You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
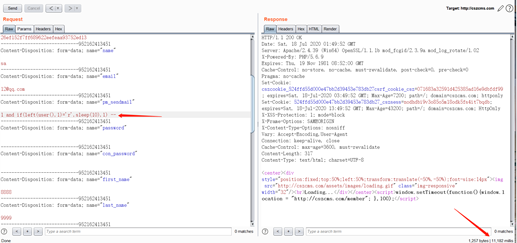
Hi, @cskaza I found a high-risk time-based blind SQL injection vulnerability in the member function module.
(http://website/member/edit)
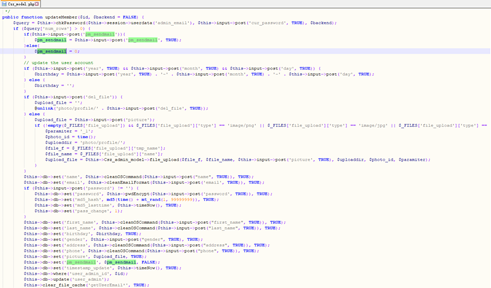
the vulnerable code is on cszcms/models/csz_model.php
The vulnerability parameter is pm_sendmail.This parameter is passed to the database query without any filtering, resulting in a vulnerability.
All the data in the database can be obtained by using sqlmap.
The text was updated successfully, but these errors were encountered:
Hi, @cskaza I found a high-risk time-based blind SQL injection vulnerability in the member function module.


(http://website/member/edit)
the vulnerable code is on cszcms/models/csz_model.php
The vulnerability parameter is pm_sendmail.This parameter is passed to the database query without any filtering, resulting in a vulnerability.
All the data in the database can be obtained by using sqlmap.
The text was updated successfully, but these errors were encountered: