Agent Debugger & Stability Monitor for AI-Assisted Development
Local-first safety for AI coding assistants.
Marketplace Categories: Machine Learning, Testing, Visualization
Current Release: v4.9.9
If this project helps you, please star it! It helps others discover FailSafe.
Quick Start | Documentation | VS Code Extension | Open VSX | Roadmap
FailSafe is open source. Fork it, open issues, and submit pull requests.
FailSafe transitioned from beta to stable release on 2026-02-28. We expect even greater things to come Thank you for being part of our journey. See Terms and Conditions.
Create or edit .failsafe/config/policies/risk_grading.json to tune risk classification:
{
"filePathTriggers": {
"L3": ["auth", "payment", "credential"]
},
"contentTriggers": {
"L3": ["DROP TABLE", "api_key"]
}
}Result: Risk grading overrides are loaded on startup when this JSON file is present. Defaults apply when it is missing. Top-level sections replace defaults, so include full sections if you want to preserve them.
FailSafe is an open-source VS Code extension and stability monitoring framework for AI-assisted development. It adds intent-gated saves, Sentinel audits, and a ledgered audit trail so risky changes are surfaced and controlled.
FailSafe separates system awareness from system control.
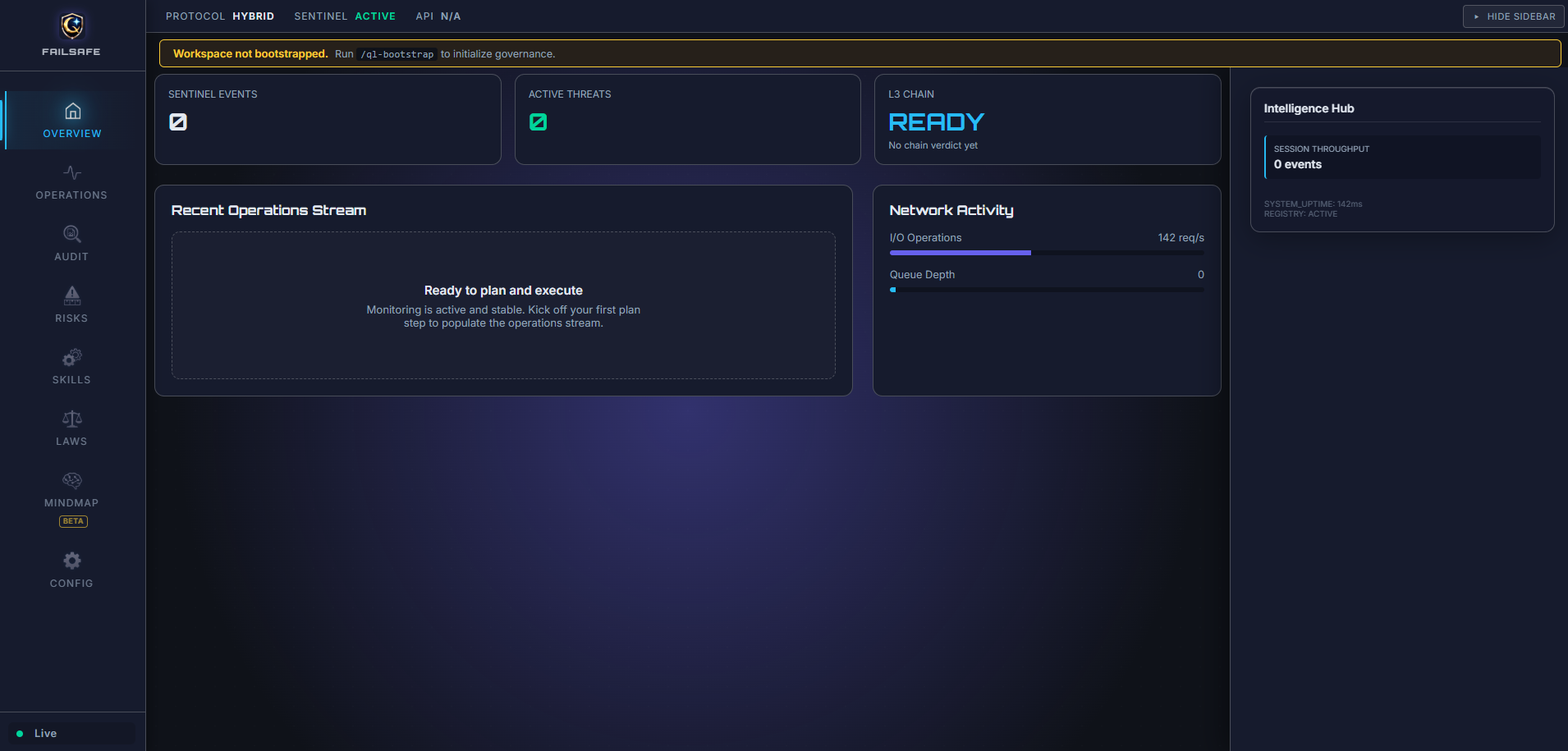
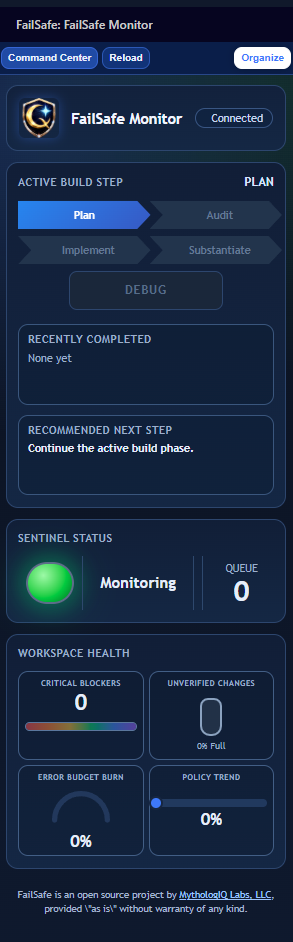
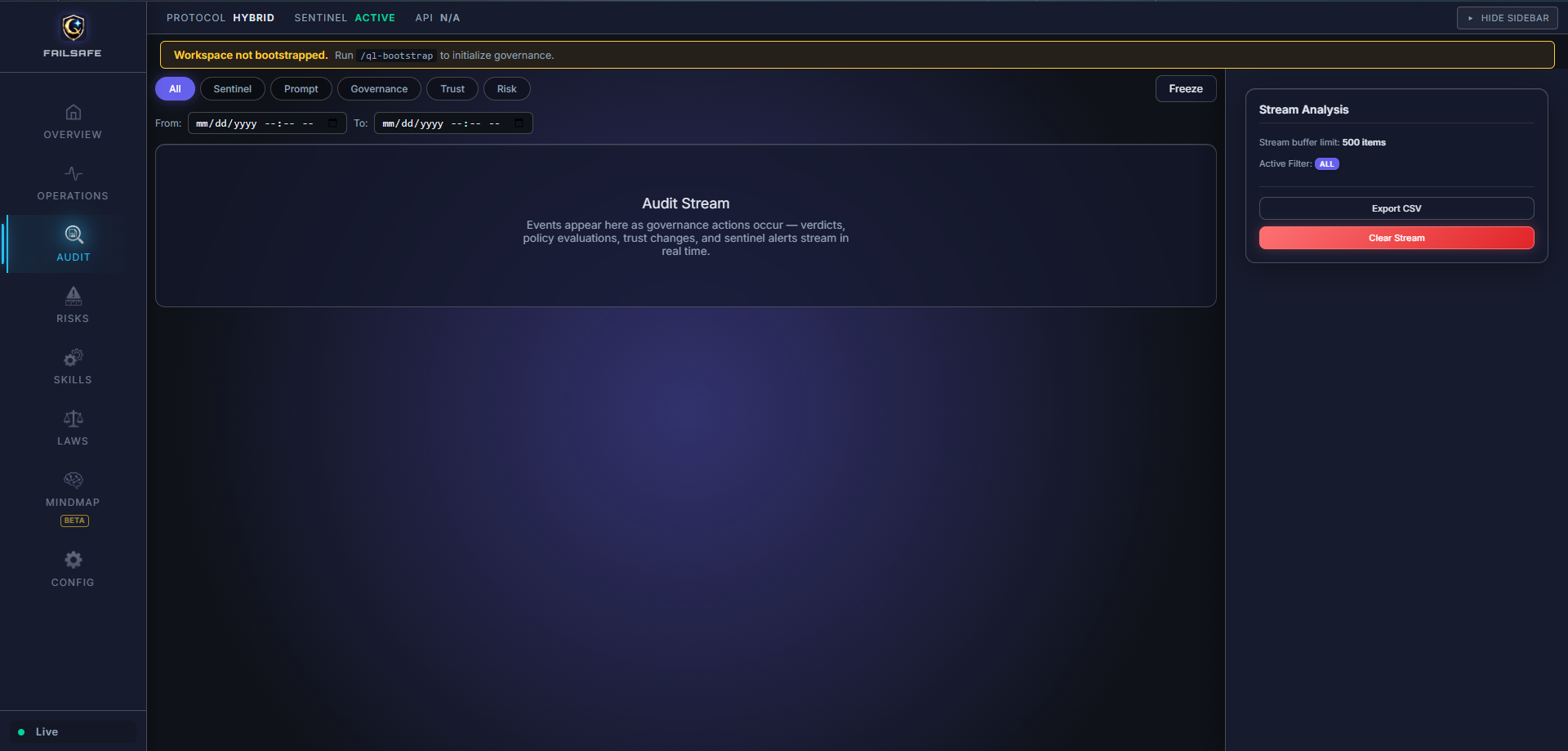
The Monitor provides real-time visibility into system health, governance posture, and operational risk. It is designed for continuous, low-effort awareness.
The Command Center is the primary control surface where teams plan, execute, and govern AI workflows. All configuration, orchestration, and audits originate here.
This separation reduces cognitive load and mirrors real-world operations environments: observe first, act deliberately.
Primary UI surfaces in the current release:
FailSafe Monitor(compact)FailSafe Command Center(extended)
Prompt-based safety asks the LLM to follow rules. The LLM decides whether to comply.
Kernel-style safety evaluates actions at the editor boundary using policies, heuristics, and optional LLM analysis.
graph TD
A[User Actions] --> B[Intent Service]
B --> C{Enforcement}
C -- Allowed --> D[File System]
C -- Blocked --> E[User Approval]
F[AI Agent] --> G[MCP Server]
G --> H[Sentinel Audit]
H --> I[SOA Ledger]
I --> J[FailSafe Command Center]
H --> J
FailSafe uses a Physical Isolation model to separate workspace governance from application development.
/ (root)
+-- .agent/ # Active workspace workflows
+-- .claude/ # Active commands + secure tokens
+-- .qorelogic/ # Workspace configuration (locked)
+-- docs/ # Workspace governance (Ledger, State, Spec)
+-- FAILSAFE_SPECIFICATION.md -> docs/FAILSAFE_SPECIFICATION.md
/FailSafe/ (container)
+-- extension/ # VS Code Extension TypeScript Project
+-- build/ # Build & validation tooling
Note: A single extension publishes to both VS Code Marketplace and Open VSX via GitHub Actions. Claude Code skills are located at .claude/skills/ql-*/SKILL.md.
| System | Layer | Description |
|---|---|---|
| Genesis | Experience | FailSafe Monitor + FailSafe Command Center |
| QoreLogic | Governance | Intent gating, policies, ledger, and trust |
| Sentinel | Enforcement | File watcher audits and verdicts |
FailSafe supports three governance modes to match your workflow needs:
| Mode | Behavior | Best For |
|---|---|---|
| Observe | No blocking, just visibility and logging. Zero friction. | New users, exploration, learning |
| Assist | Smart defaults, auto-intent creation, gentle prompts. Recommended. | Most development workflows |
| Enforce | Full control, intent-gated saves, L3 approvals. | Compliance, regulated industries |
Switch modes via the FailSafe: Set Governance Mode command or the failsafe.governance.mode setting.
QoreLogic is the deterministic governance engine that enforces safety policies at the editor boundary. It operates on a fundamental principle: governance decisions are made by code, not by asking an LLM to follow rules.
| Aspect | Prompt-Based Safety | QoreLogic Deterministic Governance |
|---|---|---|
| Decision Maker | LLM interprets rules | TypeScript code executes rules |
| Consistency | Varies with context, temperature, model | Identical output for identical input |
| Auditability | Opaque reasoning chain | Explicit code path, logged decisions |
| Bypass Risk | LLM can ignore or reinterpret | Code cannot be persuaded |
| Speed | Network latency + inference | Sub-millisecond local execution |
-
Risk Classification — Files are classified as L1 (low), L2 (medium), or L3 (high) risk based on:
- File path triggers (e.g.,
auth/,payment/,credential→ L3) - Content triggers (e.g.,
DROP TABLE,api_key,private_key→ L3) - Configurable via
.failsafe/config/policies/risk_grading.json
- File path triggers (e.g.,
-
Policy Evaluation — Each risk grade has deterministic requirements:
- L1: Heuristic check, 10% sampling, auto-approve
- L2: Full Sentinel pass, no auto-approve
- L3: Formal verification + human approval required
-
Ledger Recording — Every governance decision is recorded to an append-only SOA ledger with:
- Agent identity and trust score
- Artifact path and risk grade
- Timestamp and decision rationale
-
Trust Dynamics — Agent trust scores evolve based on outcomes:
- Approved L3 actions → trust increase
- Rejected or failed actions → trust decrease
- Trust scores influence future routing decisions
When an LLM is asked to enforce safety rules, it can:
- Reinterpret rules based on context
- Produce inconsistent decisions across similar inputs
- Be influenced by prompt engineering attacks
QoreLogic avoids these risks by executing deterministic TypeScript code at the governance boundary. The policy engine uses simple string matching and path analysis—no LLM inference required for governance decisions.
Example: A file containing api_key will always trigger L3 classification. No prompt can persuade the code to ignore this trigger.
| Extension | Description |
|---|---|
| VS Code | Save-time governance, audits, and dashboards |
FailSafe provides governance for multiple AI development environments:
Install the FailSafe extension for real-time governance, audits, and dashboards.
VS Code Marketplace:
ext install MythologIQ.mythologiq-failsafe
Or: https://marketplace.visualstudio.com/items?itemName=MythologIQ.mythologiq-failsafe
Open VSX (VSCodium, Gitpod, etc.):
ext install MythologIQ.mythologiq-failsafe
Or: https://open-vsx.org/extension/MythologIQ/mythologiq-failsafe
Install from Open VSX (VSCodium, Gitpod, Cursor, etc.):
ext install MythologIQ.mythologiq-failsafe
Or: https://open-vsx.org/extension/MythologIQ/mythologiq-failsafe
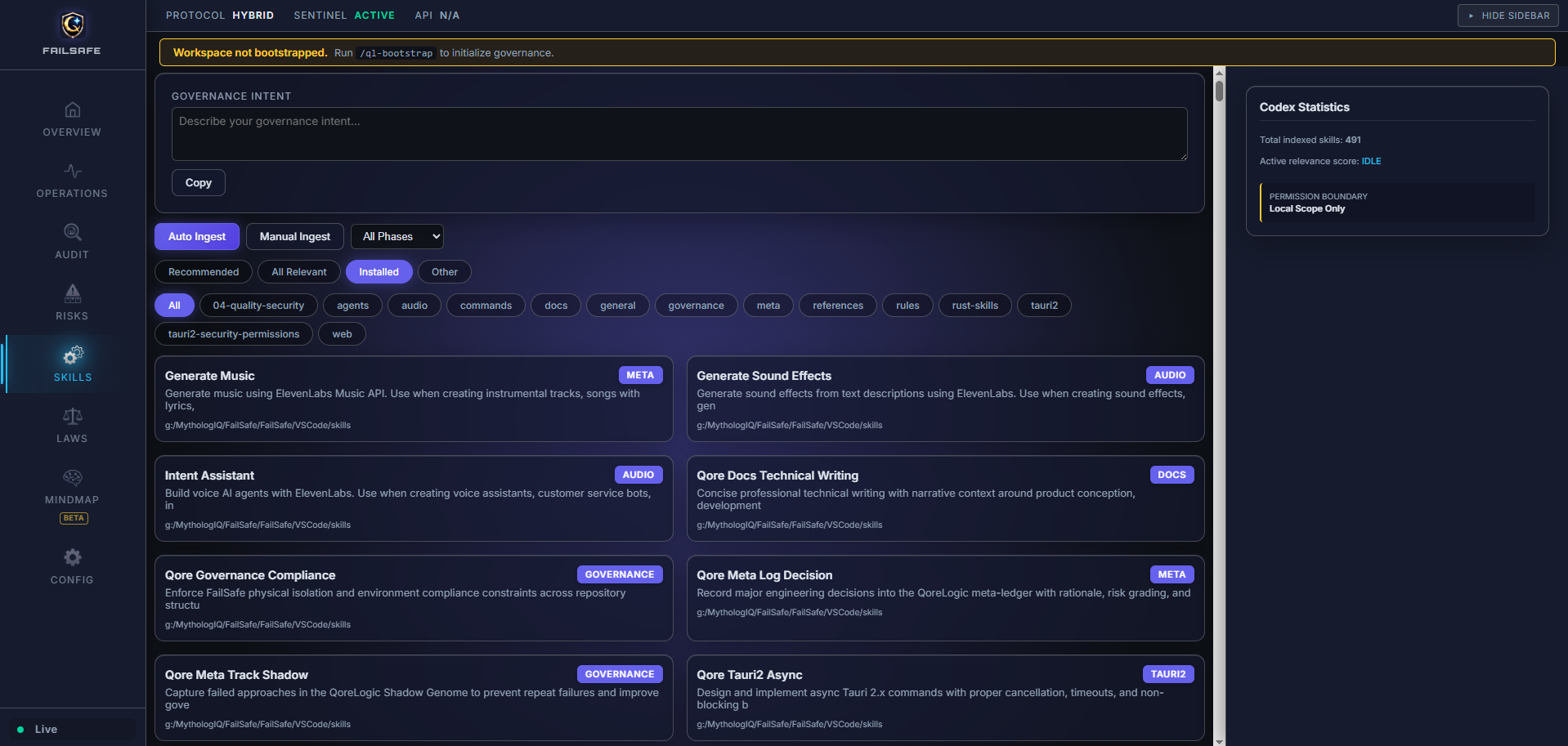
The Antigravity extension includes:
- Gemini/Antigravity workflows (
.agent/workflows/) - Claude Code skills (
.claude/skills/ql-*/SKILL.md) - QoreLogic personas (Governor, Judge, Specialist)
- Stability monitoring configuration and skills
Install from VS Code Marketplace:
ext install MythologIQ.mythologiq-failsafe
Or: https://marketplace.visualstudio.com/items?itemName=MythologIQ.mythologiq-failsafe
The VSCode extension includes:
- Copilot prompt files (
.github/prompts/) - Claude Code skills (
.claude/skills/ql-*/SKILL.md) - Agent personas (
.github/copilot-instructions/) - Stability monitoring configuration and skills
Both extensions include Claude Code slash commands that map to the physical SHIELD governance lifecycle:
- S - SECURE INTENT (
/ql-bootstrap): Seed project DNA. Document the Why, encode the architecture, initialize the Merkle chain. - H - HYPOTHESIZE (
/ql-plan): Create implementation blueprints with risk grades, file contracts, and Section 4 complexity limits. - I - INTERROGATE (
/ql-audit): Adversarial tribunal. The Judge audits the plan for security, correctness, and drift. PASS or VETO. - E - EXECUTE (
/ql-implement): Build under KISS constraints after a PASS verdict. Functions under 40 lines. Nesting under 3 levels. - L - LOCK PROOF (
/ql-substantiate): Verify Reality matches Promise. Cryptographically seal the session with Merkle hash verification. - D - DELIVER (
/ql-release): Deploy, inspect packaged artifacts before publish, hand off with traceability, and monitor for operational drift.
# Run FailSafe locally
cd FailSafe/extension
npm install
npm run compileAgent debugging, execution replay, and cross-agent skill portability.
- Agent Run Replay and Execution Timeline - Step-by-step replay of AI agent execution traces with a filterable event timeline and severity indicators for rapid root-cause analysis.
- Risk and Stability Indicators - Composite health score displayed in the status bar, combining risk grade distribution, Sentinel verdicts, and trust dynamics into a single signal.
- Shadow Genome and DiffGuard Panels - Failure pattern analysis (Shadow Genome) and AI diff risk analysis (DiffGuard) surfaced as dedicated debugging panels in the Command Center.
- Cross-Agent Skill Propagation - Skills defined once propagate across Claude Code, Codex CLI, GitHub Copilot, Gemini, Cursor, and Windsurf via standardized adapters.
We'd love your review! If FailSafe is useful to you, please leave a review on the VS Code Marketplace or Open VSX. Your feedback helps other developers discover FailSafe and directly shapes its roadmap. Bug reports and feature requests welcome on GitHub Issues.
- CI/CD Pipeline Enforcer: Headless Judge verification validating
failsafe_checkpointsvia cryptography during PRs. - Shared "Core Axioms": IDE startup synchronization of enterprise-level Policy and Axioms to enforce team-wide Q-DNA compliance.
- Air-Gapped Judge Verification: Support for routing L3 architectural audits to local LLMs (Ollama, LM Studio, etc.) for zero-leak compliance.
- CLI Overseer Lite: Lightweight CLI-compatible FailSafe for direct website integration.
FailSafe is a stable release. While we strive for reliability and completeness, all software carries inherent risks.
FailSafe is provided "as is" without warranties of any kind, express or implied. While we have made every effort to ensure the software's reliability and security, you acknowledge that you use this software at your own risk.
By using FailSafe, you agree to the following:
-
Use at Your Own Risk: FailSafe is designed to assist with debugging and stability monitoring for AI-assisted development, but it cannot guarantee complete protection against all risks. You remain responsible for reviewing and validating all AI-generated code and decisions.
-
No Warranty: MythologIQ provides no warranties, express or implied, including but not limited to warranties of merchantability, fitness for a particular purpose, or non-infringement.
-
Limitation of Liability: MythologIQ shall not be liable for any direct, indirect, incidental, special, consequential, or punitive damages arising from use of FailSafe, including but not limited to loss of data, downtime, business interruption, or any other damages.
-
Data Backups: You are responsible for maintaining appropriate backups of your work. FailSafe includes governance and checkpoint features, but these do not replace proper backup practices.
-
Compliance: You are responsible for ensuring your use of FailSafe complies with applicable laws, regulations, and organizational policies.
-
Updates and Changes: FailSafe may receive updates that include new features, bug fixes, or changes to existing functionality. You are responsible for reviewing release notes and understanding how updates may affect your workflow.
-
Feedback and Contributions: We welcome feedback, bug reports, and contributions. By contributing, you agree to license your contributions under the project's MIT license.
Thank you for being part of our journey. Your trust and feedback help us improve FailSafe for everyone.
git clone https://github.com/MythologIQ/FailSafe.git
cd FailSafe
npm installMIT - See LICENSE
FailSafe tracks more than Git state. It records governance checkpoints as signed metadata records, then stores Sentinel observations in a local retrieval store so operators can recover the what, why, and how of runtime decisions.
- Git readiness is enforced at bootstrap (
ensureGitRepositoryReady), including optional auto-install andgit initwhen needed. - Governance events are checkpointed into
failsafe_checkpointswith run/phase/status context and deterministic hashes. - Each checkpoint carries
git_hash,payload_hash,entry_hash, andprev_hashso chain integrity can be recomputed. - Hub and API surfaces expose both summary and recent checkpoint records for operational visibility.
- Sentinel writes local memory records to
.failsafe/rag/sentinel-rag.db(or JSONL fallback), includingpayload_json,metadata_json, and retrieval text.
- Tamper evidence via hash-chained checkpoint records.
- Git-linked governance state for repository-correlated audit trails.
- Local-first memory retention for security and low-latency recall.
- Deterministic fallback paths when SQLite is unavailable.
| Claim | Status | Source |
|---|---|---|
Checkpoints persist in failsafe_checkpoints with typed governance fields. |
implemented | FailSafe/extension/src/roadmap/RoadmapServer.ts |
Checkpoint records include hash-chain material (payload_hash, entry_hash, prev_hash). |
implemented | FailSafe/extension/src/roadmap/RoadmapServer.ts |
| Each checkpoint captures current Git head/hash context. | implemented | FailSafe/extension/src/roadmap/RoadmapServer.ts |
| Checkpoint history and chain validity are exposed over API. | implemented | FailSafe/extension/src/roadmap/RoadmapServer.ts |
Hub snapshot includes checkpointSummary and recentCheckpoints. |
implemented | FailSafe/extension/src/roadmap/RoadmapServer.ts |
| Sentinel local RAG persists observation payload + metadata + retrieval text. | implemented | FailSafe/extension/src/sentinel/SentinelRagStore.ts |
| Sentinel RAG can fall back to JSONL when SQLite is unavailable. | implemented | FailSafe/extension/src/sentinel/SentinelRagStore.ts |
RAG writes are controlled by failsafe.sentinel.ragEnabled (default true). |
implemented | FailSafe/extension/src/sentinel/SentinelDaemon.ts |
| Checkpoint and Sentinel RAG tables are independent (no foreign-key link). | false | Confirmed: failsafe_checkpoints (ledger DB) and sentinel_observations (RAG DB) are in separate databases with no shared keys. evidenceRefs is always []. |