AWS Client VPN is a managed client-based VPN service that enables you to securely access your AWS resources and resources in your on-premises network. With Client VPN, you can access your resources from any location using an OpenVPN-based VPN client.
This was an assignment during [SAA Certification Bootcamp- E9 - Networking Services] (https://youtu.be/ES7inmRo2Is?t=7071)
This is Part I of the series, In this one, we will be focusing on Access to a VPC
Part II will be Access to a peered VPC
We are going to setup an AWS Client VPN in US East (N. Virginia), let's get started
- Create a VPC
- Authentication
- Create a Client VPN Endpoint
- Enable VPN connectivity for clients
- Authorize clients to access a network
- (Optional) Enable access to additional networks
- Download the Client VPN endpoint configuration file
- Connect to the Client VPN endpoint
- Testing
- Client VPN scaling considerations
- Cost
- Referrals
- Navigate to
VPC Console>Create a VPC - Enter Name as 'vpn-vpc' and IPV4 CIDR as
192.168.0.0/16
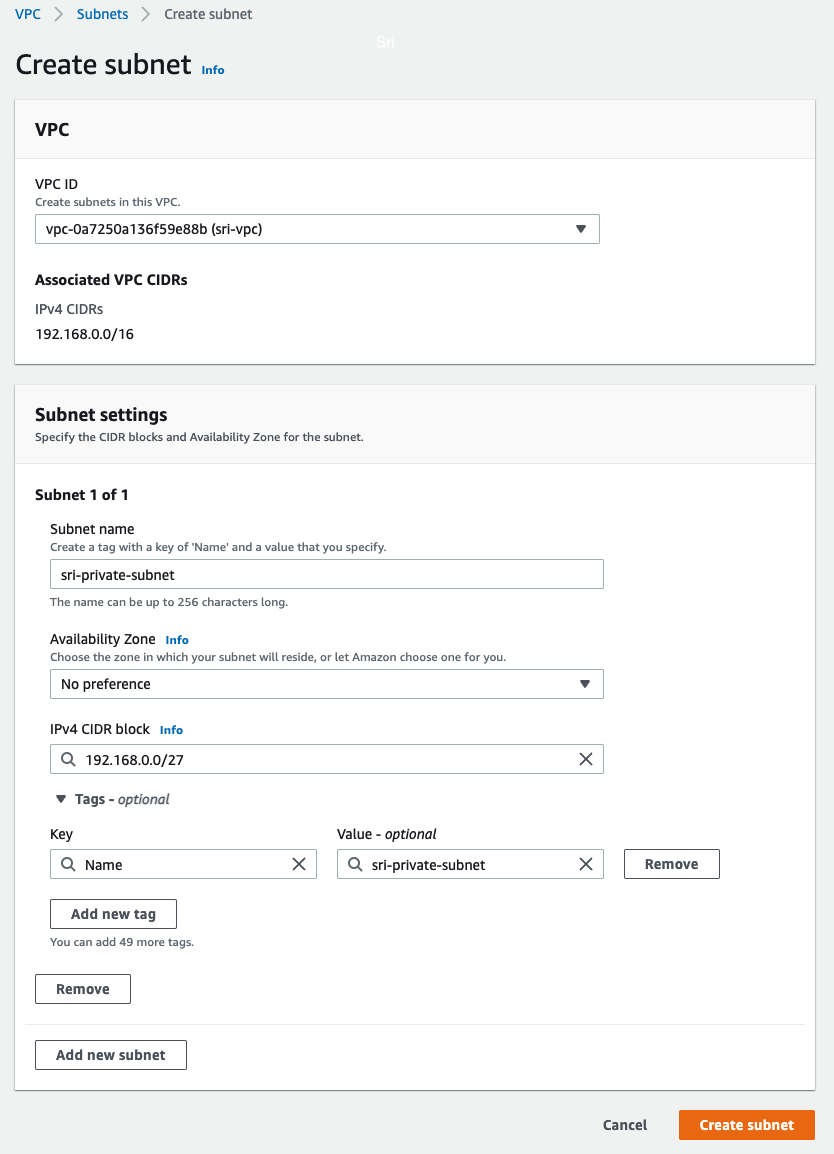
- Navigate to
Subnet> ClickCreate a Subnet> Selectvpn-vpc> Subnet name asprivate-subnetand IPV4 CIDR as192.168.0.0/27
Note: We will launch an EC2 instance into this subnet for a connectivity test at the end.
Client VPN uses Authentication as the first point of entry into the AWS cloud. There are three ways to authenticate, we are going to use Mutual authenticaiton (certificate-based)
- Active Directory authentication (user-based)
- Mutual authentication (certificate-based)
- Single sign-on (SAML-based federated authentication) (user-based)
git clone https://github.com/kasukur/clientvpn.git
cd clientvpn
chmod 755 generate_certs.sh
./generate_certs.sh
Tip: Enter a
directoryname and then you could press ENTER atCommon Nameor provide a name
You do not necessarily need to upload the client certificate to ACM. If the server and client certificates have been issued by the same Certificate Authority (CA), you can use the server certificate ARN for both server and client when you create the Client VPN endpoint.
For this exercise, we are going to upload the server and the client certificates to ACM. Be sure to use the same Region in which you intended to create the client VPN endpoint.
Server Certificate
aws acm import-certificate --certificate fileb://server.crt --private-key fileb://server.key --certificate-chain fileb://ca.crt
Client Certificate
aws acm import-certificate --certificate fileb://client1.domain.tld.crt --private-key fileb://client1.domain.tld.key --certificate-chain fileb://ca.crt
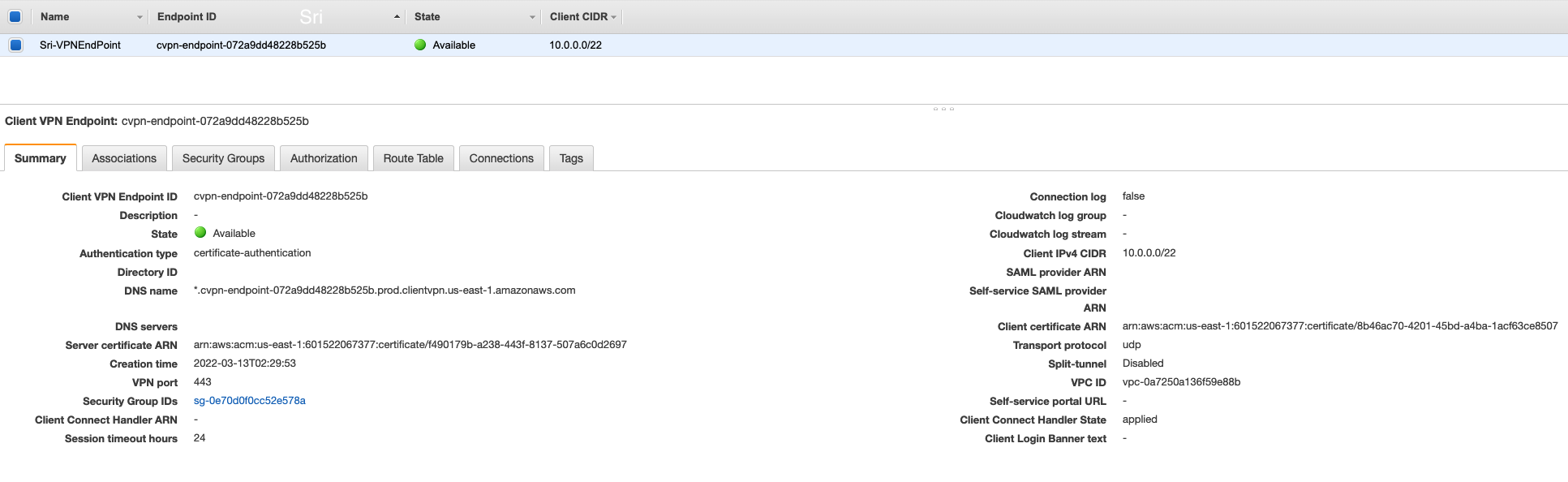
- Navigate to
VPC Console>Client VPN Enpoints>Create Clinet VPN EndPoint - Provide a
nameanddescription(optional) for the Client VPN endpoint - Enter a Client IPv4 CIDR as
10.0.0.0/22
Note: The IP address range cannot overlap with the target network or any of the routes that will be associated with the Client VPN endpoint. The client CIDR range must have a block size that is between /12 and /22 and not overlap with VPC CIDR or any other route in the route table. You cannot change the client CIDR after you create the Client VPN endpoint.
- Select
Server certificate ARN,Client certificate ARNand checkUse mutual authentication - Select no for
Connection LoggingandClient Connect Handler - Select
Enable split-tunnel - Leave the rest of the default settings, and choose
Create Client VPN Endpoint.
The status of Client VPN endpoint will be in pending-associate at this stage.
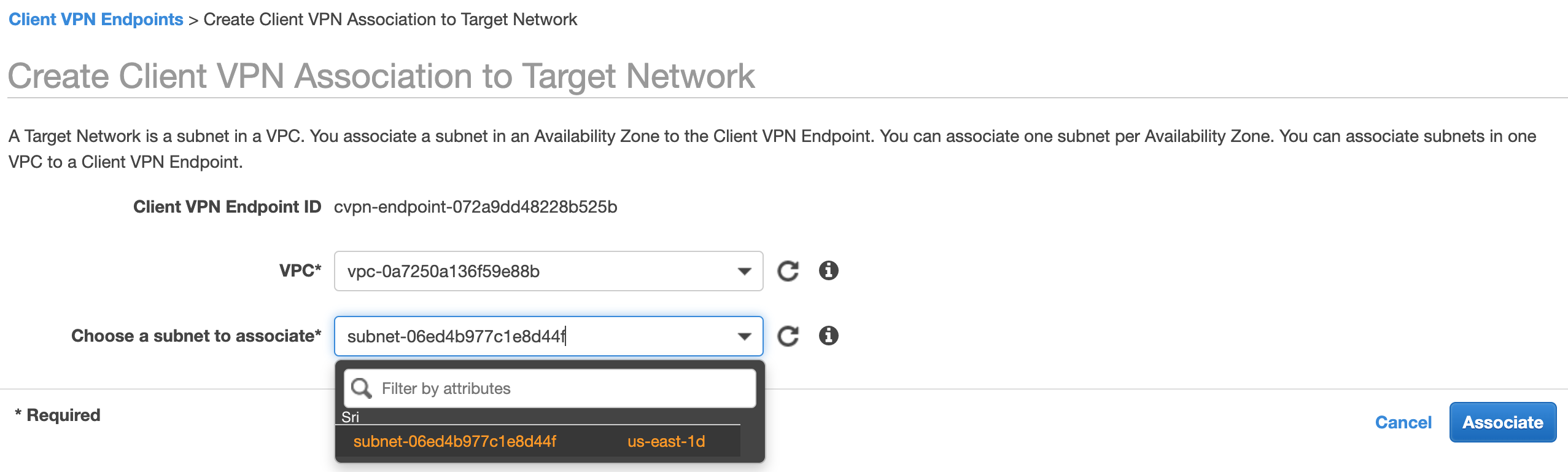
- Navigate to
VPC Console>Client VPN Enpoints> ChooseClinet VPN EndPoint> ClickAssociations> ClickAsscociate - Select the VPC (same VPC as in Step 1) and a subnet
- Click on
Associate
Note: If authorization rules allow it, one subnet association is enough for clients to access a VPC's entire network. You can associate additional subnets to provide high availability in case one of the Availability Zones goes down.
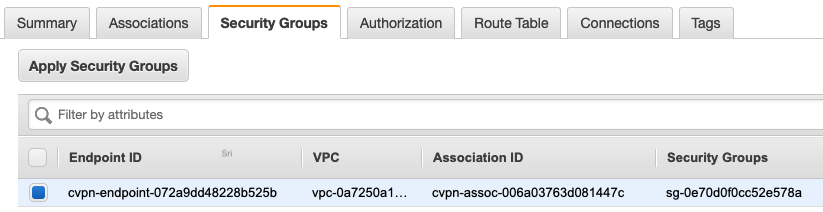
The following are created when we associate the Client VPN Enpoint with the first subnet
- The state of the Client VPN endpoint changes to available. Clients can now establish a VPN connection, but they cannot access any resources in the VPC until you add the authorization rules.
- The local route of the VPC is automatically added to the Client VPN endpoint route table.
- The VPC's default security group is automatically applied for the subnet association.
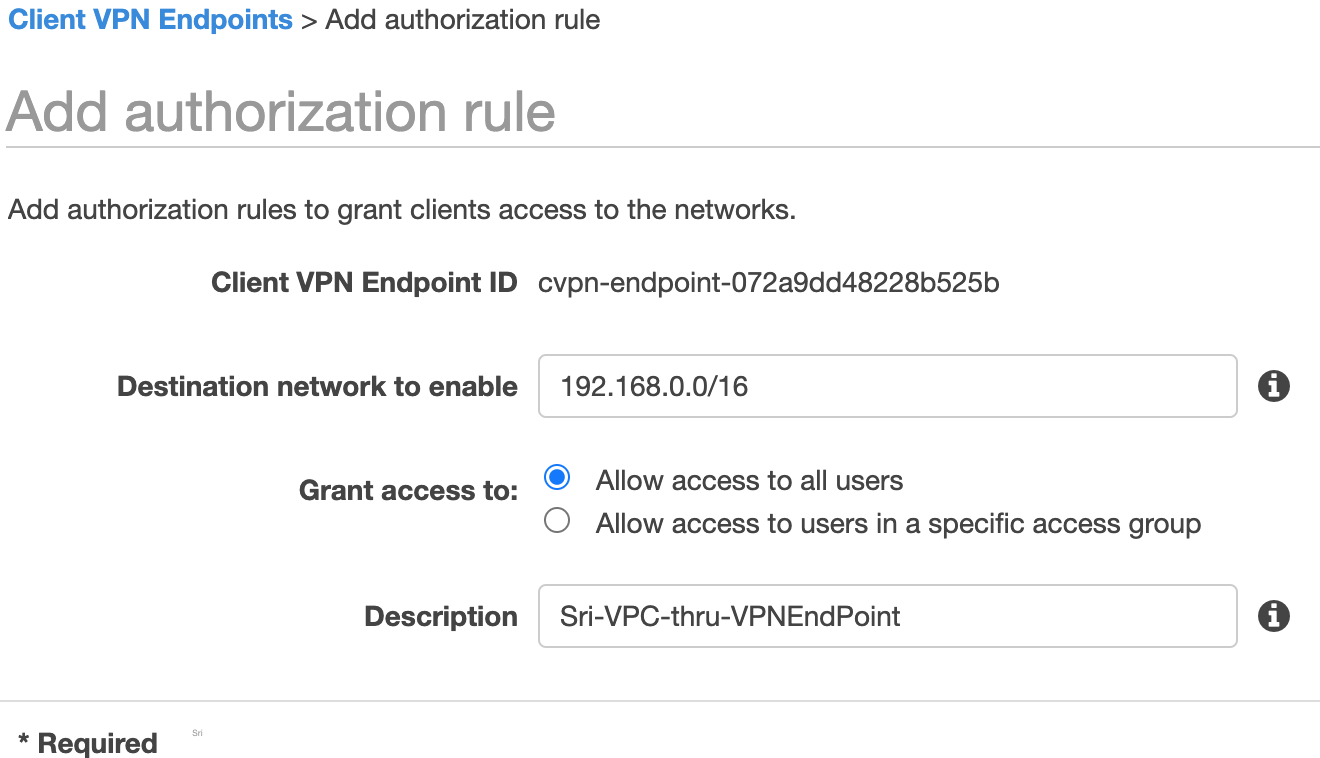
- Navigate to
VPC Console>Client VPN Enpoints> ChooseClinet VPN EndPoint> ClickAuthorization> ClickAuthorize Ingress - Enter
192.168.0.0/16forDestination network to enable,Allow access to all usersforGrant access toand Description asVPC-through-VPNEndPoint - Click
Add authorization rule
You can enable access to additional networks connected to the VPC, such as AWS services, peered VPCs, and on-premises networks. For each additional network, you must add a route to the network and configure an authorization rule to give clients access. More information at Step 5 of Getting started with Client VPN
- Navigate to
VPC Console>Client VPN Enpoints> ClickDownload Client Configuration - Open Client VPN endpoint configuraiton file and add the contents of the client certificate between tags and the contents of the private key between tags.
<cert>
Contents of client certificate (.crt) file, which is client1.domain.tld.crt under the same direcroty when the server and client certificates are located
</cert>
<key>
Contents of private key (.key) file, which is client1.domain.tld.crt
</key>
- Prepend a random string to the Client VPN endpoint DNS name and add it to Client VPN endpoint configuraiton file as shown below.
remote srivpc.cvpn-endpoint-072a9dd48228b525b.prod.clientvpn.us-east-1.amazonaws.com 443
- Save the file.
- You could distribute the Client VPN endpoint configuration file to your clients if required.
Sample Client VPN endpoint configuraiton file
Note: This is for Mac OS
- Download latest [VPN client application] (https://docs.aws.amazon.com/vpn/latest/clientvpn-user/client-vpn-connect-macos.html)
- Open the AWS VPN Client app.
- Choose File, Manage Profiles.
- Enter
Display Name, SelectVPN Configuration Fileand clickVPN Configuration File - Click Connect.
- When the connectivity is established, you can see OpenVPN Statistics by clicking on
Connection>Show Details - You could also check under
Connectionstab underClient VPN Endpoint - We can also launch an EC2 instance in the private subnet created in Step 1 and connect to it.
[Source] (https://docs.aws.amazon.com/vpn/latest/clientvpn-admin/scaling-considerations.html)
The maximum number of concurrent VPN connections depends on the following
👉 Points to note:
- When we create a Client VPN endpoint, we must specify a client CIDR range, which is an IPv4 CIDR block between a /12 and /22 netmask.
- Each VPN connection to the Client VPN endpoint is assigned a unique IP address from the client CIDR range.
- A portion of the addresses in the client CIDR range are also used to support the availability model of the Client VPN endpoint, and cannot be assigned to clients.
- We cannot change the client CIDR range after you create the Client VPN endpoint.
👉 Points to note:
- When we associate a subnet with a Client VPN endpoint, we enable users to establish VPN sessions to the Client VPN endpoint. We can associate multiple subnets with a Client VPN endpoint for high availability, and to enable additional connection capacity.
- We cannot associate multiple subnets from the same Availability Zone with a Client VPN endpoint. Therefore, the number of subnet associations also depends on the number of Availability Zones that are available in an AWS Region.
- For example, if you expect to support 4,000 VPN connections to your Client VPN endpoint, specify a minimum client CIDR range size of /19 (8,192 IP addresses), and associate at least 2 subnets with the Client VPN endpoint.
- If you’re unsure what the number of expected VPN connections is for your Client VPN endpoint, we recommend that you specify a size /16 CIDR block or larger.
For US East (N. Virginia)
- AWS Client VPN endpoint association $0.10 per hour
- AWS Client VPN connection $0.05 per hour
- There is a cost for an
Asscociated VPN Endpointeven when not in use, soDisassociatewhen not in use.