New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
URI Argument Injection in Dogecoin-Qt #2665
Comments
|
@CharesFang Thank you! I have manually back ported the fix from Bitcoin Core and have verified locally. Could you please let me know if this fix (#2666) is complete from your perspective? |
|
I hope to fix as soon as possible |
Fix is in #2666, and we're in the last stages of release preparation so this should be out real soon. |
It looks good. You can fix this vulnerability just as Bitcoin did. |
|
#2666 is merged, will be released with 1.14.5 shortly. |
URI Argument Injection in Dogecoin-Qt
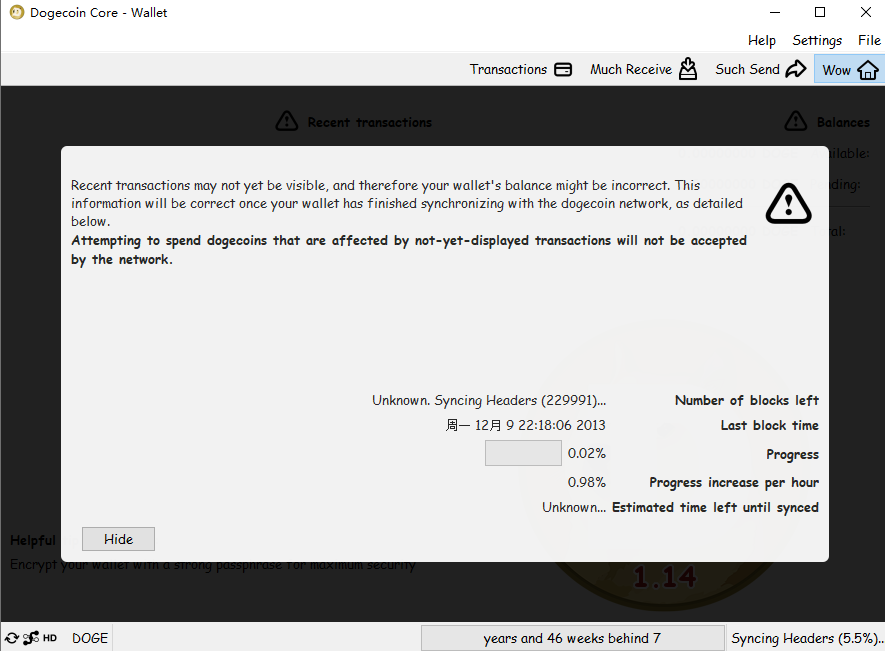
We recently found and confirmed that Dogecoin Core in the latest release (version
1.14.4) and earlier versions are affected by a remote code execution vulnerability in Qt5-based GUI apps. Specifically, theQApplicationinQtframework used by the Dogecoin GUI Program will parseQt built-inarguments, such as-reverseand-platformpluginpath(see the document here). This allows a remote attacker (i.e., a web page) to invoke the local Dogecoin Core program in a victim user machine by using this kind of URI:dogecoin:address -parameter.For a real attack, a malicious web page can first download a malicious Qt plugin (see the earlier link for how to construct the plugin) to user browser's Download folder. The malicious web page then can ask user to click the URI of
dogecoin:any_wallet_address -platformpluginpath file_path_of_downloaded_plugin. Sincedogecoin:URI has been registered by Dogecoin in the registary, the browser will automatically launch the local Dogecoin program and invoke that downloaded plugin, causing a remote code execution.Here for simple demonstration, we use another parameter
-reverseto demonstrate the feasibility. By using the attached HTML page and ask user to click the URIdogecoin:address -reverse. It will automatically launch the localdogecoin-qt.exeprogram and you will find that the GUI has been reversed due to the parameter of-reverse.We provide the screenshot and the test HTML page in the attachment.
For more details, you can refer to the following pages.
src/qt/bitcoin.cpp, see line 315 to 318.Reported by
de957ad9679f28a38f02f00cc7928bce8fb424882ff060a3c09c32895b1474cc.Attachment
The vulnerability test case.
The test HTML page code.
The text was updated successfully, but these errors were encountered: