Describe the issue
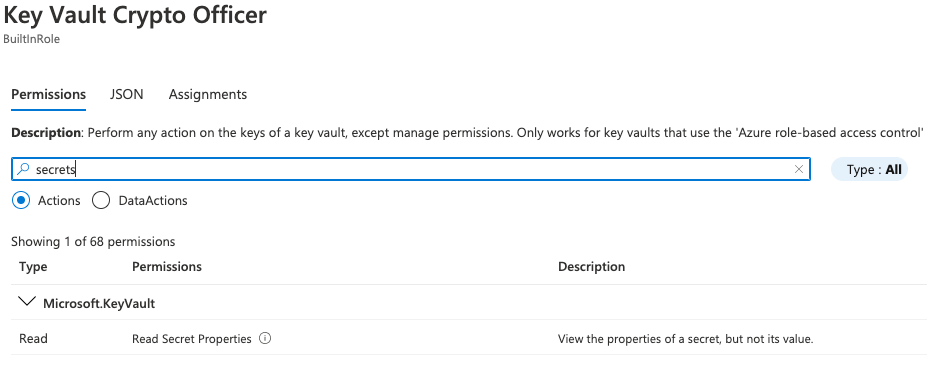
In the Key Vault component docs, the role assignment suggested for the Azure AD application is “Key Vault Crypto Officer” which is described as having "broad access". The majority of users will use this assignment and make the assumption it is going to allow them to access secrets. However, this role does not allow you to access KV secrets. In order to prevent customers from running into 403 issues when trying to make use of the component, I believe a different role should be recommended. Another solution would be to provide a link to the official RBAC docs and tell them to choose the appropriate role based on what they are trying to accomplish.
URL of the docs
https://docs.dapr.io/reference/components-reference/supported-secret-stores/azure-keyvault/
Expected content
I assign a role to the Service Principal that allows it to read secrets from Key Vault i.e. Key Vault Secrets Officer vs. Key Vault Crypto Officer. I tested this via REST APIs and also made the respective change in role assignment for the SP to resolve the issue.
Screenshots
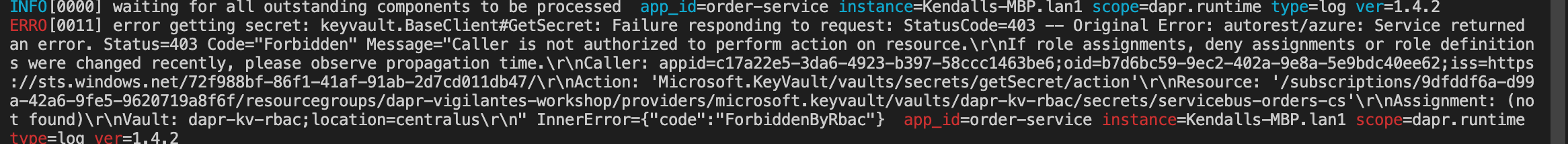
If I try to reference the Azure Key Vault component in a different component to retrieve a secret- I will get the following error using the recommended role. While it makes sense based on the role permissions, it isn't intuitive based on the docs to think that secrets would not be retrievable using the above role
Describe the issue
In the Key Vault component docs, the role assignment suggested for the Azure AD application is “Key Vault Crypto Officer” which is described as having "broad access". The majority of users will use this assignment and make the assumption it is going to allow them to access secrets. However, this role does not allow you to access KV secrets. In order to prevent customers from running into 403 issues when trying to make use of the component, I believe a different role should be recommended. Another solution would be to provide a link to the official RBAC docs and tell them to choose the appropriate role based on what they are trying to accomplish.
URL of the docs
https://docs.dapr.io/reference/components-reference/supported-secret-stores/azure-keyvault/
Expected content
I assign a role to the Service Principal that allows it to read secrets from Key Vault i.e. Key Vault Secrets Officer vs. Key Vault Crypto Officer. I tested this via REST APIs and also made the respective change in role assignment for the SP to resolve the issue.
Screenshots
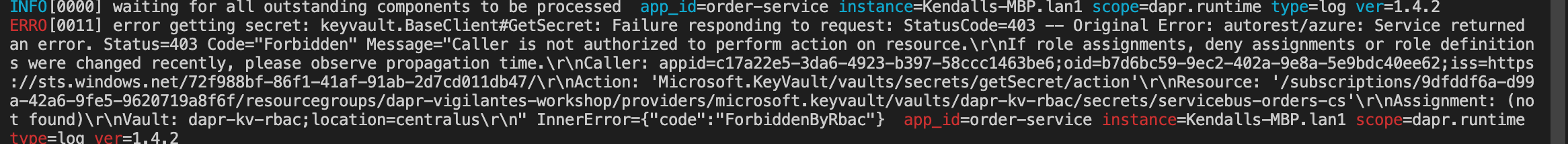
If I try to reference the Azure Key Vault component in a different component to retrieve a secret- I will get the following error using the recommended role. While it makes sense based on the role permissions, it isn't intuitive based on the docs to think that secrets would not be retrievable using the above role