-
Notifications
You must be signed in to change notification settings - Fork 113
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
NEP: dApp Platform Provider Interface #69
Conversation
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Great job!
Here are couple of other useful methods: (all are promises)
signMessage- Given a payload, allow the user to sign the message contents.getNetwork- Returns the users network - MainNet/TestNet/PrivateNet.isLoggedIn- Returns true if logged in.isReady- Might be specific to nex extension, but there are certain checks that need to be done before accepting calls from the dapp.
Events:
network_changed- fired when a user changes his network.account_changed- fired when a user logs in/out.ready- fired when the provider is ready.
let me know what you think @nickfujita
|
Also, it may be interesting to add some method to get the current block but this is not important. |
|
Thanks for the responses @nickfujita.. my intent was trying to maje it better,although I know its a challenge to change things that many providers are already using... others are directly connected to neo rpc standard,which is not perfect too. This looks like a good standard afterall, due to all these limitations, and perhaps we should just close all my comments, since this is a "nearly final" proposal (no need to change small things). Congratulations. |
|
Great point! I am also very much in agreement with this. Rather than injecting the latest version of the method interface onto the window of the dApp website, providers should be providing properly versioned packages. In the case of O3, we currently utilize NPM and CDN (JSDeliver) to ensure that dApps can protect themselves from sudden changes in the interface. In this way, dApps can lock down their NPN dependencies, or reference a specific version of the CDN package to pull into their website. Although this is how O3 choose to implement this, since the proposal is still just focused on the interface of the methods themselves, it is not currently a requirement. Do others think that we should add this as a requirement to the proposal, or should it just be left as a general "best practice" for dApps and websites in general for importing JS dependencies? |
|
I think that @corollari comment is on point. About an year ago I suggested that the provider should inject versioned libraries but if instead we can have a versioned |
|
@corollari Added |
|
@igormcoelho Thanks again for all the input. It was very helpful, and a bunch of improvements were made to the proposal per your feedback ^^ |
|
@canesin We are all excited for the launch of your platform this month, and are glad you have circled back to this proposal. I've added to the proposal a spec which briefly describes how providers of client packages should be versioning and supporting this interface. As for the integration into neon-js, we would be happy to provide any additional documentation required for the integration team. |
|
@nickfujita Looks good, sent a PR fixing several typos and grammar problems (all trivial changes). |
Fix grammar & vocab
|
@corollari Thanks! Merged in! |
|
|
|
@hal0x2328 There might be some problems with that, this interface aims to support wallets that use Ledger Nano and currently the NEO app for Ledger Nano does not seem to support encryption/decryption^[1]. Thus the following solutions appear:
Another solution for your use-case that uses the current API would be:
Also note that this systems allows implementations to use any encryption scheme they want but integrating Still, given that one of the biggest objectives of this NEP is to improve dev experience (and having to implement a Diffie-Hellman key exchange by yourself is not good dev UX) it may be interesting to consider one of the solutions I proposed. [1]: I have not verified it directly from the source code (couldn't find it easily) so this might be wrong |
|
@nickfujita would it be possible to describe in more detail how I have also tried to look into how it's currently implemented in the source code but:
|
|
@corollari here is the code to generate the |
I've verified the current Ledger Neo app does not currently support encrypt/decrypt but this might be a good time to implement it since the app will need an overhaul for Neo3 anyway. I've seen that a few other cryptocurrencies Ledger apps do support encrypt/decrypt - they do so by letting the user authorize the app to generate and return the ECDH shared secret key for a sender/receiver pair, then the actual session encryption/decryption is handled in the wallet. This is probably necessary since the Ledger's memory is so limited and also it would be kind of a pain to authorize each and every message decrypt/encrypt especially in an ongoing chat log. If this seems like a viable path I can add this code to the Neo Ledger app. My only issue is that I only have a Ledger Nano S and it would need to be tested on the Blue and Nano X also. |
|
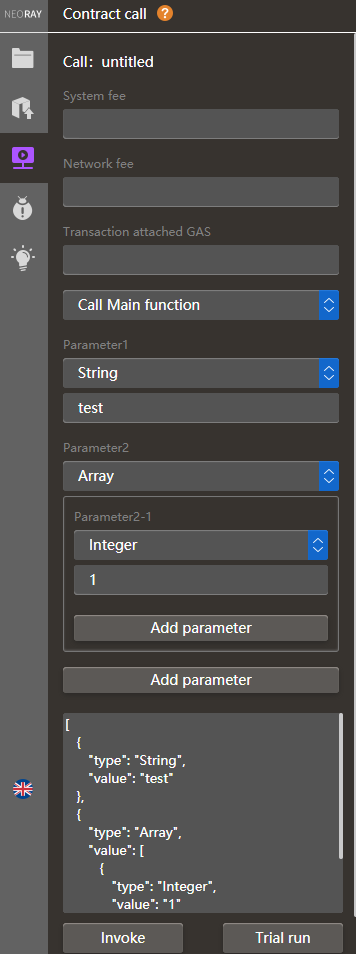
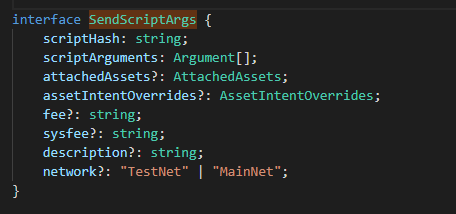
@vincentOpenSource Are you proposing that the dAPI should also support calling contracts with arbitrary parameters (eg: use a number for the first parameter) or just explaining how to use the current dAPI with NEOray's system? |
|
@hal0x2328 To me that seems like a good idea but @nickfujita has probably better insights into that. |
|
Here's my fork of the Ledger app that adds an ECDH shared-secret generation function if anyone wants to have a look at potentially adding message encrypt/decrypt to dAPI. |
|
Regarding the parameters of invokeMulti, it doesn't seem clear how can several Several attachedAsset, one for each script call, are also a bit confusing, but I assume these are combined by creating different asset intents for the same transaction, each one pointing at the address of the script hash used in each specific call, is this right? |
|
Created a PR that updates the implementation section: nickfujita#3 |
|
@QingmingZi Could you please confirm that your Teemo wallet is no longer being maintained? |
|
|
||
| <pre> | ||
| interface Networks { | ||
| networks: string[]; // Array of network names the wallet provider has available for the dapp developer to connect to. |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I think this method should return the magic number of the networks. And also, maybe these data can be returned by getProvider().
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
@neo-project/core @nickfujita

A proposal for a standardized protocol interface between dApp developers and dApp API platform providers.