?? Disclaimer: This project is intended strictly for educational and security research purposes. The author is not responsible for any misuse, damage, or illegal activity caused by this tool. Use only in isolated lab environments with explicit permission.
KillChain is a user-mode tool that leverages a vulnerable kernel driver (ProcessMonitorDriver.sys, CVE-2026-0828) to terminate protected processes from user space. It communicates with the kernel via a custom IOCTL interface, bypassing standard process protection mechanisms.
The tool embeds the driver binary directly into the executable, extracts it to a temporary location at runtime, registers it as a kernel service, loads it via NtLoadDriver, and sends termination requests through DeviceIoControl.
KillChain/
??? KillChain.cpp — Entry point, CLI argument parsing, main termination loop
??? LoadDriver.h — Driver extraction, service registration, NtLoadDriver/NtUnloadDriver logic
??? Logger.h — Thread-safe console/file logging with color-coded output
??? driverBytes.h — Embedded driver binary (raw byte array)
ProcessMonitorDriver.sys (embedded inside the executable)
??? Exposes IOCTL_KILL_PROCESS (0xB822200C) — terminates a target process by PID
1. Parse CLI arguments
2. Extract embedded .sys ? %TEMP%\EmbeddedDriverService.sys
3. Create registry service key + register via SCM
4. Load driver into kernel via NtLoadDriver (requires SeLoadDriverPrivilege)
5. Open device handle: \\.\STProcessMonitorDriver
6. Loop (up to 360 seconds):
a. Resolve PID by name on every iteration (if --name was used)
b. Send IOCTL_KILL_PROCESS with the target PID
c. After 2 successful kills, optionally disable Windows Defender via registry
7. Close device handle; optionally run --uninstall-driver cleanup
| Feature | Description |
|---|---|
| Kill by PID | Terminate any process by its numeric PID via kernel IOCTL |
| Kill by name | Resolve and terminate a process by executable name, re-checked each iteration |
| Persistence loop | Continuously monitors and re-terminates the target for up to 360 seconds |
| Disable Defender | Writes to HKLM\SOFTWARE\Policies\Microsoft\Windows Defender to disable real-time protection |
| Embedded driver | Driver binary is baked into the executable — no external .sys file required |
| Driver uninstall | Unloads driver from kernel, removes SCM service, cleans registry, deletes temp file |
| Configurable logging | Four verbosity levels with optional file output |
- Windows 10 / 11 (x64)
- Administrator privileges — required for
SeLoadDriverPrivilegeand registry access - Test Signing Mode enabled, or a valid driver signature
- Visual Studio 2022 with the C++20 toolset
- Open
KillChain.slnin Visual Studio 2022 - Select the Release | x64 configuration
- Press
Ctrl+Shift+Bto build
Output: x64\Release\KillChain.exe
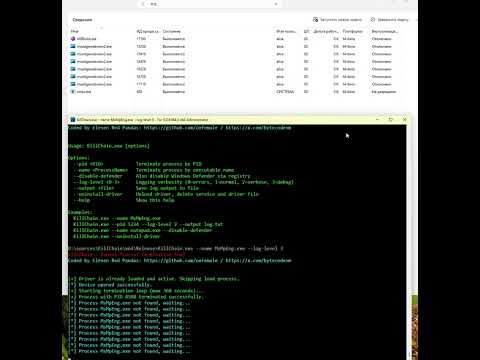
KillChain.exe [options]
Options:
--pid <PID> Terminate process by PID
--name <ProcessName> Terminate process by executable name
--disable-defender Also disable Windows Defender via registry
--log-level <0-3> Logging verbosity (0=errors, 1=normal, 2=verbose, 3=debug)
--output <file> Save log output to file
--uninstall-driver Unload driver, delete service and driver file
--help Show this help
REM Terminate a protected process by name
KillChain.exe --name MsMpEng.exe
REM Terminate by PID with verbose logging written to a file
KillChain.exe --pid 1234 --log-level 2 --output log.txt
REM Kill a process and disable Windows Defender afterwards
KillChain.exe --name notepad.exe --disable-defender
REM Clean up the driver after testing
KillChain.exe --uninstall-driver
| Constant | Value |
|---|---|
IOCTL_KILL_PROCESS |
0xB822200C |
| Field | Type | Description |
|---|---|---|
| Input buffer | ULONG64 |
Target process PID |
| Output buffer | DWORD |
Unused (dummy) |
| Device path | — | \\.\STProcessMonitorDriver |
| Level | Value | Description |
|---|---|---|
LOG_ERROR |
0 | Errors only |
LOG_INFO |
1 | Normal operational messages (default) |
LOG_WARNING |
2 | Warnings and informational messages |
LOG_DEBUG |
3 | Full debug trace |
Output is thread-safe (backed by a CRITICAL_SECTION) and can write to the console with ANSI colors and to a log file simultaneously.
| Step | Win32 / NT API |
|---|---|
| Extract to temp | CreateFile + WriteFile |
| Register service | RegCreateKeyEx + CreateService (SCM) |
| Load into kernel | NtLoadDriver (ntdll) |
| Verify active | EnumDeviceDrivers + GetDeviceDriverBaseName |
| Unload from kernel | NtUnloadDriver (ntdll) |
| Remove service | DeleteService (SCM) + RegDeleteTree |
| Delete temp file | DeleteFile |
CVE-2026-0828 — ProcessMonitorDriver.sys exposes an IOCTL that allows any user-mode caller with a handle to the device to terminate arbitrary processes — including protected system processes — without standard access-control checks.
Eleven Red Pandas
This project is provided for educational and research purposes only. Redistribution or use in production environments is strictly prohibited.