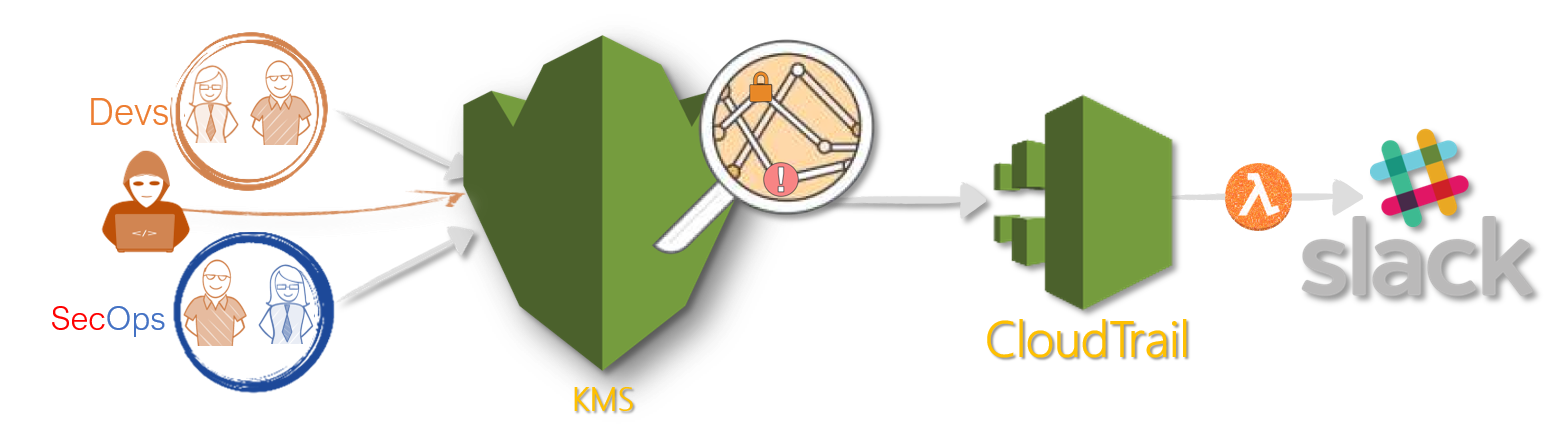
A simple lambda function to monitor certain KMS events through cloudtrail and notify users or security team through slack.
Follow this article in Youtube
-
We will need the following pre-requisites to successfully complete this activity,
Cloudtrail- Get help here to setup cloudtrail- IAM Role - i.e
Lambda Service Role- with managed permissions Get Help for setting up IAM RoleAWSLambdaBasicExecutionRole- To allow Lambda to log events
-
- The python script is written(and tested) in
Python 3.7. Copythe code fromserverless-kms-sentryin this repo to the lambda function- Optional: Add slack
SLACK_WEBHOOK_URLin the environment variable Savethe lambda function
- The python script is written(and tested) in
-
Goto the Cloudwatch Dashboard, We are going to use
Event Rules- Choose
Create a new Rule - For
Event Source- ChooseEvent pattern- For
Service, Choose/TypeKMS - For
Event Type, ChooseAWS API Call via CloudTrail - Choose
Specific Operation(s)- Add three operations
CreateAlias,DeleteAlias,DisableKey
- Add three operations
- For
- For
Target, ChooseLambda Function- From dropdown select your Lambda Function Name
- In the bottom,
Configure Details - Fill the
Rule Name&Rule Description- Make sure it is Enabled
EnableTrigger byCheckingthe box- Click
Save
Now your lambda function should be triggered when ever there is a KMS event
- Choose
-
Testing the solution Create a new alias for an existing key or delete an key, you should be getting the message in Slack(if configured). If not use the sample event in the repo to test.