Kubernetes resource state backup to git
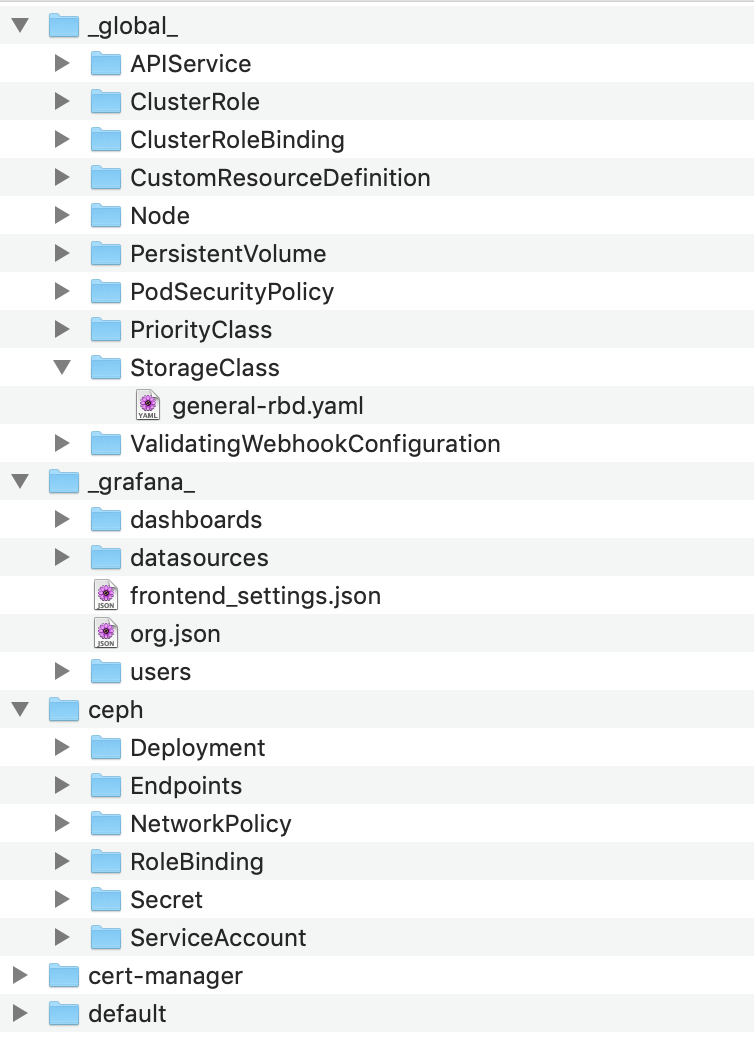
_global_ - global resources such as Node, ClusterRole, StorageClass
_grafana_ - grafana configs (when grafana enabled)
<namespace> - such as kube-system, default, etc...
<ResourceType> - folder for each resource type
<resource-name.yaml> - file for each resource
Yaml manifests are in deploy folder.
Github and gitlab support adding key only for one repository
- Create repo
- Generate ssh key
ssh-keygen -f ./new_key - Add new ssh key to repo with write access
- Save key to 2_config_map.yaml (see comments in file)
I recommend to run it periodically with kubernetes' CronJob resource, if you want to test how it works without waiting then can change running schedule or create pod with same parameters
kube_backup backup- pull remote git repository, save kubernetes state, make git commit in local repositorykube_backup push- push changes to remote repositorykube_backup help- shows help
Docker image by default runs kube_backup backup && kube_backup push
GIT_REPO_URL- remote git URL likegit@github.com:kuberhost/kube-backup.git(required)BACKUP_VERBOSEuse 1 to enable verbose loggingTARGET_PATH- local git repository folder, default./kube_stateSKIP_NAMESPACES- namespaces to exclude, separated by coma (,)ONLY_NAMESPACES- whitelist namespacesGLOBAL_RESOURCES- override global resources list, default isnode, apiservice, clusterrole, clusterrolebinding, podsecuritypolicy, storageclass, persistentvolume, customresourcedefinition, mutatingwebhookconfiguration, validatingwebhookconfiguration, priorityclassEXTRA_GLOBAL_RESOURCES- use it to add resources toGLOBAL_RESOURCESlistSKIP_GLOBAL_RESOURCES- blacklist global resourcesRESOURCES- default list of namespaces resources, seeKubeBackup::TYPESEXTRA_RESOURCES- use it to add resources toRESOURCESlistSKIP_RESOURCES- exclude resourcesSKIP_OBJECTS- use it to skip individual objects, such askube-backup/ConfigMap/kube-backup-ssh-config(separated by coma, spaces around coma ignored)GIT_USER- default iskube-backupGIT_EMAIL- default iskube-backup@$(HOSTNAME)GIT_BRANCH- Git branch, default ismasterGIT_PREFIX- Path to the subdirectory in your repositoryGRAFANA_URL- grafana api URL, e.g.https://grafana.my-cluster.comGRAFANA_TOKEN- grafana API token, create at https://your-grafana/org/apikeysTZ- timezone of commit times. e.g.:Europe/Berlin
To avoid man in a middle attack it's recommended to provide known_hosts file. Default known_hosts contain keys for github.com, gitlab.com and bitbucket.org
Let's say we have a cluster with prometheus and certmanager, they register custom resources and we want to add them in backup.
Get list of custom resource definitions:
$ kubectl get crd
NAME CREATED AT
alertmanagers.monitoring.coreos.com 2018-06-27T10:33:00Z
certificates.certmanager.k8s.io 2018-06-27T09:39:43Z
clusterissuers.certmanager.k8s.io 2018-06-27T09:39:43Z
issuers.certmanager.k8s.io 2018-06-27T09:39:44Z
prometheuses.monitoring.coreos.com 2018-06-27T10:33:00Z
prometheusrules.monitoring.coreos.com 2018-06-27T10:33:00Z
servicemonitors.monitoring.coreos.com 2018-06-27T10:33:00Z
Or get more useful output:
$ kubectl get crd -o json | jq -r '.items | (.[] | [.spec.names.singular, .spec.group, .spec.scope]) | @tsv'
alertmanager monitoring.coreos.com Namespaced
certificate certmanager.k8s.io Namespaced
clusterissuer certmanager.k8s.io Cluster
issuer certmanager.k8s.io Namespaced
prometheus monitoring.coreos.com Namespaced
prometheusrule monitoring.coreos.com Namespaced
servicemonitor monitoring.coreos.com Namespaced
Set env variables in container spec:
env:
- name: EXTRA_GLOBAL_RESOURCES
value: clusterissuer
- name: EXTRA_RESOURCES
value: alertmanager, prometheus, prometheusrule, servicemonitor, certificate, issuerSpecial thanks to Pieter Lange for original idea