-
Notifications
You must be signed in to change notification settings - Fork 13.8k
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Apache Tika CVE-2018-1335 RCE #11653
Conversation
|
I believe @sgonzalez-r7 may have been looking into this, as per #11556 |
|
Yes, @sgonzalez-r7 was assigned and has been working on it. Oops. |
| 'Author' => | ||
| [ | ||
| 'h00die', # msf module | ||
| 'David Yesland @Daveysec', #edb submission |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
No Twitter handles yet.
|
Shoot, I didn't look before leaping. Sorry @sgonzalez-r7 |
|
@h00die, I'm a bit bummed. It was gonna be my first Metasploit module. If you closed the PR on my account, please don't. It would be a waste of perfectly good code. |
|
@h00die, I can even review/land it since I already have the target setup :) |
|
It's NBD. Let's flip it. You make the module and docs, and since I have a test env I can land it! I'm pretty positive you'll come up with something much better and more reliable than what I put together anyways. |
|
|
||
| def exploit | ||
| pay = cmd_psh_payload(payload.encoded, payload_instance.arch.first, remove_comspec: true) | ||
| pay = pay.gsub(/"/, '\"') # RIP use_single_quote=true |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Is this broken?
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
There are like 4 modules that have use_single_quote=true. It wasn't in the library, nor did it make a difference in the code. I did see an issue/pr that mentioned it being removed, forgot who did/wrote it though
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
You mean use_single_quotes?
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
You didn't remove this, @sempervictus?
https://github.com/rapid7/rex-powershell/search?q=use_single_quotes
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
yea, forgot the s on the end.
https://github.com/rapid7/metasploit-framework/search?q=use_single_quotes&unscoped_q=use_single_quotes
I saw it passed as a parameter, and in a hash. Tried both, printing to screen and didn't see a difference. Never thought to check rex-powershell since this is my first time working with PSH.
I saw #9132 (comment) and thought it had been removed
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Gone in #8728. Try wrap_double_quotes. Might want to fix the regressions introduced.
| }, | ||
| 'License' => MSF_LICENSE, | ||
| 'Privileged' => false, | ||
| 'Platform' => 'win', |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I know this was written for Windows, but is there any reason a Unix system couldn't be targeted?
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Not sure. it calls a .exe on windows and passes params to it. If the .exe equivalent on linux has the same parameters, there's a good chance the flags would match. All the documentation was for windows.
Devils in the details. I thought about getting this written first, then if time permitted (most likely wouldn't) going back to see if it works for additional OSes
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Easily tested. I wanted someone to look into that. cc @sgonzalez-r7
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I know this was written for Windows, but is there any reason a Unix system couldn't be targeted?
I did a little testing on Unix when working on this and was only able to break out of the command on Windows. The command in the end looks like "injected.exe"originalcommand some args here. The way Windows interprets double quotes is what lets the injection happen. Does not mean it is not possible just what I found.
|
@sgonzalez-r7: I've reviewed this lightly. Do with it what you will for your PR. I suggest investigating Unix support. |
|
@sgonzalez-r7 any word on when you'll tika stab at this? |
|
@sgonzalez-r7 ping, just checking in since its been a month, didn't know if this made it to the priority list yet or not |
|
@h00die , thanks for the ping. I'll be putting this at the to of my priority list this week. I did try verifying your implementation on a Win 7 VM with no luck. Running |
|
Any more updates @sgonzalez-r7 ? At this point i'm leaning towards re-opening this PR so there's at least something in the framework. |
|
Go ahead and re-open your PR and run with it. |
Handle nil error code and fix version extraction based on both of the possible Apache Tika return pages.
|
I PR-ed a few changes to your branch. |
Tika module updates, check and CmdStager
|
My weak guess on why this isn't working now is either some sort of sandboxing, or the env isn't supporting |
|
I tested the changes on Win10 x64 v1703. |
|
Haven't forgotten about this, just wanted to get the hashcat and brocade testing done first |
|
Originally I thought it was a psh thing, I was starting java via PSH, and in that psh if I Also tried on my win10 1709, same results. @jrobles-r7 can you re-try this and see if its working for you? |
|
@h00die I tested the latest commit on Win10 1803. The module worked for me. I tested with tika launched from cmd.exe and psh. Both were successful. |
|
Windows 10 (running as admin from cmd) tika 1.14 java 1.80_211 no firewall, no AV: I tried a fresh checkout from the PR and still, nothing. Tried a messagebox payload, never popped. Checked the |
|
i see about taking a look more this weekend at the difference in the PUT requests to see if its something obvious, or what is going on here |
|
If you breakpoint on CreateProcess, does it hit at all? If it doesn't, there is something wrong on the Java level. If it does, there is something wrong on the OS level. I also make that sound very obvious... |
|
Some interesting things during testing. What I'm finding is that this module, and the POC work on 1.17, and 1.17 ONLY. I was unable to get the POC nor this module to work (out of the box) on <1.17 or 1.18 (which isn't vulnerable, so this is expected). |
|
I think that sounds reasonable. |
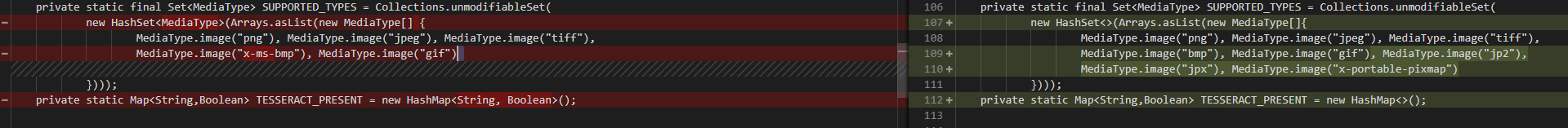
Was looking into this a bit and looks like you are correct I was able to get the POC to work on 1.16 and 1.17 but not 1.14. I think the issue is 1.14 does not look like it had support for jp2 which the exploit relies on... |
|
confirmed 16 and 15 are exploitable as well, so coverage is 15-17. Lucky guess on 14! Will update the module to accept all that and should be done in an hour or so! |
|
@jrobles-r7 / @wchen-r7 should be ready to go! |
|
Release NotesThe apache_tika_jp2_jscript module has been added to the framework. It targets CVE-2018-1335 and exploits a command injection vulnerability in Apache Tika v1.15-v1.17 on Windows. The vulnerability occurs when OCR is specified in the request, which allows command line parameters to be passed to the host. |
|
Thanks for the contribution and testing @h00die and @DaveYesland |
Fixes #11556
This module exploits an RCE in Apache Tika v 1.7-1.17.
Its Extremely simple, I simply ported the python module to ruby and the framework.
@DaveYesland if you wanted different attribution in this, let me know.
Install is easy, install java, download the sever jar
java -jar <server.jar> -h <ip>.Verification
msfconsoleuse exploits/windows/http/apache_tika_jp2_jscriptset rhostexpoit