Welcome to the MASTG Hacking Playground which is part of the OWASP Mobile Application Security (MAS) project.
The MASTG Hacking Playground is a collection of educational iOS and Android mobile apps, that are intentionally build insecure in order to give practical guidance to developers, security researches and penetration testers.
The vulnerabilities used in these apps come from the OWASP Mobile Application Security Testing Guide (MASTG) (there is no full coverage of all test cases, but you are invited to extend the current coverage).
- A developer can identify vulnerable code in the provided apps and can see the implications and risks if such patterns are used and can look for the best practices in the MASTG to mitigate the vulnerabilities.
- Penetration testers / security researchers can identify bad practices, dangerous methods and classes they should look for when assessing a mobile app and can gain more knowledge through the information provided in the MASTG.
- It is also encouraged to use these apps for education purpose during trainings and workshops.
If you want to contribute, please contact us. For instance, you could:
- Extend MASTG test case coverage
- Improve the user / hacker experience
- Bug-fix them
- Propose new ideas
- etc.
NOTE: The OWASP MAS project also includes the MASTG Crackmes which include various solutions that can guide you through the reverse engineering process and help you learn and practice.
Currently, the code is being maintained by @sushi2k. If the app does not boot, or if there is another bug: file an issue at this repository.
- Author: Sven Schleier
- Maintained by Sven Schleier
The sources can be found here: https://github.com/OWASP/MASTG-Hacking-Playground/tree/master/Android/MSTG-Android-Java-App
This app is compatible with Android 4.4 and up. Once you checkout the repo you can install the debug build:
$ adb install Android/MSTG-Android-Java-App/app/build/outputs/apk/debug/app-debug.apk The APK is also available in the release page.
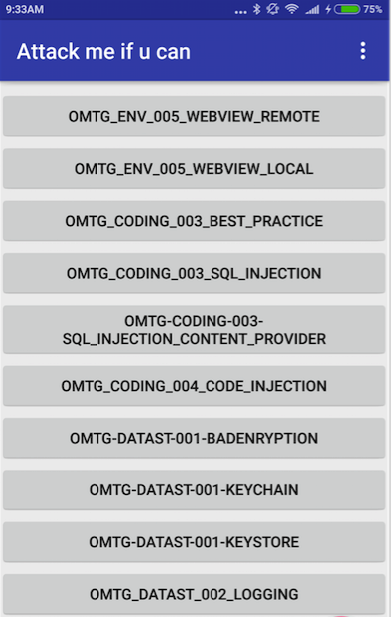
Screenshot of app:
Check the Wiki for a description of all available test cases in the MSTG-Android-Java-App.
- Author: Wen Bin Kong
- Maintained by Sven Schleier
The sources can be found here: https://github.com/OWASP/MASTG-Hacking-Playground/tree/master/Android/MSTG-Android-Kotlin-App
In order to use the Kotlin App you need to deploy the Ruby on Rails backend
This app is compatible with Android 4.4 and up. Once you checkout the repo you can install the debug build:
$ adb install Android/MSTG-Android-Kotlin-App/app/build/outputs/apk/debug/app-debug.apkThe APK is also available in the release page.
Open the project directories Android/MSTG-Android-Kotlin-App/ or Android/MSTG-Android-Java-App/ in Android Studio. The apps can be compiled with Android Studio 3.5 (tested).
In order to get the MSTG-Android-Java-App running, besides the Android SDK, also the Android NDK needs to be available. If the NDK is not available, Android Studio will ask to download or specify a local path for the NDK when the project is opened. If parts of the SDK are missing, a prompt should show up to install the additional requirements. Afterwards the App can be build and can be run in an emulator or mobile device.
- Author: Sven Schleier
- Maintained by Sven Schleier
The sources can be found here: https://github.com/OWASP/MASTG-Hacking-Playground/tree/master/iOS/MSTG-JWT
In order to use the iOS App you need to deploy the Ruby on Rails backend
The IPA is also available in the release page.
There are several ways available on how to install an IPA; have a look at the MASTG to identify which one is the best for you.
This project is using the GNU General Public License v3.0.
Wen Bin Kong (@kongwenbin) Nikhil Soni (@nikhil) Ryan Teoh (@ryantzj)