Attribute Injection leading to XSS(Cross-Site-Scripting)
Moderate severity
GitHub Reviewed
Published
Nov 24, 2023
in
louislam/uptime-kuma
•
Updated Dec 7, 2023
Description
Published to the GitHub Advisory Database
Nov 24, 2023
Reviewed
Nov 24, 2023
Published by the National Vulnerability Database
Dec 1, 2023
Last updated
Dec 7, 2023
Summary
Google Analytics element Attribute Injection leading to XSS
Details
Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks.
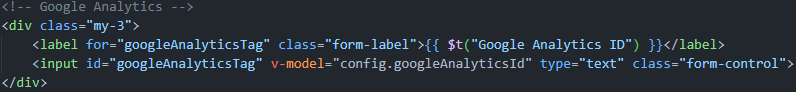
PoC
screenshots:
References