Enter into the deployment folder and execute helmfile with the envieronment (dev or nuc in this repo). Sample
helmfile --environment dev apply
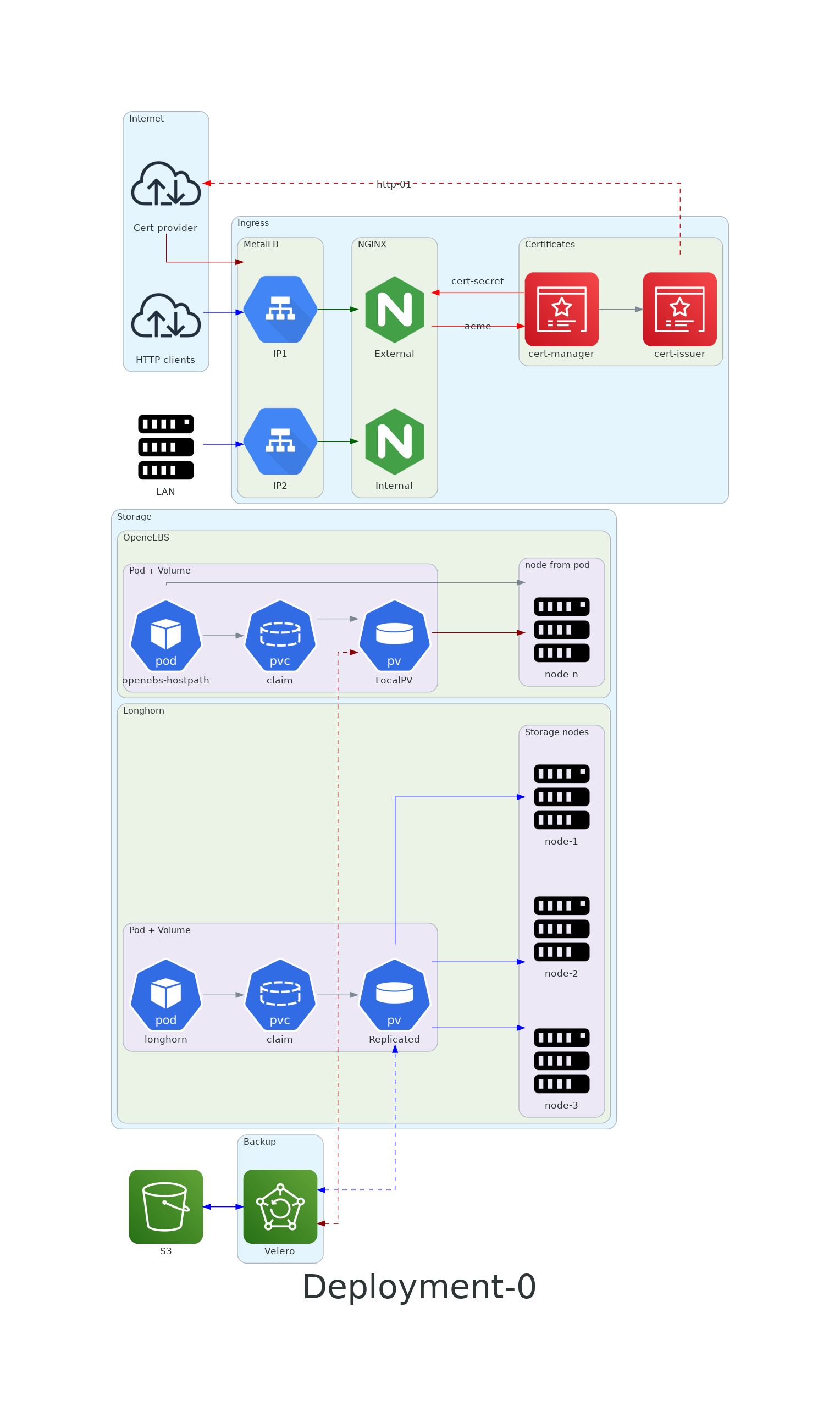
For the incomming traffice it will install a metallb load balancer, 2 nginx ingress controler (one for LAN and one for WAN, this one also with a cert manager for ssl certs).
For storage will install OpenEBS for localPV and Longhorn for distributed storage, also velero for backups.
The passwords are stored under SOPS, helmfile will automatically decode it with PGP (if you are cloning the repo you would have to make your own secrets file with your own certificate).
Some tools used for the deployment
| Tool | Small description |
|---|---|
| kustomize | Configuration management for k8s yaml files |
| SOPS | Secret management using PGP |
| helmfile | Deploy automation for depending on env using helm files |
| helmify-kustomize | Using kustomize as a helm file |
brew install kustomize
brew install sops
Setting up SOPS with PGP: https://gist.github.com/twolfson/01d515258eef8bdbda4f#setting-up-sops-with-pgp
Generate gpg key: gpg --full-generate-key
To encrypt or decrypt using PGP, specify the PGP fingerprint in the -p flag or in the SOPS_PGP_FP environment variable.
To add a new pgp key to the file and rotate the data key
$ sops -r -i --add-pgp '{{ fingerprint }}' example.yaml
brew install helmfile
helm plugin install https://github.com/zendesk/helm-secrets
Helm entrypoint even if using kustomize: https://github.com/roboll/helmfile#helmfile--kustomize