-
Notifications
You must be signed in to change notification settings - Fork 368
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Set X-XSS-Protection to 1; mode=block. #1550
Conversation
bbf5e97
to
4015ef2
Compare
|
Address #1543. This is a very small PR, so if this is deemed unnecessary, happy to discard. |
|
Pinging @MaxGabriel. I haven't been following this header in general. @StevenXL if you feel comfortable with this, you should also feel free to merge. |
|
I think that this is unlikely to cause anyone any problems, and improves the situation over the browser default by making the error more visible. I'd say it's good to merge. |
|
@MaxGabriel thanks. |
|
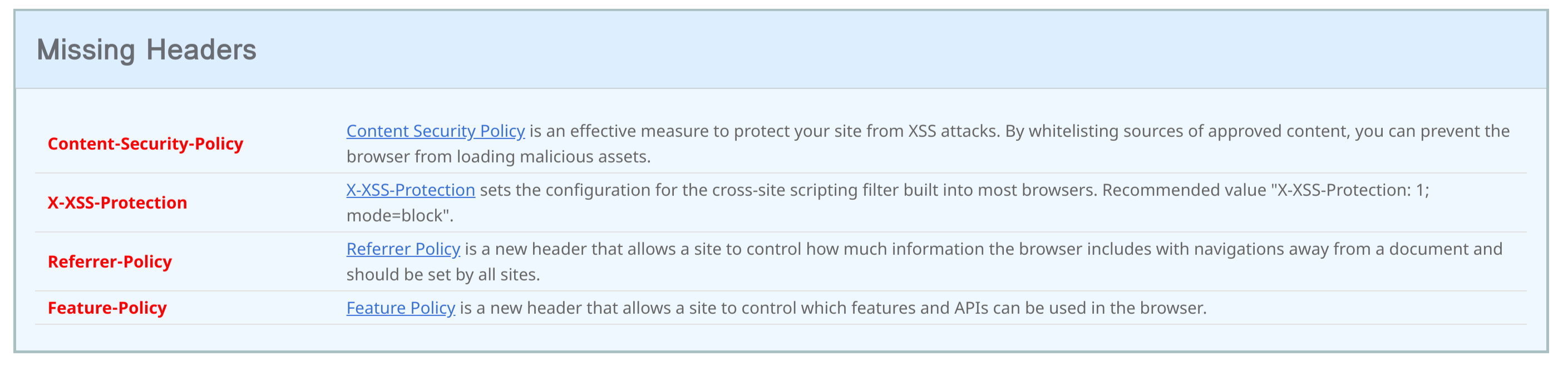
As a side note, there are other security headers that people should maybe add: They require more custom configuration compared to this one, so there isn't much a library would really be adding, but it would be cool if Yesod developers were encouraged to use them. Not sure the best way to do that—maybe some commented out code in the scaffolding? |
|
Content-Security-Policy is a huge win for security, because you can whitelist where things like Javascript can be loaded from, and prevent XSS from harming you. This is our CSP used for a single-page app (with some additions coming from headers): I think the best default you could give is to set the Referrer-Policy seems fine to enable by default. My understanding is that it improves privacy by concealing where users came from. Feature-Policy is brand spanking new, like it was on Hacker News last week, so I don't have comments on it really. But it lets you do things like prevent the site from vibrating the phone |
|
I'm a bit late to the party here, but found this issue via the changelog. It's a chrome specific feature, but would be nice to allow setting a You can combine both block and report, so it would look something like this: |
Before submitting your PR, check that you've:
@sincedeclarations to the Haddocks for new, public APIsAfter submitting your PR: