New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Cloud MISP #2548
Cloud MISP #2548
Conversation
764605b
to
f3cba3e
Compare
|
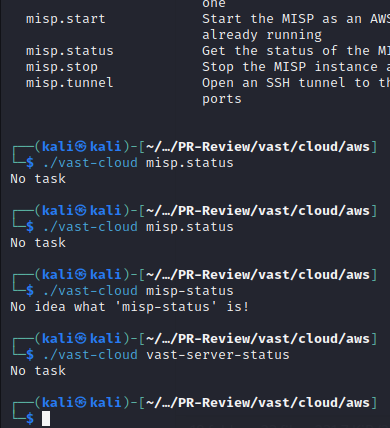
After deployment, it is really unclear what is going on in the environment. Would it be possible to give a summary text on Additionally, what could be the reason for the output below? I expected the output to align with the test case. The screenshot is after the successful deployment. Instead of "No Task", a bit more verbose output could be shown. |
Not sure how an ID/IP would be useful as the services are not exposed to the outside world. The ports are displayed when you start the tunneling, but maybe clearer listing would be nice.
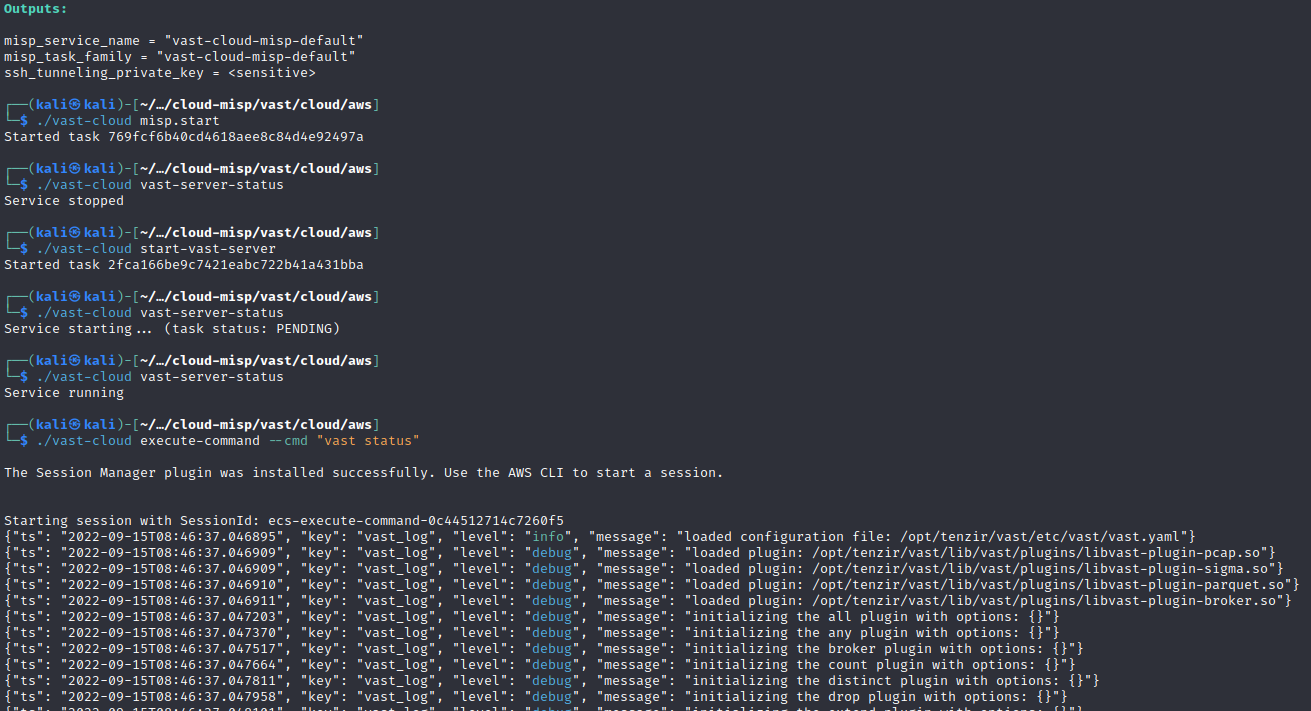
Did you start the service with |
|
I made service status messages more explicit and fixed the integration test. Could you take a new look at it @KaanSK ? |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Deployment works, and I'm able to both connect to MISP and log in.
TODO: - misp persistence - list endpoints using tf outputs - test different services - streamline security groups - add basic auth?
2305df1
to
e86b3e4
Compare
This PR adds a MISP plugin to the cloud deployment
📝 Reviewer Checklist
Review this pull request by ensuring the following items:
Also note that:
VASTCLOUD_REBUILD=1 ./vast-cloud)sudocapabilities to the user in the CLI image to enable binding low portscloud/aws/resources/configs/misp/configs where copied over from our internal repo. These should probably be shared with the docker-compose configs once they are ported to this repository