gossm is interactive CLI tool that you should select server in AWS and then could connect or send files your AWS server using start-session, ssh, scp under AWS Systems Manger Session Manager.
gossm is interactive CLI tool that is related AWS Systems Manger Session Manager.
It can select a ec2 server installed aws-ssm-agent and then can connect its server using start-session, ssh.
As well as files can send using scp.
If you will use gossm tool, this mean there will no need to open inbound 22 port in your ec2 server when is using ssh or scp command.
Because AWS Systems Manger Session Manager is using ssh protocol tunneling.
Additionally Features
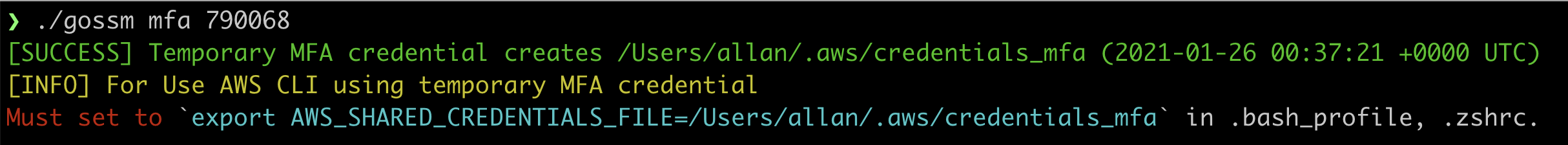
mfacommand has added. this command is to authenticate through AWS MFA, and then to save issued a temporary credentials in $HOME/.aws/credentials_mfa. (default expired time is after 6 hours)
You should export global environment, such asexport AWS_SHARED_CREDENTIALS_FILE=$HOME/.aws/credentials_mfa.
With completed, you can execute aws cli and gossm conveniently without mfa authenticated.
Refer to detail information below.
- [required] Your ec2 servers in aws are installed aws ssm agent.
EC2 severs have to apply AmazonEC2RoleforSSM iam policy.
If you would like to use ssh, scp command using gossm, aws ssm agent version 2.3.672.0 or later is installed on ec2. - [required] aws access key, aws secret key
- [required] ec2:DescribeInstances, ssm:StartSession permission, ssm:DescribeInstanceInformation
- [optional] It's better to possibly get to additional permission for ec2:DescribeRegions, ssm:TerminateSession
Support x86_64
# homebrew
$ brew tap gjbae1212/gossm
$ brew install gossm
# mac
$ wget https://github.com/gjbae1212/gossm/releases/download/v1.3.0/gossm_1.3.0_Darwin_x86_64.tar.gz
# linux
$ wget https://github.com/gjbae1212/gossm/releases/download/v1.3.0/gossm_1.3.0_Linux_x86_64.tar.gz
# window
$ wget https://github.com/gjbae1212/gossm/releases/download/v1.3.0/gossm_1.3.0_Windows_x86_64.tar.gz| args | Description | Default |
|---|---|---|
| -c | (optional) aws credentials file | $HOME/.aws/credentials |
| -p | (optional) if you are having multiple aws profiles in credentials, it is name one of profiles | default |
| -r | (optional) region in AWS that would like to connect | |
| -t | (optional) instanceId of server in AWS that would like to connect |
If your machine don't exist $HOME/.aws/.credentials, have to pass -c args.
# credentials file format
[default]
aws_access_key_id = AWS ACCESS KEY
aws_secret_access_key = AWS SECRET KEY
-r or -t don't pass args, it can select through interactive CLI.
$ gossm start -e must pass args when is using scp.
-e args is command and args when usually used to pass ssh or scp.
# ssh(if pem is already registered using ssh-add)
$ gossm ssh -e 'user@server-domain'
# ssh(if pem isn't registered)
$ gossm ssh -e '-i key.pem user@server-domain'
# ssh(if pem is already registered using ssh-add and don't pass -e option) -> select server using interactive cli
$ gossm ssh
# ssh(if pem isn't registered and don't pass -e option) -> select server using interactive cli
$ gossm ssh -i key.pem
# scp(if pem is already registered using ssh-add)
$ gossm scp -e 'file user@server-domain:/home/blahblah'
# scp(if pem isn't registered)
$ gossm scp -e '-i key.pem file user@server-domain:/home/blahblah'
-e required args, it is a parameter for execute to command on selected servers.
# It is to execute a command("uptime") on selected multiple servers, waiting for a response on its result.
$ gossm cmd -e "uptime" ex)
-deadline it's to set expire time for temporary credentials. default is 6 hours.
-device it's to set mfa device. default is your virtual mfa device.
$ gossm mfa <your-mfa-code>Must set to export AWS_SHARED_CREDENTIALS_FILE=$HOME/.aws/credentials_mfa in .bash_profile, .zshrc.
ex)
This project is following The MIT.