New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Content Security Policy (CSP) blocks application of inline styles #2625
Comments
|
Hi @Identekit 👋, Also, let's link #1263 (so everything is better documented :) |
|
@Markel Version 2.8.3 is the most recent version available in NuGet...so that is the version I have. Has this been fixed in a more recent version? If so, when will the latest version be available in NuGet? I also added a comment to #1263, thanks for linking this back to that. |
|
I actually don't know if this issue has been fixed in newer version, I'm relatively new to the project so those "backlog" issues still get me. Maybe @patrickkettner knows something about it? 🤔 Regarding Nuget (first time I heard about it, I won't go to sleep without learning something new :), there isn't an official release of Modernizr there (as far as I know) and the unofficial package is outdated as previously mentioned. You may want to try an updated version that I found, it's v3.4 which is outdated (from 2017) but definitely newer than the version that you are using, which dates back to mid-2014. |
|
@Markel |
|
Is there any new information about this issue? Is there any plan to move on with this? |

Type of bug
Describe the bug
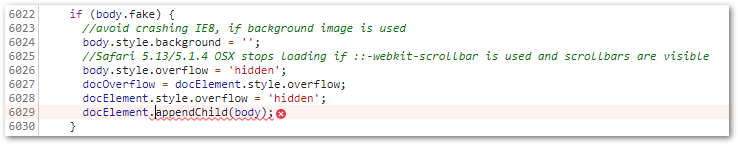
Code within modernizr-2.8.3.js is being blocked by the Content Security Policy because it requires inline execution.
How to Reproduce
content-security-policy: default-src 'self'; font-src 'self'; img-src 'self'; style-src 'self';Expected behavior
modernizr functionality is not blocked by the Content Security Policy.
Additional context
Unfortunately the use of a hash also requires the 'unsafe-inline' which does not prevent malicious inline code.
The text was updated successfully, but these errors were encountered: