feat: implement refresh schema#373
Conversation
|
Thanks @Danielwinkelmann ❤️ 💯 This would be a great controbution, I will look into it in a bit (: Note already: Tests are failing - can you check it out and resolve it? |
|
@BracketJohn I updated the lock file 
|
|
@BracketJohn I can't figure out the problem. It must be an dependency problem. Maybe we should disable the Listing Rule "import/namespace" |
|
I figured it out! The problem is that you made I:
I wanted to push the fix into your branch but don't have permissions on the fork. So for the time being here's the diff: diff --git a/.github/workflows/ci.yaml b/.github/workflows/ci.yaml
index ab2ac7c..94bff65 100644
--- a/.github/workflows/ci.yaml
+++ b/.github/workflows/ci.yaml
@@ -67,8 +67,6 @@ jobs:
# start prod-app and curl from it
- run: "timeout 60 pnpm start & (sleep 45 && curl --fail localhost:3000)"
-
-
test-playground-authjs:
runs-on: ubuntu-latest
defaults:
@@ -99,3 +97,34 @@ jobs:
env:
AUTH_ORIGIN: 'http://localhost:3001'
PORT: 3001
+
+ test-playground-refresh:
+ runs-on: ubuntu-latest
+ defaults:
+ run:
+ working-directory: ./playground-refresh
+ steps:
+ - uses: actions/checkout@v3
+
+ - name: Use Node.js 16.14.2
+ uses: actions/setup-node@v3
+ with:
+ node-version: 16.14.2
+
+ - uses: pnpm/action-setup@v2
+ name: Install pnpm
+ id: pnpm-install
+ with:
+ version: 8
+
+ # Install deps
+ - run: pnpm i
+
+ # Check building
+ - run: pnpm build
+
+ # start prod-app and curl from it
+ - run: "timeout 60 pnpm start & (sleep 45 && curl --fail localhost:$PORT)"
+ env:
+ AUTH_ORIGIN: 'http://localhost:3002'
+ PORT: 3002
diff --git a/src/module.ts b/src/module.ts
index 72983f3..314d3e4 100644
--- a/src/module.ts
+++ b/src/module.ts
@@ -60,7 +60,8 @@ const defaultsByBackend: { [key in SupportedAuthProviders]: DeepRequired<Extract
refreshToken: {
signInResponseRefreshTokenPointer: '/refreshToken',
maxAgeInSeconds: 60 * 60 * 24 * 7 // 7 days
- }
+ },
+ sessionDataType: { id: 'string | number' }
},
authjs: {
type: 'authjs',
diff --git a/tsconfig.json b/tsconfig.json
index 92f65fd..2a7b6fa 100644
--- a/tsconfig.json
+++ b/tsconfig.json
@@ -1,6 +1,6 @@
{
// Note: we need to explicitly extend one of the playgrounds here in order to have a nice and working typecheckk, otherwise `nuxt`-types are going to be unknown
- "extends": ["./playground-local/.nuxt/tsconfig.json", "./playground-refresh/.nuxt/tsconfig.json"],
+ "extends": "./playground-refresh/.nuxt/tsconfig.json",
"exclude": ["../docs"],
"include": ["src/"]
}
|
This reverts commit 1ecd9d8.
 BracketJohn
left a comment
BracketJohn
left a comment
There was a problem hiding this comment.
Can you please also extends the docs for this feature?
You'd only need to focus on the v0.6 docs. There I remember at least the following places that need an update:
docs/content/v0.6/1.getting-started/1.index.md-> update the feature tabledocs/content/v0.6/1.getting-started/3.quick-start.md-> add a refresh specific section (can also be very small if there's nothing special to consider)docs/content/v0.6/2.configuration/2.nuxt-config.md-> add provider specific config optionsdocs/content/v0.6/3.application-side/2.session-access-and-management.md-> add provider specific section
If in some cases refresh behaves the same as local provicder you can of course keep the sections small and reference the local provider
| @@ -0,0 +1,39 @@ | |||
| import { _fetch } from '../../utils/fetch' | |||
There was a problem hiding this comment.
Here I have some points:
- Do we need this plugin? Can we not rely on the server-side execution of the
plugin.tswe already defined on the app to refresh the token on load? - The existance of this plugin forces the user to have a server, without it refresh could also work for fully-static apps. So if we keep this plugin (depends on the answer to my previous question) we should at least make it opt-in to ensure that static apps still work
| name: 'refresh-token-plugin', | ||
| enforce: 'pre', | ||
| async setup (nuxtApp) { | ||
| // TODO: get rid of duplicate code |
There was a problem hiding this comment.
I think you can resolve this now?
You could add helpers into the refresh/ composable folder and import them here - I guess it's mostly about pointer extraction?
If you want to go a bit further you could add a more generic pointer extraction helper that can be used here, in your useAuth composable and in the local useAuth composable
|
Hi @Danielwinkelmann 👋 I am going through some PRs and noticed yours is still open! Do you still want to continue with it or should we see that we take this over? 🤗 |
|
Hi @zoey-kaiser can you create a beta based on this pull request please! this is very helpfull, litteraly what the package need to support local provider |
|
@zoey-kaiser Sorry for delay. Had a litte bit to much private stuff going on. |
Sounds good! Ill get around to another review by Wednesday and then I can release a pre-version, so @dommi10 can test it! |
|
@zoey-kaiser i’m so excited to test |
|
Hi @dommi10 I released a test version of this branch in a new package, as there is no documentation yet and there are still some kinks to iron out. However, I did want to let you have a look at it and see if everything works in your projects: https://www.npmjs.com/package/sidebase-auth-refresh Feedback is super appreciated, maybe you can find some issues or have some improvement tips! Once we merge this and finish the documentation you should be able to switch to the official package! This one is just for temporary testing. |
Yes for sure |
Still have an issue when you select refresh as provider, the entire app crash |
|
Published a new test version: https://www.npmjs.com/package/sidebase-auth-refresh Should be available under |
Let’s us test again |
Let me know how it goes! If everything works well I want to aim to publish it properly next week! |
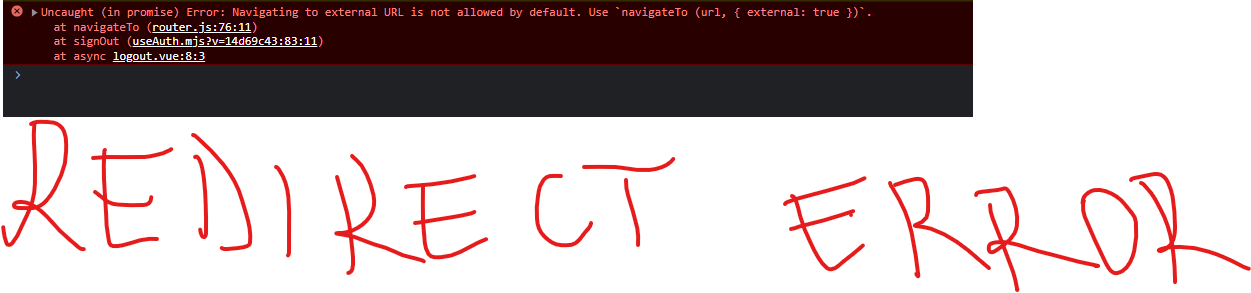
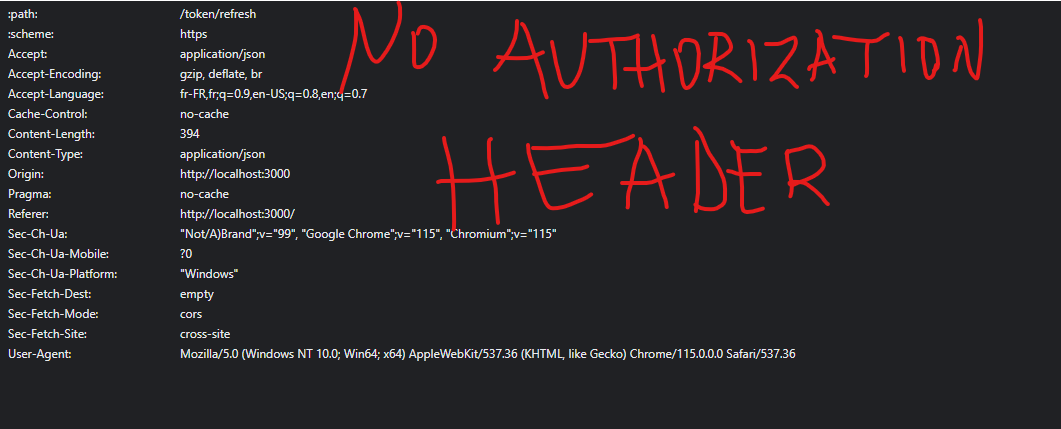
An issues on logout redirect and issus when you try to refresh the token it doesn't add AUTORIZATION HEADER |
An issues on logout redirect and issus when you try to refresh the token it doesn't add AUTORIZATION HEADER |
Okay good to know! Thank you for the initial testing 💪 |
Error on Redirect after logoutNo Autorization Header in refresh token request |
@zoey-kaiser !! |
| // TODO: get rid of duplicate code | ||
| const { rawToken, rawRefreshToken, refreshToken, lastRefreshedAt } = useAuthState() | ||
| if (refreshToken.value) { | ||
| const config = nuxtApp.$config.auth |
There was a problem hiding this comment.
I think that you forgot to put .public. level for the path. But actually, you can use useRuntimeConfig().public.auth like in the /src/runtime/plugin.ts for code consistency.
|
Any update on this? |
|
I originally used nuxtjs/auth and the server side was running refresh token with express. is the sidebase/nuxt-auth refresh token going to work with third party servers such as express? |
This specific version can answer our questions @zoey-kaiser any updates please ?? another beta please based on new modifications made by @MaxNvk |
|
this would be amazing to get asap |
fix bugs on reference of runtime config add headers on refresh methode Refs: sidebase#373
|
Taken over and merged in #581 |




Implement the local "refresh" schema, it's based on the local schema and extends it.
I used as much code and types as possible from the 'local' schema.
Types are always extended and not rewritten, to maximize the compatibility between the schemas.
Checklist: