This repository is an overview of what you need to learn in penetration testing and a collection of the necessary tools you can use during your pentesting, and it is also a collection of resources and references to practice offensive security. You can always comeback here, to check if you forgot any step. This will be mainly focused only on Linux machines.
- Introduction
- Before Hacking
- Steps of Pen-Testing
- Enumeration
- Privilege Escalation
- Tools - 🕵️♂️ Information Gathering - 🔒 Password Attacks - 📝 Wordlists - 🌐 Wireless Testing - 🔧 Exploitation Tools - 👥 Sniffing & Spoofing - 🚀 Web Hacking - 🎉 Post Exploitation - 📦 Frameworks
- Additional resources
- Conclusion.
The goal of this repository is to help out beginners-medium hackers. Practicing is the only way to improve in this domain, and there are plenty of websites where you can learn, and hack at the same time. But before that, let's talk a bit about what you will find in the repository.
To become a great pentester you have to be patient. Learning and practicing are definetly your way into this domain. But it will take some time. Here's a simple list of things you should and shouldn't do in order to imporve :
- Don't be a script kiddie, not having any idea on what you're doing means you're a script kiddie.
- You have to master at least one programming language. And if you still haven't learn a single programming language. I would advise you to start with Python.
- Don't just use tools without knowing how they work. Here's a list of tools you will need.
- You're not ready for real targets, just focus on practicing and learning and you will get there. Hopefully in a lawful way.
- Learning doesn't only rely on videos on youtube, reading could be a great way as well. From books to manuals and articles.
- Assembly language is far important than you think, specially if you're into Reverse engineeering or PWN. It would be easier to learn it if you master C language before.
- You have to know how computers and operating system works. Do you know what a kernel is ? If not you should do some googling.
- Twitter, as dumb as this idea looks, but i'd really recommend you to have a twitter account, and follow the community related and be part of them. Staying up to date with the world is not such a bad idea after all.
- Last but not least, don't learn hacking for wrong reasons. Don't waste your time if your goal is to hack your girl(boy)friends Facebook account. Set a goal, no matter how big it looks like, and chase it. Dreams without goals are the ultimate fuel of disappointment.
Here you will find multiple resources to learn and practice hacking.
Here's a list of one the best youtubers I personally follow.
| Name | Description | Link |
|---|---|---|
| IPPSEC | Does retired machines from HackTheBox, great way to learn what to do before every machine. | link |
| Liveoverflow | One of the best channels on youtube to learn reverse engineering and PWN. | Link |
| John Hammond | Does different kind of CTFs, you can learn how to use lot of tools, and techniques. | Link |
| David Bombal | Great channel to imporve professionally in hacking if you are looking for jobs. | Link |
| NetworkChuck | If you are looking where to learn very basic stuff with a fun way (specially networking), this guy is yours. | Link |
| The Cyber Mentor | Our cyber security mentor... This channel contains real world pentesting examples and courses, this guy will definitely be your mentor aswell. | link |
| HackerSploit | This one explains tools, and does HackTheBox retired machines. And also does real life scenarios hacking. | Link |
Here's where you can learn and practice at the same time.
| Name | Description | Link |
|---|---|---|
| HackTheBox | Perhaps the greatest platform with the hardest possible challenge. specialise in Boxes (don't start here) | HackTheBox |
| TryHackMe | This one is similar to HackTheBox, difference is that is has easier challenges than HTB | TryHackMe |
| PwnTillDawn | Although the name would give you PWN vibes, it has a big number of boxes ready to be PWNed | PwnTillDawn |
| CyberTalents | A good platform for beginners to start their journey into hacking. It has only CTFs though | CyberTalents |
| Pwnable | Fun platform to learn PWN from the very basics. You will need to learn C language before | Pwnable |
| HackThisSite | Free platform for hackers to test and expand their knowledge with CTFs, challenges and many more | HackThisSite |
| Hacker101 | Free class for web security. Whether you're a programmer with an interest in bug bounties or a seasoned security professional | Hacker101 |
| PicoCTF | Free computer security education program, with original created challenges to practice your skills in different domains. | PicoCTF |
Go ahead a knock yourself out.
There are certain things you need to learn before even diving into hacking. Here's a list you should definetly check out.
Many might think that programming is not really necessary in hacking, they're not just wrong they're stupid. But you need to know that not all programming languages serve the same purpose. There are different types, you should learn at least one language in each category. Let's go ahead and check them out.
These are the languages that will on a daily basis in your hacking journey.
- C / Assembly : Low level language, for binary exploitation.
- Bash : Linux scripting language.
- Powershell : Windows scripting language.
- Python : Easy to learn language, that can help you automate lot of work you do frequently.
- PHP : You cannot do web pentesting or bug bounty without knowing PHP.
- Javascript : Learning Javascript is as important as learning PHP, specially if you are into web app security.
- C++
- Ruby
- Go
- Java
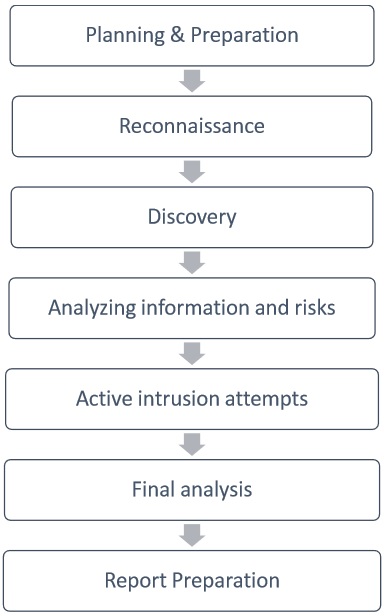
In this section, We'll give you a certain steps you should always follow when you're pentesting.
Now since we're finished with the introduction, let's go ahead and hack a box for the sake of an example. The Box I chose, is Boot2Root, a project in 42 Cursus.
The first step you should think of, is trying to identify what exactly you're attacking (hopefully in a lawful way). You need to gather maximum of informations from this target. A great way to do so, is to use a tool called NMAP. It's used to to scan ip addresses, it can also be used to identify ip addresses connected to your network. Since we do not know the ip address of our box, we have to scan our network in order to identify its ip address.
Depending on what's your network class, you can use the following command in order to scan a certain subnet.
$> nmap 10.12.100.x/24You will get an output similar to this :
And as you can see we have the ip address of the machine. But you'll ask what else we can do with nmap. Great question, can't answer it all. You have to discover more yourself. But let me show you some couple of commands you can use in order to do stuff.In order to use the following commands, you have to specify -A tag on your scan. It for aggressive scanning.
$> nmap -A 10.12.11.100Using nmap, you can detect what Operatin System the target uses. Note that this is not always accurate, and also you will need root privelege. Here's an example :
$> sudo nmap -o 10.12.11.100You can also detect what services are running on that target, the version of those services as well. Note that -sV is for the version scanning.
$> nmap -sV 10.12.11.100How about running a scan on all the ports from in a total of 65,535 ports.
$> nmap -p- 10.12.11.100You want only one port ?
$> nmap -p 80 10.22.11.100How about multiple ports ?
$> nmap -p 80,443 10.22.11.100A range of ports ?
$> nmap -p 80-8080 10.22.11.100There is also timing templates, if you want your scan to take more or less time.
$> nmap -T[ID] 10.22.11.100Sometimes you will counter targets that blocks your pings. Use the -Pn tag to skip the host discovery. This treats your target as an online target.
$> nmap -Pn 10.22.11.100If you want to save the results of your scan you can do it like this :
$> nmap 10.22.11.100 -oA output.nameLet's go ahead and gather all the tags, under one powerful command, you have to know that a command like this would take ~20-30 minutes :
$> sudo nmap -A -O -Pn -p- -T4 -sV 10.22.11.100There are a lot more commands than this, you should visit the nmap man page or their Docs to learn even more about this tool.
There are lot of other tools that you can use in order to dir bust, and each tools gives you different options.
Let's say you scanned a target and you found a web application, this web application can contains a multiple subdomains that you should check.
You might ask what a subdomain is. It's simply a good way to seperate the content of you website. It's piece of additional information added to the beginning of a website’s domain name. It allows websites to separate and organize content for a specific function — such as a blog or an online store — from the rest of your website.
Like sub-directories, you can also search for sub-domains , using a wordlist and a tool. In this case we'll be using as an example gobuster
Using the following command :
$> gobuster dns -d google.com -w /path/to/wordlist.txt
-d : To specify the domain name
-w : To specify a wordlistThus you will get something like this(don't take this example seriously, it's not true... or maybe ?).
www.google.com
blog.google.com
store.google.com
etc...
This can help you find more information about a certain website that you didn't know. Maybe even find login pannels or so.
After generating a list of subdomain and hosts, it's time to check those who work. Doing it manualy will take a long time if a long list was generated, so here's a tools httpx that make that task easy for us. Using the following command :
$> cat hosts.txt | httpxhttpx have more other intersting functionality, check the repo for more info.
You find a web app and its subdomains too, so what can you do with it. For instance you can try and find directories or files. There are lot of tools you can use to do that. But for now let's use dirb.
You'll need wordlist, in order to test on multiple directories or files. Check wordlists for more infos.
This is an example on how to use dirb command.
$> dirb http://ip_add/ /path/to/wordlistA good thing to do is to pay attention to the request you make on a website. Some websites can show you different outputs depending on what domain name you requested. Specially when you're playing challenges on websites like HackTheBox or TryHackMe, always change your host file to whatever you find while scanning or while enumerating in general.
$> nano /etc/hosts
10.1.1.1 1337.htb #exampleLogs are really important when it comes to tracing one's moves. You can even find credentials on them. We will talk more about it in the Privilege Escalation part
Using HackTricks, we can use multiple commands to monitor a system and thus finding an exploit we can use to privesc the system.
uname -a
cat /etc/os-release
cat /proc/version
uname -r
sudo -v (might not work sometimes if you don't have the password of the user)
ps aux
ps -ef
top -n 1
crontab -l
ls -al /etc/cron* /etc/at*
cat /etc/cron* /etc/at* /etc/anacrontab /var/spool/cron/crontabs/root 2>/dev/null | grep -v "^#"
Information Gathering tools allows you to collect host metadata about services and users. Check informations about a domain, IP address, phone number or an email address.
| Tool | Language | Support | Description |
|---|---|---|---|
| theHarvester | Python | Linux/Windows/macOS |
E-mails, subdomains and names Harvester. |
| CTFR | Python | Linux/Windows/macOS |
Abusing Certificate Transparency logs for getting HTTPS websites subdomains. |
| Sn1per | bash | Linux/macOS |
Automated Pentest Recon Scanner. |
| RED Hawk | PHP | Linux/Windows/macOS |
All in one tool for Information Gathering, Vulnerability Scanning and Crawling. A must have tool for all penetration testers. |
| Infoga | Python | Linux/Windows/macOS |
Email Information Gathering. |
| KnockMail | Python | Linux/Windows/macOS |
Check if email address exists. |
| a2sv | Python | Linux/Windows/macOS |
Auto Scanning to SSL Vulnerability. |
| Wfuzz | Python | Linux/Windows/macOS |
Web application fuzzer. |
| Nmap | C/C++ | Linux/Windows/macOS |
A very common tool. Network host, vuln and port detector. |
| PhoneInfoga | Go | Linux/macOS |
An OSINT framework for phone numbers. |
Crack passwords and create wordlists.
| Tool | Language | Support | Description |
|---|---|---|---|
| John the Ripper | C | Linux/Windows/macOS |
John the Ripper is a fast password cracker. |
| hashcat | C | Linux/Windows/macOS |
World's fastest and most advanced password recovery utility. |
| Hydra | C | Linux/Windows/macOS |
Parallelized login cracker which supports numerous protocols to attack. |
| ophcrack | C++ | Linux/Windows/macOS |
Windows password cracker based on rainbow tables. |
| Ncrack | C | Linux/Windows/macOS |
High-speed network authentication cracking tool. |
| WGen | Python | Linux/Windows/macOS |
Create awesome wordlists with Python. |
| SSH Auditor | Go | Linux/macOS |
The best way to scan for weak ssh passwords on your network. |
| Tool | Description |
|---|---|
| Probable Wordlist | Wordlists sorted by probability originally created for password generation and testing. |
| SecLists | A collection of multiple types of lists used during security assessments, collected in one place. List types include usernames, passwords, URLs, sensitive data patterns, fuzzing payloads, web shells, and many more. |
Used for intrusion detection and wifi attacks.
| Tool | Language | Support | Description |
|---|---|---|---|
| Aircrack | C | Linux/Windows/macOS |
WiFi security auditing tools suite. |
| bettercap | Go | Linux/Windows/macOS/Android |
bettercap is the Swiss army knife for network attacks and monitoring. |
| WiFi Pumpkin | Python | Linux/Windows/macOS/Android |
Framework for Rogue Wi-Fi Access Point Attack. |
| Airgeddon | Shell | Linux/Windows/macOS |
This is a multi-use bash script for Linux systems to audit wireless networks. |
| Airbash | C | Linux/Windows/macOS |
A POSIX-compliant, fully automated WPA PSK handshake capture script aimed at penetration testing. |
Acesss systems and data with service-oriented exploits.
| Tool | Language | Support | Description |
|---|---|---|---|
| SQLmap | Python | Linux/Windows/macOS |
Automatic SQL injection and database takeover tool. |
| XSStrike | Python | Linux/Windows/macOS |
Advanced XSS detection and exploitation suite. |
| Commix | Python | Linux/Windows/macOS |
Automated All-in-One OS command injection and exploitation tool. |
| Nuclei | Go | Linux/Windows/macOS |
Fast and customisable vulnerability scanner based on simple YAML based DSL. |
Listen to network traffic or fake a network entity.
| Tool | Language | Support | Description |
|---|---|---|---|
| Wireshark | C/C++ | Linux/Windows/macOS |
Wireshark is a network protocol analyzer. |
| WiFi Pumpkin | Python | Linux/Windows/macOS/Android |
Framework for Rogue Wi-Fi Access Point Attack. |
| Zarp | Python | Linux/Windows/macOS |
A free network attack framework. |
Exploit popular CMSs that are hosted online.
| Tool | Language | Support | Description |
|---|---|---|---|
| WPScan | Ruby | Linux/Windows/macOS |
WPScan is a black box WordPress vulnerability scanner. |
| Droopescan | Python | Linux/Windows/macOS |
A plugin-based scanner to identify issues with several CMSs, mainly Drupal & Silverstripe. |
| Joomscan | Perl | Linux/Windows/macOS |
Joomla Vulnerability Scanner. |
| Drupwn | Python | Linux/Windows/macOS |
Drupal Security Scanner to perform enumerations on Drupal-based web applications. |
| CMSeek | Python | Linux/Windows/macOS |
CMS Detection and Exploitation suite - Scan WordPress, Joomla, Drupal and 130 other CMSs. |
Exploits for after you have already gained access.
| Tool | Language | Support | Description |
|---|---|---|---|
| TheFatRat | C | Linux/Windows/macOS |
Easy tool to generate backdoor and easy tool to post exploitation attack like browser attack, dll. |
Frameworks are packs of pen testing tools with custom shell navigation and documentation.
| Tool | Language | Support | Description |
|---|---|---|---|
| Operative Framework | Python | Linux/Windows/macOS |
Framework based on fingerprint action, this tool is used to get information on a website or a enterprise target with multiple modules. |
| Metasploit | Ruby | Linux/Windows/macOS |
A penetration testing framework for ethical hackers. |
| cSploit | Java | Android |
The most complete and advanced IT security professional toolkit on Android. |
| radare2 | C | Linux/Windows/macOS/Android |
Unix-like reverse engineering framework and commandline tools. |
| Wifiphisher | Python | Linux |
The Rogue Access Point Framework. |
| Beef | Javascript | Linux/Windows/macOS |
The Browser Exploitation Framework. It is a penetration testing tool that focuses on the web browser. |
| Mobile Security Framework (MobSF) | Python | Linux/Windows/macOS |
Mobile Security Framework (MobSF) is an automated, all-in-one mobile application (Android/iOS/Windows) pen-testing, malware analysis and security assessment framework capable of performing static and dynamic analysis. |
| Burp Suite | Java | Linux/Windows/macOS |
Burp Suite is a leading range of cybersecurity tools, brought to you by PortSwigger. This tool is not free and open source |
- The Life of a Security Researcher
- Awesome-Hacking Lists
- Security Mindmap
- Exploit Database
- Hackavision
- Hackmethod
- Packet Storm Security
- SecLists
- SecTools
- Smash the Stack
- Don't use VPN services
- How to Avoid Becoming a Script Kiddie
- 2017 Top 10 Application Security Risks
- Starting in cybersecurity ?
I would highly advise you guys to go and checkout sundowndev.
The idea behind this repository is to help promoting cyber and information security across our club, and teach the various tools used in offensive cyber security.