New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Custom handler for expectedOrigin and expectedRPID #102
Comments
|
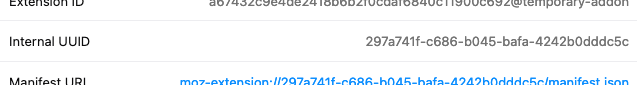
After bootstrapping a new extension using Mozilla's "baby's first extension" tutorial I tried to find out if it's possible for an extension to discover its internal UUID. It seems it is indeed possible to get the current UUID via the const imgURL = browser.runtime.getURL('manifest.json');
const idRegEx = /^moz-extension:\/\/[0-9a-f]{8}-[0-9a-f]{4}-[0-9a-f]{4}-[0-9a-f]{4}-[0-9a-f]{12}/;
console.log(`extension UUID: ${idRegEx.exec(imgURL)}`);Which matches with the UUID that's visible from the extensions page: Can you use this technique to get a given instance's UUID string, which you can then pass in as Edit: Have you figured out what the RP ID is that comes out of an attestation that takes place in a browser extension? |
|
So we've made some tests and we found out that the RP ID is similar to the origin. See this assertion in the SWA debugger here. If you take the rpID hash it's Now trying to found this hash from the uuid: So in this example the RPID === origin. But what's interesting is that the parameter passed to webauthn.create was only And here is a interesting PR on webauthn project: w3c/webauthn#1033 that may explain this behavior. We also tried to pass different things to the webauthn.create but ended up with Concerning the fact that we can get the uuid with I hope this helps but to be honest there is a big lack of documentation around webauthn and extensions 😞 |
|
I suspect you're suffering from nuances of the CTAP2 protocol, the part of WebAuthn that dictates how the authenticator generates a response for whatever options the browser gives it. It seems for Chrome specifically you need to pass in the full extension URI for I feel like this isn't related to WebAuthn extensions...it might save you some headache to table that investigation for now. I'm going to look at the CTAP2 part of the spec a bit closer and see if anything in there explains this. Maybe it's a browser implementation issue 🤷♂️ |
|
I found this part in the spec:
Now I'm suspecting Chrome itself will end up being the culprit, as it's responsible for passing along your It's worth noting you're in a bit of uncharted waters with all of this because I don't think the spec particularly accounts for the use of this API in browser extensions. |
|
So I made a series of tests. For Chrome:
For Firefox: |
|
I think webextensions fits in this part of the spec:
|
|
So here is a reply from Google team: |
|
Hello again, Also I created a test extension: https://github.com/Mikescops/webauthn-extension-playground |
|
@Mikescops Thank you for the update! Seeing WebAuthn in action in a browser extension is pretty exciting for me, even with Firefox giving you issues (and I totally approve of how you linked to the SimpleWebAuthn debugger 😛). I'll be following that Mozilla bugzilla entry you linked, here's hoping for a speedy resolution 🤞 |
|
The debugger is a rich idea you had 👍 hopes we make webauthn a great standard everywhere 😄 |
|
I'm going to go ahead and close this as there's not much in the way of action items for me. I'll take another look at this in the morning and maybe migrate it to a discussion so we don't lose the links you provided earlier to the Closed Issues tab. |


Hello,
As a followup of #90, when using a browser extension, having multiple origin/rpID possible was really cool but we got into facing another issue which is that some browsers like Firefox are using random IDs for their extensions that means it's impossible to maintain a hard-coded list of origins/rpID.
For instance here is the way to validate a FF origin:
I know it's yet another addition but would you allow to have a custom function handler to validate origins and rpIDs?
Let me know if you have a better solution but I guess anyone using SWA with browser extension will face this issue.
The text was updated successfully, but these errors were encountered: