An on-the-fly Powershell script obfuscator meant for red team engagements. Built out of necessity.
This only obfuscates functions and removes found in PowerShell scripts. Roadmap includes bfuscating variables. Pull requests and collaborative welcomed.
This was built out of the need to bypass endpoint security on a recent engagement. During priv esc attempts I could not download PowerUp.ps1 until it was obfuscated.
This is technically v2 and has been updated to remove comments.
git clone https://github.com/cwolff411/powerob
python3 powerob.py obfuscate originalfile.ps1 obfuscatedfile.ps1
Takes an INPUTFILE obfuscates it and dumps the obfuscated version into OUTPUTFILE.
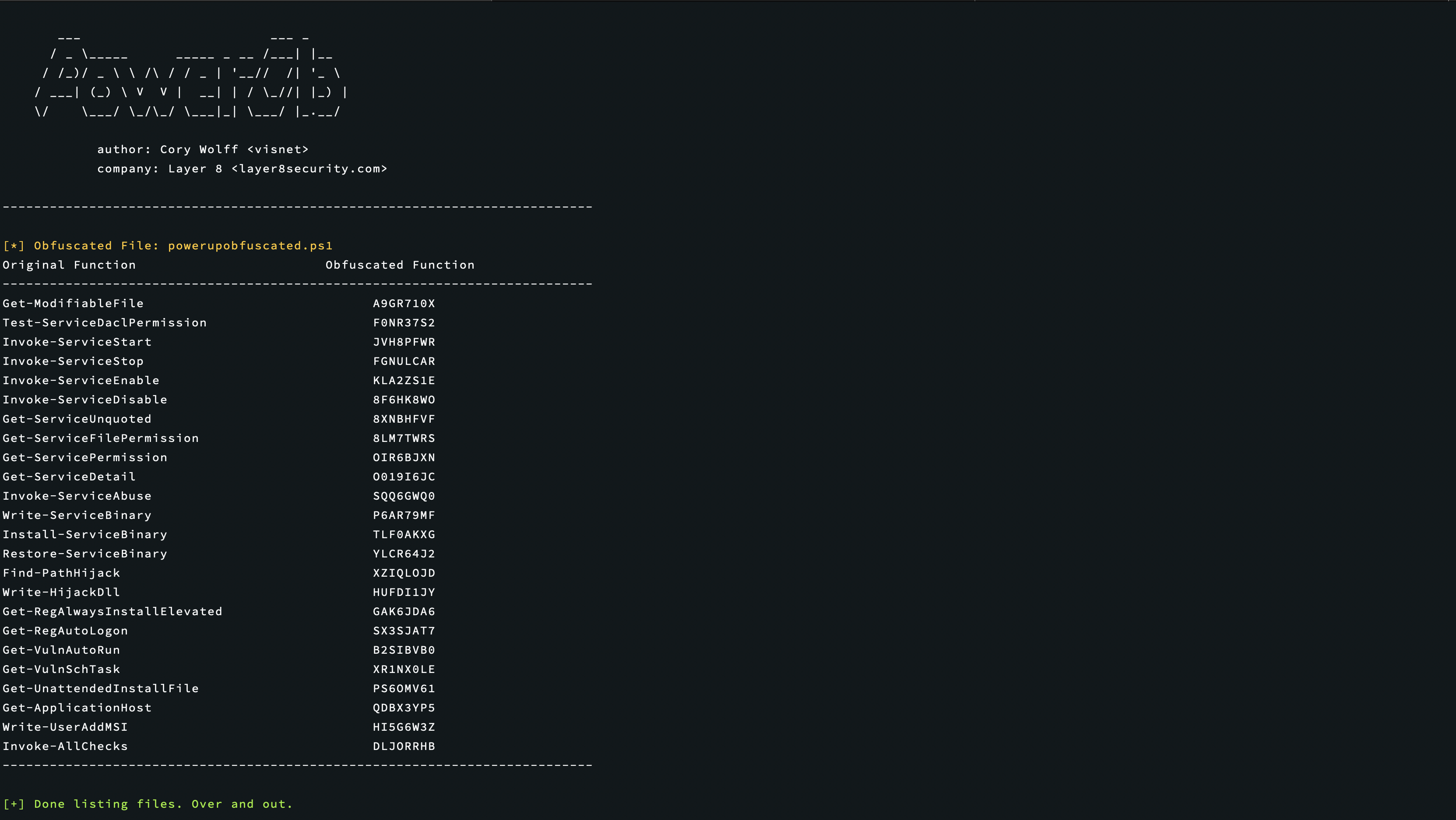
python3 powerob.py list
Lists all of the currently obfuscated files along with their commands and associated obfuscated commands.
python3 powerob.py getcommand COMMAND_NAME
For reference on the fly for when you forget. Takes the original command name and displays the obfuscated command name to be used in Powershell.
python3 powerob.py cleardb
Maintenance function to clear the db of past obfuscated files and functions.