AcmeClient support cert upload via sftp#1455
Conversation
This change avoids that all contents in any subfolder is set to mode 0750 as this is illegal e.g. for private keys for SSH.
29d762c to
16e0baf
Compare
|
@jkellerer First of all: thanks, this looks very good at first glance. I'll do a proper review later. I've noticed that the "remote path" is configurable. Could you also make the remote filenames configurable, so that one could freely choose the filename on the target host for the certificate, private key and ca? |
|
@fraenki, thanks for the prompt and nice feedback. Yes it may really make sense to configure file names (or better paths) as well since the certs can then be placed right at the desired location with the correct naming. I'm thinking to use template values like this " |
Just to be sure we're talking about the same thing: I'd like to be able to use "my_cert_name.crt" as target filename instead of "cert.pem". Same for key and ca filenames. :) |
|
Yes we do, I think :) .. currently the final path is created as " |
Filename templates for cert, key and ca-chain can be configured in the UI and user input is sanitized to ensure valid file names are produced. New and some existing fields are using "advanced" markers to reduce amount of fields visible in the default UI. Also fixed minor bugs including one with unicode characters in names.
 fabianfrz
left a comment
fabianfrz
left a comment
There was a problem hiding this comment.
some of my findings in a quick review.
security/acme-client/src/opnsense/mvc/app/views/OPNsense/AcmeClient/actions.volt
Show resolved
Hide resolved
security/acme-client/src/opnsense/mvc/app/views/OPNsense/AcmeClient/actions.volt
Outdated
Show resolved
Hide resolved
security/acme-client/src/opnsense/scripts/OPNsense/AcmeClient/upload_sftp.php
Outdated
Show resolved
Hide resolved
security/acme-client/src/opnsense/scripts/OPNsense/AcmeClient/upload_sftp.php
Outdated
Show resolved
Hide resolved
6c267d5 to
a93b802
Compare
|
@jkellerer I haven't read all recent commits yet, so... do you consider it to be ready for merge? If that is the case I'd like to do some testing on my own before merging it. |
|
@fraenki I've tested it after the refactoring on 3 different SSH servers (one with non default port and non default SSH implementation) that's why I added some extra commits. |
@jkellerer I've merged the current state. Thanks for your contribution! 👍 However, I'd like to see freely configurable filenames. Hope you'll find some time to contribue this in a future PR :) (Due to my notoriously bad timing this won't be in tomorrow's 19.7.4 release, but instead in the next release.) |
|
Thanks a lot, @fraenki . Btw. names for all 3 files can be set in "Advanced Mode" (along with unix permissions, group-id and alternate SSH port). So no need for an additional PR, it's already there :) |
Thanks! 👍 |
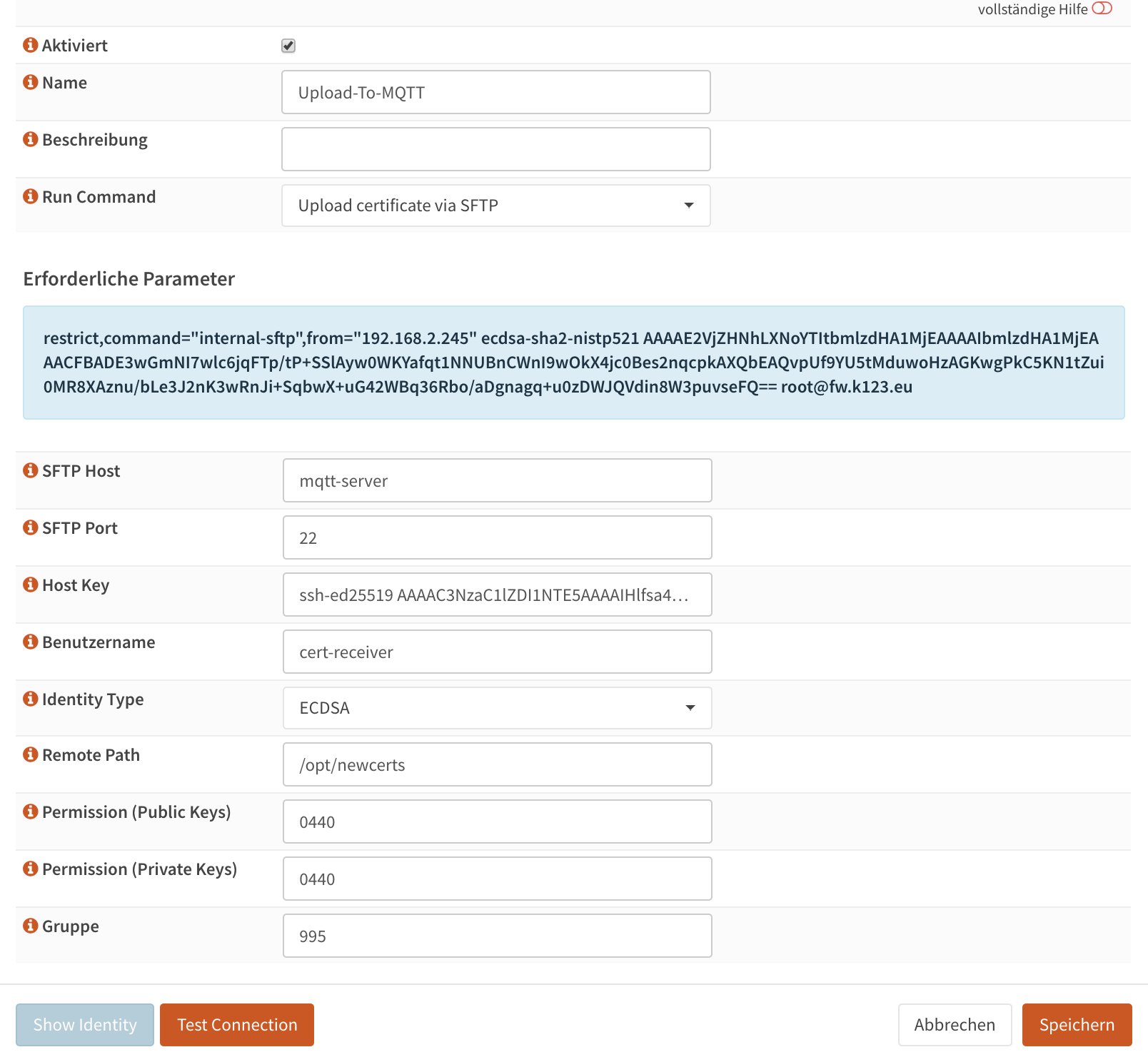
This PR implements a new automation action for the Let's Encrypt (AcmeClient) client that allows to deploy certs to remote hosts using SFTP after they have been created or renewed.
The purpose of the extension is to securely transfer certificates generated on the firewall to protected hosts that may not be public reachable on ports required to generate certs directly.
Notes:
./upload_sftp.php --log --certificates=my.domain.orgwhich will run all SFTP upload automations assigned to this cert and print detailed log to the console.More examples can be found via "
--help".Screenshot of UI enhancements: