You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
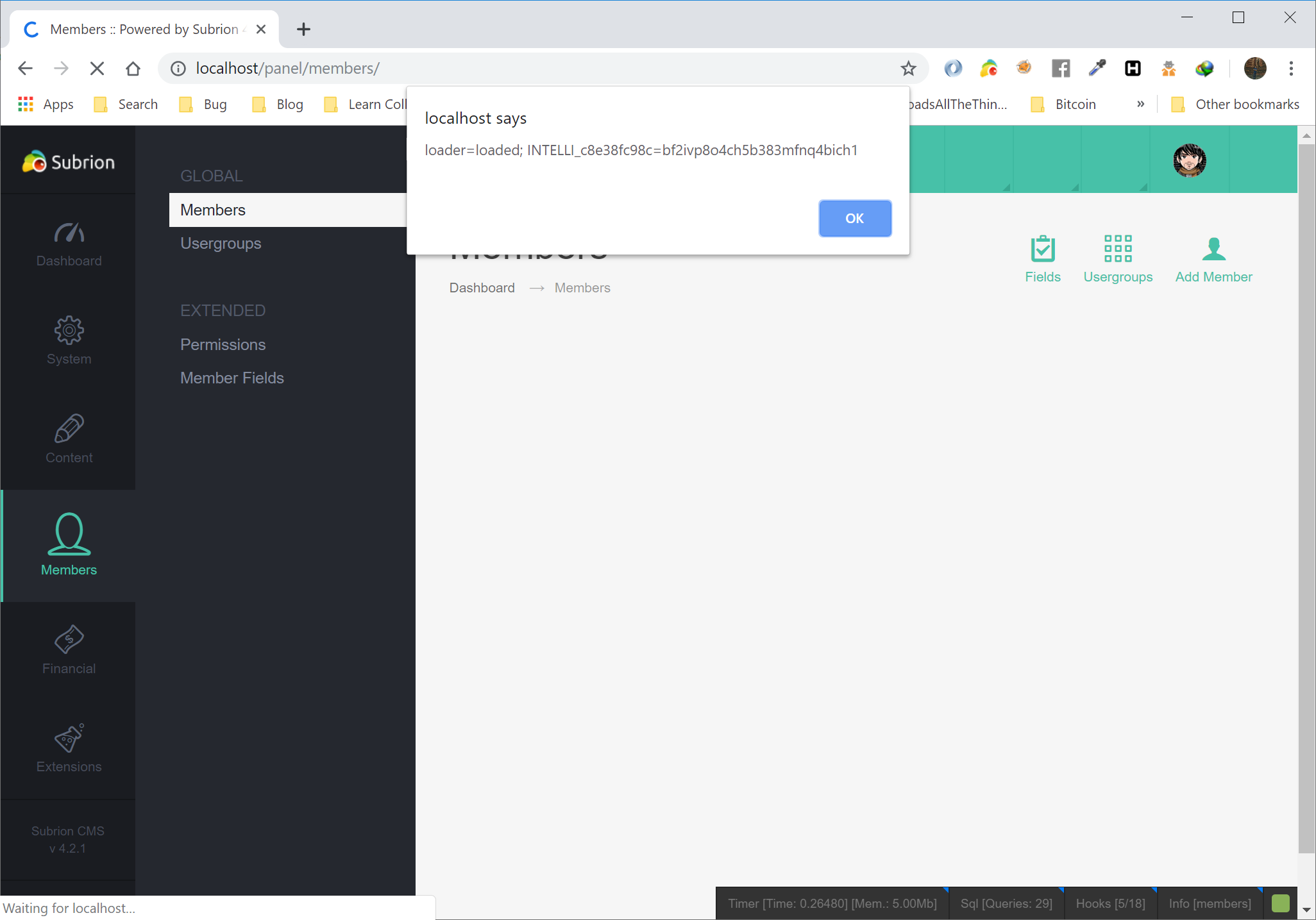
First login the panel with user credential, Go to member tag from left menu.
http://localhost/panel/members/
Username, Full Name, Email are editable with double click on it. Insert the following payload
<img src=x onerror=alert(document.cookie)>
Xss alert are trigger.
Poc
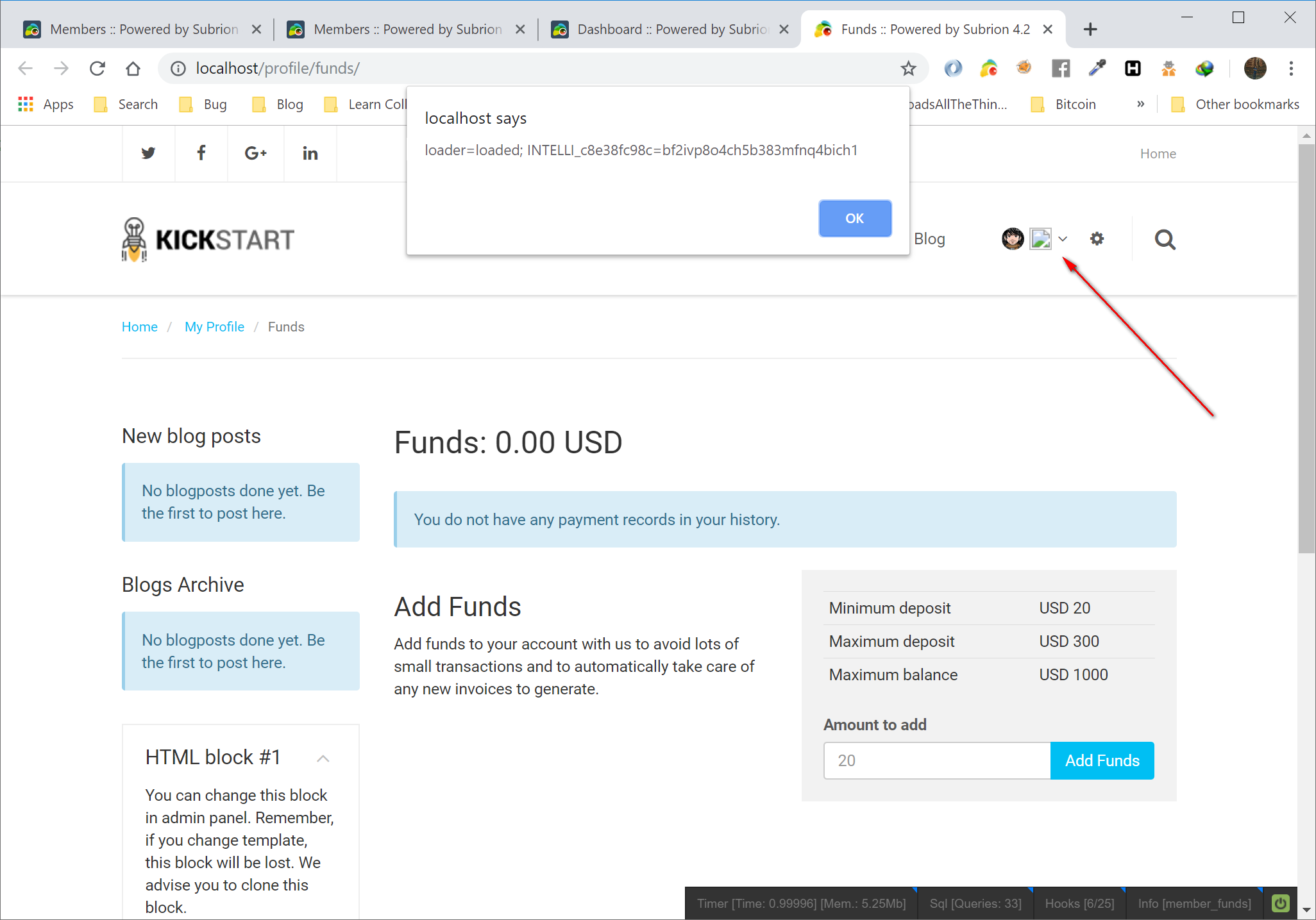
Note. Script tag are filter in the input field. it is work at username <img src="//www.gravatar.com/avatar/1667c96fb90d94769e72069d6cad71b6?s=100&d=mm&r=g" alt="<script>alert(1);</script>">
Poc 2
Please fix and filter all input tag.
Thank you.
The text was updated successfully, but these errors were encountered:
Can you explain what benefit it would be, if you already have admin access? Frontend input is properly sanitized, so why would admin need to use that line for user? I don't quite understand the idea.
Test it on version 4.2.1.
First login the panel with user credential, Go to member tag from left menu.
http://localhost/panel/members/Username, Full Name, Email are editable with double click on it. Insert the following payload
<img src=x onerror=alert(document.cookie)>Xss alert are trigger.
Poc
Note. Script tag are filter in the input field. it is work at username
<img src="//www.gravatar.com/avatar/1667c96fb90d94769e72069d6cad71b6?s=100&d=mm&r=g" alt="<script>alert(1);</script>">Poc 2
Please fix and filter all input tag.
Thank you.
The text was updated successfully, but these errors were encountered: