Important
Powerpipe is now the preferred way to run this mod! Migrating from Steampipe →
All v0.x versions of this mod will work in both Steampipe and Powerpipe, but v1.0.0 onwards will be in Powerpipe format only.
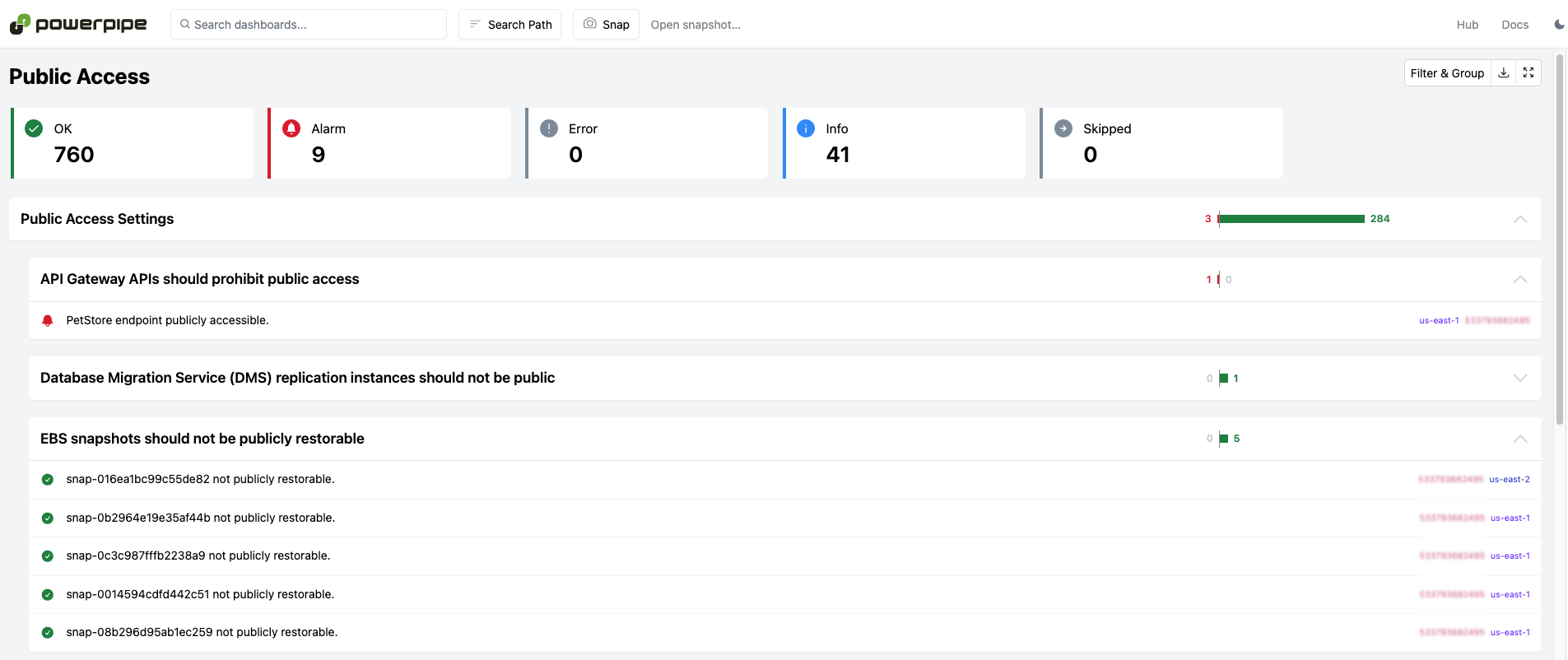
An AWS perimeter checking tool that can be used to look for resources that are publicly accessible, shared with untrusted accounts, have insecure network configurations, and more.
Install Powerpipe (https://powerpipe.io/downloads), or use Brew:
brew install turbot/tap/powerpipeThis mod also requires Steampipe with the AWS plugin as the data source. Install Steampipe (https://steampipe.io/downloads), or use Brew:
brew install turbot/tap/steampipe
steampipe plugin install awsSteampipe will automatically use your default AWS credentials. Optionally, you can setup multiple accounts or customize AWS credentials.
Finally, install the mod:
mkdir dashboards
cd dashboards
powerpipe mod init
powerpipe mod install github.com/turbot/steampipe-mod-aws-perimeterStart Steampipe as the data source:
steampipe service startStart the dashboard server:
powerpipe serverBrowse and view your dashboards at http://localhost:9033.
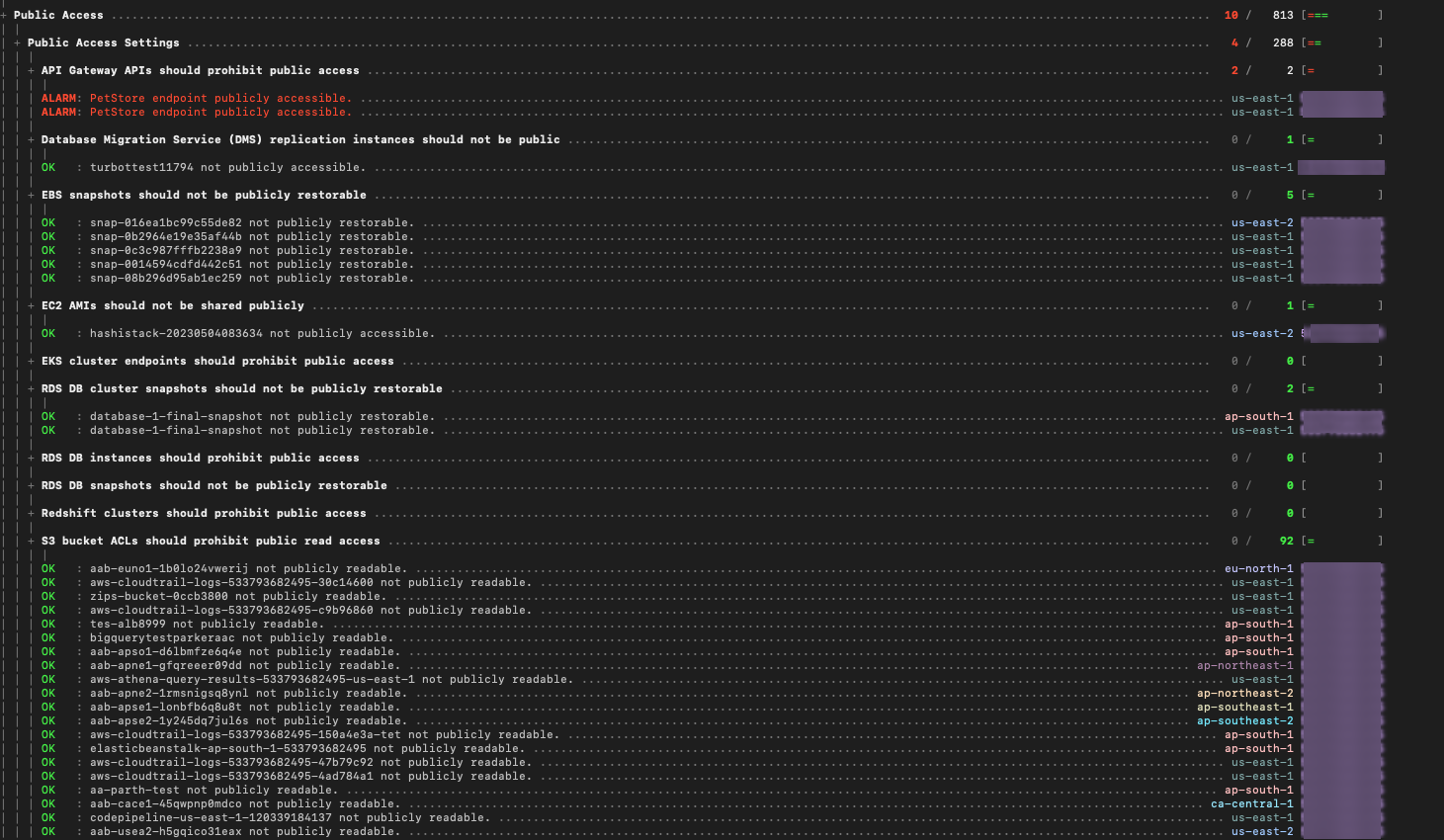
Instead of running benchmarks in a dashboard, you can also run them within your
terminal with the powerpipe benchmark command:
List available benchmarks:
powerpipe benchmark listRun a benchmark:
powerpipe benchmark run public_accessRun a specific control:
powerpipe control run ec2_instance_ami_prohibit_public_accessDifferent output formats are also available, for more information please see Output Formats.
Several benchmarks have input variables that can be configured to better match your environment and requirements. Each variable has a default defined in its source file, e.g., perimeter/shared_access.sp, but these can be overwritten in several ways:
It's easiest to setup your vars file, starting with the sample:
cp steampipe.spvars.example steampipe.spvars
vi steampipe.spvarsAlternatively you can pass variables on the command line:
powerpipe benchmark run shared_access --var='trusted_accounts=["123456789012", "123123123123"]'Or through environment variables:
export PP_VAR_trusted_accounts='["123456789012", "123123123123"]'
powerpipe control run ram_resource_shared_with_trusted_accountsThese are only some of the ways you can set variables. For a full list, please see Passing Input Variables.
The benchmark queries use common properties (like account_id, connection_name and region) and tags that are defined in the form of a default list of strings in the variables.sp file. These properties can be overwritten in several ways:
It's easiest to setup your vars file, starting with the sample:
cp steampipe.spvars.example steampipe.spvars
vi steampipe.spvarsAlternatively you can pass variables on the command line:
powerpipe benchmark run public_access_settings --var 'common_dimensions=["account_id", "connection_name", "region"]'Or through environment variables:
export PP_VAR_common_dimensions='["account_id", "connection_name", "region"]'
powerpipe control run eks_cluster_endpoint_prohibit_public_accessThis repository is published under the Apache 2.0 license. Please see our code of conduct. We look forward to collaborating with you!
Steampipe and Powerpipe are products produced from this open source software, exclusively by Turbot HQ, Inc. They are distributed under our commercial terms. Others are allowed to make their own distribution of the software, but cannot use any of the Turbot trademarks, cloud services, etc. You can learn more in our Open Source FAQ.
Want to help but don't know where to start? Pick up one of the help wanted issues: