-
-
Notifications
You must be signed in to change notification settings - Fork 9.2k
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Provide ciphers list for HTTPS requests #1308
Comments
|
Let us pick and choose what version of SSL we use. curl https://www.bbva.pt/ |
|
The accepted way of doing this in Requests is to use the Transport Adapter functionality. You can see an example of doing exactly this here. |
|
@Lukasa thanks, this solves my problem. |
|
@Lukasa Thanks for the quick answer. I've looked at your post and I think it's a good start to solve my problem maybe (which is setting the ciphers, not the SSL version :p) The VerifiedHTTPSConnection wraps the socket and that's where I need to provide ciphers (this is the only way apparently). I'm not sure i'll be able to create a pool and then use it in a adapter, all without having to copy/paste existing code (I'm looking for a clean way of doing it) Many thanks again |
|
@damiengermonville you might then need to petition over at shazow/urllib3 for an easier way to pass in the ciphers to the VerifiedHTTPSConnection object. We have no clue what your code looks like, but I imagine this might make it easier. It's also something I don't believe @shazow would be that adverse to, but I'm pretty sick at the moment so it's probable that I'm wrong. :) |
|
You should already be able to select what version of SSL/TLS you want to force, iirc. Either way, I'm open to adjustments to the VerifiedHTTPSConnection object as long as they're sensible and don't significantly increase code complexity. :) |
|
@shazow I'm afraid that adjustments have to be made in VerifiedHTTPSConnection but also in urllib3/util.py ssl_wrap_socket() so it can give the ciphers argument to ssl.wrap_socket(). |
|
@damiengermonville Sounds fine. :) |
|
Hi, I had exactly the same needs, and I needed some time to find how to add the specific ciphers. So if I may, I will just add what I did so people can find it (please correct me if I am completely wrong): from requests.packages.urllib3.contrib import pyopenssl This will also be handy for people bumping into issues with the OpenSSL version of Ubuntu 14.04 and Requests 2.7 and python 2.7.6 |
|
Hi, The following worked for me! |
|
Please do not do it this way. Instead, follow the approach in this blog post and change the ciphers only for specific sites. RC4 is extremely dangerous and broken, and enabling it in the way shown in @athoik's comment will enable it for all sites, opening you up to trivial attacks. If you must allow RC4 or other removed ciphers, do so on a site-by-site basis. |
|
@Lukasa, I had to enable only the AES256-SHA in my case. I just copy / pasted the original solution. |
|
Ah, I see. In general this is still using a sledgehammer to crack a nut, and a per-host approach as discussed above is the better way to go. |
|
I am wondering why does requests provide a list of DEFAULT_CYPHERS in ssl_ when ssl already provides one. |
A number of reasons. For example:
Yes. However, Sessions are a good thing that should be used in all but the simplest of codebases, so it's a major help. And if your code is simple, you can just create a global session and change all your calls to
This represents a severe misunderstanding of how TLS works. The client and server together decide which cipher suite is used, based on the server selecting its preference from the list the client supports. The client is responsible for defending itself against the server making bad choices. Clients need to have an opinion about what ciphers are acceptable for use. If your assertion is that the client should allow whatever cipher suite the server chooses, then you are essentially saying that TLS does not serve a security purpose for you at all: it is merely an operational inconvenience. In that case I recommend you don't use HTTPS: you're just adding complexity to your work for no reason. Otherwise, the client is responsible for preventing old and badly configured servers from leaking client data.
No. Requests has a strong cultural bias towards "secure by default". Essentially, if you use Requests in the default configuration then we guarantee that you are using a configuration that is secure based on our understanding of the network threat ecosystem at the time we released. Users should not opt-in to secure configurations because that creates an ecosystem in which only those who have the knowledge to understand the risks are secure. Requests aims to ensure all our users are secure, not just those who are keeping up to date with the crypto literature. So our policy is that we will be secure, and give you opt-outs. We don't promise to make them easy: we'll let you point the gun at your foot, but we won't necessarily provide an easy switch to do it. If you have to do a little bit of work to reduce your security, then that is a reasonable trade-off for ensuring that casual users don't accidentally do it. |
|
Thank you, you are making very good points. I wish the customization would be documented in requests doc along with some troubleshooting tips, the interface is awesome but this was not a good experience... |
|
Yeah, this is an understandable concern. Generally we don't want to make things like this super easy to find just to discourage their use a bit more, which is why we've traditionally resorted to "documenting" this kind of thing in blog posts rather than inline. |
|
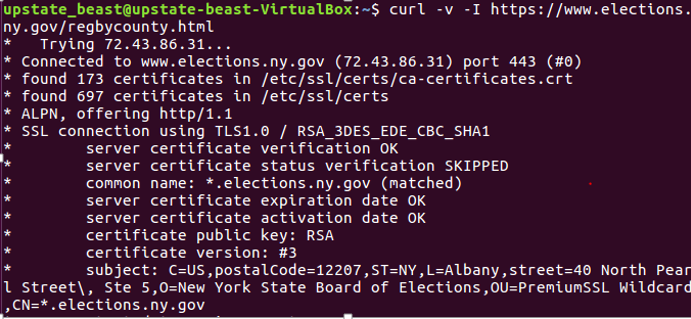
Hi, Error is on this line -> bad handshake / unexpected EOF I'm using Python 2.7.11 curl makes connection fine with TLSv1.0 and Cipher: RSA_WITH_3DES_EDE_CBC_SHA1 I've tried both the not recommended way (adding my cipher string to the DEFAULT_CIPHERS) and the preferred way from https://lukasa.co.uk/2017/02/Configuring_TLS_With_Requests/ with no luck. I think DES-CBC3-SHA is the string I need to be adding, not sure if I'm just doing it wrong (I've tried concatenating to the end of CIPHERS making it the only string in CIPHERS etc.) or if there's something else going on here. And the output (bad handshake) Thanks in advance! |
|
I've been bitten in the ass by this "bug" as well. It's not a requests issue, nor do the requests authors really care whether or not their documentation RE old ciphers is actually useful, given that it's unreasonable to detect if and when the provided OpenSSL support libraries have the ciphers you ask for. After a lot of work, I've determined that if you have pyOpenSSL installed, you will get the above error. At least, that's what I thought the issue was, given that removal of pyOpenSSL magically allowed your test program to pass (after enabling the DES-CBC3-SHA cipher) Looking closer, I determined that the binary assets being distributed for If you can prove that the following works with your desired cipher: Then you may be able to just I was able to make everything "work" (even with pyOpenSSL) by making a usable |


Hi,
Since Python 2.7, the ssl module implements a way to provide a list of available ciphers to the SSL object [1]. It would be nice if this feature could be reflected in Requests (and in Urllib3 as well).
I know it's not a key feature but some web servers have a Long Handshake intolerance [2] and that makes tools (and Python scripts) based on OpenSSL 1.0.1+ fail at handshake. A workaround is to provide a short list of ciphers instead of all the available ones.
I've looked into trough the Requests documentation and googled. I didn't find a way to do it. Maybe there is, if so i would appreciate a bit of help :)
Thanks !
[1] http://docs.python.org/2/library/ssl.html?highlight=ssl#ssl.wrap_socket
[2] https://github.com/ssllabs/research/wiki/Long-Handshake-Intolerance
The text was updated successfully, but these errors were encountered: