Home of the OpenSSF SBOM Everywhere SIG. We're glad you're here!
- Official communications occur on the openssf-sig-sbom mailing list
- We have a Slack Channel for discussion various SBOM related activities
- Every other Tuesday @ 11:05am EST. The invite is available on the OpenSSF Community Calendar.
- Meeting Minutes can be found in this Google Document. Feel free to add agenda items, please put your name next to items you add.
To provide a better overview of the available tooling and their capabilities, this group maintains an SBOM Catalog which can be found under the following link:
https://sbom-catalog.openssf.org/
If you want to get involved, please see the document here
More data needs to be added to the catalog
The goal of this project is to understand what open source projects need to start publishing SBOMs
[https://docs.google.com/document/d/15_FKO8D03VSYDTNsMQZtn1aRfgVmModF-NM6VBnlrZA/](Draft document)
This document needs to be better defined to construct a plan to help open source projects
Best Practices for Naming and Directory Conventions for SBOMs (Software Bill of Materials) in Open Source Projects
This document describes where to put an SBOM to be distributed and how to name it. It currently has a very narrow scope.
It needs to be expanded to cover other use cases
[https://github.com/ossf/sbom-everywhere/blob/main/reference/sbom_naming.md](Reference doument)
- The initial motivation for the formation of the OSSF SBOM Everywhere SIG is born from OpenSSF's The Open Source Software Security Mobilization Plan. SBOM standardization and consensus from within the open source community is integral to adoption of universal constructs that reveal themselves via the exploration of use cases beyond a compliance check box.
- Securing OSS Production: focus on preventing security defects and vulnerabilities in code and open source packages in the first place
- Improving Vulnerability Discovery & Remediation: improving the process for finding defects and fixing them
- Shorten Ecosystem Patching Response Time: Shorten the response time for distributing and implementing fixes.
- The requirements needed to build use cases using SBOMs are clearly understood, documented and implemented in current SBOM specifications
- There are “friction free” open source tools that generate SBOMs that meet these requirements
- There is readily accessible education, awareness and implementation guidance and 3rd party support
The mobilization plan defines scope as By focusing on tools and advocacy, we can remove the barriers to generation, consumption, and overall adoption of SBOMs everywhere, we can improve the security posture of the entire open source ecosystem: producers, consumers, and maintainers.
For the purposes of establishing ubiquity to ensure sustainability for SBOM related tooling, and future solutions for consumption, “supported” formats must be defined. At this time there are two supported formats that will be in scope for the purposes of this group: CycloneDX and SPDX.
Utilization of these specifications would likely be discretionary and interchangeable depending on the use case and SBOM type and the requirements of individual organizations and internal tooling.
This group's interpretation is
- Use cases
- Defining types of SBOMs
- Source
- Binary analysis
- Build
- Deploy Runtime
- Generation
- Formats - clearly define expectations
- Consumption
- How do we track and encourage the consumption of the artifacts
- something about tools
- Adoption (how do we encourage others to create and use SBOMs)
- Something about producers, consumers, and maintainers
- Where does the burden lie on accountability and enforcement?
- something about tools
- Tools are everywhere, what do we do with this?
- something about advocacy
- Attestation?
- Not part of tooling, this needs to be a policy decision in these conversations, don't worry about the technical details (yet)
- Where does this fit in? Producers, consumers, ???
- https://github.com/in-toto/attestation
- Compliance (regulated industry)
The Federal Government exists at every point of the Software Delivery Lifecycle, hence their minimum requirements are good guides to establish a baseline scope.
- Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations NIST SP 800-161 Rev. 1
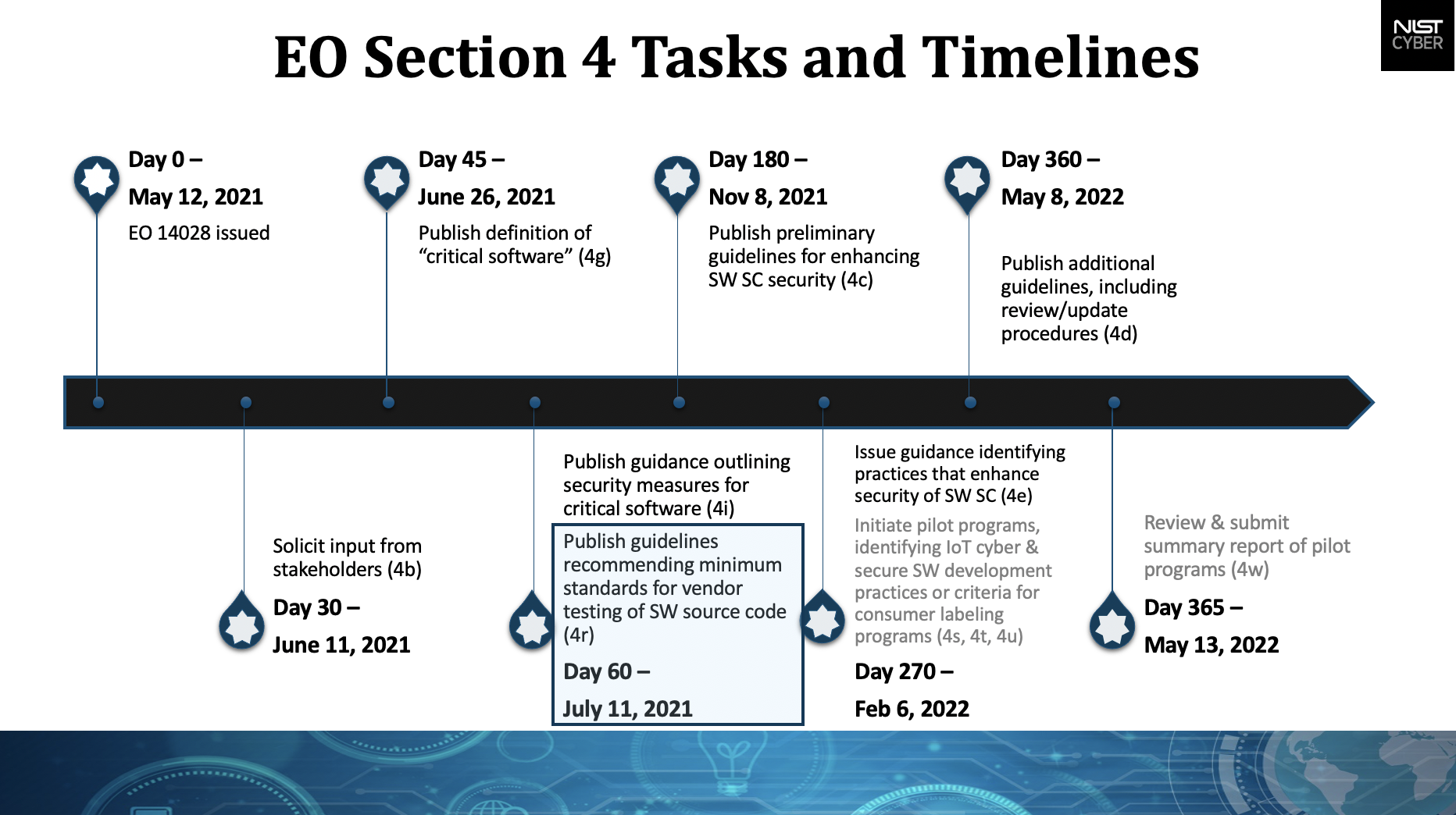
- Executive Order 14028
- Minimum Standards for Federal Government End Users
- NTIA SBOM Resources
- Software Bill of Materials Elements and Considerations
- Plan to Congress on Declassification and Clearances related to The Communications Supply Chain Risk Information Partnership
NTIA's legwork has been a guiding source having done the most comprehensive research to date.
- OWASP/Software-Component-Verification-Standard#34
- OWASP/Software-Component-Verification-Standard#35
- OWASP/Software-Component-Verification-Standard#36
The CHARTER.md outlines the scope and governance of our group activities.