- Used to control privileged access to Azure resources
- IT Admins must ensure that authorized users have the required access to do their job.
- If a user leaves the department or company, PIM will ensure that their access is managed.
- JIT access to Azure AD and Azure Resources
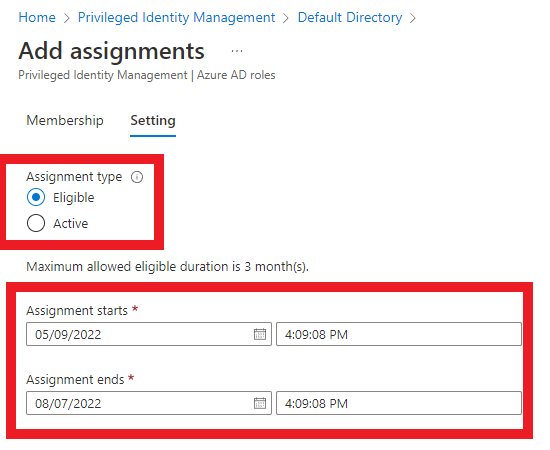
- Assign time-bound access to resources using start and end dates
- Require approval to activate privileged roles
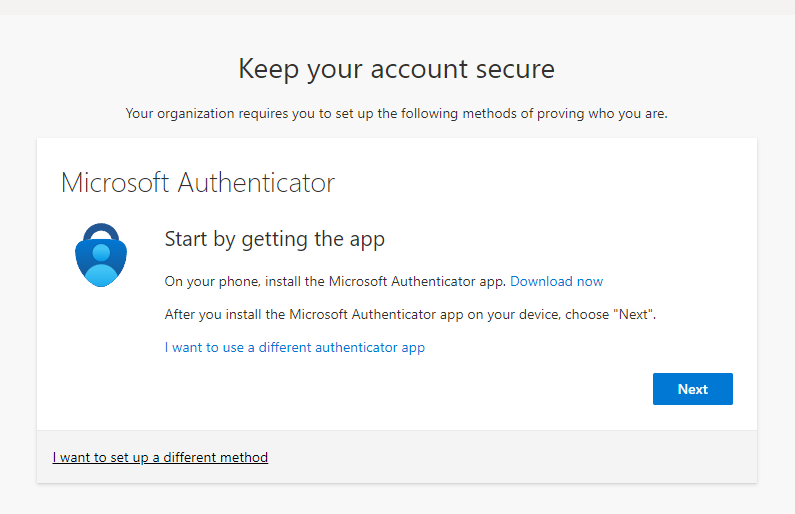
- Enfore MFA to activate any role
- Get notifications when privileged roles are activated
- Conduct User Access Reviews (UAR) to ensure users still require the roles to perform their duties
- and MORE..
- IT admins will need to log in as the Global Administrator
- Consent to using PIM
- Verify identity with MFA
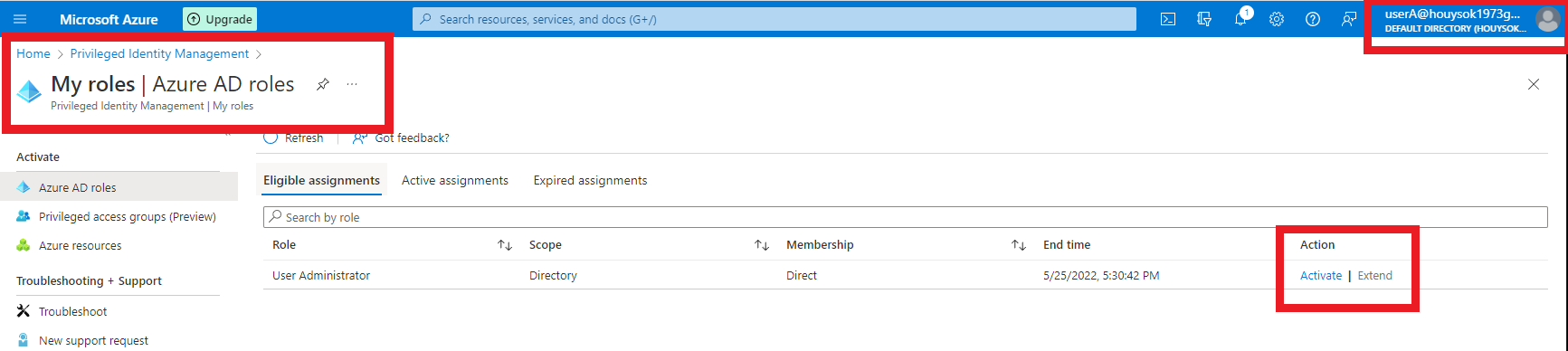
- Important ** After assigning a Azure AD role, the user must activate the role assigned to them.
- Note that IT admins can edit settings of the Azure AD role assigned to users such as limiting the time duration a user has access to a particular role or require MFA
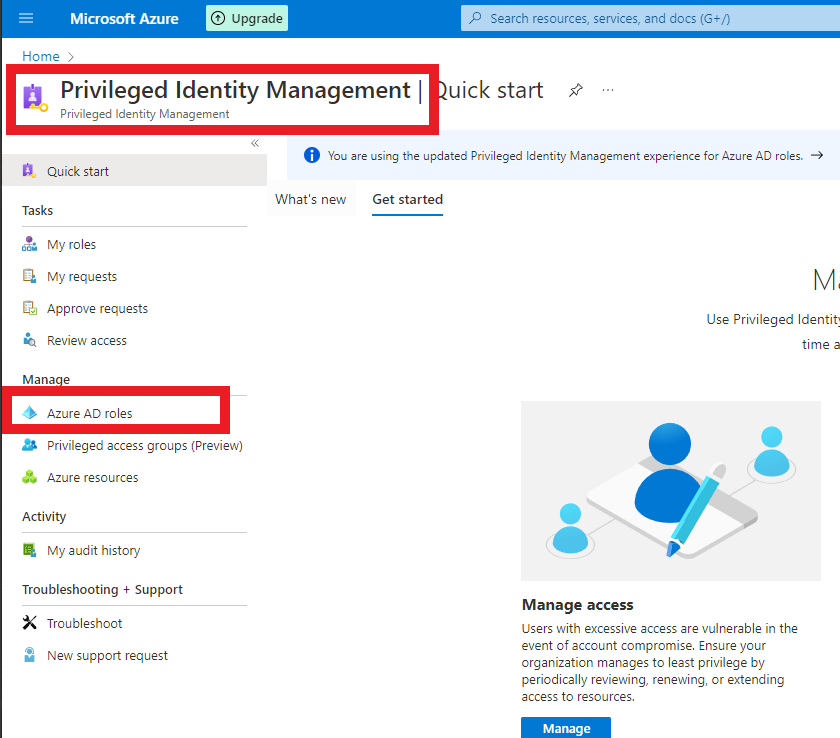
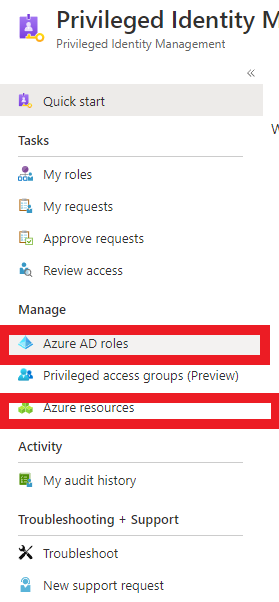
- Search for the service Privileged Identity Mananagement > Azure AD Roles > Assignments > Add assignments for your users
After a user activates a role, MFA will be required. It acts a another layer of protection for privileged roles.
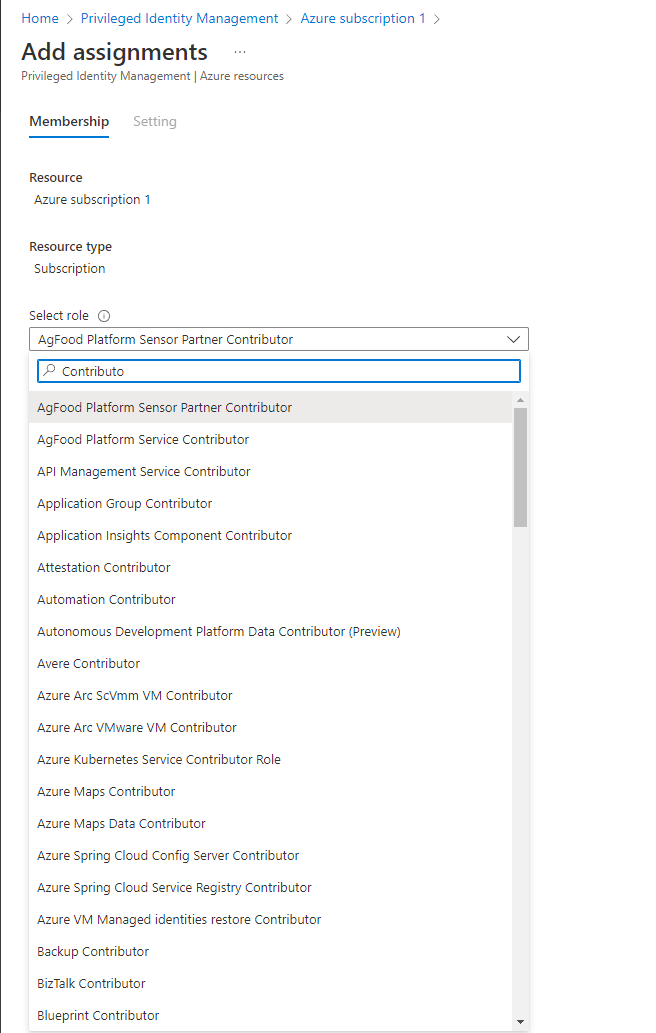
- Not only does PIM offer management for Azure AD Roles, PIM also manages RBAC roles.
- Navigate to PIM > Azure Resources > Select your resource within the subscription > Select Assignments and add the assignment
- Remember, before adding assignments for RBAC roles, IT admins may need to "Discover Resources" so that PIM can identify the resources within the Azure Subscription.
- Note that IT admins may need to select "Discover Resources" so that PIM can identigy the resources within your subscription
- "Eligible" means that the user can elevate up to the assigned role.
- The user assigned the eligible does not have the role until they activate it.
- "Active" assignment type means the user has the role. Admins can time-bound the role where the user only has it for a specified amount of time.
- PIM also offers IT admins to create User Access Reviews for particular roles.
- Navigate to Azure AD or Azure Resources
- If user selects Azure Resources, select the resource that needs an access review, then select "Access Review"
- Remember, if the Azure resource does not appear, the user must select Discover or Activate a role.