New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Activate TOR Network on Setup #592
Comments
|
I agree with Tor on by default. It also helps with port forward issues. Would go as far as experimenting with running a Tor relay node as well to strengthen the anonymous side of the network. Would help a lot with Initial Block Download through Tor. See as example: https://github.com/seth586/guides/blob/master/FreeNAS/extras.md#tor-relay-node Guide for Debian/Ubuntu: https://trac.torproject.org/projects/tor/wiki/TorRelayGuide/DebianUbuntu |
|
Go for TOR as default! Great suggestion. |
|
Not sure with TOR as a forced default - I like to let the user start with the mininum and then add to it by option. If TOR is a forced default, then there is no way for a user to start with the RaspiBlitz without TOR/hiddenService. Let me paint a dramatic picture: Think of a country where its punishable by law to run TOR. Every outed RaspiBlitz user could been accused of having run TOR/hiddenService at least once, just because of the use of RaspiBlitz. Or maybe a more paranoid picture: Someone who belives that TOR is run/subverted by a gov agency and is a honey pot would be forced joined. BUT I think TOR on or off can be a OPTION DURING THE SETUP and so running TOR can be the first/default option here to foster its use. I think that could be the best compromise here. |
💯% agree, yes can keep clearnet as the default, but give the option during the initial setup to have everything on Tor from the very start. This way the user's IP address and LN node public key does not get associated at all. That will be a huge improvement in privacy. |
|
I'd still recommend to default to TOR during initial setup with the user being able to opt-out of TOR if she wants to do so. Maybe a short explainer why to run with or without TOR. IMHO if a user don't know what to pick here, the privacy risk by exposing the IP and the funds tied to it is far more severe than running TOR (and afaik only exit nodes had been problematic, which we are not using). |
|
An argument for clearnet as the default is that the Raspiblitz is also for people who are completely new to the space and just want to try out having a full node. They might feel being forced into participating in Tor as well which is again another thing to digest and accept. Might repel some people and decrease adoption (not even going as far the potential legal /trust issues mentioned by @rootzoll). Regarding the funds I would not suggest anyone keeping significant amounts on a "cheapest as possible" Raspberry Pi node so the "tainting" is minimal. Also I think running the bitcoin software would probably flag one up less than running Tor, but this can change and is very different between jurisdictions and threat models. As a more advanced/paranoid user or running on an alternative platform one would build their own SD card anyway. In that we could make an option to install and activate Tor already before the first reboot. In that case by building their own SD card one could have the option to have Tor on by default and others could choose to opt-in during the initial setup. |
|
Made a branch where introduced a third parameter Command to test building the SD card (https://github.com/rootzoll/raspiblitz#build-the-sd-card-image): |
|
PR incoming with this one after I have done a couple of test builds. |
|
LN Tor usage getting more attention lately: |
|
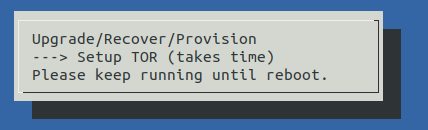
OK implemented for v1.3 release .. needs testing if working within setup process. |
|
I must admit I had trouble with my implementation so will be excited to try a working one! |
|
First test during setup shows that TOR gets installed and bitcoin syncs on it ... but bitcoin seems quite slow on catching up on sync when running behind TOR. Will see if it will catchup over night. LND configuration looks correct for TOR after setup. Showing no URIs yet ... will wait after it has finished initial scan. |
|
I have just finished testing an SSD with an Odroid XU4. Initial Block Download took ~3 days with some Internet/router troubles one night. Will try syncing on Tor now. If syncing behind Tor (I presume) depends more on the network speed rather than processing power, running a Tor relay should be considered to strengthen the network. It only takes as much as modifying the configuration file Could be activated from the service menu after initial sync. What do you think @rootzoll ? |
|
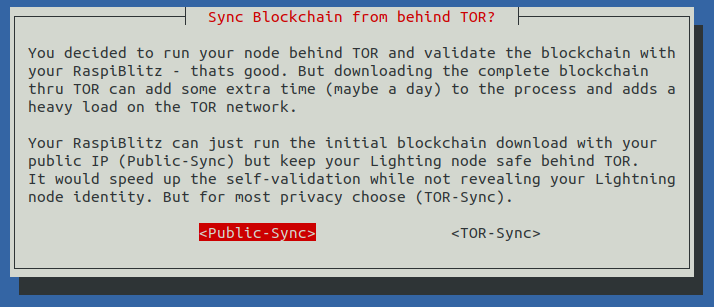
@openoms about activating TOR as relay node I added to this to a later issue here: #659 I am considering if the user chooses to activate TOR on setup to just apply this to the Lightning Node first (so that bitcoind is not getting that slow on ctachup syncing) and then (once full synced) you can switch also your bitcoind behind TOR ... not sure if practical possible, but from a theoretical view it should be OK as long as you dont associate your Lightning NodeID with your IP. Any concerns with that? |
|
Catchup of bitcoind behind TOR is slow but seems to work. Will test a bit longer. |
I agree that the most important option is to not advertise the IP of the new Lightning Node being set up, but that is an option already if port forwarding is simply not set up for 9735. If someone wants to hide the fact that he is using Bitcoin and LN, Tor should be switched on for both before the Initial Sync knowing that it will affect the performance. |
|
Yep, that's probably the best choice: Just let the user decide if he wants to use clearnet for faster initial sync with less privacy. When finished, switch back to everything over tor. Thanks for implementing this, unfortunately I don't have time for testing currently... |
Started the IBD behind Tor last last night with the same config. ~20% after 10 hours. Expecting to finish roughly the same within 2-3 days. Will update this comment as it goes. |
|
TODO: Info that torrent download is not done thru TOR (advise to copy) |
This node of mine got inaccessible the second time now. First I needed to do a hard restart (pulling the plug) as it seemed to freeze and on restart it started to sync the blockchain again from 0%. Now it is again lost connection, but I am away so cannot look into it for a couple of days. Issue: the 00raspiblitz.sh is too radical deleting all the blockchaindata in the case when there is a restart during IBD. UPDATE: the XU4 SBC was in an off-state. Froze or failed to to power the SSD (Samsung EVO 860 rated to 1.2A). Anyway it does not seem to be problem related to the Tor network. |
|
TODO: Test on RP3 was soo slow I will testest on a RP4. @openoms there might even be faster way todo this I wil test on speed now - please let me know if you see any "danger" there:
|
|
Same RPi4 node. Building the SDcard manually with |
|
Choosing TOR will be a two step if needed: During Setup user has to choose between PublicIP and TOR in general. And if user chooses to self-validate/sync with the Blitz it will ask again if the IBD (just for Bitcoind) can be PublicP or should also be behind TOR. Here is the info text on that second choice the Blitz will show: |
|
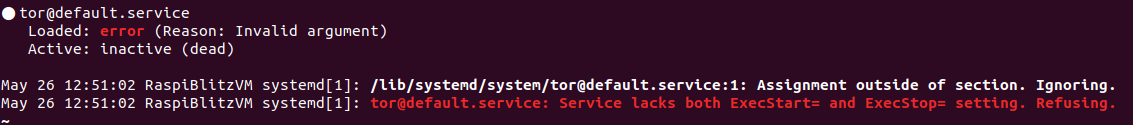
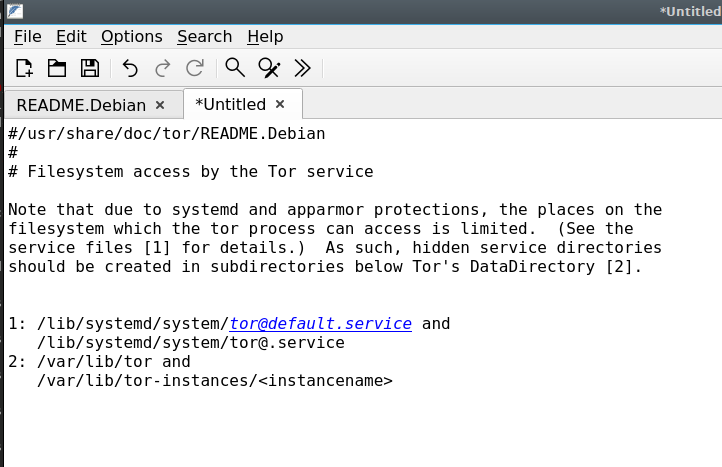
@openoms I've played around with various settings and I think it's quite possible the problem, which appears to be rights related is due to "Apparmor" and this I think was installed by default with Debian 10 by defailt. It's also running in Raspbian, right? |
|
Testing with TOR looks good so far on my Raspberries with Debian Buster. |
What configuration and kind of test(s) was performed so far and observed working? |
|
@fluidvoice with RC5 (release today). I did both options like you can see from the dialog above and they run without problem so far. Maybe give the RC5 a try as soon as its out. |
yes, will try latest now. Btw really looks like in non-Raspbian OS it's related to the |
|
Looks like Tor works in my Debian Buster x86 VM now. |
|
IBD on Clearnet with Tor activated for Lightning went well, in 2days 2 hours on my RPi4 4gb + SSD: https://twitter.com/openoms/status/1162118831965446145. Only concern was that, when the IBD finished the LND was restarted and waited to finish the blockchain scan until unlocked again. This added hours to have LND ready because it needed to scan the last ~5 percent of the blockchain. Ideally both bitcoin and LND sync should finish before restarting the services to put bitcoin behind Tor too or maybe wait for a manual trigger and keep in sync until looked at? |
|
edit: moved to revisiting fast-sync subject |
@rootzoll what's the best way to backup an existing installation to try out RC5 ? |
https://github.com/rootzoll/raspiblitz#backup-for-on-chain---channel-funds |
I will check on this before final release - but maybe such optimization will get pushed to next released to not further delay the v1.3 release. |
Is this the preferred method for switching between 1.3rc3 -> 1.3rc5 without losing funds? |
|
@woeisme on v1.3rc3 you can use the "UPDATE" option in the SSH main menu and just use "continue anyway" if reported that no new version is available. |
|
Hey @rootzoll @openoms post v1.5.1 update. I am seeing this in TOR logs. /run/tor is not owned by this user (bitcoin, 1002) but by debian-tor (111). Can you help me understand what exactly is going here and a possible solution. |
|
@codeoholic those warnings are not critical - see issue: #402 The idea is to clean this up, when we make TOR by default in an upcoming version. |
|
Okay. I was thinking this could be the reason for the LND REST service being unreachable via TOR. If this is normal, could you point me how to debug it? |
|
To monitor TOR connections check the |
Most Raspiblitz users are running their node from home, which makes them prone to privacy and security failures.
When setting up a new Raspiblitz, it should default to run only on TOR network. Clearnet should only be possible if the user wants to actively opt-in to advertise his node IP.
Advantages:
Disadvantages:
More info: https://github.com/lightningnetwork/lnd/blob/master/docs/configuring_tor.md
The text was updated successfully, but these errors were encountered: