New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Validate user input and keep path in a separate argument for importwallet, createwallet and dumpwallet #20128
Comments
|
I think it has previously been suggested to only allow absolute paths |
std::__cxx11::regex invalid_chars("(/|\\.)(.*)");
if (regex_match(request.params[0].get_str(), invalid_chars)) {
throw JSONRPCError(RPC_WALLET_ERROR, "Invalid characters in wallet name");
}How about this? And can someone help me understand what all files need to be changed for this
|
|
Not sure what needs to be validated, if it's a valid file path then it should be fine. |
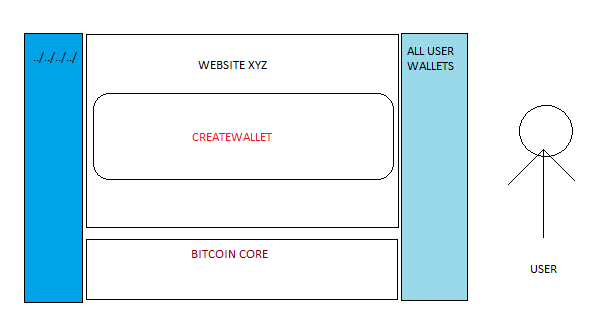
I think we can just validate if the wallet name string has any characters in the beginning that can be used to do more than just creating a wallet in an expected directory. I am thinking to include few more characters in it like Trying to stop the user to do anything in the blue area on left when he uses the web application. I have never tried to fix things in past, only break lol so not really sure if this thing may affect web apps using bitcoin core but its always good to restrict the user by validating inputs. Other thing which I understood after reading everything is that users should not have privileges to access other directories. This is something we can't control so just basic checks in place. If validating the wallet name string for 3-4 special chars in the beginning breaks anything we can ignore this issue and PR. I will do more research this week and add everything in the PR with tests. |
Clearly you could validate user input on the web app. You could even assign a "safe" wallet name for the desired wallet name. |
|
Sure. That's why I mentioned 4 things in the issue description earlier:
|
|
I can't figure out what the issue is here. The problem is with a web app allows users to specify bitcoin wallet names? Like the web app has some code like: if (wallet_name == "big wallet") {
throw error("Can't spend from big wallet!")
}but the user can get around this by spending from |
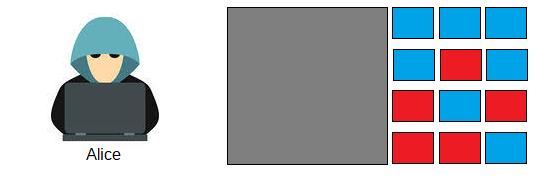
Alice is trying to test few websites and apps that use bitcoin core. Red boxes on right represent vulnerable apps and Blue boxes are secure. Grey box is bitcoin core. We are trying to prevent Alice to exploit any of those small boxes (bitcoin projects using bitcoin core) on right by making bitcoin core more secure and not depend on devs involved in different bitcoin projects. |
|
But what is the vulnerability you're trying to protect against? |
|
Path/Directory Traversal with the help of Example: https://medium.com/tenable-techblog/android-mx-player-path-traversal-to-code-execution-9134b623eb34 |
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
7117d75 Update 'Secure string handling' (Prayank) Pull request description: - Add information about possible path traversal attack - [wallet_name](https://bitcoincore.org/en/doc/0.20.0/rpc/wallet/createwallet/) (string): _The name for the new wallet. If this is a 'path', the wallet will be created at the 'path' location._ Fixes bitcoin#20128 (Not really fixing it but workaround) This PR is an alternative to bitcoin#20393 ACKs for top commit: michaelfolkson: ACK 7117d75 RiccardoMasutti: ACK bitcoin@7117d75 benthecarman: ACK 7117d75 Tree-SHA512: 0d6c4f8db5feba848bbb583e87a99e6c4b655deaa2b566164e2632acc1aabf470d4626d2dc4b82c4997effc30d9b474d860d0e0d3e896648c5cc9bfdb623da6d
Is your feature request related to a problem? Please describe.
Wallets with weird names possible which can be exploited in vulnerable web applications that use Bitcoin Core and allow the users to create and import/export wallet
../testwalletfor Linux..\testwalletfor WindowsTried on Bitcoin Core v 0.20.0
#20080 (comment)
Describe the solution you'd like
Keep two arguments:
wallet_nameandwallet_pathforcreatewalletfilenameandfilepathfordumpwalletimportwalletValidate user input. Name should not contain special characters. Path should be optional and if not specified use a default value.
Describe alternatives you've considered
Web developers should create secure web apps that use Bitcoin Core.
Additional context
I understand its not a vulnerability in Bitcoin Core and only affects vulnerable web apps that use Bitcoin Core. However we can at least consider it a bug that may affect something in future or other projects that use Bitcoin Core. Basic checks for user input can improve the security. In 2017 I had a website in which someone had reported a vulnerability that could be used to change price of flight tickets and book with almost zero bitcoin. It was an issue with the website and we had to fix it although nobody could exploit it because the third party APIs that we were using to book the fight tickets were validating all the things. So a ticket couldn't be processed after tampering and changing the price by attacker. Similarly, if any web developer makes a mistake and using Bitcoin Core for the web app would still be unaffected if Bitcoin Core itself doesn't allow such things for wallet names.
There have been lot of directory traversal related vulnerabilities, recently one was reported in Facebook android app:
https://portswigger.net/daily-swig/vulnerability-in-facebook-android-app-nets-10k-bug-bounty
The text was updated successfully, but these errors were encountered: