docs/platform-services/automation-service/app-central/integrations/vmray/) |
-| }) | [VMware](https://www.vmware.com/) | Apps:
| [VMware](https://www.vmware.com/) | Apps: - [Carbon Black Cloud](/docs/integrations/security-threat-detection/carbon-black-cloud/)
- [VMware](/docs/integrations/containers-orchestration/vmware/)
- [VMware Legacy](/docs/integrations/containers-orchestration/vmware-legacy/)
- [VMware Carbon Black](/docs/integrations/security-threat-detection/vmware-carbon-black/)
Automation integrations:
- [Lastline Analyst](/docs/platform-services/automation-service/app-central/integrations/lastline-analyst/)
- [VMware Carbon Black Cloud Endpoint Standard](/docs/platform-services/automation-service/app-central/integrations/vmware-carbon-black-cloud-endpoint-standard/)
- [VMware Carbon Black Cloud Endpoint Standard V2](/docs/platform-services/automation-service/app-central/integrations/vmware-carbon-black-cloud-endpoint-standard-v2/)
- [VMware Carbon Black Cloud Enterprise EDR](/docs/platform-services/automation-service/app-central/integrations/vmware-carbon-black-cloud-enterprise-edr/)
- [VMware Carbon Black Cloud Platform](/docs/platform-services/automation-service/app-central/integrations/vmware-carbon-black-cloud-platform/)
- [VMware vSphere](/docs/platform-services/automation-service/app-central/integrations/vmware-vsphere/)
- [VMware Workspace ONE](/docs/platform-services/automation-service/app-central/integrations/vmware-workspace-one/)
Cloud SIEM integrations:
- [Carbon Black](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c2ea2e5e-92f2-49e8-9812-64e60dba63a2.md)
- [VMware](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/fbf25b91-89f1-45c4-903d-664b328bc6e0.md)
Collectors:
- [Carbon Black Cloud Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/carbon-black-cloud-source/)
- [Carbon Black Inventory Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/carbon-black-inventory-source/)
- [Carbon Black Cloud - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/carbon-black/)
- [Collect Metrics from VMware vRealize Operations Manager 8 Enterprise](/docs/send-data/collect-from-other-data-sources/collect-metrics-vrealize-operations-manager/)
- [VMware AirWatch Integration for Sumo Logic](/docs/send-data/collect-from-other-data-sources/vmware-airwatch-integration/)
- [VMware vRealize Log Insight](/docs/send-data/collect-from-other-data-sources/vmware-vrealize-log-insight/)
Partner integration: [VMware Tanzu](https://docs.vmware.com/en/Sumo-Logic-Nozzle-for-VMware-Tanzu/services/sumologic-nozzle-vmware-tanzu/index.html) | -|
}) | [Votiro](https://votiro.com/) | Partner integration: [Votiro](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Votiro#votiro) |
-
-## W
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-|
| [Votiro](https://votiro.com/) | Partner integration: [Votiro](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Votiro#votiro) |
-
-## W
-
-| Logo | Vendors and Products | Integrations |
-| :-- | :-- | :-- |
-| }) | [Watchguard](https://www.watchguard.com/) | Automation integration: [Panda EDR](/docs/platform-services/automation-service/app-central/integrations/panda-edr/) |
-|
| [Watchguard](https://www.watchguard.com/) | Automation integration: [Panda EDR](/docs/platform-services/automation-service/app-central/integrations/panda-edr/) |
-| }) | [WhoisXML](https://main.whoisxmlapi.com/) | Automation integration: [WhoisXML](/docs/platform-services/automation-service/app-central/integrations/whoisxml/) |
-|
| [WhoisXML](https://main.whoisxmlapi.com/) | Automation integration: [WhoisXML](/docs/platform-services/automation-service/app-central/integrations/whoisxml/) |
-| }) | [Windows](https://www.microsoft.com/en-us/windows) | Apps:
| [Windows](https://www.microsoft.com/en-us/windows) | Apps: - [Windows Cloud Security Monitoring and Analytics](/docs/integrations/cloud-security-monitoring-analytics/windows/)
- [Windows - Cloud Security Monitoring and Analytics - OpenTelemetry](/docs/integrations/cloud-security-monitoring-analytics/opentelemetry/windows-opentelemetry/)
- [Windows JSON](/docs/integrations/microsoft-azure/windows-json/)
- [Windows - OpenTelemetry](/docs/integrations/hosts-operating-systems/opentelemetry/windows-opentelemetry/)
- [Windows Performance](/docs/integrations/microsoft-azure/performance/)
- [Windows Legacy](/docs/integrations/microsoft-azure/windows-legacy/)
- [PCI Compliance For Windows (JSON)](/docs/integrations/microsoft-azure/windows-json-pci-compliance/)
- [PCI Compliance for Windows JSON - OpenTelemetry](/docs/integrations/pci-compliance/opentelemetry/windows-json-opentelemetry/)
Automation integration: [PowerShell Tools](/docs/platform-services/automation-service/app-central/integrations/powershell-tools/)
Collectors:
- [Add a Collector to a Windows Machine Image](/docs/send-data/installed-collectors/collector-installation-reference/add-collector-windows-machine-image/)
- [Install a Collector on Windows](/docs/send-data/installed-collectors/windows/)
- [Install OpenTelemetry Collector on Windows](/docs/send-data/opentelemetry-collector/install-collector/windows/)
- [Local Windows Event Log Source](/docs/send-data/installed-collectors/sources/local-windows-event-log-source/)
- [Local Windows Performance Monitor Log Source](/docs/send-data/installed-collectors/sources/local-windows-performance-monitor-log-source/)
- [Microsoft Windows - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/microsoft-windows/)
- [Preconfigure a Machine to Collect Remote Windows Events](/docs/send-data/installed-collectors/sources/preconfigure-machine-collect-remote-windows-events/)
- [Preconfigure a Machine to Collect Remote Windows Performance Monitoring Logs](/docs/send-data/installed-collectors/sources/preconfigure-machine-collect-remote-windows-performance-monitoring-logs/)
- [Remote Windows Event Log Source](/docs/send-data/installed-collectors/sources/remote-windows-event-log-source/)
- [Remote Windows Performance Monitor Log Source](/docs/send-data/installed-collectors/sources/remote-windows-performance-monitor-log-source/)
- [Windows Event Source Custom Channels](/docs/send-data/installed-collectors/sources/windows-event-source-custom-channels/)| -|
}) | [WithSecure](https://www.withsecure.com/en/home) | Automation integrations:
| [WithSecure](https://www.withsecure.com/en/home) | Automation integrations: - [WithSecure Elements](/docs/platform-services/automation-service/app-central/integrations/withsecure-elements/)
- [WithSecure Endpoint Protection](/docs/platform-services/automation-service/app-central/integrations/withsecure-endpoint-protection/) | -|
}) | [Wittra](https://www.wittra.io/) | Automation integration: [Wittra](/docs/platform-services/automation-service/app-central/integrations/wittra/) |
-|
| [Wittra](https://www.wittra.io/) | Automation integration: [Wittra](/docs/platform-services/automation-service/app-central/integrations/wittra/) |
-| }) | [Wiz](https://www.wiz.io/) | Cloud SIEM integration: [Wiz](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/2cde0cac-102b-4756-9a56-81437fea1400.md) |
-|
| [Wiz](https://www.wiz.io/) | Cloud SIEM integration: [Wiz](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/2cde0cac-102b-4756-9a56-81437fea1400.md) |
-| }) | [Workday](https://www.workday.com/) | App: [Workday](/docs/integrations/saas-cloud/workday/)
| [Workday](https://www.workday.com/) | App: [Workday](/docs/integrations/saas-cloud/workday/) Cloud SIEM integration: [Workday](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/6e7ce4b2-569e-476d-b732-7b3a71b1e12a.md)
Collector: [Workday Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/workday-source/) | - -## Z - -| Logo | Vendors and Products | Integrations | -| :-- | :-- | :-- | -|
}) | [Zebrium](https://www.zebrium.com/) | Webhook: [Zebrium RCaaS](/docs/integrations/webhooks/zebrium-rcaas/) |
-|
| [Zebrium](https://www.zebrium.com/) | Webhook: [Zebrium RCaaS](/docs/integrations/webhooks/zebrium-rcaas/) |
-| }) | [Zendesk](https://www.zendesk.com/) | Automation integration: [Zendesk](/docs/platform-services/automation-service/app-central/integrations/zendesk/) |
-|
| [Zendesk](https://www.zendesk.com/) | Automation integration: [Zendesk](/docs/platform-services/automation-service/app-central/integrations/zendesk/) |
-| }) | [Zenduty](https://www.zenduty.com/) | Webhook: [Zenduty](/docs/integrations/webhooks/zenduty/) |
-|
| [Zenduty](https://www.zenduty.com/) | Webhook: [Zenduty](/docs/integrations/webhooks/zenduty/) |
-| Collector: [Zero Networks Segment Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/zero-networks-segment-source/) | -|
}) | [ZeroFox](https://www.zerofox.com/) | Automation integration: [ZeroFOX](/docs/platform-services/automation-service/app-central/integrations/zerofox/)
| [ZeroFox](https://www.zerofox.com/) | Automation integration: [ZeroFOX](/docs/platform-services/automation-service/app-central/integrations/zerofox/) Partner integration: [ZeroFox integration](https://drive.google.com/file/d/13svc5FP0WP3WAES6DvXhK1O8WRiPenf3/edit) | -|
}) | [Zoom](https://zoom.us/) | App: [Zoom](/docs/integrations/saas-cloud/zoom/)
| [Zoom](https://zoom.us/) | App: [Zoom](/docs/integrations/saas-cloud/zoom/) Automation integration: [Zoom](/docs/platform-services/automation-service/app-central/integrations/zoom/)
Cloud SIEM integration: [Zoom](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/bda720cd-399c-4dcc-9289-19ad0c9cb221.md)
Collector: [Zoom Source](/docs/send-data/hosted-collectors/webhook-sources/zoom/) | -|
}) | [Zscaler](https://www.zscaler.com/) | Apps:
| [Zscaler](https://www.zscaler.com/) | Apps: - [Zscaler Internet Access](/docs/integrations/security-threat-detection/zscaler-internet-access/)
- [Zscaler Private Access](/docs/integrations/security-threat-detection/zscaler-private-access/)
Automation integration: [Zscaler](/docs/platform-services/automation-service/app-central/integrations/zscaler/)
Cloud SIEM integration: [Zscaler](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9dfd2223-1656-4faf-a38a-5a91978fa15e.md)
Collectors:
- [ZScaler NSS - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/zscaler-nss/)
- [Zscaler Private Access - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/zscaler-private-access/) | diff --git a/docs/integrations/product-list/product-list-m-z.md b/docs/integrations/product-list/product-list-m-z.md new file mode 100644 index 0000000000..74fc3b1e1f --- /dev/null +++ b/docs/integrations/product-list/product-list-m-z.md @@ -0,0 +1,227 @@ +--- +id: product-list-m-z +title: Product List M-Z +description: This article lists all the products M-Z that Sumo Logic integrates with. +--- + +import useBaseUrl from '@docusaurus/useBaseUrl'; + +Following are the vendors and products that Sumo Logic integrates with, listed M-Z. We've divided the list into two articles to make the list easier to navigate. For the remainder, see [Product List A-L](/docs/integrations/product-list/product-list-a-l/). + +For descriptions of the different types of integrations Sumo Logic offers, see [Product List](/docs/integrations/product-list/). + + +## M + +| Logo | Vendors and Products | Integrations | +| :-- | :-- | :-- | +|
Collectors:
- [Install a Collector on macOS](/docs/send-data/installed-collectors/macos/)
- [Install OpenTelemetry Collector on macOS](/docs/send-data/opentelemetry-collector/install-collector/macos/) | +|
}) | [Mailgun](https://www.mailgun.com/) | Webhook: [Mailgun](/docs/integrations/webhooks/mailgun/) |
+|
| [Mailgun](https://www.mailgun.com/) | Webhook: [Mailgun](/docs/integrations/webhooks/mailgun/) |
+| }) | [Malwarebytes](https://www.malwarebytes.com/) | Automation integration: [Malwarebytes Nebula](/docs/platform-services/automation-service/app-central/integrations/malwarebytes-nebula/)
| [Malwarebytes](https://www.malwarebytes.com/) | Automation integration: [Malwarebytes Nebula](/docs/platform-services/automation-service/app-central/integrations/malwarebytes-nebula/) Cloud SIEM integration: [Malwarebytes](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/2e08dea2-4048-4f0f-9af8-aa85881151ad.md) | +|
}) | [ManageEngine](https://www.manageengine.com/) | Automation integration: [ManageEngine Desktop Central](/docs/platform-services/automation-service/app-central/integrations/manage-engine-desktop-central/)
| [ManageEngine](https://www.manageengine.com/) | Automation integration: [ManageEngine Desktop Central](/docs/platform-services/automation-service/app-central/integrations/manage-engine-desktop-central/) Cloud SIEM integration: [ManageEngine](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/e6417fdd-1aa1-436e-a659-38d71e51599f.md) | +|
}) | [MariaDB](https://mariadb.org/) | Apps:
| [MariaDB](https://mariadb.org/) | Apps: - [MariaDB](/docs/integrations/databases/mariadb/)
- [MariaDB - OpenTelemetry](/docs/integrations/databases/opentelemetry/mariadb-opentelemetry/) | +|
}) | [Material Security](https://material.security/) | Automation integration: [Material Security](/docs/platform-services/automation-service/app-central/integrations/material-security/) |
+|
| [Material Security](https://material.security/) | Automation integration: [Material Security](/docs/platform-services/automation-service/app-central/integrations/material-security/) |
+| }) | [Mattermost](https://mattermost.com/) | Automation integration: [Mattermost](/docs/platform-services/automation-service/app-central/integrations/mattermost/) |
+|
| [Mattermost](https://mattermost.com/) | Automation integration: [Mattermost](/docs/platform-services/automation-service/app-central/integrations/mattermost/) |
+| }) | [MaxMind](https://www.maxmind.com/en/home) | Automation integration: [MaxMind V2](/docs/platform-services/automation-service/app-central/integrations/maxmind-v2/) |
+|
| [MaxMind](https://www.maxmind.com/en/home) | Automation integration: [MaxMind V2](/docs/platform-services/automation-service/app-central/integrations/maxmind-v2/) |
+| }) | [McAfee](https://www.mcafee.com/) | Automation integrations:
| [McAfee](https://www.mcafee.com/) | Automation integrations: - [McAfee ATD](/docs/platform-services/automation-service/app-central/integrations/mcafee-atd/)
- [McAfee ESM](/docs/platform-services/automation-service/app-central/integrations/mcafee-esm/)
- [McAfee MVISION](/docs/platform-services/automation-service/app-central/integrations/mcafee-mvision/)
- [McAfee Network Security Platform Manager (NSM)](/docs/platform-services/automation-service/app-central/integrations/mcafee-network-security-platform-manager-nsm/)
- [McAfee Web Gateway](/docs/platform-services/automation-service/app-central/integrations/mcafee-web-gateway/)
Cloud SIEM integration: [McAfee](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/20dec895-f649-4959-9717-104fb68bb5b4.md) | +|
}) | [Memcached](https://memcached.org/) | Apps:
| [Memcached](https://memcached.org/) | Apps: - [Memcached](/docs/integrations/databases/memcached/)
- [Memcached - OpenTelemetry](/docs/integrations/databases/opentelemetry/memcached-opentelemetry/) | +|
}) | [Microsoft](https://www.microsoft.com/) | Apps:
| [Microsoft](https://www.microsoft.com/) | Apps: - [Azure Active Directory](/docs/integrations/microsoft-azure/active-directory-azure/)
- [Microsoft Dynamics 365](/docs/integrations/microsoft-azure/microsoft-dynamics365-customer-insights/)
- [Microsoft Exchange Trace Logs](/docs/integrations/saas-cloud/microsoft-exchange-trace-logs/)
- [Microsoft Graph Azure AD Reporting](/docs/integrations/saas-cloud/microsoft-graph-azure-ad-reporting/)
- [Microsoft Graph Identity Protection](/docs/integrations/microsoft-azure/microsoft-graph-identity-protection/)
- [Microsoft Graph Security V1](/docs/integrations/saas-cloud/microsoft-graph-security-v1/)
- [Microsoft Graph Security V2](/docs/integrations/saas-cloud/microsoft-graph-security-v2/)
- [Microsoft Office 365](/docs/integrations/microsoft-azure/office-365/)
- [Microsoft SQL Server](/docs/integrations/microsoft-azure/sql-server/)
- [Microsoft SQL Server - OpenTelemetry](/docs/integrations/microsoft-azure/opentelemetry/sql-server-opentelemetry)
- [Microsoft SQL Server for Linux - OpenTelemetry](/docs/integrations/microsoft-azure/opentelemetry/sql-server-linux-opentelemetry)
- [Microsoft Teams](/docs/integrations/microsoft-azure/teams/)
Automation integrations:
- [Microsoft 365 Defender](/docs/platform-services/automation-service/app-central/integrations/microsoft-365-defender/)
- [Microsoft Azure Log Analytics](/docs/platform-services/automation-service/app-central/integrations/microsoft-azure-log-analytics/)
- [Microsoft Azure Security Center](/docs/platform-services/automation-service/app-central/integrations/microsoft-azure-security-center/)
- [Microsoft Defender ATP](/docs/platform-services/automation-service/app-central/integrations/microsoft-defender-atp/)
- [Microsoft EWS](/docs/platform-services/automation-service/app-central/integrations/microsoft-ews/)
- [Microsoft EWS Daemon](/docs/platform-services/automation-service/app-central/integrations/microsoft-ews-daemon/)
- [Microsoft EWS Extension](/docs/platform-services/automation-service/app-central/integrations/microsoft-ews-extension/)
- [Microsoft Graph Security](/docs/platform-services/automation-service/app-central/integrations/microsoft-graph-security/)
- [Microsoft OneDrive](/docs/platform-services/automation-service/app-central/integrations/microsoft-onedrive/)
- [Microsoft Sharepoint](/docs/platform-services/automation-service/app-central/integrations/microsoft-sharepoint/)
- [Microsoft Sentinel](/docs/platform-services/automation-service/app-central/integrations/microsoft-sentinel/)
- [MSSQL](/docs/platform-services/automation-service/app-central/integrations/mssql/)
- [Microsoft Teams](/docs/platform-services/automation-service/app-central/integrations/microsoft-teams/)
Cloud SIEM integration: [Microsoft](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/2b002817-fd14-49b3-a3fe-c9761275b931.md)
Collectors:
- [Microsoft 365 Audit (Office 365 Audit) - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/microsoft-audit-office/)
- [Microsoft Exchange Trace Logs](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-exchange-trace-logs/)
- [Microsoft Office 365 Audit Source](/docs/send-data/hosted-collectors/microsoft-source/ms-office-audit-source/)
- [Microsoft Graph Azure AD Reporting Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-azure-ad-reporting-source/)
- [Microsoft Graph Identity Protection Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-identity-protection-source/)
- [Microsoft Graph Security API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-security-api-source/)
Community app: [Sumo Logic Microsoft Defender for EndPoint](https://github.com/SumoLogic/sumologic-content/tree/master/Microsoft/Defender_4_EndPoint)
Webhook: [Webhook Connection for Microsoft Teams](/docs/alerts/webhook-connections/microsoft-teams/) | +|
}) | [Mimecast](https://www.mimecast.com/) | App: [Mimecast](/docs/integrations/saas-cloud/mimecast/)
| [Mimecast](https://www.mimecast.com/) | App: [Mimecast](/docs/integrations/saas-cloud/mimecast/) Automation integration: [Mimecast](/docs/platform-services/automation-service/app-central/integrations/mimecast/)
Cloud SIEM integration: [Mimecast](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/7BC43DFE-C5DD-4766-88E7-C163D82BBBF8.md)
Collector: [Mimecast Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/mimecast-source/)
Partner integration: [Mimecast app for Sumo Logic](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Mimecast) | +|
}) | [Miro](https://miro.com/) | App: [Miro](/docs/integrations/saas-cloud/miro/)
| [Miro](https://miro.com/) | App: [Miro](/docs/integrations/saas-cloud/miro/) Cloud SIEM integration: [Miro](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9f149da1-2831-465f-8bb1-a5950ccaec0c.md)
Collector: [Miro Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/miro-source/) | +|
}) | [MISP](https://www.misp-project.org/) | Automation integration: [MISP](/docs/platform-services/automation-service/app-central/integrations/misp/)
| [MISP](https://www.misp-project.org/) | Automation integration: [MISP](/docs/platform-services/automation-service/app-central/integrations/misp/)Community app: [Sumo Logic for MISP](https://github.com/SumoLogic/sumologic-content/tree/master/MISP) | +|
}) | [MITRE ATT&CK](https://attack.mitre.org/) | Automation integration: [Mitre Matrix](/docs/platform-services/automation-service/app-central/integrations/mitre-matrix/) |
+|
| [MITRE ATT&CK](https://attack.mitre.org/) | Automation integration: [Mitre Matrix](/docs/platform-services/automation-service/app-central/integrations/mitre-matrix/) |
+| }) | [MongoDB](https://www.mongodb.com/) | Apps:
| [MongoDB](https://www.mongodb.com/) | Apps: - [MongoDB](/docs/integrations/databases/mongodb/)
- [MongoDB - OpenTelementry](/docs/integrations/databases/opentelemetry/mongodb-opentelemetry/) | +|
}) | [MongoDB Atlas](https://www.mongodb.com/atlas) | App: [MongoDB Atlas](/docs/integrations/databases/mongodb-atlas/) |
+|
| [MongoDB Atlas](https://www.mongodb.com/atlas) | App: [MongoDB Atlas](/docs/integrations/databases/mongodb-atlas/) |
+| }) | [mParticle](https://www.mparticle.com/) | Webhook: [mParticle](/docs/integrations/webhooks/mparticle/) |
+|
| [mParticle](https://www.mparticle.com/) | Webhook: [mParticle](/docs/integrations/webhooks/mparticle/) |
+| }) | [MxToolbox](https://mxtoolbox.com/) | Automation integration: [MxToolbox](/docs/platform-services/automation-service/app-central/integrations/mxtoolbox/) |
+|
| [MxToolbox](https://mxtoolbox.com/) | Automation integration: [MxToolbox](/docs/platform-services/automation-service/app-central/integrations/mxtoolbox/) |
+| }) | [MySQL](https://www.mysql.com/) | Apps:
| [MySQL](https://www.mysql.com/) | Apps: - [MySQL](/docs/integrations/databases/mysql/)
- [MySQL - OpenTelemetry](/docs/integrations/databases/opentelemetry/mysql-opentelemetry/) | + +## N + +| Logo | Vendors and Products | Integrations | +| :-- | :-- | :-- | +|
}) | [Netlify](https://www.netlify.com/) | Webhook: [Netlify](/docs/integrations/webhooks/netlify/) |
+|
| [Netlify](https://www.netlify.com/) | Webhook: [Netlify](/docs/integrations/webhooks/netlify/) |
+| }) | [NETSCOUT](https://www.netscout.com/) | Automation integration: [Arbor (NETSCOUT)](/docs/platform-services/automation-service/app-central/integrations/arbor/) |
+|
| [NETSCOUT](https://www.netscout.com/) | Automation integration: [Arbor (NETSCOUT)](/docs/platform-services/automation-service/app-central/integrations/arbor/) |
+| }) | [Netskope](https://www.netskope.com/) | Apps:
| [Netskope](https://www.netskope.com/) | Apps: - [Netskope](/docs/integrations/security-threat-detection/netskope/)
- [Netskope Legacy](/docs/integrations/security-threat-detection/netskope-legacy-collection/)
Automation integrations:
- [Netskope](/docs/platform-services/automation-service/app-central/integrations/netskope/)
- [Netskope V2](/docs/platform-services/automation-service/app-central/integrations/netskope-v2/)
Cloud SIEM integration: [Netskope](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/E9BF4F45-AB91-40F6-9EA0-21B48D69FF1F.md)
Collectors:
- [Netskope Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/netskope-source/)
- [Netskope WebTx Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/netskope-webtx-source/) | +|
}) | [Neustar](https://www.home.neustar/) | Automation integration: [Neustar IP GeoPoint](/docs/platform-services/automation-service/app-central/integrations/neustar-ip-geopoint/) |
+|
| [Neustar](https://www.home.neustar/) | Automation integration: [Neustar IP GeoPoint](/docs/platform-services/automation-service/app-central/integrations/neustar-ip-geopoint/) |
+| }) | [New Relic](https://newrelic.com/) | Webhook: [Webhook Connection for New Relic](/docs/alerts/webhook-connections/new-relic/) |
+|
| [New Relic](https://newrelic.com/) | Webhook: [Webhook Connection for New Relic](/docs/alerts/webhook-connections/new-relic/) |
+| }) | [Nmap](https://nmap.org/) | Automation integration: [Nmap](/docs/platform-services/automation-service/app-central/integrations/nmap/) |
+|
| [Nmap](https://nmap.org/) | Automation integration: [Nmap](/docs/platform-services/automation-service/app-central/integrations/nmap/) |
+| }) | [Nobl9](https://www.nobl9.com/) | Webhook: [Nobl9](/docs/integrations/webhooks/nobl9/) |
+|
| [Nobl9](https://www.nobl9.com/) | Webhook: [Nobl9](/docs/integrations/webhooks/nobl9/) |
+| }) | [Nozomi Networks](https://www.nozominetworks.com/) | Automation integration: [Nozomi Networks](/docs/platform-services/automation-service/app-central/integrations/nozomi-networks/) |
+|
| [Nozomi Networks](https://www.nozominetworks.com/) | Automation integration: [Nozomi Networks](/docs/platform-services/automation-service/app-central/integrations/nozomi-networks/) |
+| }) | [Nucleon](https://nucleoncyber.com/) | Automation integration: [Nucleon Cyber](/docs/platform-services/automation-service/app-central/integrations/nucleon-cyber/)
| [Nucleon](https://nucleoncyber.com/) | Automation integration: [Nucleon Cyber](/docs/platform-services/automation-service/app-central/integrations/nucleon-cyber/) Partner integration: [Nucleon](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Nucleon) | +|
}) | [NXLog](https://nxlog.co/) | Partner integration: [NXLog](https://nxlog.co/technology-ecosystem) |
+
+## O
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+|
| [NXLog](https://nxlog.co/) | Partner integration: [NXLog](https://nxlog.co/technology-ecosystem) |
+
+## O
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+| }) | [Observable Networks](https://www.cisco.com/c/en/us/services/acquisitions/observable-networks.html) | App: [Observable Networks](/docs/integrations/security-threat-detection/observable-networks/) |
+|
| [Observable Networks](https://www.cisco.com/c/en/us/services/acquisitions/observable-networks.html) | App: [Observable Networks](/docs/integrations/security-threat-detection/observable-networks/) |
+| }) | [OISF](https://oisf.net/) | Cloud SIEM integration: [OISF](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9c138edd-dc14-43a6-b751-52e41a8bd105.md) |
+|
| [OISF](https://oisf.net/) | Cloud SIEM integration: [OISF](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9c138edd-dc14-43a6-b751-52e41a8bd105.md) |
+| }) | [Okta](https://www.okta.com/) | App: [Okta](/docs/integrations/saml/okta/)
| [Okta](https://www.okta.com/) | App: [Okta](/docs/integrations/saml/okta/) Automation integration: [Okta](/docs/platform-services/automation-service/app-central/integrations/okta/)
Cloud SIEM integration: [Okta](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/d8d14556-180c-4463-90da-d8b8600f7362.md)
Collectors:
- [Okta Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/okta-source/)
- [Okta - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/okta/) | +|
}) | [OneLogin](https://www.onelogin.com/) | App: [OneLogin](/docs/integrations/saml/onelogin/)
| [OneLogin](https://www.onelogin.com/) | App: [OneLogin](/docs/integrations/saml/onelogin/) Automation integration: [OneLogin](/docs/platform-services/automation-service/app-central/integrations/onelogin/)
Cloud SIEM integration: [OneLogin](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/e34a3430-613f-47c0-9ddd-a320bc3e5c4d.md)
Collector: [OneLogin - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/onelogin/) | +|
}) | [1Password](https://1password.com/) | App: [1Password](/docs/integrations/1password/)
| [1Password](https://1password.com/) | App: [1Password](/docs/integrations/1password/) Cloud SIEM integration: [1Password](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/d0455ea1-e901-4999-b047-0533d16adfdc.md)
Collector: [1Password Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/1password-source/) | +|
}) | [OneTrust](https://www.onetrust.com/) | Automation integration: [OneTrust](/docs/platform-services/automation-service/app-central/integrations/onetrust/) |
+|
| [OneTrust](https://www.onetrust.com/) | Automation integration: [OneTrust](/docs/platform-services/automation-service/app-central/integrations/onetrust/) |
+| }) | [OpenAI](https://openai.com/) | Automation integration: [OpenAI ChatGPT](/docs/platform-services/automation-service/app-central/integrations/openai-chatgpt/) |
+|
| [OpenAI](https://openai.com/) | Automation integration: [OpenAI ChatGPT](/docs/platform-services/automation-service/app-central/integrations/openai-chatgpt/) |
+| }) | [OpenLDAP](https://www.openldap.org/) | Automation integration: [OpenLDAP](/docs/platform-services/automation-service/app-central/integrations/openldap/) |
+|
| [OpenLDAP](https://www.openldap.org/) | Automation integration: [OpenLDAP](/docs/platform-services/automation-service/app-central/integrations/openldap/) |
+| }) | [OpenSSH](https://www.openssh.com/) | Cloud SIEM integration: [OpenSSH](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/d0bf0b9f-162e-4d1e-9b89-38e8d526a434.md) |
+|
| [OpenSSH](https://www.openssh.com/) | Cloud SIEM integration: [OpenSSH](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/d0bf0b9f-162e-4d1e-9b89-38e8d526a434.md) |
+| }) | [OpenText](https://www.opentext.com/) | Automation integrations:
| [OpenText](https://www.opentext.com/) | Automation integrations: - [Arcsight ESM](/docs/platform-services/automation-service/app-central/integrations/arcsight-esm/)
- [Arcsight Logger](/docs/platform-services/automation-service/app-central/integrations/arcsight-logger/)
- [HP Universal CMDB](/docs/platform-services/automation-service/app-central/integrations/hp-universal-cmdb/)
- [Micro Focus Service Management](/docs/platform-services/automation-service/app-central/integrations/micro-focus-service-management/)
- [OpenText EnCase Endpoint Security](/docs/platform-services/automation-service/app-central/integrations/opentext-encase-endpoint-security/)
Cloud SIEM integration: [Micro Focus](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/23850303-a1da-4c95-83f1-bd9d3b5104b8.md) | +|
}) | [OpenVPN](https://openvpn.net/) | Cloud SIEM integration: [OpenVPN](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/8e5a85b3-a95e-47d9-adcf-bb543e6580c0.md) |
+|
| [OpenVPN](https://openvpn.net/) | Cloud SIEM integration: [OpenVPN](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/8e5a85b3-a95e-47d9-adcf-bb543e6580c0.md) |
+| }) | [Opsgenie](https://www.atlassian.com/software/opsgenie) | App: [Opsgenie](/docs/integrations/saas-cloud/opsgenie/)
| [Opsgenie](https://www.atlassian.com/software/opsgenie) | App: [Opsgenie](/docs/integrations/saas-cloud/opsgenie/)Automation integration: [Atlassian Opsgenie](/docs/platform-services/automation-service/app-central/integrations/atlassian-opsgenie/)
Webhooks:
- [Webhook Connection for Opsgenie](/docs/alerts/webhook-connections/opsgenie/)
- [Webhook Connection for Opsgenie (Legacy)](/docs/alerts/webhook-connections/opsgenie-legacy/) | +|
}) | [OpsRamp](https://www.opsramp.com/) | Partner integration: [OpsRamp](https://docs.opsramp.com/integrations/a2r/3rd-party/sumologic/) |
+|
| [OpsRamp](https://www.opsramp.com/) | Partner integration: [OpsRamp](https://docs.opsramp.com/integrations/a2r/3rd-party/sumologic/) |
+| }) | [Opswat](https://www.opswat.com/) | Automation integration: [Opswat Metadefender](/docs/platform-services/automation-service/app-central/integrations/opswat-metadefender/) |
+|
| [Opswat](https://www.opswat.com/) | Automation integration: [Opswat Metadefender](/docs/platform-services/automation-service/app-central/integrations/opswat-metadefender/) |
+| }) | [Oracle Database](https://www.oracle.com/database/) | Apps:
| [Oracle Database](https://www.oracle.com/database/) | Apps: - [Oracle](/docs/integrations/databases/oracle/)
- [Oracle - OpenTelemetry](/docs/integrations/databases/opentelemetry/oracle-opentelemetry/)
Collector: [Collect Logs from Oracle Cloud Infrastructure](/docs/send-data/collect-from-other-data-sources/collect-logs-oracle-cloud-infrastructure/) | +|
}) | [Orca Security](https://orca.security/) | Cloud SIEM integration: [Orca Security](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/ab5b4909-20f7-4cf7-b8de-24f4a5b2ba57.md) |
+|
| [Orca Security](https://orca.security/) | Cloud SIEM integration: [Orca Security](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/ab5b4909-20f7-4cf7-b8de-24f4a5b2ba57.md) |
+| }) | [osquery](https://osquery.io/) | Cloud SIEM integration: [Osquery](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/eca511e4-0daa-41f7-919e-ec4d0ac1558f.md)
| [osquery](https://osquery.io/) | Cloud SIEM integration: [Osquery](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/eca511e4-0daa-41f7-919e-ec4d0ac1558f.md) Collector: [Osquery - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/osquery/) | +|
}) | [Ossec](https://www.ossec.net/) | Cloud SIEM integration: [Ossec](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/1eceb40f-85d7-45ea-b341-864a38ea0775.md) |
+
+## P
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+|
| [Ossec](https://www.ossec.net/) | Cloud SIEM integration: [Ossec](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/1eceb40f-85d7-45ea-b341-864a38ea0775.md) |
+
+## P
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+| }) | [PagerDuty](https://www.pagerduty.com/) | Apps:
| [PagerDuty](https://www.pagerduty.com/) | Apps: - [PagerDuty V2](/docs/integrations/saas-cloud/pagerduty-v2/)
- [PagerDuty V3](/docs/integrations/saas-cloud/pagerduty-v3/)
Automation integration: [PagerDuty](/docs/platform-services/automation-service/app-central/integrations/pagerduty/)
Webhook: [Webhook Connection for PagerDuty](/docs/alerts/webhook-connections/pagerduty/) | +|
}) | [Palo Alto Networks](https://www.paloaltonetworks.com/) | Apps:
| [Palo Alto Networks](https://www.paloaltonetworks.com/) | Apps: - [Evident.io ESP](/docs/integrations/security-threat-detection/evident-security-platform/)
- [Palo Alto Firewall 9](/docs/integrations/cloud-security-monitoring-analytics/palo-alto-firewall-9/)
- [Palo Alto Firewall 10](/docs/integrations/cloud-security-monitoring-analytics/palo-alto-firewall-10/)
- [Palo Alto Networks 9](/docs/integrations/security-threat-detection/palo-alto-networks-9/)
- [PCI Compliance for Palo Alto Networks 9](/docs/integrations/pci-compliance/palo-alto-networks-9/)
- [PCI Compliance for Palo Alto Networks 10](/docs/integrations/pci-compliance/palo-alto-networks-10/)
- [Palo Alto Cortex XDR](/docs/integrations/saas-cloud/palo-alto-cortex-xdr/)
- [Twistlock](/docs/integrations/security-threat-detection/twistlock/)
Automation integrations:
- [Cortex XDR](/docs/platform-services/automation-service/app-central/integrations/cortex-xdr/)
- [Palo Alto AutoFocus](/docs/platform-services/automation-service/app-central/integrations/palo-alto-autofocus/)
- [Palo Alto Networks NGFW](/docs/platform-services/automation-service/app-central/integrations/palo-alto-networks-ngfw/)
- [Palo Alto Networks Panorama V2](/docs/platform-services/automation-service/app-central/integrations/palo-alto-networks-panorama-v2/)
- [Prisma Cloud](/docs/platform-services/automation-service/app-central/integrations/prisma-cloud/)
Cloud SIEM integrations:
- [Demisto](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/C279B799-AD59-4B49-9582-5F9FD106079F.md)
- [Palo Alto Networks](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/938210de-ab6c-46fb-89d7-8530682581c6.md)
- [Redlock](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/94c035a7-d8ba-4c66-bda6-2fe19db458d6.md)
- [Twistlock](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/97C36046-B516-41F8-9751-4C788AA33785.md)
Collectors:
- [Collect Logs from Palo Alto Networks Cortex Data Lake](/docs/send-data/collect-from-other-data-sources/collect-logs-palo-alto-networks-cortex/)
- [Palo Alto Cortex XDR Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/palo-alto-cortex-xdr-source/)
- [Palo Alto Firewall - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/palo-alto-firewall/)
Community app: [Sumo Logic for Palo Alto Cortex XDR](https://github.com/SumoLogic/sumologic-content/tree/master/Palo_Alto_Networks/Cortex_XDR)
Partner integration: [Cortex XSOAR](https://xsoar.pan.dev/docs/reference/integrations/sumo-logic) | +|
}) | [PaperTrail](https://www.papertrail.com/) | Webhook: [PaperTrail](/docs/integrations/webhooks/papertrail/) |
+|
| [PaperTrail](https://www.papertrail.com/) | Webhook: [PaperTrail](/docs/integrations/webhooks/papertrail/) |
+| }) | [Phantombuster](https://phantombuster.com/) | Automation integration: [Phantombuster](/docs/platform-services/automation-service/app-central/integrations/phantombuster/) |
+|
| [Phantombuster](https://phantombuster.com/) | Automation integration: [Phantombuster](/docs/platform-services/automation-service/app-central/integrations/phantombuster/) |
+| }) | [PhishTank](https://phishtank.org/) | Automation integration: [PhishTank](/docs/platform-services/automation-service/app-central/integrations/phishtank/) |
+|
| [PhishTank](https://phishtank.org/) | Automation integration: [PhishTank](/docs/platform-services/automation-service/app-central/integrations/phishtank/) |
+| }) | [PostgreSQL](https://www.postgresql.org/) | Apps:
| [PostgreSQL](https://www.postgresql.org/) | Apps: - [PostgreSQL](/docs/integrations/databases/postgresql/)
- [PostgreSQL - OpenTelemetry](/docs/integrations/databases/opentelemetry/postgresql-opentelemetry/) | +|
}) | [Postman](https://www.postman.com/) | Webhook: [Postman](/docs/integrations/webhooks/postman/) |
+|
| [Postman](https://www.postman.com/) | Webhook: [Postman](/docs/integrations/webhooks/postman/) |
+| }) | [Pritunl](https://pritunl.com/) | Cloud SIEM integration: [Pritunl](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/598b6820-feff-4169-89da-77211493a91d.md) |
+|
| [Pritunl](https://pritunl.com/) | Cloud SIEM integration: [Pritunl](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/598b6820-feff-4169-89da-77211493a91d.md) |
+| }) | [Prometheus](https://prometheus.io/) | Collector: [Collect Prometheus Metrics](/docs/send-data/collect-from-other-data-sources/collect-prometheus-metrics/) |
+|
| [Prometheus](https://prometheus.io/) | Collector: [Collect Prometheus Metrics](/docs/send-data/collect-from-other-data-sources/collect-prometheus-metrics/) |
+| }) | [Proofpoint](https://www.proofpoint.com/us) | Apps:
| [Proofpoint](https://www.proofpoint.com/us) | Apps: - [Proofpoint on Demand](/docs/integrations/saas-cloud/proofpoint-on-demand/)
- [Proofpoint TAP](/docs/integrations/saas-cloud/proofpoint-tap/)
Automation integration: [Proofpoint TAP](/docs/platform-services/automation-service/app-central/integrations/proofpoint-tap/)
Cloud SIEM integrations:
- [ObserveIT](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/BBBEB05C-6CFE-4BF8-8AA6-73CD73DF2464.md)
- [Proofpoint](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/e0bbbae5-9a03-48f4-b138-9c3b49522f1a.md)
Collectors:
- [Proofpoint On Demand Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/proofpoint-on-demand-source/)
- [Proofpoint TAP Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/proofpoint-tap-source/)
Community app: [Sumo Logic for Proofpoint TAP](https://github.com/SumoLogic/sumologic-content/tree/master/Proofpoint/Proofpoint_TAP) | +|
}) | [ProtectOnce](https://protectonce.com/) | Automation integration: [ProtectOnce](/docs/platform-services/automation-service/app-central/integrations/protectonce/) |
+|
| [ProtectOnce](https://protectonce.com/) | Automation integration: [ProtectOnce](/docs/platform-services/automation-service/app-central/integrations/protectonce/) |
+| }) | [Pulsedive](https://pulsedive.com/) | Automation integration: [Pulsedive](/docs/platform-services/automation-service/app-central/integrations/pulsedive/) |
+|
| [Pulsedive](https://pulsedive.com/) | Automation integration: [Pulsedive](/docs/platform-services/automation-service/app-central/integrations/pulsedive/) |
+| }) | [Puppet](https://www.puppet.com/) | Apps:
| [Puppet](https://www.puppet.com/) | Apps: - [Puppet](/docs/integrations/app-development/puppet/)
- [Puppet - OpenTelemetry](/docs/integrations/app-development/opentelemetry/puppet-opentelemetry/)
Collector: [Install OpenTelemetry Collector on Puppet](/docs/send-data/opentelemetry-collector/install-collector/puppet/) | +|
}) | [Pusher](https://pusher.com/) | Webhook: [Pusher](/docs/integrations/webhooks/pusher/) |
+
+## Q
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+|
| [Pusher](https://pusher.com/) | Webhook: [Pusher](/docs/integrations/webhooks/pusher/) |
+
+## Q
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+| Automation integrations:
- [Qualys](/docs/platform-services/automation-service/app-central/integrations/qualys/)
- [Qualys EDR](/docs/platform-services/automation-service/app-central/integrations/qualys-edr/)
- [Qualys WAS](/docs/platform-services/automation-service/app-central/integrations/qualys-was/)
Cloud SIEM integration: [Qualys](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/fb83d074-c6cf-4fc7-9020-5d3e364acd17.md)
Collector: [Qualys VMDR Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/qualys-vmdr-source/)
Community app: [Sumo Logic for Qualys VMDR and Inventory](https://github.com/SumoLogic/sumologic-content/tree/master/Qualys) | + +## R + +| Logo | Vendors and Products | Integrations | +| :-- | :-- | :-- | +|
}) | [RabbitMQ](https://www.rabbitmq.com/) | Apps:
| [RabbitMQ](https://www.rabbitmq.com/) | Apps: - [RabbitMQ](/docs/integrations/containers-orchestration/rabbitmq/)
- [RabbitMQ - OpenTelemetry](/docs/integrations/containers-orchestration/opentelemetry/rabbitmq-opentelemetry/) | +|
}) | [Rapid7](https://www.rapid7.com/) | App: [Rapid7](/docs/integrations/saas-cloud/rapid7/)
| [Rapid7](https://www.rapid7.com/) | App: [Rapid7](/docs/integrations/saas-cloud/rapid7/) Automation integrations:
- [Rapid 7 InsightVM](/docs/platform-services/automation-service/app-central/integrations/rapid-7-insightvm/)
- [Rapid7 Nexpose](/docs/platform-services/automation-service/app-central/integrations/rapid7-nexpose/) | +|
}) | [RapidAPI](https://rapidapi.com/) | Automation integration: [RapidAPI](/docs/platform-services/automation-service/app-central/integrations/rapidapi/) |
+|
| [RapidAPI](https://rapidapi.com/) | Automation integration: [RapidAPI](/docs/platform-services/automation-service/app-central/integrations/rapidapi/) |
+| }) | [Recorded Future](https://www.recordedfuture.com/) | Automation integration: [Recorded Future](/docs/platform-services/automation-service/app-central/integrations/recorded-future/) |
+|
| [Recorded Future](https://www.recordedfuture.com/) | Automation integration: [Recorded Future](/docs/platform-services/automation-service/app-central/integrations/recorded-future/) |
+| }) | [Red Hat OpenShift](https://www.redhat.com/en/technologies/cloud-computing/openshift) | Partner integration: [Red Hat OpenShift](https://docs.openshift.com/acs/3.74/integration/integrate-with-sumologic.html)
| [Red Hat OpenShift](https://www.redhat.com/en/technologies/cloud-computing/openshift) | Partner integration: [Red Hat OpenShift](https://docs.openshift.com/acs/3.74/integration/integrate-with-sumologic.html) Collector: [Rapid7 Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/rapid7-source/) | +|
}) | [Redis](https://redis.io/) | Apps:
| [Redis](https://redis.io/) | Apps: - [Redis](/docs/integrations/databases/redis/)
- [Redis - OpenTelemetry](/docs/integrations/databases/opentelemetry/redis-opentelemetry/) | +|
}) | [RiskIQ](https://community.riskiq.com/) | Automation integration: [Passive Total](/docs/platform-services/automation-service/app-central/integrations/passive-total/) |
+|
| [RiskIQ](https://community.riskiq.com/) | Automation integration: [Passive Total](/docs/platform-services/automation-service/app-central/integrations/passive-total/) |
+| }) | [Rollbar](https://rollbar.com/) | Webhook: [Rollbar](/docs/integrations/webhooks/rollbar/) |
+|
| [Rollbar](https://rollbar.com/) | Webhook: [Rollbar](/docs/integrations/webhooks/rollbar/) |
+| }) | [RSA](https://www.rsa.com/) | Automation integrations:
| [RSA](https://www.rsa.com/) | Automation integrations: - [RSA NetWitness Logs](/docs/platform-services/automation-service/app-central/integrations/rsa-netwitness-logs/)
- [RSA NetWitness](/docs/platform-services/automation-service/app-central/integrations/rsa-netwitness/)
Cloud SIEM integration: [RSA](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/8c02f96f-60b2-48d6-bfe6-1605adaf4d51.md) | +|
}) | [rsyslog](https://www.rsyslog.com/) | Collector: [rsyslog](/docs/send-data/hosted-collectors/cloud-syslog-source/rsyslog/) |
+|
| [rsyslog](https://www.rsyslog.com/) | Collector: [rsyslog](/docs/send-data/hosted-collectors/cloud-syslog-source/rsyslog/) |
+| }) | [Ruby on Rails](https://rubyonrails.org/) | Collector: [Collect Ruby on Rails Logs](/docs/send-data/collect-from-other-data-sources/collect-ruby-on-rails-logs/) |
+
+
+## S
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+|
| [Ruby on Rails](https://rubyonrails.org/) | Collector: [Collect Ruby on Rails Logs](/docs/send-data/collect-from-other-data-sources/collect-ruby-on-rails-logs/) |
+
+
+## S
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+| Automation integration: [SailPoint](/docs/platform-services/automation-service/app-central/integrations/sailpoint/)
Cloud SIEM integration: [SailPoint](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/965fe719-5d9f-4100-b0b6-684191925884.md)
Collector: [SailPoint Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/sailpoint-source/) | +|
Automation integration: [Salesforce](/docs/platform-services/automation-service/app-central/integrations/salesforce/)
Cloud SIEM integration: [Salesforce](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/02cab927-d7d7-4be6-bd59-18522f741544.md)
Collector: [Salesforce Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/salesforce-source/) | +|
}) | [Sauce Labs](https://saucelabs.com/) | Partner integration: [Sauce Labs](https://docs.saucelabs.com/basics/integrations/sumo/) |
+|
| [Sauce Labs](https://saucelabs.com/) | Partner integration: [Sauce Labs](https://docs.saucelabs.com/basics/integrations/sumo/) |
+| }) | [Screenshot Machine](https://www.screenshotmachine.com/) | Automation integration: [Screenshot Machine](/docs/platform-services/automation-service/app-central/integrations/screenshot-machine/) |
+|
| [Screenshot Machine](https://www.screenshotmachine.com/) | Automation integration: [Screenshot Machine](/docs/platform-services/automation-service/app-central/integrations/screenshot-machine/) |
+| }) | [SecureAuth](https://www.secureauth.com/) | Cloud SIEM integration: [SecureAuth](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/72744d1c-ddff-4ead-b76e-60430704f945.md) |
+|
| [SecureAuth](https://www.secureauth.com/) | Cloud SIEM integration: [SecureAuth](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/72744d1c-ddff-4ead-b76e-60430704f945.md) |
+| }) | [Security Scorecard](https://securityscorecard.com/) | Automation integration: [Security Scorecard](/docs/platform-services/automation-service/app-central/integrations/security-scorecard/) |
+|
| [Security Scorecard](https://securityscorecard.com/) | Automation integration: [Security Scorecard](/docs/platform-services/automation-service/app-central/integrations/security-scorecard/) |
+| }) | [SecurityTrails](https://securitytrails.com/) | Automation integration: [SecurityTrails](/docs/platform-services/automation-service/app-central/integrations/securitytrails/) |
+|
| [SecurityTrails](https://securitytrails.com/) | Automation integration: [SecurityTrails](/docs/platform-services/automation-service/app-central/integrations/securitytrails/) |
+| }) | [Securonix](https://www.securonix.com/) | Automation integrations:
| [Securonix](https://www.securonix.com/) | Automation integrations: - [Securonix](/docs/platform-services/automation-service/app-central/integrations/securonix/)
- [Securonix V2](/docs/platform-services/automation-service/app-central/integrations/securonix-v2/) | +|
}) | [SendGrid](https://sendgrid.com/) | Webhook: [SendGrid](/docs/integrations/webhooks/sendgrid/) |
+|
| [SendGrid](https://sendgrid.com/) | Webhook: [SendGrid](/docs/integrations/webhooks/sendgrid/) |
+| Automation integration: [SentinelOne](/docs/platform-services/automation-service/app-central/integrations/sentinelone/)
Cloud SIEM integration: [SentinelOne](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/20617100-01e3-409a-8918-fd665fc31c88.md)
Collectors:
- [Collect Logs for SentinelOne](/docs/send-data/collect-from-other-data-sources/collect-logs-sentinelone/)
- [SentinelOne Mgmt API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/sentinelone-mgmt-api-source/)
- [SentinelOne - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/sentinelone/) | +|
}) | [Sensu](https://sensu.io/) | Partner integration: [Send data to Sumo Logic with Sensu](https://docs.sensu.io/sensu-go/latest/observability-pipeline/observe-process/send-data-sumo-logic/) |
+|
| [Sensu](https://sensu.io/) | Partner integration: [Send data to Sumo Logic with Sensu](https://docs.sensu.io/sensu-go/latest/observability-pipeline/observe-process/send-data-sumo-logic/) |
+| }) | [SIGNL4](https://www.signl4.com/) | Webhooks:
| [SIGNL4](https://www.signl4.com/) | Webhooks: - [SIGNL4](/docs/integrations/webhooks/signl4/)
- [Webhook Connection for SIGNL4](/docs/alerts/webhook-connections/signl4/) | +|
}) | [Sentry](https://sentry.io/welcome/) | Webhook: [Sentry](/docs/integrations/webhooks/sentry/) |
+|
| [Sentry](https://sentry.io/welcome/) | Webhook: [Sentry](/docs/integrations/webhooks/sentry/) |
+| }) | [ServiceNow](https://www.servicenow.com/) | Automation integration: [ServiceNow V2](/docs/platform-services/automation-service/app-central/integrations/servicenow-v2/)
| [ServiceNow](https://www.servicenow.com/) | Automation integration: [ServiceNow V2](/docs/platform-services/automation-service/app-central/integrations/servicenow-v2/) Webhook: [ServiceNow](/docs/alerts/webhook-connections/servicenow/) | +|
}) | [Shodan](https://www.shodan.io/) | Automation integration: [Shodan](/docs/platform-services/automation-service/app-central/integrations/shodan/) |
+|
| [Shodan](https://www.shodan.io/) | Automation integration: [Shodan](/docs/platform-services/automation-service/app-central/integrations/shodan/) |
+| }) | [Silent Push](https://www.silentpush.com/) | Automation integration: [Silent Push](/docs/platform-services/automation-service/app-central/integrations/silent-push) |
+|
| [Silent Push](https://www.silentpush.com/) | Automation integration: [Silent Push](/docs/platform-services/automation-service/app-central/integrations/silent-push) |
+| }) | [Slack](https://slack.com/) | App: [Slack](/docs/integrations/saas-cloud/slack/)
| [Slack](https://slack.com/) | App: [Slack](/docs/integrations/saas-cloud/slack/) Automation integration: [Slack](/docs/platform-services/automation-service/app-central/integrations/slack/)
Cloud SIEM integration: [Slack](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c93d9bf6-0a88-49fc-aebb-ac7b2ea6792c.md)
Collector: [Slack Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/slack-source/)
Webhook: [Webhook Connection for Slack](/docs/alerts/webhook-connections/slack/) | +|
}) | [Snare](https://www.snaresolutions.com/) | Cloud SIEM integration: [Intersect Alliance](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/005c835d-f067-4147-9da9-fe4d2691247e.md) |
+|
| [Snare](https://www.snaresolutions.com/) | Cloud SIEM integration: [Intersect Alliance](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/005c835d-f067-4147-9da9-fe4d2691247e.md) |
+| }) | [Snowflake](https://www.snowflake.com/en/) | Cloud SIEM integration: [Snowflake](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/5541f59d-e27d-48e6-a35c-34fb75e9cf13.md) |
+|
| [Snowflake](https://www.snowflake.com/en/) | Cloud SIEM integration: [Snowflake](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/5541f59d-e27d-48e6-a35c-34fb75e9cf13.md) |
+| }) | [Snyk](https://snyk.io/) | Automation integration: [Snyk](/docs/platform-services/automation-service/app-central/integrations/snyk/) |
+|
| [Snyk](https://snyk.io/) | Automation integration: [Snyk](/docs/platform-services/automation-service/app-central/integrations/snyk/) |
+| }) | [SOCRadar](https://socradar.io/) | Automation integration: [SOCRadar](/docs/platform-services/automation-service/app-central/integrations/socradar/) |
+|
| [SOCRadar](https://socradar.io/) | Automation integration: [SOCRadar](/docs/platform-services/automation-service/app-central/integrations/socradar/) |
+| }) | [SonicWall](https://www.sonicwall.com/) | Automation integration: [SonicWall](/docs/platform-services/automation-service/app-central/integrations/sonicwall/) |
+|
| [SonicWall](https://www.sonicwall.com/) | Automation integration: [SonicWall](/docs/platform-services/automation-service/app-central/integrations/sonicwall/) |
+| }) | [Sophos](https://www.sophos.com/en-us) | Automation integrations:
| [Sophos](https://www.sophos.com/en-us) | Automation integrations: - [Sophos Central](/docs/platform-services/automation-service/app-central/integrations/sophos-central/)
- [Sophos Central V3](/docs/platform-services/automation-service/app-central/integrations/sophos-central-v3/)
Cloud SIEM integration: [Sophos](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/dc8564e3-6c44-463a-8bad-36618a688d57.md)
Collector: [Sophos Central Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/sophos-central-source/)
Community app: [Sumo Logic for Sophos Central](https://github.com/SumoLogic/sumologic-content/tree/master/Sophos/Sophos-Central) | +|
}) | [SpiderFoot HX](https://login.hx.spiderfoot.net/) | Automation integration: [SpiderFoot HX](/docs/platform-services/automation-service/app-central/integrations/spiderfoot-hx/) |
+|
| [SpiderFoot HX](https://login.hx.spiderfoot.net/) | Automation integration: [SpiderFoot HX](/docs/platform-services/automation-service/app-central/integrations/spiderfoot-hx/) |
+| }) | [Spinnaker](https://spinnaker.io/) | Partner integration: [Spinnaker](https://docs.armory.io/continuous-deployment/armory-admin/observe/integrations-sumologic/) |
+|
| [Spinnaker](https://spinnaker.io/) | Partner integration: [Spinnaker](https://docs.armory.io/continuous-deployment/armory-admin/observe/integrations-sumologic/) |
+| }) | [Split](https://www.split.io/) | Webhook: [Split](/docs/integrations/webhooks/split/) |
+|
| [Split](https://www.split.io/) | Webhook: [Split](/docs/integrations/webhooks/split/) |
+| }) | [Splunk](https://www.splunk.com/) | Automation integration: [Splunk](/docs/platform-services/automation-service/app-central/integrations/splunk/)
| [Splunk](https://www.splunk.com/) | Automation integration: [Splunk](/docs/platform-services/automation-service/app-central/integrations/splunk/) Collector: [Import Raw Data from Splunk](/docs/send-data/collect-from-other-data-sources/import-raw-data-splunk/) | +|
}) | [Squadcast](https://www.squadcast.com/) | Webhook: [Squadcast](/docs/integrations/webhooks/squadcast/) |
+|
| [Squadcast](https://www.squadcast.com/) | Webhook: [Squadcast](/docs/integrations/webhooks/squadcast/) |
+| }) | [Squid Cache](http://www.squid-cache.org/) | Apps:
| [Squid Cache](http://www.squid-cache.org/) | Apps: - [Squid Proxy](/docs/integrations/web-servers/squid-proxy/)
- [Squid Proxy - OpenTelemetry](/docs/integrations/web-servers/opentelemetry/squid-proxy-opentelemetry/)
Cloud SIEM integration: [Squid](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/470cb4ad-ac19-442b-9b3a-28b979d47d8e.md) | +|
}) | [StackRox](https://www.stackrox.io/) | Collector: [StackRox](https://cdn.stackrox.io/integrations/sumologic-stackrox-app.pdf)
| [StackRox](https://www.stackrox.io/) | Collector: [StackRox](https://cdn.stackrox.io/integrations/sumologic-stackrox-app.pdf) Partner integration: [StackRox app](https://cdn.stackrox.io/integrations/sumologic-stackrox-app.pdf) | +|
}) | [StatsD](https://www.datadoghq.com/blog/statsd/) | Collector: [Collect StatsD Metrics](/docs/send-data/collect-from-other-data-sources/collect-statsd-metrics/) |
+|
| [StatsD](https://www.datadoghq.com/blog/statsd/) | Collector: [Collect StatsD Metrics](/docs/send-data/collect-from-other-data-sources/collect-statsd-metrics/) |
+| }) | [Stellar Cyber](https://stellarcyber.ai/) | Automation integration: [Stellar Cyber Starlight](/docs/platform-services/automation-service/app-central/integrations/stellar-cyber-starlight/) |
+|
| [Stellar Cyber](https://stellarcyber.ai/) | Automation integration: [Stellar Cyber Starlight](/docs/platform-services/automation-service/app-central/integrations/stellar-cyber-starlight/) |
+| }) | [Strimzi](https://strimzi.io/) | App: [Strimzi Kafka](/docs/integrations/containers-orchestration/strimzi-kafka/) |
+|
| [Strimzi](https://strimzi.io/) | App: [Strimzi Kafka](/docs/integrations/containers-orchestration/strimzi-kafka/) |
+| }) | [Stripe](https://stripe.com/) | Webhook: [Stripe](/docs/integrations/webhooks/stripe/) |
+|
| [Stripe](https://stripe.com/) | Webhook: [Stripe](/docs/integrations/webhooks/stripe/) |
+| }) | [Sucuri](https://sucuri.net/) | Cloud SIEM integration: [Sucuri](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/cdfd2ba0-77eb-4e11-b071-6f4d01fda607.md) |
+|
| [Sucuri](https://sucuri.net/) | Cloud SIEM integration: [Sucuri](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/cdfd2ba0-77eb-4e11-b071-6f4d01fda607.md) |
+| }) | [Sumo Logic](https://www.sumologic.com/) | Apps:
| [Sumo Logic](https://www.sumologic.com/) | Apps: - [Enterprise Audit - Cloud SIEM](/docs/integrations/sumo-apps/cse/)
- [Sumo Logic Audit App](/docs/integrations/sumo-apps/audit/)
- [Sumo Logic Data Volume App](/docs/integrations/sumo-apps/data-volume/)
- [Sumo Logic Enterprise Audit Apps](/docs/integrations/sumo-apps/enterprise-audit/) (multiple apps)
- [Sumo Logic Enterprise Search Audit App](/docs/integrations/sumo-apps/enterprise-search-audit/)
- [Sumo Logic Infrequent Data Tier App](/docs/integrations/sumo-apps/infrequent-data-tier/)
- [Sumo Logic Log Analysis QuickStart App](/docs/integrations/sumo-apps/log-analysis-quickstart/)
- [Sumo Logic Security Analytics App](/docs/integrations/sumo-apps/security-analytics/)
Automation integrations:
- [Basic Tools](/docs/platform-services/automation-service/app-central/integrations/basic-tools/)
- [ESMTP](/docs/platform-services/automation-service/app-central/integrations/esmtp/)
- [HTTP Tools](/docs/platform-services/automation-service/app-central/integrations/http-tools/)
- [Incident Tools](/docs/platform-services/automation-service/app-central/integrations/incident-tools/)
- [IMAP](/docs/platform-services/automation-service/app-central/integrations/imap/)
- [Mail Tools](/docs/platform-services/automation-service/app-central/integrations/mail-tools/)
- [POP3](/docs/platform-services/automation-service/app-central/integrations/pop3/)
- [SMTP V3](/docs/platform-services/automation-service/app-central/integrations/smtp-v3/)
- [Sumo Logic Cloud SIEM](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-cloud-siem/)
- [Sumo Logic Cloud SIEM Internal](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-cloud-siem-internal/)
- [Sumo Logic Log Analytics](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-log-analytics/)
- [Sumo Logic Log Analytics Internal](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-log-analytics-internal/)
- [Sumo Logic Notifications](/docs/platform-services/automation-service/app-central/integrations/sumo-logic-notifications/)
- [Triage Tools](/docs/platform-services/automation-service/app-central/integrations/triage-tools/)
- [ZIP Tools](/docs/platform-services/automation-service/app-central/integrations/zip-tools/)
Cloud SIEM integration: [Sumo Logic](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/34A5019C-7BEC-4BF8-A3B7-C38D567126C6.md)
Community app: [Cloud Security Posture Management (CSPM) for Sumo Logic](https://github.com/SumoLogic/sumologic-content/tree/master/CSPM) | +|
}) | [Superwise](https://superwise.ai/) | Webhook: [Superwise](/docs/integrations/webhooks/superwise/) |
+|
| [Superwise](https://superwise.ai/) | Webhook: [Superwise](/docs/integrations/webhooks/superwise/) |
+| }) | [Symantec](https://sep.securitycloud.symantec.com/v2/landing) | App: [Symantec Web Security Service](/docs/integrations/saas-cloud/symantec-web-security-service/)
| [Symantec](https://sep.securitycloud.symantec.com/v2/landing) | App: [Symantec Web Security Service](/docs/integrations/saas-cloud/symantec-web-security-service/) Automation integrations:
- [Javelin AD Protect](/docs/platform-services/automation-service/app-central/integrations/javelin-ad-protect/)
- [Symantec DeepSight](/docs/platform-services/automation-service/app-central/integrations/symantec-deepsight/)
- [Symantec EDR](/docs/platform-services/automation-service/app-central/integrations/symantec-edr/)
- [Symantec Endpoint Protection](/docs/platform-services/automation-service/app-central/integrations/symantec-endpoint-protection/)
- [Symantec Endpoint Protection Cloud](/docs/platform-services/automation-service/app-central/integrations/symantec-endpoint-protection-cloud/)
- [Symantec Secure Web Gateway (Bluecoat)](/docs/platform-services/automation-service/app-central/integrations/symantec-secure-web-gateway-bluecoat/)
- [Symantec WebPulse](/docs/platform-services/automation-service/app-central/integrations/symantec-webpulse/)
Collectors:
- [Symantec Web Security Service Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/symantec-web-security-service-source/)
- [Symantec Proxy Secure Gateway - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/symantec-proxy-secure-gateway/)
- [Symantec Proxy Secure Gateway (Blue Coat Proxy) - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/symantec-proxy-secure-gateway-blue-coat-proxy/)
Cloud SIEM integration: [Symantec](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/64c7f49c-f95a-4f4a-8540-56ec5fb1d96b.md)
Community app: [Sumo Logic for Symantec WSS](https://github.com/SumoLogic/sumologic-content/tree/master/Symantec/WSS) | +|
}) | [Sysdig](https://sysdig.com/) | Cloud SIEM integration: [Sysdig](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c4de0854-e718-45e1-a4c8-63623755aa43.md) |
+|
| [Sysdig](https://sysdig.com/) | Cloud SIEM integration: [Sysdig](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c4de0854-e718-45e1-a4c8-63623755aa43.md) |
+| }) | [syslog-ng](https://www.syslog-ng.com/) | Automation integration: [Syslog-NG](/docs/platform-services/automation-service/app-central/integrations/syslog-ng/)
| [syslog-ng](https://www.syslog-ng.com/) | Automation integration: [Syslog-NG](/docs/platform-services/automation-service/app-central/integrations/syslog-ng/) Collector: [syslog-ng](/docs/send-data/hosted-collectors/cloud-syslog-source/syslog-ng/) | + +## T + +| Logo | Vendors and Products | Integrations | +| :-- | :-- | :-- | +|
}) | [Tanium](https://www.tanium.com/) | Cloud SIEM integration: [Tanium](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c7a342e6-5621-401a-ac5c-80ea3f2db23c.md)
| [Tanium](https://www.tanium.com/) | Cloud SIEM integration: [Tanium](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c7a342e6-5621-401a-ac5c-80ea3f2db23c.md) Collector: [Tanium](https://community.tanium.com/s/article/How-can-I-send-Tanium-data-to-Sumo-Logic) | +|
}) | [Telegraf](https://www.influxdata.com/time-series-platform/telegraf/) | Collector: [Telegraf](/docs/send-data/collect-from-other-data-sources/collect-metrics-telegraf/) |
+|
| [Telegraf](https://www.influxdata.com/time-series-platform/telegraf/) | Collector: [Telegraf](/docs/send-data/collect-from-other-data-sources/collect-metrics-telegraf/) |
+| }) | [Telegram](https://telegram.org/) | Automation integration: [Telegram V2](/docs/platform-services/automation-service/app-central/integrations/telegram-v2/) |
+|
| [Telegram](https://telegram.org/) | Automation integration: [Telegram V2](/docs/platform-services/automation-service/app-central/integrations/telegram-v2/) |
+| }) | [Tenable](https://www.tenable.com/) | App: [Tenable](/docs/integrations/saas-cloud/tenable/)
| [Tenable](https://www.tenable.com/) | App: [Tenable](/docs/integrations/saas-cloud/tenable/) Automation integrations:
- [Tenable.io](/docs/platform-services/automation-service/app-central/integrations/tenable.io/)
- [Tenable.sc](/docs/platform-services/automation-service/app-central/integrations/tenable.sc/)
Cloud SIEM integration: [Tenable](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/600BEF8F-BE81-4767-8322-72116C16DB20.md)
Collector: [Tenable Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/tenable-source/)
Community app: [Sumo Logic for Tenable IO](https://github.com/SumoLogic/sumologic-content/tree/master/Tenable/Tenable_IO) | +|
}) | [Tessian](https://www.tessian.com/) | Partner integration: [Tessian for Sumo Logic](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Tessian#tessian-for-sumo-logic) |
+|
| [Tessian](https://www.tessian.com/) | Partner integration: [Tessian for Sumo Logic](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Tessian#tessian-for-sumo-logic) |
+| }) | [TheHive](https://thehive-project.org/) | Automation integration: [TheHive](/docs/platform-services/automation-service/app-central/integrations/thehive/) |
+|
| [TheHive](https://thehive-project.org/) | Automation integration: [TheHive](/docs/platform-services/automation-service/app-central/integrations/thehive/) |
+| }) | [Thinkst Canary](https://canary.tools/) | Cloud SIEM integration: [Thinkst Canary](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/0152e233-fce6-4cbf-9edc-721d7bef94f8.md) |
+|
| [Thinkst Canary](https://canary.tools/) | Cloud SIEM integration: [Thinkst Canary](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/0152e233-fce6-4cbf-9edc-721d7bef94f8.md) |
+| }) | [ThreatConnect](https://threatconnect.com/) | Automation integration: [ThreatConnect](/docs/platform-services/automation-service/app-central/integrations/threatconnect/) |
+|
| [ThreatConnect](https://threatconnect.com/) | Automation integration: [ThreatConnect](/docs/platform-services/automation-service/app-central/integrations/threatconnect/) |
+| }) | [Threat Crowd](https://otx.alienvault.com/) | Automation integration: [Threat Crowd](/docs/platform-services/automation-service/app-central/integrations/threat-crowd/) |
+|
| [Threat Crowd](https://otx.alienvault.com/) | Automation integration: [Threat Crowd](/docs/platform-services/automation-service/app-central/integrations/threat-crowd/) |
+| }) | [Threater](https://www.threater.com/) | Cloud SIEM integration: [Bandura](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/ec354a4c-a761-4e18-8ceb-194d6e8692e2.md) |
+|
| [Threater](https://www.threater.com/) | Cloud SIEM integration: [Bandura](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/ec354a4c-a761-4e18-8ceb-194d6e8692e2.md) |
+| }) | [ThreatMiner](https://www.threatminer.org/) | Automation integration: [ThreatMiner](/docs/platform-services/automation-service/app-central/integrations/threatminer/) |
+|
| [ThreatMiner](https://www.threatminer.org/) | Automation integration: [ThreatMiner](/docs/platform-services/automation-service/app-central/integrations/threatminer/) |
+| }) | [ThreatQ](https://www.threatq.com/) | Automation integration: [ThreatQ](/docs/platform-services/automation-service/app-central/integrations/threatq/) |
+|
| [ThreatQ](https://www.threatq.com/) | Automation integration: [ThreatQ](/docs/platform-services/automation-service/app-central/integrations/threatq/) |
+| }) | [Trellix](https://www.trellix.com/en-us/index.html) | Automation integrations:
| [Trellix](https://www.trellix.com/en-us/index.html) | Automation integrations: - [FireEye AX](/docs/platform-services/automation-service/app-central/integrations/fireeye-ax/)
- [FireEye Central Management (CM)](/docs/platform-services/automation-service/app-central/integrations/fireeye-central-management-cm/)
- [FireEye Email Security (EX)](/docs/platform-services/automation-service/app-central/integrations/fireeye-email-security-ex/)
- [FireEye Endpoint Security (HX)](/docs/platform-services/automation-service/app-central/integrations/fireeye-endpoint-security-hx/)
- [FireEye Helix](/docs/platform-services/automation-service/app-central/integrations/fireeye-helix/)
- [FireEye Network Security (NX)](/docs/platform-services/automation-service/app-central/integrations/fireeye-network-security-nx/)
Cloud SIEM integrations:
- [FireEye](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/1430ab5c-7b8b-44e9-a8ec-83076fa374eb.md)
- [Trellix](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9bec8407-4182-46ec-99dd-2adfade15652.md)
Collector: [Trellix mVision ePO Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/trellix-mvisio-epo-source/) | +|
Automation integrations:
- [Trend Micro Deep Security](/docs/platform-services/automation-service/app-central/integrations/trend-micro-deep-security/)
- [Trend Micro Vision ONE](/docs/platform-services/automation-service/app-central/integrations/trend-micro-vision-one/)
Cloud SIEM integration: [Trend Micro](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/8af48b83-18bf-4233-ad51-db37baca0313.md) | +|
}) | [Tufin](https://www.tufin.com/) | Automation integrations:
| [Tufin](https://www.tufin.com/) | Automation integrations: - [Tufin SecureChange](/docs/platform-services/automation-service/app-central/integrations/tufin-securechange/)
- [Tufin SecureTrack V2](/docs/platform-services/automation-service/app-central/integrations/tufin-securetrack-v2/) | + +## U + +| Logo | Vendors and Products | Integrations | +| :-- | :-- | :-- | +|
}) | [Uptime](https://uptime.com/) | Webhook: [Uptime](/docs/integrations/webhooks/uptime/) |
+|
| [Uptime](https://uptime.com/) | Webhook: [Uptime](/docs/integrations/webhooks/uptime/) |
+| }) | [URLScan.io](https://urlscan.io/) | Automation integration: [URLScan.io](/docs/platform-services/automation-service/app-central/integrations/urlscan.io/) |
+
+## V
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+|
| [URLScan.io](https://urlscan.io/) | Automation integration: [URLScan.io](/docs/platform-services/automation-service/app-central/integrations/urlscan.io/) |
+
+## V
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+| }) | [Varnish](https://www.varnish-software.com/) | Apps:
| [Varnish](https://www.varnish-software.com/) | Apps: - [Varnish](/docs/integrations/web-servers/varnish/)
- [Varnish - OpenTelemetry](/docs/integrations/web-servers/opentelemetry/varnish-opentelemetry/) | +|
}) | [Varonis](https://www.varonis.com/) | Cloud SIEM integration: [Varonis](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/20270f89-127e-4055-96ec-56045e67e163.md) |
+|
| [Varonis](https://www.varonis.com/) | Cloud SIEM integration: [Varonis](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/20270f89-127e-4055-96ec-56045e67e163.md) |
+| }) | [Vectra](https://www.vectra.ai/) | Automation integration: [Vectra](/docs/platform-services/automation-service/app-central/integrations/vectra/)
| [Vectra](https://www.vectra.ai/) | Automation integration: [Vectra](/docs/platform-services/automation-service/app-central/integrations/vectra/) Cloud SIEM integration: [Vectra](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/7a3d1a5c-ba67-4597-971f-7057e8f6c8bb.md) | +|
}) | [VirusTotal](https://www.virustotal.com/) | Automation integration: [VirusTotal](/docs/platform-services/automation-service/app-central/integrations/virustotal/) |
+|
| [VirusTotal](https://www.virustotal.com/) | Automation integration: [VirusTotal](/docs/platform-services/automation-service/app-central/integrations/virustotal/) |
+| }) | [VMRay](https://www.vmray.com/) | Automation integration: [VMRay](/docs/platform-services/automation-service/app-central/integrations/vmray/) |
+|
| [VMRay](https://www.vmray.com/) | Automation integration: [VMRay](/docs/platform-services/automation-service/app-central/integrations/vmray/) |
+| }) | [VMware](https://www.vmware.com/) | Apps:
| [VMware](https://www.vmware.com/) | Apps: - [Carbon Black Cloud](/docs/integrations/security-threat-detection/carbon-black-cloud/)
- [VMware](/docs/integrations/containers-orchestration/vmware/)
- [VMware Legacy](/docs/integrations/containers-orchestration/vmware-legacy/)
- [VMware Carbon Black](/docs/integrations/security-threat-detection/vmware-carbon-black/)
Automation integrations:
- [Lastline Analyst](/docs/platform-services/automation-service/app-central/integrations/lastline-analyst/)
- [VMware Carbon Black Cloud Endpoint Standard](/docs/platform-services/automation-service/app-central/integrations/vmware-carbon-black-cloud-endpoint-standard/)
- [VMware Carbon Black Cloud Endpoint Standard V2](/docs/platform-services/automation-service/app-central/integrations/vmware-carbon-black-cloud-endpoint-standard-v2/)
- [VMware Carbon Black Cloud Enterprise EDR](/docs/platform-services/automation-service/app-central/integrations/vmware-carbon-black-cloud-enterprise-edr/)
- [VMware Carbon Black Cloud Platform](/docs/platform-services/automation-service/app-central/integrations/vmware-carbon-black-cloud-platform/)
- [VMware vSphere](/docs/platform-services/automation-service/app-central/integrations/vmware-vsphere/)
- [VMware Workspace ONE](/docs/platform-services/automation-service/app-central/integrations/vmware-workspace-one/)
Cloud SIEM integrations:
- [Carbon Black](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/c2ea2e5e-92f2-49e8-9812-64e60dba63a2.md)
- [VMware](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/fbf25b91-89f1-45c4-903d-664b328bc6e0.md)
Collectors:
- [Carbon Black Cloud Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/carbon-black-cloud-source/)
- [Carbon Black Inventory Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/carbon-black-inventory-source/)
- [Carbon Black Cloud - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/carbon-black/)
- [Collect Metrics from VMware vRealize Operations Manager 8 Enterprise](/docs/send-data/collect-from-other-data-sources/collect-metrics-vrealize-operations-manager/)
- [VMware AirWatch Integration for Sumo Logic](/docs/send-data/collect-from-other-data-sources/vmware-airwatch-integration/)
- [VMware vRealize Log Insight](/docs/send-data/collect-from-other-data-sources/vmware-vrealize-log-insight/)
Partner integration: [VMware Tanzu](https://docs.vmware.com/en/Sumo-Logic-Nozzle-for-VMware-Tanzu/services/sumologic-nozzle-vmware-tanzu/index.html) | +|
}) | [Votiro](https://votiro.com/) | Partner integration: [Votiro](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Votiro#votiro) |
+
+## W
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+|
| [Votiro](https://votiro.com/) | Partner integration: [Votiro](https://github.com/SumoLogic/sumologic-public-partner-apps/tree/master/Votiro#votiro) |
+
+## W
+
+| Logo | Vendors and Products | Integrations |
+| :-- | :-- | :-- |
+| }) | [Watchguard](https://www.watchguard.com/) | Automation integration: [Panda EDR](/docs/platform-services/automation-service/app-central/integrations/panda-edr/) |
+|
| [Watchguard](https://www.watchguard.com/) | Automation integration: [Panda EDR](/docs/platform-services/automation-service/app-central/integrations/panda-edr/) |
+| }) | [WhoisXML](https://main.whoisxmlapi.com/) | Automation integration: [WhoisXML](/docs/platform-services/automation-service/app-central/integrations/whoisxml/) |
+|
| [WhoisXML](https://main.whoisxmlapi.com/) | Automation integration: [WhoisXML](/docs/platform-services/automation-service/app-central/integrations/whoisxml/) |
+| }) | [Windows](https://www.microsoft.com/en-us/windows) | Apps:
| [Windows](https://www.microsoft.com/en-us/windows) | Apps: - [Windows Cloud Security Monitoring and Analytics](/docs/integrations/cloud-security-monitoring-analytics/windows/)
- [Windows - Cloud Security Monitoring and Analytics - OpenTelemetry](/docs/integrations/cloud-security-monitoring-analytics/opentelemetry/windows-opentelemetry/)
- [Windows JSON](/docs/integrations/microsoft-azure/windows-json/)
- [Windows - OpenTelemetry](/docs/integrations/hosts-operating-systems/opentelemetry/windows-opentelemetry/)
- [Windows Performance](/docs/integrations/microsoft-azure/performance/)
- [Windows Legacy](/docs/integrations/microsoft-azure/windows-legacy/)
- [PCI Compliance For Windows (JSON)](/docs/integrations/microsoft-azure/windows-json-pci-compliance/)
- [PCI Compliance for Windows JSON - OpenTelemetry](/docs/integrations/pci-compliance/opentelemetry/windows-json-opentelemetry/)
Automation integration: [PowerShell Tools](/docs/platform-services/automation-service/app-central/integrations/powershell-tools/)
Collectors:
- [Add a Collector to a Windows Machine Image](/docs/send-data/installed-collectors/collector-installation-reference/add-collector-windows-machine-image/)
- [Install a Collector on Windows](/docs/send-data/installed-collectors/windows/)
- [Install OpenTelemetry Collector on Windows](/docs/send-data/opentelemetry-collector/install-collector/windows/)
- [Local Windows Event Log Source](/docs/send-data/installed-collectors/sources/local-windows-event-log-source/)
- [Local Windows Performance Monitor Log Source](/docs/send-data/installed-collectors/sources/local-windows-performance-monitor-log-source/)
- [Microsoft Windows - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/microsoft-windows/)
- [Preconfigure a Machine to Collect Remote Windows Events](/docs/send-data/installed-collectors/sources/preconfigure-machine-collect-remote-windows-events/)
- [Preconfigure a Machine to Collect Remote Windows Performance Monitoring Logs](/docs/send-data/installed-collectors/sources/preconfigure-machine-collect-remote-windows-performance-monitoring-logs/)
- [Remote Windows Event Log Source](/docs/send-data/installed-collectors/sources/remote-windows-event-log-source/)
- [Remote Windows Performance Monitor Log Source](/docs/send-data/installed-collectors/sources/remote-windows-performance-monitor-log-source/)
- [Windows Event Source Custom Channels](/docs/send-data/installed-collectors/sources/windows-event-source-custom-channels/)| +|
}) | [WithSecure](https://www.withsecure.com/en/home) | Automation integrations:
| [WithSecure](https://www.withsecure.com/en/home) | Automation integrations: - [WithSecure Elements](/docs/platform-services/automation-service/app-central/integrations/withsecure-elements/)
- [WithSecure Endpoint Protection](/docs/platform-services/automation-service/app-central/integrations/withsecure-endpoint-protection/) | +|
}) | [Wittra](https://www.wittra.io/) | Automation integration: [Wittra](/docs/platform-services/automation-service/app-central/integrations/wittra/) |
+|
| [Wittra](https://www.wittra.io/) | Automation integration: [Wittra](/docs/platform-services/automation-service/app-central/integrations/wittra/) |
+| }) | [Wiz](https://www.wiz.io/) | Cloud SIEM integration: [Wiz](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/2cde0cac-102b-4756-9a56-81437fea1400.md) |
+|
| [Wiz](https://www.wiz.io/) | Cloud SIEM integration: [Wiz](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/2cde0cac-102b-4756-9a56-81437fea1400.md) |
+| }) | [Workday](https://www.workday.com/) | App: [Workday](/docs/integrations/saas-cloud/workday/)
| [Workday](https://www.workday.com/) | App: [Workday](/docs/integrations/saas-cloud/workday/) Cloud SIEM integration: [Workday](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/6e7ce4b2-569e-476d-b732-7b3a71b1e12a.md)
Collector: [Workday Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/workday-source/) | + +## Z + +| Logo | Vendors and Products | Integrations | +| :-- | :-- | :-- | +|
}) | [Zebrium](https://www.zebrium.com/) | Webhook: [Zebrium RCaaS](/docs/integrations/webhooks/zebrium-rcaas/) |
+|
| [Zebrium](https://www.zebrium.com/) | Webhook: [Zebrium RCaaS](/docs/integrations/webhooks/zebrium-rcaas/) |
+| }) | [Zendesk](https://www.zendesk.com/) | Automation integration: [Zendesk](/docs/platform-services/automation-service/app-central/integrations/zendesk/) |
+|
| [Zendesk](https://www.zendesk.com/) | Automation integration: [Zendesk](/docs/platform-services/automation-service/app-central/integrations/zendesk/) |
+| }) | [Zenduty](https://www.zenduty.com/) | Webhook: [Zenduty](/docs/integrations/webhooks/zenduty/) |
+|
| [Zenduty](https://www.zenduty.com/) | Webhook: [Zenduty](/docs/integrations/webhooks/zenduty/) |
+| Collector: [Zero Networks Segment Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/zero-networks-segment-source/) | +|
}) | [ZeroFox](https://www.zerofox.com/) | Automation integration: [ZeroFOX](/docs/platform-services/automation-service/app-central/integrations/zerofox/)
| [ZeroFox](https://www.zerofox.com/) | Automation integration: [ZeroFOX](/docs/platform-services/automation-service/app-central/integrations/zerofox/) Partner integration: [ZeroFox integration](https://drive.google.com/file/d/13svc5FP0WP3WAES6DvXhK1O8WRiPenf3/edit) | +|
}) | [Zoom](https://zoom.us/) | App: [Zoom](/docs/integrations/saas-cloud/zoom/)
| [Zoom](https://zoom.us/) | App: [Zoom](/docs/integrations/saas-cloud/zoom/) Automation integration: [Zoom](/docs/platform-services/automation-service/app-central/integrations/zoom/)
Cloud SIEM integration: [Zoom](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/bda720cd-399c-4dcc-9289-19ad0c9cb221.md)
Collector: [Zoom Source](/docs/send-data/hosted-collectors/webhook-sources/zoom/) | +|
}) | [Zscaler](https://www.zscaler.com/) | Apps:
| [Zscaler](https://www.zscaler.com/) | Apps: - [Zscaler Internet Access](/docs/integrations/security-threat-detection/zscaler-internet-access/)
- [Zscaler Private Access](/docs/integrations/security-threat-detection/zscaler-private-access/)
Automation integration: [Zscaler](/docs/platform-services/automation-service/app-central/integrations/zscaler/)
Cloud SIEM integration: [Zscaler](https://github.com/SumoLogic/cloud-siem-content-catalog/blob/master/vendors/9dfd2223-1656-4faf-a38a-5a91978fa15e.md)
Collectors:
- [ZScaler NSS - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/zscaler-nss/)
- [Zscaler Private Access - Cloud SIEM](/docs/cse/ingestion/ingestion-sources-for-cloud-siem/zscaler-private-access/) | diff --git a/docs/integrations/web-servers/iis-10.md b/docs/integrations/web-servers/iis-10.md index a63e2b0979..5106b5bf7c 100644 --- a/docs/integrations/web-servers/iis-10.md +++ b/docs/integrations/web-servers/iis-10.md @@ -526,7 +526,7 @@ Locate and install the app you need from the **App Catalog**. If you want to see Version selection is not available for all apps. ::: 3. To install the app, complete the following fields. - 1. **App Name**. You can retain the existing name, or enter a name of your choice for the app. + 1. **App Name**. You can retain the existing name, or enter a name of your choice for the app. 2. **Data Source**. Choose **Enter a Custom Data Filter**, and enter a custom IIS Server farm filter. Examples: * For all IIS Server farms, `webserver_farm=*`. * For a specific farm, `webserver_farm=iis.dev.01`. diff --git a/docs/integrations/web-servers/nginx-ingress.md b/docs/integrations/web-servers/nginx-ingress.md index 989c576e91..85ffa12ad0 100644 --- a/docs/integrations/web-servers/nginx-ingress.md +++ b/docs/integrations/web-servers/nginx-ingress.md @@ -106,7 +106,7 @@ There are limits to how many alerts can be enabled - for details, see the [Alert * For alerts applicable only to a specific farm, your custom filter would be: `webserver_farm=nginx-ingress.01` * For alerts applicable to all farms that start with `nginx-ingress`, your custom filter would be: `webserver_system=nginx-ingress*` * For alerts applicable to a specific farm within a production environment, your custom filter would be: `webserver_farm=nginx-ingress-1` AND `environment=dev` (This assumes you have set the optional environment tag while configuring collection) -3. Go to Manage Data > Alerts > Monitors. +3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**. 4. Click **Add**. 5. Click Import and then copy-paste the above JSON to import monitors. @@ -189,7 +189,7 @@ Locate and install the app you need from the **App Catalog**. If you want to see 1. From the **App Catalog**, search for and select the app. 2. Select the version of the service you're using and click **Add to Library**. 3. To install the app, complete the following fields. - 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app. + 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app. 2. **Data Source.** 3. Choose **Enter a Custom Data Filter**, and enter a custom Nginx Ingress farm filter. Examples: 1. For all Nginx Ingress farms: `webserver_farm=*`. diff --git a/docs/integrations/web-servers/nginx-plus-ingress.md b/docs/integrations/web-servers/nginx-plus-ingress.md index 9d31d776b0..13d3e38176 100644 --- a/docs/integrations/web-servers/nginx-plus-ingress.md +++ b/docs/integrations/web-servers/nginx-plus-ingress.md @@ -125,7 +125,7 @@ Alerts can be installed by either importing them via a JSON or via a Terraform s 1. Download [this JSON file](https://github.com/SumoLogic/terraform-sumologic-sumo-logic-monitor/blob/main/monitor_packages/nginx-plus-ingress/nginxplusingress.json) describing all the monitors. 2. Replace **$$logs_data_source** with logs data source. * For example, `_sourceCategory=Labs/NginxIngress/Logs` -3. Go to Manage Data > Alerts > Monitors. +3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**. 4. Click **Add**. 1. Click **Import** to import monitors from the JSON above. diff --git a/docs/integrations/web-servers/nginx-plus.md b/docs/integrations/web-servers/nginx-plus.md index cf3749dbbd..d404d96710 100644 --- a/docs/integrations/web-servers/nginx-plus.md +++ b/docs/integrations/web-servers/nginx-plus.md @@ -300,7 +300,7 @@ Alerts can be installed by either importing them via a JSON or via a Terraform s 1. Download the [JSON file](https://github.com/SumoLogic/terraform-sumologic-sumo-logic-monitor/blob/main/monitor_packages/nginx-plus/nginxplus.json) describing all the monitors. 2. Replace **$$logs_data_source** and **$$metric_data_source** with logs and metrics data sources respectively. For example, `_sourceCategory=Labs/Nginx/Plus/Logs`. -3. Go to Manage Data > Alerts > Monitors. +3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**. 4. Click **Add**. 5. Click **Import** to import monitors from the JSON above. diff --git a/docs/integrations/web-servers/nginx.md b/docs/integrations/web-servers/nginx.md index 75042e28be..aa7ee91f5f 100644 --- a/docs/integrations/web-servers/nginx.md +++ b/docs/integrations/web-servers/nginx.md @@ -382,7 +382,7 @@ To view the full list, see [Nginx](#nginx-alerts). There are limits to how many * For alerts applicable only to a specific farm, your custom filter would be `webserver_farm=nginx-standalone.01`. * For alerts applicable to all farms that start with nginx-standalone, your custom filter would be `webserver_system=nginx-standalone*`. * For alerts applicable to a specific farm within a production environment, your custom filter would be,`webserver_farm=nginx-1` and `environment=standalone`. This assumes you have set the optional environment tag while configuring collection. -3. Go to Manage Data > Alerts > Monitors. +3. In the main Sumo Logic menu, select **Manage Data > Monitoring > Monitors**. 4. Click **Add**. 5. Click Import and then copy-paste the above JSON to import monitors. @@ -466,7 +466,7 @@ This section demonstrates how to install the Nginx app. Version selection is not available for all apps. ::: 3. To install the app, complete the following fields. - 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app. + 1. **App Name.** You can retain the existing name, or enter a name of your choice for the app. 2. **Data Source.** Choose **Enter a Custom Data Filter**, and enter a custom Nginx farm filter. Examples: 1. For all Nginx farms, `webserver_farm=*`. 2. For a specific farm, `webserver_farm=nginx.dev.01`. diff --git a/docs/platform-services/automation-service/automation-service-bridge.md b/docs/platform-services/automation-service/automation-service-bridge.md index 9a8c29e11f..1a6b94e427 100644 --- a/docs/platform-services/automation-service/automation-service-bridge.md +++ b/docs/platform-services/automation-service/automation-service-bridge.md @@ -123,10 +123,13 @@ An example of a configuration file would be: { "SOAR_URL":"API_ENDPOINT_FROM_FIREWALL_DOC_FOR_YOUR_REGION", "SOAR_TOKEN":"TOKEN_FROM_ADMINISTRATION_-->_SECURITY_-->_INSTALLATION TOKEN", - "SIEM_URL":"https://YOUR_CLOUD_SIEM_URL/sec", + "SIEM_URL":"The HTTPS Source endpoint URL from a Hosted Sumo Logic Collector", "ALIAS":"YOUR_ALIAS_NO_SPACES_LESS_THAN_20_CHARACTERS" } ``` +To create a Hosted Sumo Logic Collector, see [Hosted Collectors](/docs/send-data/hosted-collectors/). To add an HTTPS Source to a Hosted Collector, see [HTTP Logs and Metrics Source](/docs/send-data/hosted-collectors/http-source/logs-metrics/). + +By adding this endpoint to `SIEM_URL`, this will enable the automation bridge logs to be forwarded to Sumo Logic Log Analytics. ### Bridge ALIAS @@ -246,7 +249,7 @@ The automation bridge needs to be able to communicate with the Docker API to wor |:------------------------------------|:---------------|:----------| |`API_URL_HERE` | To determine which is the correct SOAR_URL, see [Sumo Logic Endpoints by Deployment and Firewall Security](/docs/api/getting-started/#sumo-logic-endpoints-by-deployment-and-firewall-security) and get the URL under the API Endpoint column. For example: `https://api.eu.sumologic.com/api/` | | |`SOAR_TOKEN_HERE` | Log in to Sumo Logic and create a new [installation token](/docs/manage/security/installation-tokens/) with the name prefix `csoar-bridge-token`. | | -|`SIEM_URL_HERE` | The HTTP Sumo Logic collector to send the bridge logs. | NONE | +|`SIEM_URL_HERE` | The HTTPS Source endpoint URL from a Hosted Sumo Logic Collector. | NONE | |`BRIDGE_ALIAS_HERE` | Provide the alias name. With bridge ALIAS, it is possible to distinguish which integration resources will be executed with this automation bridge. When a new integration resource is created or edited, it is possible to select the default ALIAS or to create a new one. So every automatic action configured to use this resource will be performed with the bridge that has the same ALIAS. | NONE | ### Methodologies diff --git a/docs/send-data/collect-from-other-data-sources/collect-ruby-on-rails-logs.md b/docs/send-data/collect-from-other-data-sources/collect-ruby-on-rails-logs.md index 8bac397f1e..626e956f5b 100644 --- a/docs/send-data/collect-from-other-data-sources/collect-ruby-on-rails-logs.md +++ b/docs/send-data/collect-from-other-data-sources/collect-ruby-on-rails-logs.md @@ -32,7 +32,8 @@ and the multiline setup. 1. Click **Save**. -1. In Sumo Logic, go to **Manage Data > Collection > Status** to verify that the logs are being ingested. If you do not see any data coming in after 2-3 minutes, check that your file path is correct, that the Sumo Logic Collector has read access to the logs, and that your time zone is configured correctly. +1. Verify that the logs are being ingested. In the main Sumo Logic menu, select **Manage Data > Collection > Status**. +1. If you do not see any data coming in after 2-3 minutes, check that your file path is correct, that the Sumo Logic Collector has read access to the logs, and that your time zone is configured correctly. ## Parsing RoR Logs diff --git a/docs/send-data/opentelemetry-collector/remote-management/source-templates/docker.md b/docs/send-data/opentelemetry-collector/remote-management/source-templates/docker.md new file mode 100644 index 0000000000..35b0ddb9e6 --- /dev/null +++ b/docs/send-data/opentelemetry-collector/remote-management/source-templates/docker.md @@ -0,0 +1,93 @@ +--- +id: docker +title: Docker Source Template +sidebar_label: Docker +description: Learn about the Sumo Logic Docker source template for OpenTelemetry. +--- + +import useBaseUrl from '@docusaurus/useBaseUrl'; +import Tabs from '@theme/Tabs'; +import TabItem from '@theme/TabItem'; + + + + + + + +
})
})
}) +
+}) +
+}) -
-}) +
+}) ### Automation bridge update
-For Ubuntu and CentOS/RedHat, the update process works as the installation process. Follow the same steps described in [Automation bridge installation](#automation-installation) above.
+For Ubuntu and CentOS/RedHat, the update process works as the installation process. Follow the same steps described in [Automation bridge installation](#automation-bridge-installation) above.
:::note
If you are not using the SIEM:
1. Set `SIEM_URL` to `NONE`.
1. Restart the service with:
- ```sh
+ ```
systemctl restart automation-bridge
```
1. If you need to allow automation-bridge communication through a proxy, edit the file `/etc/opt/automation-bridge/automation-bridge.conf` and set the correct value. Below is an example:
- ```sh
- HTTP_PROXY="http://proxy.example.com:8080"
- HTTPS_PROXY="http://proxy.example.com:8080"
+ ```
+ HTTP_PROXY="http://proxy.example.com:8080\"
+ HTTPS_PROXY="http://proxy.example.com:8080\"
```
1. Restart the service with:
- ```sh
+ ```
systemctl restart automation-bridge
```
:::
### Configuring the automation bridge for high availability
-You may elect to deploy and register multiple bridges to your Cloud SOAR tenant for high availability. To cluster automation bridges together logically within Cloud SOAR and ensure high availability, you must set the same ALIAS for each bridge within the cluster in each respective `user-configuration.conf` file upon installation.
+You may elect to deploy and register multiple bridges to your tenant for high availability. To cluster automation bridges together logically within the Automation Service and ensure high availability, you must set the same ALIAS for each bridge within the cluster in each respective `user-configuration.conf` file upon installation.
When multiple bridges are registered with the same ALIAS, they will appear as active. If one or more bridges within the cluster go offline, playbooks will execute via the active nodes utilizing the same ALIAS. So long as there is parity between the nodes and there is at least one active node registered, there will be no disruption in playbook execution.
@@ -177,11 +177,11 @@ To check if the bridge is running correctly, run the following command:
ps faux |grep automation-bridge
```
-This is an example of running `automation-bridge`:
### Automation bridge update
-For Ubuntu and CentOS/RedHat, the update process works as the installation process. Follow the same steps described in [Automation bridge installation](#automation-installation) above.
+For Ubuntu and CentOS/RedHat, the update process works as the installation process. Follow the same steps described in [Automation bridge installation](#automation-bridge-installation) above.
:::note
If you are not using the SIEM:
1. Set `SIEM_URL` to `NONE`.
1. Restart the service with:
- ```sh
+ ```
systemctl restart automation-bridge
```
1. If you need to allow automation-bridge communication through a proxy, edit the file `/etc/opt/automation-bridge/automation-bridge.conf` and set the correct value. Below is an example:
- ```sh
- HTTP_PROXY="http://proxy.example.com:8080"
- HTTPS_PROXY="http://proxy.example.com:8080"
+ ```
+ HTTP_PROXY="http://proxy.example.com:8080\"
+ HTTPS_PROXY="http://proxy.example.com:8080\"
```
1. Restart the service with:
- ```sh
+ ```
systemctl restart automation-bridge
```
:::
### Configuring the automation bridge for high availability
-You may elect to deploy and register multiple bridges to your Cloud SOAR tenant for high availability. To cluster automation bridges together logically within Cloud SOAR and ensure high availability, you must set the same ALIAS for each bridge within the cluster in each respective `user-configuration.conf` file upon installation.
+You may elect to deploy and register multiple bridges to your tenant for high availability. To cluster automation bridges together logically within the Automation Service and ensure high availability, you must set the same ALIAS for each bridge within the cluster in each respective `user-configuration.conf` file upon installation.
When multiple bridges are registered with the same ALIAS, they will appear as active. If one or more bridges within the cluster go offline, playbooks will execute via the active nodes utilizing the same ALIAS. So long as there is parity between the nodes and there is at least one active node registered, there will be no disruption in playbook execution.
@@ -177,11 +177,11 @@ To check if the bridge is running correctly, run the following command:
ps faux |grep automation-bridge
```
-This is an example of running `automation-bridge`:}) +This is an example of running `automation-bridge`:
+This is an example of running `automation-bridge`:}) +
+On the **Bridge** tab in the [Automation Service UI](/docs/platform-services/automation-service/about-automation-service/#automation-service-ui), a list of live bridge agents will be displayed along with their status.
-On the SOAR instance, a list of live bridge agents will be displayed along with their status:
-1. Click the gear icon
+
+On the **Bridge** tab in the [Automation Service UI](/docs/platform-services/automation-service/about-automation-service/#automation-service-ui), a list of live bridge agents will be displayed along with their status.
-On the SOAR instance, a list of live bridge agents will be displayed along with their status:
-1. Click the gear icon }) ### Configuring the automation bridge for CyberArk
@@ -195,13 +195,13 @@ If you are using CyberArk, you must add the following certificates provided by C
#### Enable Podman socket
1. Run the following commands:
- ```bash
- systemctl enable podman.socket && systemctl start podman.socket
- ```
+ ```bash
+ systemctl enable podman.socket && systemctl start podman.socket
+ ```
1. Create a symbolic link:
- ```bash
- ln -s /run/podman/podman.sock /var/run/docker.sock
- ```
+ ```bash
+ ln -s /run/podman/podman.sock /var/run/docker.sock
+ ```
#### Change automation bridge configuration
@@ -219,7 +219,7 @@ ExecStop=/bin/kill -s TERM $MAINPID
Restart=on-failure
TimeoutStartSec=10
RestartSec=10
-
+##
NoNewPrivileges=yes
PrivateTmp=yes
PrivateDevices=yes
@@ -232,25 +232,25 @@ WantedBy=multi-user.target
This is the current solution and it needs to run service as `root`.
:::
-## Cloud SOAR automation bridge for Docker
+## Automation bridge for Docker
-This repository provides Docker images to run the Sumo Logic Cloud SOAR automation bridge. The images contain an automation bridge able to connect to the Sumo Logic SOAR environment.
+This repository provides Docker images to run the Sumo Logic automation bridge. The images contain an automation bridge able to connect to the Automation Service environment.
### Use the Docker automation bridge image
There are images tagged `latest` and for specific versions to run the automation bridge.
-When run, the automation bridge listens on the Docker Unix socket to be able to execute the Cloud SOAR integration or run a standalone daemon.
+When run, the automation bridge listens on the Docker Unix socket to be able to execute the integration or to run a standalone daemon.
-The Cloud SOAR automation bridge needs to be able to communicate with the Docker API to work.
+The automation bridge needs to be able to communicate with the Docker API to work.
### Prerequisites and configuration
-|Environment Variable |Description |Default |
-|:--|:--|:--|
-|`API_URL_HERE` |To determine which is the correct SOAR_URL, see [Sumo Logic Endpoints by Deployment and Firewall Security](/docs/api/getting-started/#sumo-logic-endpoints-by-deployment-and-firewall-security) and get the URL under the API Endpoint column. For example: `https://api.eu.sumologic.com/api/` | |
-|`SOAR_TOKEN_HERE`|Log in to Sumo Logic and create a new [installation token](/docs/manage/security/installation-tokens/) with the name prefix `csoar-bridge-token`. | |
-|`SIEM_URL_HERE` | The HTTP Sumo Logic collector to send the bridge logs. | NONE |
+|Environment Variable |Description |Default |
+|:------------------------------------|:---------------|:----------|
+|`API_URL_HERE` | To determine which is the correct SOAR_URL, see [Sumo Logic Endpoints by Deployment and Firewall Security](/docs/api/getting-started/#sumo-logic-endpoints-by-deployment-and-firewall-security) and get the URL under the API Endpoint column. For example: `https://api.eu.sumologic.com/api/` | |
+|`SOAR_TOKEN_HERE` | Log in to Sumo Logic and create a new [installation token](/docs/manage/security/installation-tokens/) with the name prefix `csoar-bridge-token`. | |
+|`SIEM_URL_HERE` | The HTTPS Source endpoint URL from a hosted Sumo Logic Collector. | NONE |
|`BRIDGE_ALIAS_HERE` | Provide the alias name. With bridge ALIAS, it is possible to distinguish which integration resources will be executed with this automation bridge. When a new integration resource is created or edited, it is possible to select the default ALIAS or to create a new one. So every automatic action configured to use this resource will be performed with the bridge that has the same ALIAS. | NONE |
### Methodologies
@@ -275,15 +275,15 @@ public.ecr.aws/u5z5f8z6/sumologic/csoar-automation-bridge:latest
In the DooD approach, you use the Docker daemon from the host system to interact with containers. Containers themselves do not have their own Docker runtime; they communicate with the host's Docker. This offers some distinct advantages, including simplicity in managing the containers and resource efficiency, as containers do not need to run their own Docker daemon.
-This way, the main container will have access to the Docker socket and can start containers. The only difference is that instead of starting “child” containers, it will start “sibling” containers.
+This way, the main container will have access to the Docker socket and will, therefore, be able to start containers. The only difference is that instead of starting “child” containers, it will start “sibling” containers.
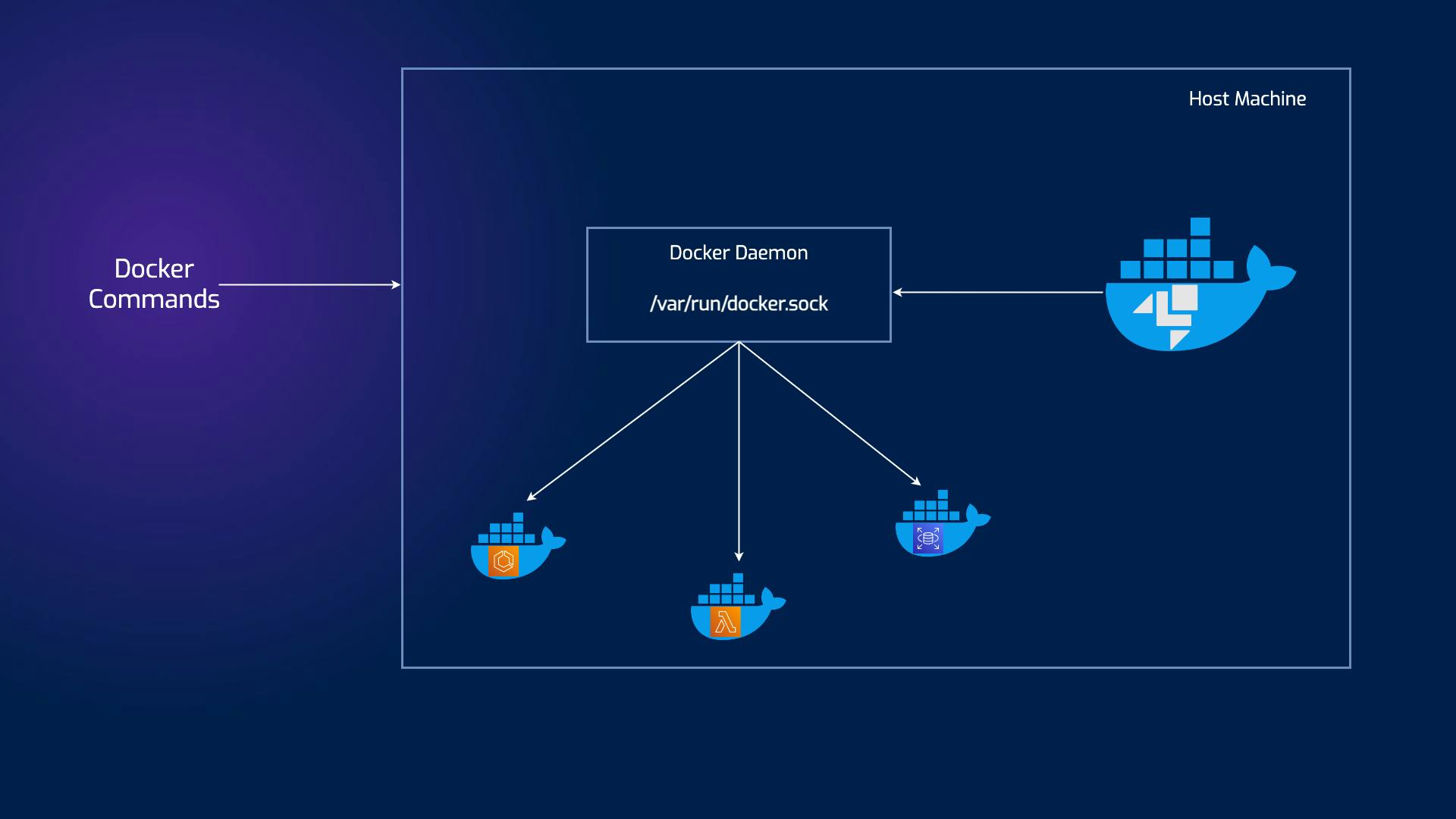
-It's useful to share pulled images with all bridges running on the host machine.
+It's useful to share the pulled image with all bridges running on the host machine.
#### With privileged option
- ```bash
+```bash
docker run -d \
--privileged \
-e SOAR_URL=API_URL_HERE \
@@ -293,7 +293,7 @@ docker run -d \
-e DOCKER_TLS_CERTDIR=/certs \
-v docker-certs-ca:/certs/ca -v docker-certs-client:/certs/client \
public.ecr.aws/u5z5f8z6/sumologic/csoar-automation-bridge:latest
- ```
+```
Privileged containers are special containers with elevated privileges and direct access to the host system. Unlike their non-privileged counterparts, which are isolated and restricted in their capabilities, privileged containers can perform tasks requiring higher-level access. They achieve this by interacting with the host kernel and accessing sensitive resources, including hardware devices and network interfaces.
diff --git a/docs/contributing/style-guide.md b/docs/contributing/style-guide.md
index 2b18bea570..8040368600 100644
--- a/docs/contributing/style-guide.md
+++ b/docs/contributing/style-guide.md
@@ -1410,14 +1410,14 @@ See the following tabbed code examples:
### Configuring the automation bridge for CyberArk
@@ -195,13 +195,13 @@ If you are using CyberArk, you must add the following certificates provided by C
#### Enable Podman socket
1. Run the following commands:
- ```bash
- systemctl enable podman.socket && systemctl start podman.socket
- ```
+ ```bash
+ systemctl enable podman.socket && systemctl start podman.socket
+ ```
1. Create a symbolic link:
- ```bash
- ln -s /run/podman/podman.sock /var/run/docker.sock
- ```
+ ```bash
+ ln -s /run/podman/podman.sock /var/run/docker.sock
+ ```
#### Change automation bridge configuration
@@ -219,7 +219,7 @@ ExecStop=/bin/kill -s TERM $MAINPID
Restart=on-failure
TimeoutStartSec=10
RestartSec=10
-
+##
NoNewPrivileges=yes
PrivateTmp=yes
PrivateDevices=yes
@@ -232,25 +232,25 @@ WantedBy=multi-user.target
This is the current solution and it needs to run service as `root`.
:::
-## Cloud SOAR automation bridge for Docker
+## Automation bridge for Docker
-This repository provides Docker images to run the Sumo Logic Cloud SOAR automation bridge. The images contain an automation bridge able to connect to the Sumo Logic SOAR environment.
+This repository provides Docker images to run the Sumo Logic automation bridge. The images contain an automation bridge able to connect to the Automation Service environment.
### Use the Docker automation bridge image
There are images tagged `latest` and for specific versions to run the automation bridge.
-When run, the automation bridge listens on the Docker Unix socket to be able to execute the Cloud SOAR integration or run a standalone daemon.
+When run, the automation bridge listens on the Docker Unix socket to be able to execute the integration or to run a standalone daemon.
-The Cloud SOAR automation bridge needs to be able to communicate with the Docker API to work.
+The automation bridge needs to be able to communicate with the Docker API to work.
### Prerequisites and configuration
-|Environment Variable |Description |Default |
-|:--|:--|:--|
-|`API_URL_HERE` |To determine which is the correct SOAR_URL, see [Sumo Logic Endpoints by Deployment and Firewall Security](/docs/api/getting-started/#sumo-logic-endpoints-by-deployment-and-firewall-security) and get the URL under the API Endpoint column. For example: `https://api.eu.sumologic.com/api/` | |
-|`SOAR_TOKEN_HERE`|Log in to Sumo Logic and create a new [installation token](/docs/manage/security/installation-tokens/) with the name prefix `csoar-bridge-token`. | |
-|`SIEM_URL_HERE` | The HTTP Sumo Logic collector to send the bridge logs. | NONE |
+|Environment Variable |Description |Default |
+|:------------------------------------|:---------------|:----------|
+|`API_URL_HERE` | To determine which is the correct SOAR_URL, see [Sumo Logic Endpoints by Deployment and Firewall Security](/docs/api/getting-started/#sumo-logic-endpoints-by-deployment-and-firewall-security) and get the URL under the API Endpoint column. For example: `https://api.eu.sumologic.com/api/` | |
+|`SOAR_TOKEN_HERE` | Log in to Sumo Logic and create a new [installation token](/docs/manage/security/installation-tokens/) with the name prefix `csoar-bridge-token`. | |
+|`SIEM_URL_HERE` | The HTTPS Source endpoint URL from a hosted Sumo Logic Collector. | NONE |
|`BRIDGE_ALIAS_HERE` | Provide the alias name. With bridge ALIAS, it is possible to distinguish which integration resources will be executed with this automation bridge. When a new integration resource is created or edited, it is possible to select the default ALIAS or to create a new one. So every automatic action configured to use this resource will be performed with the bridge that has the same ALIAS. | NONE |
### Methodologies
@@ -275,15 +275,15 @@ public.ecr.aws/u5z5f8z6/sumologic/csoar-automation-bridge:latest
In the DooD approach, you use the Docker daemon from the host system to interact with containers. Containers themselves do not have their own Docker runtime; they communicate with the host's Docker. This offers some distinct advantages, including simplicity in managing the containers and resource efficiency, as containers do not need to run their own Docker daemon.
-This way, the main container will have access to the Docker socket and can start containers. The only difference is that instead of starting “child” containers, it will start “sibling” containers.
+This way, the main container will have access to the Docker socket and will, therefore, be able to start containers. The only difference is that instead of starting “child” containers, it will start “sibling” containers.
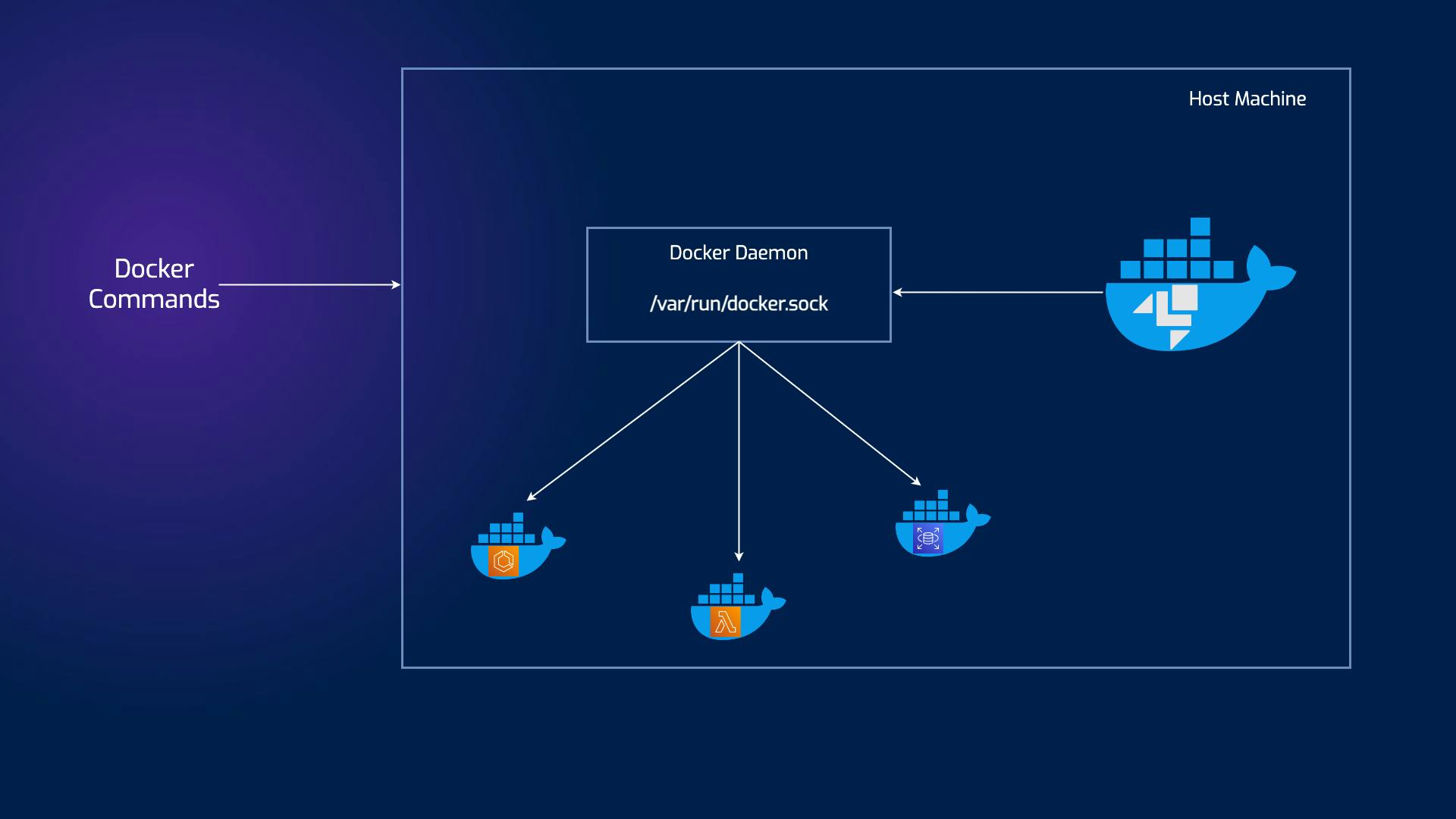
-It's useful to share pulled images with all bridges running on the host machine.
+It's useful to share the pulled image with all bridges running on the host machine.
#### With privileged option
- ```bash
+```bash
docker run -d \
--privileged \
-e SOAR_URL=API_URL_HERE \
@@ -293,7 +293,7 @@ docker run -d \
-e DOCKER_TLS_CERTDIR=/certs \
-v docker-certs-ca:/certs/ca -v docker-certs-client:/certs/client \
public.ecr.aws/u5z5f8z6/sumologic/csoar-automation-bridge:latest
- ```
+```
Privileged containers are special containers with elevated privileges and direct access to the host system. Unlike their non-privileged counterparts, which are isolated and restricted in their capabilities, privileged containers can perform tasks requiring higher-level access. They achieve this by interacting with the host kernel and accessing sensitive resources, including hardware devices and network interfaces.
diff --git a/docs/contributing/style-guide.md b/docs/contributing/style-guide.md
index 2b18bea570..8040368600 100644
--- a/docs/contributing/style-guide.md
+++ b/docs/contributing/style-guide.md
@@ -1410,14 +1410,14 @@ See the following tabbed code examples: