dev branch |
Reference Docs | # of Downloads per different platforms | # of Downloads per recent MSAL versions | Benchmark Diagram |
|---|---|---|---|---|
 |
 |
📉 |
The Microsoft Authentication Library for Python enables applications to integrate with the Microsoft identity platform. It allows you to sign in users or apps with Microsoft identities (Microsoft Entra ID, External identities, Microsoft Accounts and Azure AD B2C accounts) and obtain tokens to call Microsoft APIs such as Microsoft Graph or your own APIs registered with the Microsoft identity platform. It is built using industry standard OAuth2 and OpenID Connect protocols
Not sure whether this is the SDK you are looking for your app? There are other Microsoft Identity SDKs here.
Quick links:
| Getting Started | Docs | Samples | Support | Feedback |
|---|
Click on the following thumbnail to visit a large map with clickable links to proper samples.
You can find MSAL Python on Pypi.
- If you haven't already, install and/or upgrade the pip of your Python environment to a recent version. We tested with pip 18.1.
- As usual, just run
pip install msal.
This library follows Semantic Versioning.
You can find the changes for each version under Releases.
Before using MSAL Python (or any MSAL SDKs, for that matter), you will have to register your application with the Microsoft identity platform.
Acquiring tokens with MSAL Python follows this 3-step pattern. (Note: That is the high level conceptual pattern. There will be some variations for different flows. They are demonstrated in runnable samples hosted right in this repo. )
-
MSAL proposes a clean separation between public client applications, and confidential client applications. So you will first create either a
PublicClientApplicationor aConfidentialClientApplicationinstance, and ideally reuse it during the lifecycle of your app. The following example shows aPublicClientApplication:from msal import PublicClientApplication app = PublicClientApplication( "your_client_id", authority="https://login.microsoftonline.com/Enter_the_Tenant_Name_Here")
Later, each time you would want an access token, you start by:
result = None # It is just an initial value. Please follow instructions below.
-
The API model in MSAL provides you explicit control on how to utilize token cache. This cache part is technically optional, but we highly recommend you to harness the power of MSAL cache. It will automatically handle the token refresh for you.
# We now check the cache to see # whether we already have some accounts that the end user already used to sign in before. accounts = app.get_accounts() if accounts: # If so, you could then somehow display these accounts and let end user choose print("Pick the account you want to use to proceed:") for a in accounts: print(a["username"]) # Assuming the end user chose this one chosen = accounts[0] # Now let's try to find a token in cache for this account result = app.acquire_token_silent(["your_scope"], account=chosen)
-
Either there is no suitable token in the cache, or you chose to skip the previous step, now it is time to actually send a request to AAD to obtain a token. There are different methods based on your client type and scenario. Here we demonstrate a placeholder flow.
if not result: # So no suitable token exists in cache. Let's get a new one from AAD. result = app.acquire_token_by_one_of_the_actual_method(..., scopes=["User.Read"]) if "access_token" in result: print(result["access_token"]) # Yay! else: print(result.get("error")) print(result.get("error_description")) print(result.get("correlation_id")) # You may need this when reporting a bug
Refer the Wiki pages for more details on the MSAL Python functionality and usage.
If your application is using ADAL Python, we recommend you to update to use MSAL Python. No new feature work will be done in ADAL Python.
See the ADAL to MSAL migration guide.
You can follow the latest updates and plans for MSAL Python in the Roadmap published on our Wiki.
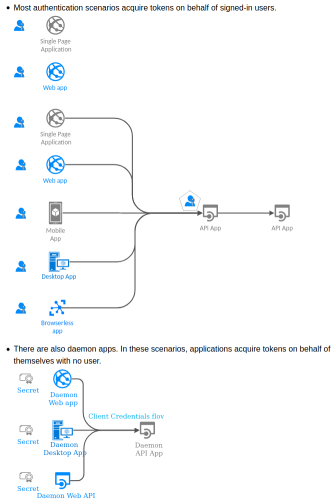
MSAL Python supports multiple application types and authentication scenarios. The generic documents on Auth Scenarios and Auth protocols are recommended reading.
We provide a full suite of sample applications and documentation to help you get started with learning the Microsoft identity platform.
We leverage Stack Overflow to work with the community on supporting Microsoft Entra and its SDKs, including this one! We highly recommend you ask your questions on Stack Overflow (we're all on there!) Also browser existing issues to see if someone has had your question before.
We recommend you use the "msal" tag so we can see it! Here is the latest Q&A on Stack Overflow for MSAL: http://stackoverflow.com/questions/tagged/msal
We'd like your thoughts on this library. Please complete this short survey.
If you find a security issue with our libraries or services please report it to secure@microsoft.com with as much detail as possible. Your submission may be eligible for a bounty through the Microsoft Bounty program. Please do not post security issues to GitHub Issues or any other public site. We will contact you shortly upon receiving the information. We encourage you to get notifications of when security incidents occur by visiting this page and subscribing to Security Advisory Alerts.
All code is licensed under the MIT license and we triage actively on GitHub. We enthusiastically welcome contributions and feedback. Please read the contributing guide before starting.
This project has adopted the Microsoft Open Source Code of Conduct. For more information see the Code of Conduct FAQ or contact opencode@microsoft.com with any additional questions or comments.