Elytron replacement in Quarkus distribution of Keycloak #19281
Replies: 8 comments 17 replies
-
I think we should support any type supported by W.r.t. FIPS, if running in the approved mode you are only left with the In the future, we should also consider supporting PKCS#11 as per #17099. |
Beta Was this translation helpful? Give feedback.
-
What about: The motivation is that |
Beta Was this translation helpful? Give feedback.
-
Tha means we now have |
Beta Was this translation helpful? Give feedback.
-
How users are going to generate the encrypted value? Do we want a command in our CLI or additional script? Perhaps we want something like: Not sure about the command position/name but I hope you get the idea. Behind the scenes, we encrypt the value and make it ready for use as an option value. We might also expose specific options to configure how to encrypt the value (e.g: alg). Looks |
Beta Was this translation helpful? Give feedback.
-
|
I'd go with the idea of using SmallRye as mentioned by Pedro, unless we have a strong argument for it. From my understanding, SmallRye with Jasypt provides support for AES/GCM, while Keycloak Vault supports PBEWithMD5AndDES, considered an insecure password-based key derivation function. |
Beta Was this translation helpful? Give feedback.
-
|
Hello, |
Beta Was this translation helpful? Give feedback.
-
|
Hello everyone, I went through the discussion, gathered the feedback and polished the final PR[1] accordingly. [1] #19644 |
Beta Was this translation helpful? Give feedback.
-
|
Hi all, here's the PR[1] that covers the remaining part - integration with the SmallRye Keystore, which allows us to use a Java keystore as a Quarkus config source as well as masking plaintext properties in config files. Feedback is very welcomed, so PTAL and let me know. Thanks! [1] #20375 |
Beta Was this translation helpful? Give feedback.
-
PoC: https://github.com/Pepo48/keycloak/tree/file-vault
OVERVIEW
The previous and now removed WildFly distribution provided a built-in vault provider that reads secrets from a keystore-backed Elytron credential store. This was used both by our Keycloak Vault implementation, as well as encrypting config values in standalone.xml. Since Keycloak is now based on Quarkus, the ElytronCS provider, which was implemented as a WildFly extension, can’t be supported anymore.
Naturally, we feel the responsibility to come up with an alternative solution and currently there seem to be two options that we can leverage - SmallRye Keystore and Keycloak Vault.
Adding an integration with upcoming SmallRye Keystore
smallrye/smallrye-config#833
Affected scope: Quarkus properties
Similar functionality in WildFly distribution: elytron-tool.sh script (to mask plaintext property values)
SmallRye Keystore offers to us two main features:
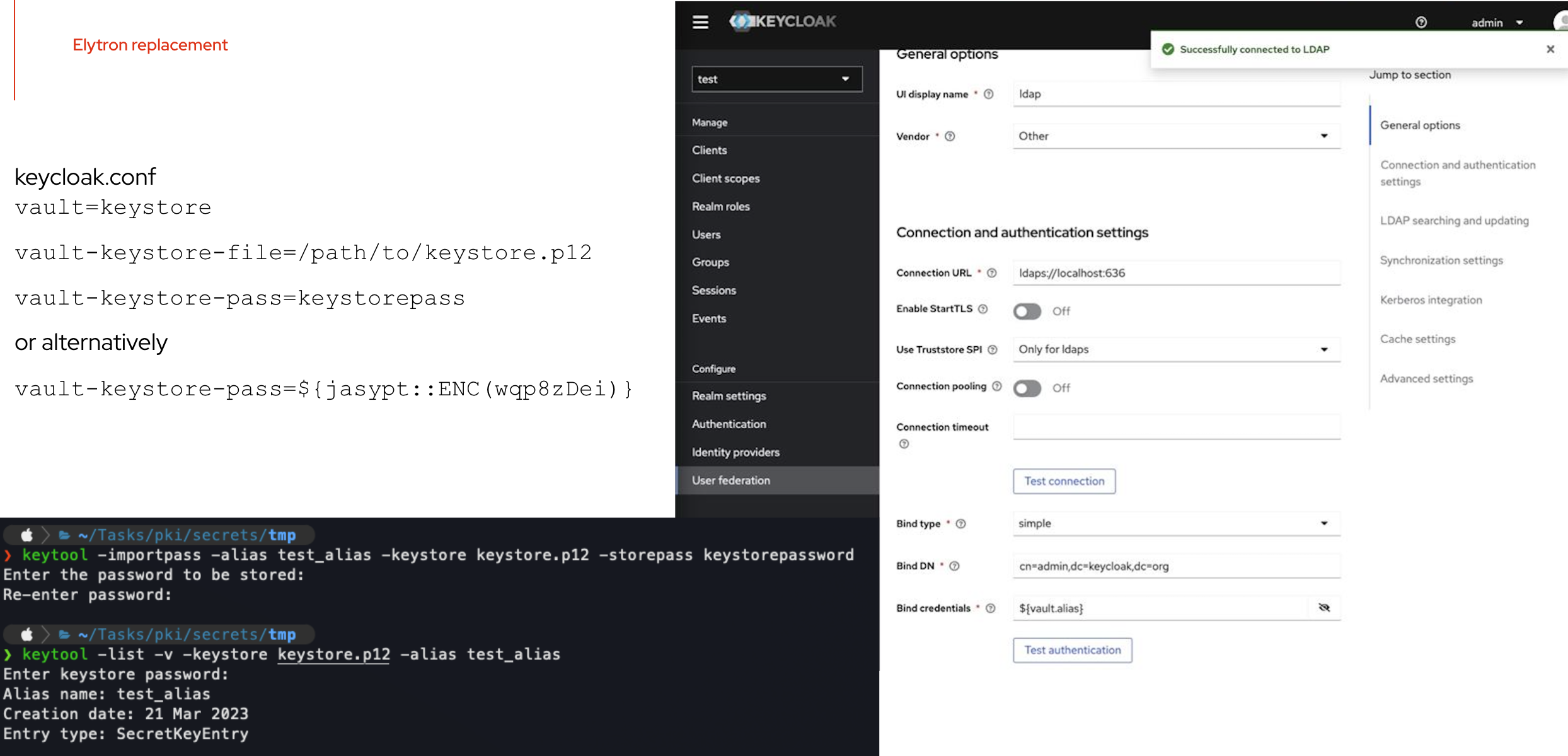
.conf/.propretiesfiles - this is the most requested feature by the community, SmallRye provides us with couple SecretKeysHandler implementations, in the PoC and the examples below we useJasypt.Resulting Java Keystore config file can then be created like:
Alternatively, encrypting plain text values using jasypt:
Tests for demonstrating the proposed behavior can be found here.
Adding Keycloak (Java) Keystore Vault
Affected scope: Keycloak realm
Similar functionality in WildFly distribution: Plaintext vault, Elytron Credential Store
The idea was to use the existing Vault interface in order to implement Java Keystore Vault SPI. The current implementation of the provider expects imported password in the keystore, e.g. via following command:
This by default stores the password in a form of generic PBEKey (password based encryption) within SecretKeyEntry using PBEWithMD5AndDES as the algorithm.
Values in the Vault can then be accessed in Realm as (assuming using the
REALM_UNDERSCORE_KEYkey resolver):${vault.realm-name_alias}.E.g. given a Realm is named “my-realm” and an alias is named “test_alias”, the resulting placeholder is
${vault.my-realm_test_alias}.The current implementation results into following behavior:
Tests for demonstrating the proposed behavior can be found here.
Proposed property nomenclature:
We intentionally decided to distinguish between the two sets of properties, simply because there are relevant use-cases, where a user may want to use both. For example, Keycloak provides a way to use Kubernetes secrets for multiple purposes within a Keycloak realm (see the Available integrations section). For these integrations though, the usage of (plain-text) file-based vault is required. At the same time, a user still may want to leverage the functionality that SmallRye Keystore offers. Our current perception is that these two approaches are not mutually exclusive and they can coexist together. Hence the following proposal:
SmallRye keystore
Keycloak vault
Things to consider:
JKS and JCEKS keystore types are not recommended to use for quite some time[1][2][3]. Do we want to give users an opportunity to choose even less secure Keystore formats, or should we be more opinionated? PKCS#12 is the default recommended format since Java 9[4]. We should also consider FIPS support.
[1] https://www.ndss-symposium.org/wp-content/uploads/2018/02/ndss2018_02B-1_Focardi_paper.pdf
[2] https://neilmadden.blog/2017/11/17/java-keystores-the-gory-details/
[3] https://www.youtube.com/watch?v=viOds2uniC0&list=PLA-8aGQm6tkJgHnLcTyKo_4Qmhc6it5AF&index=1
[4] https://openjdk.org/jeps/229
Beta Was this translation helpful? Give feedback.
All reactions