-
Notifications
You must be signed in to change notification settings - Fork 193
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Require ID.me Identify proofing for all DS Logon accounts for DD access (Post DD launch) #1798
Comments
|
@Justin-Pickett , please add this to the DD post launch list of items to take care of. |
|
@erikphansen will look into this item. Will follow up if additional information is needed. |
|
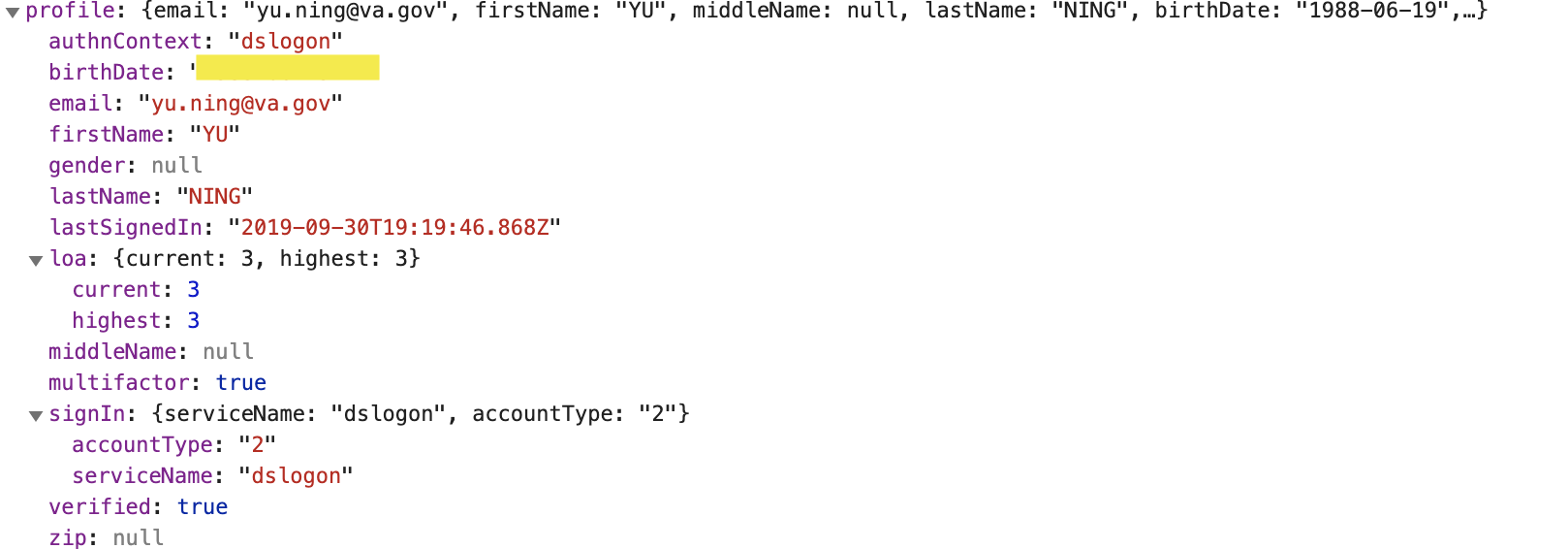
So the profile itself is gated on the user being verified: https://github.com/department-of-veterans-affairs/vets-website/blob/bd4e32db6f87b800820e8dffdda02c90f0b66414/src/applications/personalization/profile360/components/ProfileView.jsx#L93 I know nothing about DSLogon; is it possible for them to be verified without going through the ID.me ID proofing procedure? Is that what this "remote proofing of DS Logon" is that is mentioned in the ticket description? |
|
I just found the thread in Slack that is the root of this issue: https://dsva.slack.com/archives/C909ZG2BB/p1568420910001800 This change is going to be a much larger task than I had initially thought. We need to change the info we get back from the At a higher level: while we have a way to determine if a user is verified, we don't currently have a way to determine which method of verification they used. I currently know of ID.me and DS Logon verification. Maybe there are more? At any rate, the front end needs a way to determine if the user is ID.me verified. |
|
Will follow up with @annaswims on Monday regarding the feasibility of expanding the user model to include something that would indicate if the user was verified via ID.me or not. |
|
Based on a chat with Anna, we can use the
|
|
We can now safely ignore my last message. We shouldn't use |
|
This ticket should probably be turned into an epic now. It'll be a multi-team effort and might also require some new UX/design work as well. |
|
@erikphansen ill work on getting this broken up into a new Epic ticket. |
|
@lkoenigsberg will follow up on this item. Will set up a discussion for this item. |
|
Going to track design in #2844 |
|
@Justin-Pickett please turn this into the epic. We'll create design/development tickets as needed for granular tasks. |
|
@Samara-Strauss gotcha! WIll do . |
|
@lkoenigsberg — After talking with Erik and Anna, we decided that the best way to handle this would be to require DS logon user to sign in with MHV or ID.me to access direct deposit. We talked through other flows that were super complex from a technical perspective, and I think this solution makes the most sense from both a UX and technical perspective. Let me know if you have any questions. We can regroup on this on Monday if you do. @Justin-Pickett the top comment in this ticket does not need the full checklist for a project epic. Can you please clean this up? This is more of a feature instead of a product/project. We don't need to do a good portion of what's listed (user testing; UAT; reaching out to comms; etc). We really only need a centralized place to track the tickets that have to do with this feature, and for that list to be updated accordingly over time. Also, you can just type the # sign and ticket number without including the link in order to link to a ticket. You only need to hyperlink if you're linking to a ticket that is in a different repo. |
|
@Samara-Strauss okay thank you will do. |
|
I circled back with Anna to ask about the following scenario re: gating direct deposit — why someone who is DS Logon LOA3 and ID.me LOA3 wouldn't be able to access direct deposit if they logged in with DS Logon. This was her response:
So currently, we have no way of knowing a user who is logged in with DS Logon LOA3 might be also LOA3 through ID.me. That's why we can't just put a prompt on the profile for DS Logon users to verify their identity — they could do it, but we wouldn't be able to detect this on subsequent visits to the profile. In theory, I think we could talk about whether we want to add an additional check that would detect whether a user has also verified through ID.me instead of just checking for their highest level of LOA, but this is a larger question for the identity team and that kind of update seems out of scope for this project. It also doesn't seem worth it given our team's longer term strategy re: login. So, that's why we landed on this approach — we don't have to perform any extra checks or do anything technically complex and weird in order to show a prompt that tells DS Logon users to login with MHV or ID.me to update direct deposit. But we would inevitably have to do something technically weird/complex if we wanted to allow DS Logon users to login with DS logon and then access direct deposit if they were also LOA3 through ID.me. Given this, I think we should move forward with the approach to require DS Logon user login with MHV or ID.me to access direct deposit. This should cover everything we talked about today, but let me know if you have any other specific questions. |
|
Should have closed this a while ago — DEPO team decided to not move forward with this. |
Due to the direct deposit data breach, remote proofing of DS Logon was disabled.. it was very Knowledge Base Authentication heavy and prone to compromise
In addition, about 3000 DS Logon accounts associated with the breach have been disabled. Those folks will be instructed to go in person to re-enable their accounts
We need to make changes that require ID.me identity proofing for all DS Logon accounts attempting to access Direct Deposit. While putting up more roadblocks, it will help counter any already compromised accounts that were not part of the identified 3000.
Summary
If a user is logged in with DS Logon but has not done ID.me identity proofing, put the user through ID.me identify proofing flow before allowing them to access direct deposit.
Design
Build
The text was updated successfully, but these errors were encountered: