New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
CLOUDSTACK-9977: Enhance SSL protocol used by Console Proxy #2177
CLOUDSTACK-9977: Enhance SSL protocol used by Console Proxy #2177
Conversation
5cac229
to
4056ea1
Compare
|
LGTM :) |
| @@ -38,6 +38,11 @@ | |||
| private static final Logger s_logger = Logger.getLogger(ConsoleProxySecureServerFactoryImpl.class); | |||
|
|
|||
| private SSLContext sslContext = null; | |||
| private static String[] SSL_PROTOCOLS = { "TLSv1", "TLSv1.1", "TLSv1.2" }; | |||
| private static String[] SSL_CIPHERS = { "TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA", "TLS_DHE_RSA_WITH_AES_128_GCM_SHA256", "TLS_DHE_RSA_WITH_AES_128_CBC_SHA256", | |||
| "TLS_RSA_WITH_AES_128_GCM_SHA256", "TLS_RSA_WITH_AES_128_CBC_SHA256", "TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256", "TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256", | |||
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
@GabrielBrascher do you think we can get the list of ciphers moved/refactored to SSLUtils and other parts of the system may use it (now or in future?)
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I will check this approach and provide a feedback soon. Thanks for the hint @rhtyd !
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I transfered those SSL protocols and ciphers to methos getRecommendedProtocols and getRecommendedCiphers in SSLUtils.
|
Re-kicked travis. |
|
@rhtyd a Jenkins job has been kicked to build packages. I'll keep you posted as I make progress. |
|
Packaging result: ✖centos6 ✖centos7 ✖debian. JID-799 |
|
@GabrielBrascher check and fix build/packaging/Travis failures |
|
Thanks for the feedback @rhtyd ! |
4056ea1
to
a2c91a2
Compare
| /** | ||
| * It returns recommended protocols that are considered secure. | ||
| */ | ||
| public static String[] getRecommendedProtocols() { |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Thanks @GabrielBrascher much better!
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I have to very small comments here @GabrielBrascher
| * It returns recommended protocols that are considered secure. | ||
| */ | ||
| public static String[] getRecommendedProtocols() { | ||
| String[] supportedProtocols = { "TLSv1", "TLSv1.1", "TLSv1.2" }; |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
This is a little cosmetic, but, how about returning directly the array? Instead of assigning it to a variable first?
Also, what about test cases? I mean, if someone starts using this method because it expected the behavior of returning { "TLSv1", "TLSv1.1", "TLSv1.2" }, but later some other person changes it to return only { "TLSv1.1", "TLSv1.2" }, this might affect people using this method
a2c91a2
to
fb8c383
Compare
|
Thanks for the comments @rafaelweingartner. Hope I have addressed them all. |
|
|
||
| @Test | ||
| public void getSupportedProtocolsTest() { | ||
| ArrayList<String> protocolsList = new ArrayList<>(Arrays.asList(spySSLUtils.getSupportedProtocols(new String[] { "TLSv1", "TLSv1.1", "TLSv1.2", "SSLv3", "SSLv2Hello" }))); |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I did not understand this test. You are not using the return of the method, but configuring a return.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Unfortunately, if I did something like the test getRecommendedCiphersTest (with a simple Assert.assertArrayEquals) it would always fail. This method returns an array where the protocols are in a different position of the expected [TLSv1, TLSv1.1, TLSv1.2]. The input is [TLSv1, TLSv1.1, TLSv1.2, SSLv3, SSLv2Hello] but the output is [TLSv1, TLSv1.2, TLSv1.1].
In order to ensure that it will return the expected protocols without caring with their position in the array, I pick the returned array and set as an ArrayList to use the contains method.
Additionally, if someone in the future changes the method getSupportedProtocols and/or getRecommendedProtocols to return a sorted array according to the most recommended protocols (starting from TLSv1.2 then) this test would not fail because it still returning secure protocols.
I can use the returned array and verify all positions without changing the output to an ArrayList.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Aha, my bad. I confused the method "getSupportedProtocols" with "getRecommendedProtocols".
Now I understand what you are doing here.
Everything is just fine +1
fb8c383
to
2c996f3
Compare
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
LGTM
|
|
||
| @Test | ||
| public void getSupportedProtocolsTest() { | ||
| ArrayList<String> protocolsList = new ArrayList<>(Arrays.asList(spySSLUtils.getSupportedProtocols(new String[] { "TLSv1", "TLSv1.1", "TLSv1.2", "SSLv3", "SSLv2Hello" }))); |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Aha, my bad. I confused the method "getSupportedProtocols" with "getRecommendedProtocols".
Now I understand what you are doing here.
Everything is just fine +1
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Thanks, @GabrielBrascher.
Code LGTM
|
LGTM. |
2c996f3
to
fcd40f7
Compare
|
@blueorangutan package |
|
@rhtyd a Jenkins job has been kicked to build packages. I'll keep you posted as I make progress. |
|
Packaging result: ✔centos6 ✔centos7 ✔debian. JID-819 |
|
@blueorangutan test |
|
@rhtyd a Trillian-Jenkins test job (centos7 mgmt + kvm-centos7) has been kicked to run smoke tests |
fcd40f7
to
d10e824
Compare
|
Trillian test result (tid-1217)
|
| @@ -49,10 +66,10 @@ | |||
| } | |||
|
|
|||
| public static SSLContext getSSLContext() throws NoSuchAlgorithmException { | |||
| return SSLContext.getInstance("TLSv1"); | |||
| return SSLContext.getInstance("TLSv1.2"); | |||
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
This might break clients (non-browser) for some cases where TLSv1.2 is not supported.
| } | ||
|
|
||
| public static SSLContext getSSLContext(String provider) throws NoSuchAlgorithmException, NoSuchProviderException { | ||
| return SSLContext.getInstance("TLSv1", provider); | ||
| return SSLContext.getInstance("TLSv1.2", provider); |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
This might break clients (non-browser) for some cases where TLSv1.2 is not supported.
|
@blueorangutan test centos7 vmware55u3 |
|
@rhtyd unsupported parameters provided. Supported mgmt server os are: |
|
@blueorangutan test centos7 vmware-55u3 |
|
@rhtyd a Trillian-Jenkins test job (centos7 mgmt + vmware-55u3) has been kicked to run smoke tests |
|
LGTM! I think that any client that doesn't support TLSv1.2 shouldn't be out there anyway. |
|
@blueorangutan package |
|
@rhtyd a Jenkins job has been kicked to build packages. I'll keep you posted as I make progress. |
|
Packaging result: ✔centos6 ✔centos7 ✔debian. JID-857 |
|
Trillian test result (tid-1242)
|
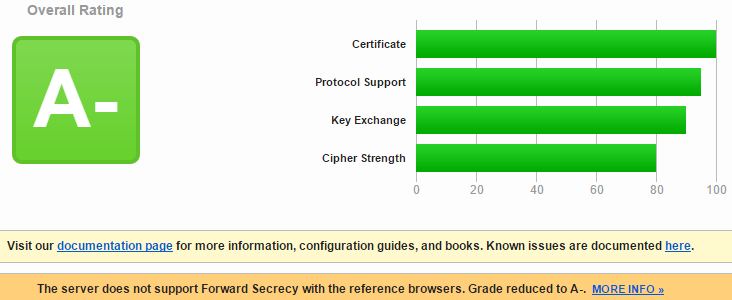
Current SSL protocol and ciphers used in SystemVMs are not the recommended. To analyze it is possible to use tests such as from SSL Labs (https://www.ssllabs.com/ssltest/). This commit changes the grade from C to -A
d10e824
to
f6bd590
Compare
ACS CI BVT RunSumarry: Link to logs Folder (search by build_no): https://www.dropbox.com/sh/r2si930m8xxzavs/AAAzNrnoF1fC3auFrvsKo_8-a?dl=0 Failed tests:
Skipped tests: Passed test suits: |
|
@blueorangutan package |
|
@rhtyd a Jenkins job has been kicked to build packages. I'll keep you posted as I make progress. |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
LGTM, I see some failures -- will kick a test matrix on xen+kvm+vmware to rule our regressions.
|
Packaging result: ✔centos6 ✔centos7 ✔debian. JID-860 |
|
@blueorangutan test matrix |
|
@rhtyd a Trillian-Jenkins matrix job (centos6 mgmt + xs65sp1, centos7 mgmt + vmware55u3, centos7 mgmt + kvmcentos7) has been kicked to run smoke tests |
|
Trillian test result (tid-1251)
|
|
Trillian test result (tid-1252)
|
|
Trillian test result (tid-1253)
|
|
Test LGTM, the failed tests are intermittent (for r/vpc) and some env induced errors for vmware/xenserver. |
Current SSL protocol and ciphers used in SystemVMs are not the recommended. One can verify this with tests such as the one from SSL Labs (https://www.ssllabs.com/ssltest/). The grade was capped to C because of SSL ciphers and protocol. The grade was capped to B because it was allowed to use Diffie-Hellman keys with size lesser than 2048 bits. This commit changes the grade from C to A-.
The following image shows the test result before any changes.

After including the changes from this commit the test result was A-.