Summary
There is a Path Traversal vulnerability in Attachments that allows attackers with admin rights to upload malicious files to other locations of the web root.
PoC
-
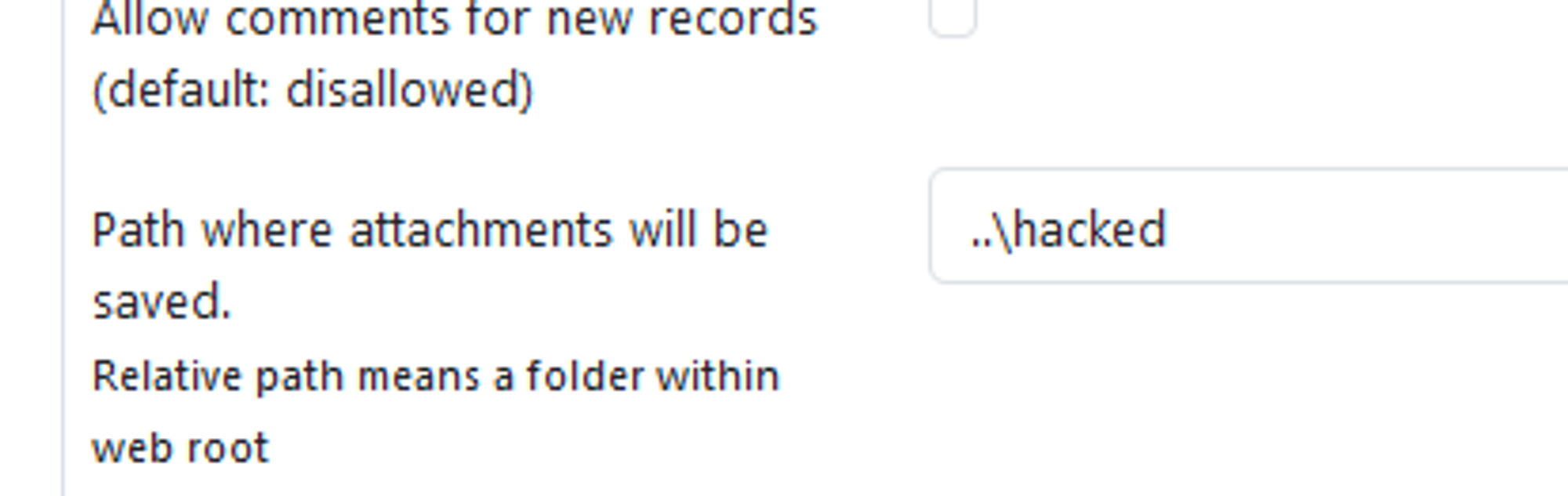
In settings, the attachment location is vulnerable to path traversal and can be set to e.g ..\hacked
-
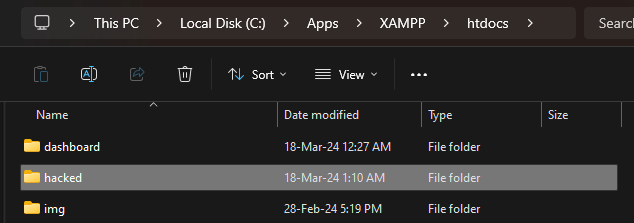
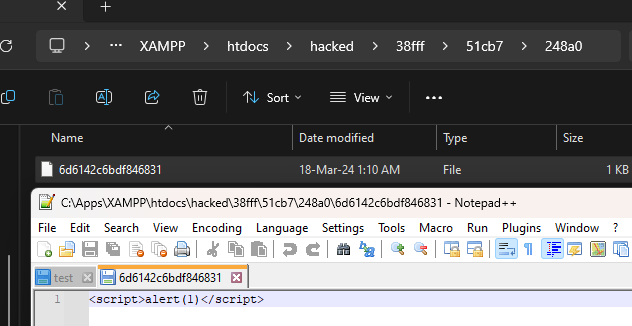
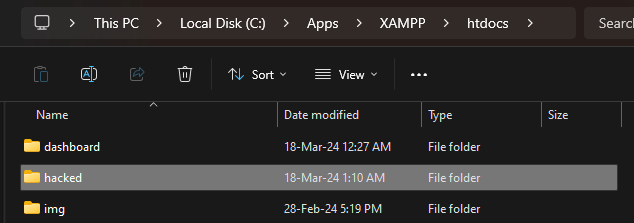
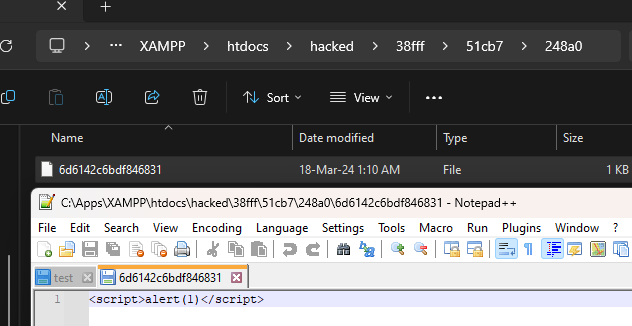
When the above is set, attachments files are now uploaded to e.g C:\Apps\XAMPP\htdocs\hacked instead of C:\Apps\XAMPP\htdocs\phpmyfaq\attachments
-
Verify this by uploading an attachment and see that the "hacked" directory is now created in the web root folder with the attachment file inside.
Impact
Attackers can potentially upload malicious files outside the specified directory.
References
Summary
There is a Path Traversal vulnerability in Attachments that allows attackers with admin rights to upload malicious files to other locations of the web root.
PoC
In settings, the attachment location is vulnerable to path traversal and can be set to e.g ..\hacked
When the above is set, attachments files are now uploaded to e.g C:\Apps\XAMPP\htdocs\hacked instead of C:\Apps\XAMPP\htdocs\phpmyfaq\attachments
Verify this by uploading an attachment and see that the "hacked" directory is now created in the web root folder with the attachment file inside.
Impact
Attackers can potentially upload malicious files outside the specified directory.
References