-
Notifications
You must be signed in to change notification settings - Fork 793
Introduction
Alex Feyerke edited this page Nov 9, 2023
·
14 revisions
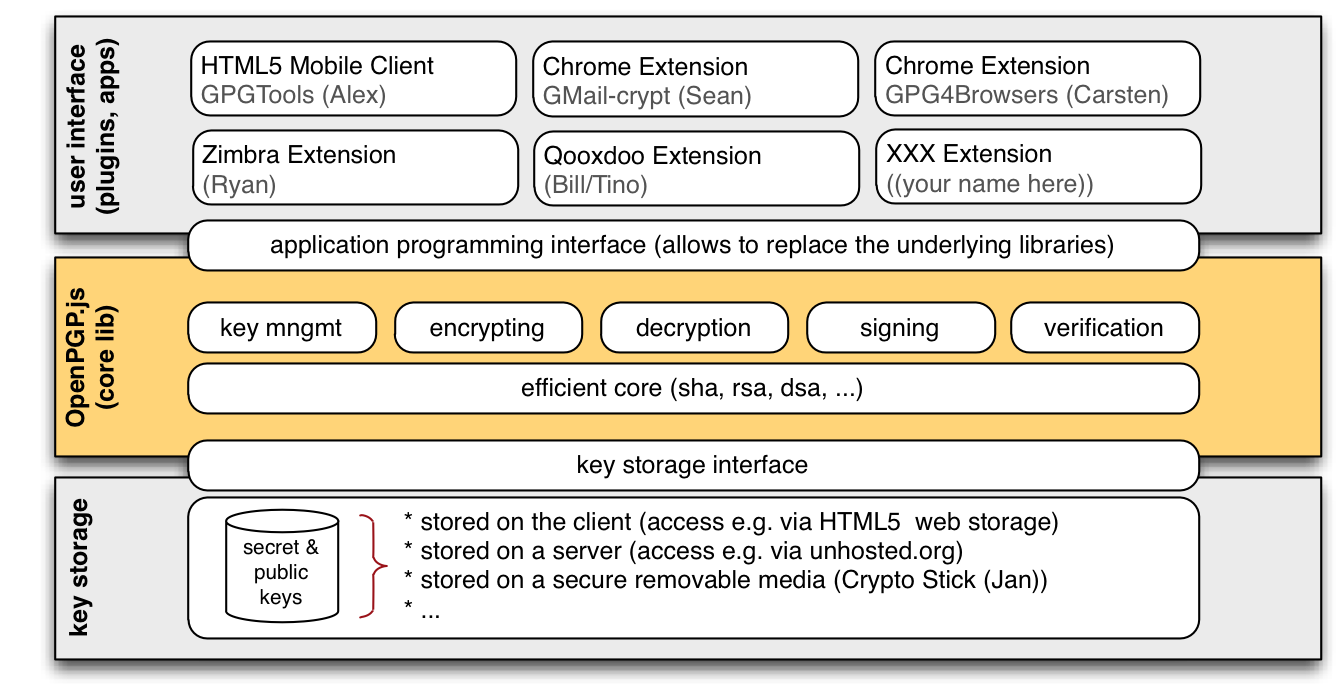
- Visual Overview
- Functionalities
- Other JavaScript OpenPGP Implementation
- Other OpenSource OpenPGP Implementation
- Other Related Projects
- Hanewinkel
- Goal: First known OpenPGP JavaScript implementation
- URL: http://www.hanewin.net/encrypt/
- Barry
- Goal: Zimbra plugin
- URL: https://github.com/barrydegraaff/pgp-zimlet
- Mete0r
- Goal: Core library
- URL: https://github.com/mete0r/openpgp-js
- Prometheus
- Goal: Google Mail integration
- URL: https://github.com/seancolyer/gmail-crypt
- Contact: sean@colyer.name
- gpg4browsers
- Goal: Chrome Browser Extension
- URL: http://gpg4browsers.recurity.com/
- Qooxdoo
- Goal: Integration into universal javascript framework
- URL: http://qooxdoo.org/contrib/project/crypto
- GPGTools
- Goal: Core Library + Mobile Phone GUI
- URL: https://github.com/GPGTools/Mobile/wiki/Introduction
- GnuPG (C, most complete OpenPGP implementation)
- Bouncy Castle OpenPGP Generator/Processor (for Java and C#)
- ObjectivePGP (Objective-C, Swift)
- Crypt-OpenPGP (Perl, most complete OpenPGP implementation besides GPG)
- openpgp-php
- openpgp-python
- openpgp-ruby
- openpgp-haskell
- php-gpg (Pure PHP implementation of PGP encryption)
- cr-gpg: A chrome plugin that enables gpg encryption and decryption for the gmail web interface
- firebreath: FireBreath aims to be a cross-platform plugin architecture, targeting browsers that support NPAPI and Internet Explorer on Windows, Mac and Linux.
- domcrypt: fast, native Public Key Encryption exposed to JavaScript/DOMWindows for Firefox
- FirePG: FireGPG is a Firefox extension that provides an integrated interface to apply GnuPG operations to the text of any web page, including encryption, decryption, signing, and signature verification.
- CryptoStick: A secure USB private key storage.