Access Watch is a flexible access log processor that helps operators analyze the web traffic reaching their infrastructure.
Access Watch is built on a real-time stream processor handling logs from inputs of any type:
- CDNs (Cloudfront, Cloudflare, Akamai, ...)
- Load Balancers (ELB)
- Reverse Proxies (Nginx, Haproxy, ...)
- Web Servers (Nginx, Apache, ...)
- Applications (Node, Ruby, PHP, ...)
Access Watch is currently in open beta. For more details, go to: https://access.watch
Make sure you have Node.js version >= 7. We recommend using nvm.
git clone https://github.com/access-watch/access-watch.git
cd access-watch
npm installnpm startIt's loading the default configuration, it's the same as:
npm start config/defaultThe first thing you might want is configuring inputs to connect Access Watch to your traffic sources and convert it in the proper format.
In order to do this, you need to create a new configuration file such as config/custom.js.
See Input Configuration for the list of available input types and how to configure them.
There are also a couple of constants you might configure with a simple config file, to learn more you can head to Constants Configuration.
npm start config/customThe Access Watch API and interface will be served from port 3000 by default.
You can change that using an environment variable:
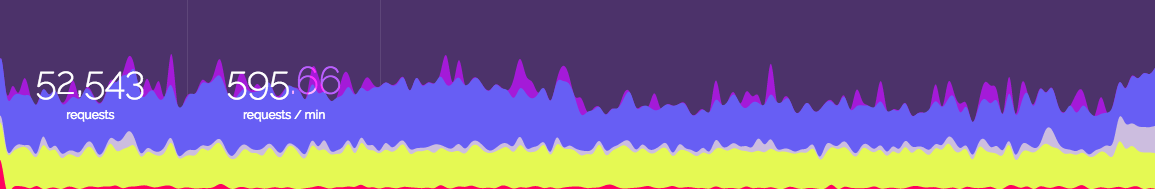
PORT=80 npm start config/customNow, you can point your browser on the address:port where Access Watch is running, for example http://localhost:3000/.
If you see data flowing, congratulations you made it!
Warning: There is currently no built in authentication mechanism, if installed on a public server, you need to properly configure a firewall to restrict access to it.