This repository was archived by the owner on Dec 19, 2023. It is now read-only.
Arbitrary code execution fix: Replace exec with execFile #1
Open
d3v53c wants to merge 1 commit into418sec:masterfrom
Open
Arbitrary code execution fix: Replace exec with execFile #1d3v53c wants to merge 1 commit into418sec:masterfrom
d3v53c wants to merge 1 commit into418sec:masterfrom
Conversation
huntr-helper
pushed a commit
to 418sec/huntr
that referenced
this pull request
Feb 4, 2021
|
👋 Hello, @andrewimm - @d3v53c has opened a PR to us with a fix for a potential vulnerability in your repository. To view the vulnerability, please refer to the bounty URL in the first comment, above. Ultimately, you get to decide if the fix is 👍 or 👎. If you are happy with the fix, please write a new comment ( If you have any questions or need support, come and join us on our community Discord! @andrewimm & @d3v53c - thank you for your efforts in securing the world’s open source code! 🎉 |
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to subscribe to this conversation on GitHub.
Already have an account?
Sign in.
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
📊 Metadata *
Command Injection in
xopenBounty URL: https://www.huntr.dev/bounties/1-npm-xopen/
⚙️ Description *
Used child_process.execFile() instead of child_process.exec().
💻 Technical Description *
The use of the child_process function exec() is highly discouraged if you accept user input and don't sanitize/escape them. This PR replaces it with execFile() which mitigates any possible Command Injections as it accepts input as arrays.
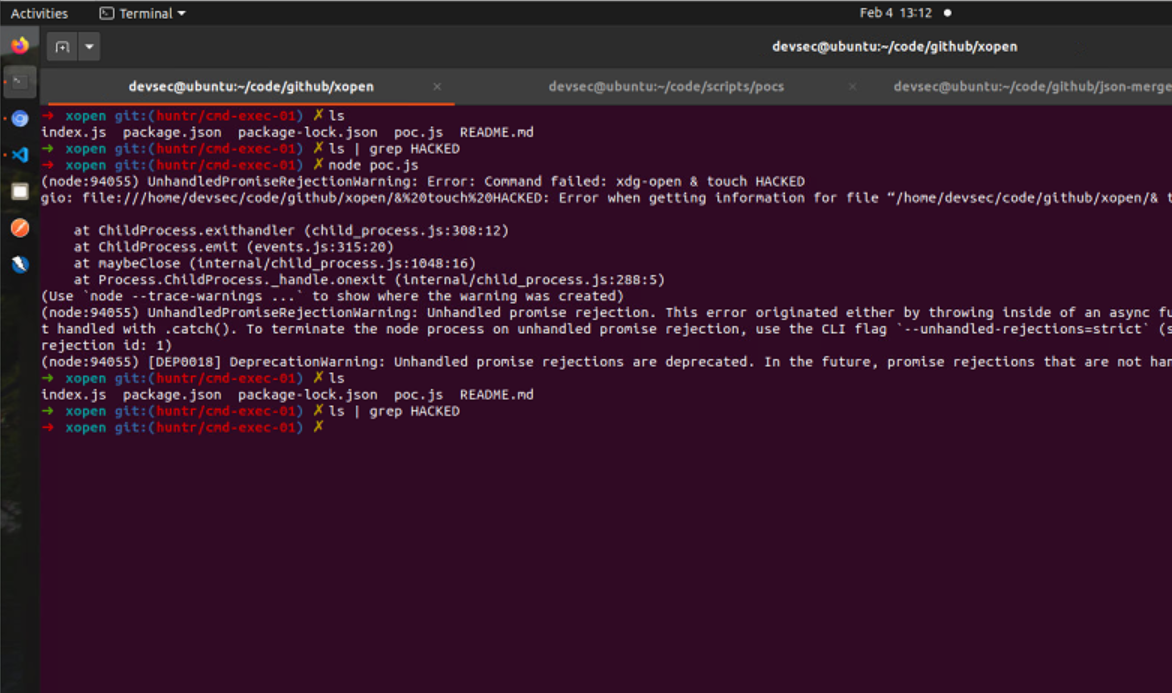
🐛 Proof of Concept (PoC) *
3.Check the Output using ls command before and after the execution.
🔥 Proof of Fix (PoF) *
Before:
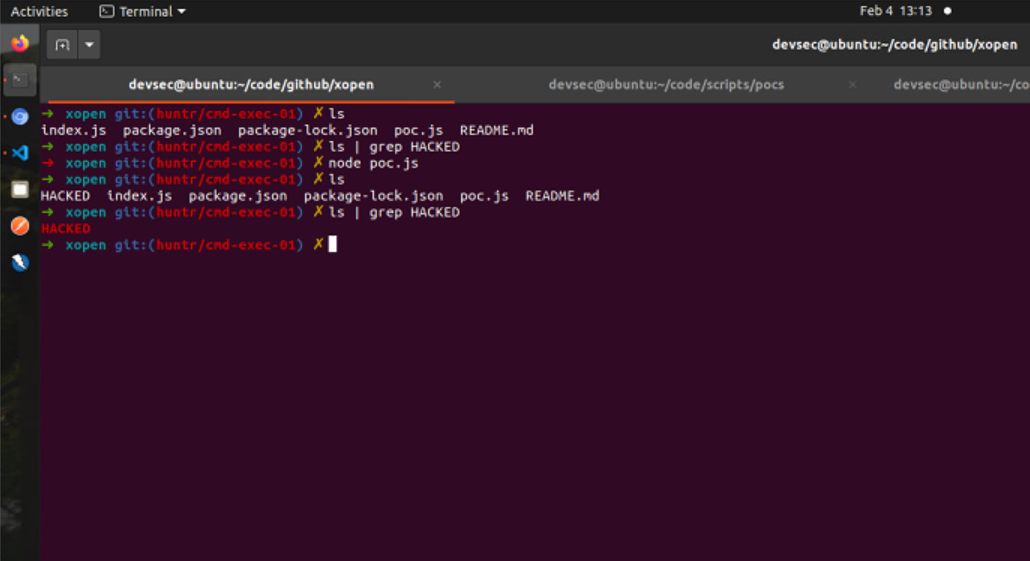
After:
👍 User Acceptance Testing (UAT)
After the fix, functionality is unaffected.
🔗 Relates to...
418sec/huntr#1838