Creating Email Verified Anonymous Identities and Private Groups using Zero Knowledge Proof
Anonymous identities are of prime importance today for applications that promise privacy and anonymity to its users. However, often there is a need for these applications to confirm if their users are authentic, i.e, probably belong to a certain group or an organization. One of the possible methods to confirm this would be to verify the user's official email, without compromising on the user's anonymity. zkEmailAuth project aims to achieve the same. The methodology involves getting user's official email, create anonymous identities, verify the email then finally add him/her to the private Semaphore group.
The methodology employs 2 phases to achieve email verification without compromising on the anonymity of the user. The user first connects his wallet to the application to begin the verification procedure.
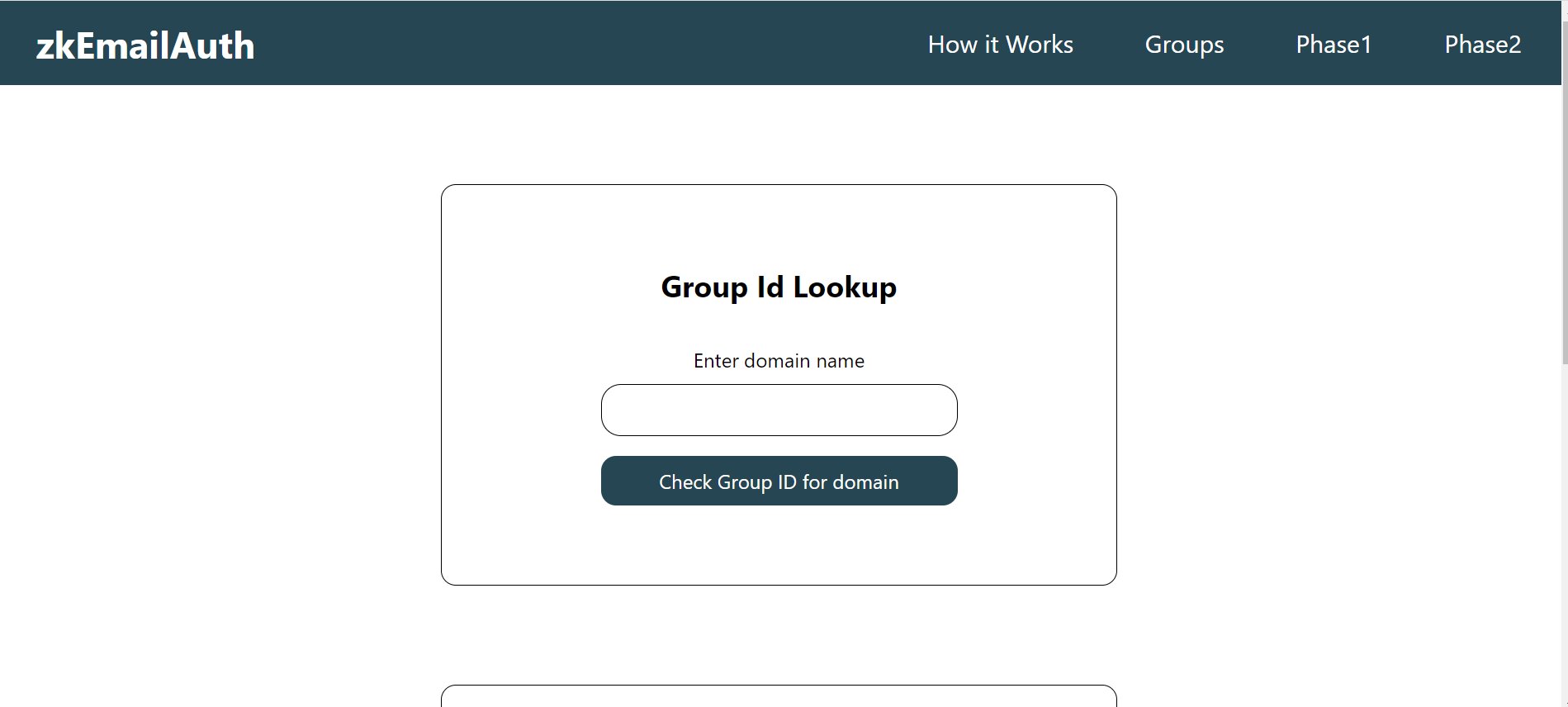
Anonymous identities are added to Semaphore groups. These Semaphore groups represent the organization or group tied to the domain of the official email. Each Semaphore group has its own unique ID. Users are allowed to create their own groups by entering the domain of the official email and by choosing an arbitrary ID. If the group already exists, users can check the group ID using the lookup.
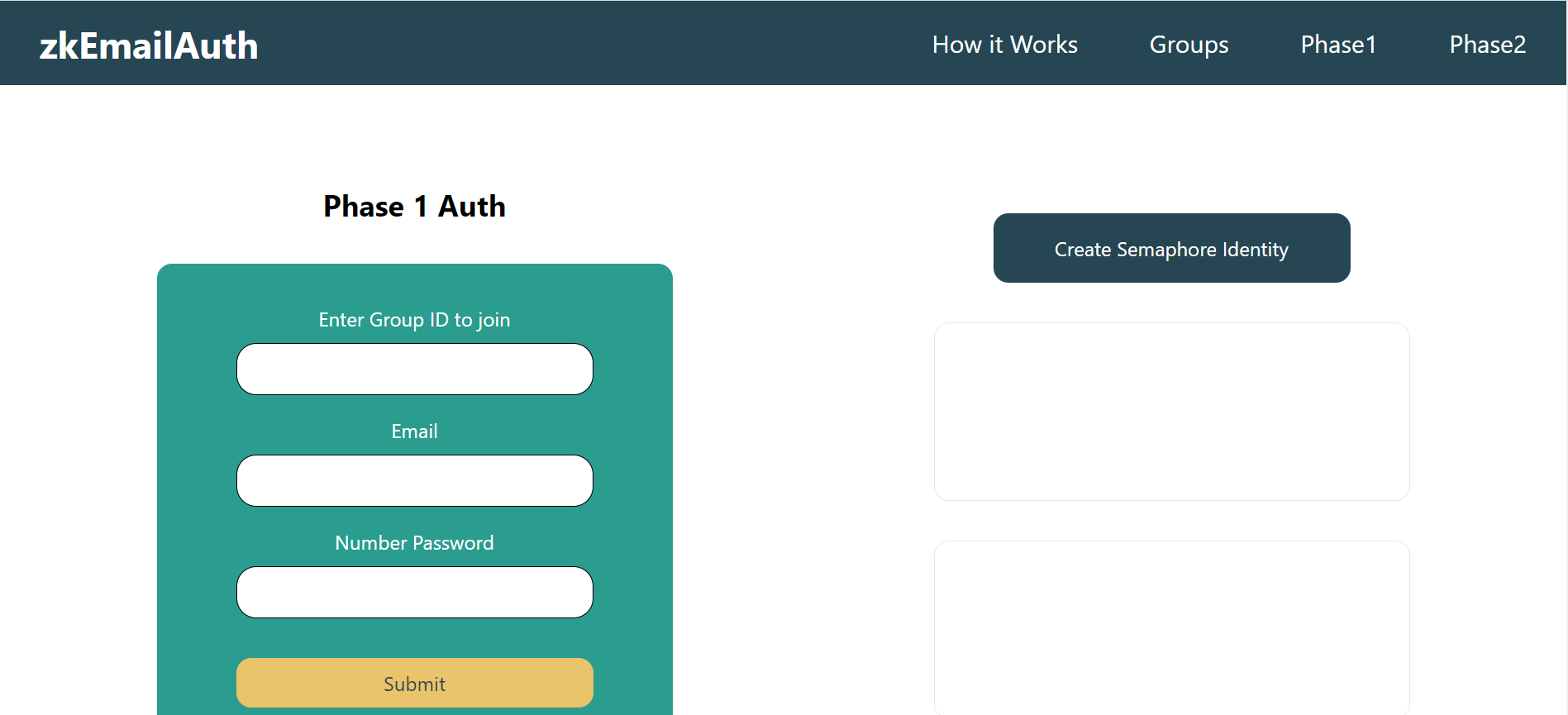
In Phase 1, user submits the group ID of the intended group user wishes to join, email address and a secret numeric password. The group ID, public key and secret password are hashed together to create an intermediate hash and sent to a backend server. The backend server generates a cryptographically secure random string and hashes it further to the intermediate hash to generate the final public hash. This public hash is returned to the front end and displayed to the user. Additionally, it is also stored on chain. The random string generated at the server is then sent over email to the address specified by the user. Also, user generates an anonymous identity using Semaphore in this stage and the identity commitment is stored on the browser.
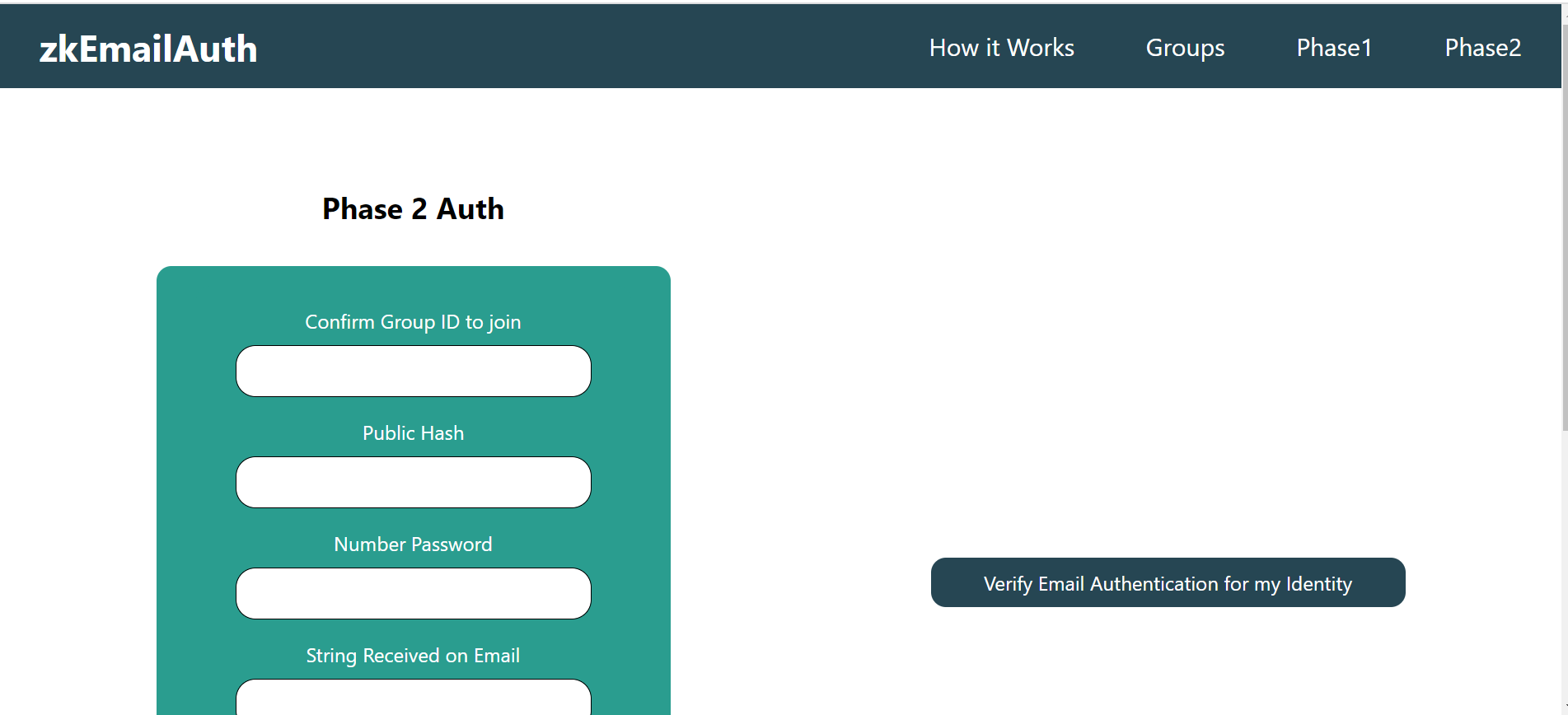
User needs to produce the following in Phase 2 - the group ID, the public hash generated in Phase 1 (this needs to be same as the one stored on chain), the secret numeric password used by the user in Phase 1 and the random string received over user's email. These inputs are then provided as inputs to verify proof generated by a circuit to ensure that the user has not cheated and that this user is same as the one who submitted the data in Phase 1. If the proof verification is successful, user's anonymous identity (stored in browser in Phase 1) is email-verified and thus will be added to the intended group ID.
The project consists of three folders
- circuits - contains the circuit written in Circom which helps generate the proof
- contracts - contains the main contract and verify contract files along with tests
- frontend - NextJS project with the front end and server for sending email Refer to each folders to understand how to use them.
Clone the repository
git clone https://github.com/suhasBR/zku-final-project.gitCompile Circuits
cd circuitsFollow instructions given in circuits folder to compile circuits
Run Contracts
cd contractsFollow instructions given in contracts folder
Run Frontend Enter frontend
cd frontendInstall Dependencies
yarn iRun Dev Server
yarn dev