[HUDI-4991] Allow kafka-like configs to set truststore and keystore for the SchemaProvider#7576
Merged
nsivabalan merged 1 commit intoapache:masterfrom Jan 25, 2023
Merged
Conversation
Contributor
|
Can you check CI failures. |
CTTY
reviewed
Jan 17, 2023
hudi-utilities/src/main/java/org/apache/hudi/utilities/schema/SchemaRegistryProvider.java
Outdated
Show resolved
Hide resolved
CTTY
reviewed
Jan 17, 2023
hudi-utilities/src/main/java/org/apache/hudi/utilities/schema/SchemaRegistryProvider.java
Outdated
Show resolved
Hide resolved
CTTY
reviewed
Jan 17, 2023
Contributor
 CTTY
left a comment
CTTY
left a comment
There was a problem hiding this comment.
Thanks for the contribution! This LGTM in general, left some minor comments.
codope
reviewed
Jan 23, 2023
| } | ||
| sslSocketFactory = sslContextBuilder.build().getSocketFactory(); | ||
| } catch (UnrecoverableKeyException | IOException | KeyStoreException | NoSuchAlgorithmException | CertificateException | KeyManagementException e) { | ||
| throw new RuntimeException(e); |
Member
There was a problem hiding this comment.
Should we wrap in HoodieIOException instead of RuntimeException, after all it's file i/o?
hudi-utilities/src/test/java/org/apache/hudi/utilities/schema/TestSchemaRegistryProvider.java
Outdated
Show resolved
Hide resolved
777e992 to
0a0d47d
Compare
nsivabalan
approved these changes
Jan 24, 2023
Collaborator
Contributor
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
Change Logs
Update the SchemaRegistryProvider to take in kafka-like configs for truststore and keystore.
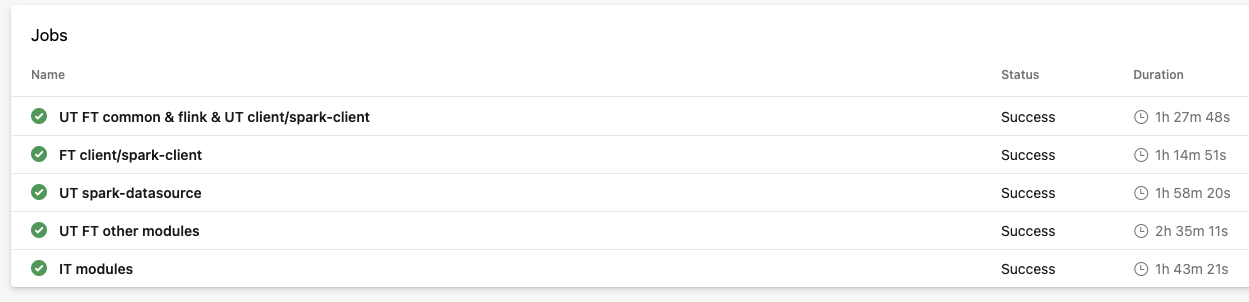
Testing:
To test this, I modified the examples from Oracle's Sample Code Illustrating a Secure Socket Connection Between a Client and a Server to work similarly to the SchemaRegistryProvider code. To set up the client and server truststore and keystore, I followed the guide from this comment. Note that you should make common name 'localhost'. In step 4, the password that goes in the command line parameter is the PEM pass phrase. Additionally in steps 7 and 8 you are setting the truststore passwords even though you will be prompted to set a keystore password.
ClassFileServer.java
ClassServer.java
SSLSocketClient.java
Impact
User requested this feature in this issue
Risk level (write none, low medium or high below)
medium
The testing above was done to make sure this change will work
Documentation Update
N/A
Contributor's checklist