This repository has been archived by the owner on Dec 13, 2022. It is now read-only.
Identity server /connect/token is returning unauthorized client #1567
Comments
|
You set the allowed grant type to be hybrid - but you are using the password grant type in postman. Hence the error. |
|
@leastprivilege available grant types are authorization_code, client_credentials, password, refresh_token |
|
I have same issue, did you manage to resolve it? |
|
@GuerrillaCoder make sure you are using AllowedGrantTypes = GrantTypes.ResourceOwnerPassword for client, and must be a same Scope as defined in your client scopes |
|
@rahulmistry25425 Thanks. My issue was that and I had to make the callback URLS match my local callback url. |
|
This thread has been automatically locked since there has not been any recent activity after it was closed. Please open a new issue for related bugs. |
Sign up for free
to subscribe to this conversation on GitHub.
Already have an account?
Sign in.

I am using .net core 2.0 identity server 4 approach
I am trying to get access token from identity server using postman.
Postman post request
x-www-form-urlencode post
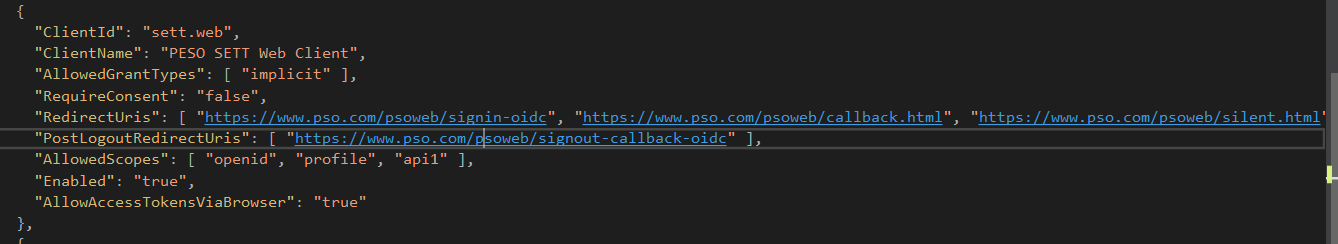
Client configuration
Start token request validation
dbug: IdentityServer4.Validation.TokenRequestValidator[0]
Start resource owner password token request validation
fail: IdentityServer4.Validation.TokenRequestValidator[0]
ASAP-Mobile not authorized for resource owner flow
fail: IdentityServer4.Validation.TokenRequestValidator[0]
{
"ClientId": "ASAP-Mobile",
"ClientName": "ASAP Mobile Client",
"GrantType": "password",
"Raw": {
"client_id": "ASAP-Mobile",
"client_secret": "REDACTED",
"response_type": "code id_token",
"scope": "openid profile aspa-api offline_access",
"grant_type": "password"
}
}
Here is Screenshot
The text was updated successfully, but these errors were encountered: