-
Notifications
You must be signed in to change notification settings - Fork 260
Move Cidr translation from iptable to ipset. #582
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Merged
Merged
Changes from all commits
Commits
File filter
Filter by extension
Conversations
Failed to load comments.
Loading
Jump to
Jump to file
Failed to load files.
Loading
Diff view
Diff view
There are no files selected for viewing
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| Original file line number | Diff line number | Diff line change |
|---|---|---|
|
|
@@ -3,8 +3,11 @@ | |
| package npm | ||
|
|
||
| import ( | ||
| "strconv" | ||
|
|
||
| "github.com/Azure/azure-container-networking/log" | ||
| "github.com/Azure/azure-container-networking/npm/iptm" | ||
| "github.com/Azure/azure-container-networking/npm/ipsm" | ||
| "github.com/Azure/azure-container-networking/npm/util" | ||
| networkingv1 "k8s.io/api/networking/v1" | ||
| ) | ||
|
|
@@ -49,7 +52,7 @@ func (npMgr *NetworkPolicyManager) AddNetworkPolicy(npObj *networkingv1.NetworkP | |
| } | ||
|
|
||
| if !npMgr.isAzureNpmChainCreated { | ||
| if err = allNs.ipsMgr.CreateSet(util.KubeSystemFlag, util.IpsetNetHashFlag); err != nil { | ||
| if err = allNs.ipsMgr.CreateSet(util.KubeSystemFlag, append([]string{util.IpsetNetHashFlag})); err != nil { | ||
| log.Errorf("Error: failed to initialize kube-system ipset.") | ||
| return err | ||
| } | ||
|
|
@@ -63,11 +66,12 @@ func (npMgr *NetworkPolicyManager) AddNetworkPolicy(npObj *networkingv1.NetworkP | |
| } | ||
|
|
||
| var ( | ||
| hashedSelector = HashSelector(&npObj.Spec.PodSelector) | ||
| addedPolicy *networkingv1.NetworkPolicy | ||
| sets, namedPorts, lists []string | ||
| iptEntries []*iptm.IptEntry | ||
| ipsMgr = allNs.ipsMgr | ||
| hashedSelector = HashSelector(&npObj.Spec.PodSelector) | ||
| addedPolicy *networkingv1.NetworkPolicy | ||
| sets, namedPorts, lists []string | ||
| ingressIPCidrs, egressIPCidrs [][]string | ||
| iptEntries []*iptm.IptEntry | ||
| ipsMgr = allNs.ipsMgr | ||
| ) | ||
|
|
||
| // Remove the existing policy from processed (merged) network policy map | ||
|
|
@@ -93,16 +97,16 @@ func (npMgr *NetworkPolicyManager) AddNetworkPolicy(npObj *networkingv1.NetworkP | |
|
|
||
| ns.rawNpMap[npObj.ObjectMeta.Name] = npObj | ||
|
|
||
| sets, namedPorts, lists, iptEntries = translatePolicy(npObj) | ||
| sets, namedPorts, lists, ingressIPCidrs, egressIPCidrs, iptEntries = translatePolicy(npObj) | ||
| for _, set := range sets { | ||
| log.Printf("Creating set: %v, hashedSet: %v", set, util.GetHashedName(set)) | ||
| if err = ipsMgr.CreateSet(set, util.IpsetNetHashFlag); err != nil { | ||
| if err = ipsMgr.CreateSet(set, append([]string{util.IpsetNetHashFlag})); err != nil { | ||
| log.Printf("Error creating ipset %s", set) | ||
| } | ||
| } | ||
| for _, set := range namedPorts { | ||
| log.Printf("Creating set: %v, hashedSet: %v", set, util.GetHashedName(set)) | ||
| if err = ipsMgr.CreateSet(set, util.IpsetIPPortHashFlag); err != nil { | ||
| if err = ipsMgr.CreateSet(set, append([]string{util.IpsetIPPortHashFlag})); err != nil { | ||
| log.Printf("Error creating ipset named port %s", set) | ||
| } | ||
| } | ||
|
|
@@ -114,6 +118,8 @@ func (npMgr *NetworkPolicyManager) AddNetworkPolicy(npObj *networkingv1.NetworkP | |
| if err = npMgr.InitAllNsList(); err != nil { | ||
| log.Printf("Error initializing all-namespace ipset list.") | ||
| } | ||
| createCidrsRule("in", npObj.ObjectMeta.Name, npObj.ObjectMeta.Namespace, ingressIPCidrs, ipsMgr) | ||
| createCidrsRule("out", npObj.ObjectMeta.Name, npObj.ObjectMeta.Namespace, egressIPCidrs, ipsMgr) | ||
| iptMgr := allNs.iptMgr | ||
| for _, iptEntry := range iptEntries { | ||
| if err = iptMgr.Add(iptEntry); err != nil { | ||
|
|
@@ -154,7 +160,7 @@ func (npMgr *NetworkPolicyManager) DeleteNetworkPolicy(npObj *networkingv1.Netwo | |
| npMgr.nsMap[npNs] = ns | ||
| } | ||
|
|
||
| _, _, _, iptEntries := translatePolicy(npObj) | ||
| _, _, _, ingressIPCidrs, egressIPCidrs, iptEntries := translatePolicy(npObj) | ||
|
|
||
| iptMgr := allNs.iptMgr | ||
| for _, iptEntry := range iptEntries { | ||
|
|
@@ -163,6 +169,9 @@ func (npMgr *NetworkPolicyManager) DeleteNetworkPolicy(npObj *networkingv1.Netwo | |
| } | ||
| } | ||
|
|
||
| removeCidrsRule("in", npObj.ObjectMeta.Name, npObj.ObjectMeta.Namespace, ingressIPCidrs, allNs.ipsMgr) | ||
| removeCidrsRule("out", npObj.ObjectMeta.Name, npObj.ObjectMeta.Namespace, egressIPCidrs, allNs.ipsMgr) | ||
|
|
||
| delete(ns.rawNpMap, npObj.ObjectMeta.Name) | ||
|
|
||
| hashedSelector := HashSelector(&npObj.Spec.PodSelector) | ||
|
|
@@ -189,3 +198,35 @@ func (npMgr *NetworkPolicyManager) DeleteNetworkPolicy(npObj *networkingv1.Netwo | |
|
|
||
| return nil | ||
| } | ||
|
|
||
| func createCidrsRule(ingressOrEgress, policyName, ns string, ipsetEntries [][]string, ipsMgr *ipsm.IpsetManager) { | ||
| spec := append([]string{util.IpsetNetHashFlag, util.IpsetMaxelemName, util.IpsetMaxelemNum}) | ||
| for i, ipCidrSet := range ipsetEntries { | ||
| if ipCidrSet == nil || len(ipCidrSet) == 0 { | ||
| continue | ||
| } | ||
| setName := policyName + "-in-ns-" + ns + "-" + strconv.Itoa(i) + ingressOrEgress | ||
| log.Printf("Creating set: %v, hashedSet: %v", setName, util.GetHashedName(setName)) | ||
| if err := ipsMgr.CreateSet(setName, spec); err != nil { | ||
| log.Printf("Error creating ipset %s", ipCidrSet) | ||
| } | ||
| for _, ipCidrEntry := range util.DropEmptyFields(ipCidrSet) { | ||
| if err := ipsMgr.AddToSet(setName, ipCidrEntry, util.IpsetNetHashFlag); err != nil { | ||
| log.Printf("Error adding ip cidrs %s into ipset %s", ipCidrEntry, ipCidrSet) | ||
| } | ||
| } | ||
| } | ||
| } | ||
|
|
||
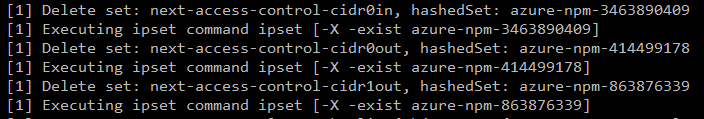
| func removeCidrsRule(ingressOrEgress, policyName, ns string, ipsetEntries [][]string, ipsMgr *ipsm.IpsetManager) { | ||
| for i, ipCidrSet := range ipsetEntries { | ||
| if ipCidrSet == nil || len(ipCidrSet) == 0 { | ||
|
Contributor
There was a problem hiding this comment. Choose a reason for hiding this commentThe reason will be displayed to describe this comment to others. Learn more. I don't think this func will work as intended since the length of the set includes all the entries to be deleted
Contributor
Author
There was a problem hiding this comment. Choose a reason for hiding this commentThe reason will be displayed to describe this comment to others. Learn more. |
||
| continue | ||
| } | ||
| setName := policyName + "-in-ns-" + ns + "-" + strconv.Itoa(i) + ingressOrEgress | ||
| log.Printf("Delete set: %v, hashedSet: %v", setName, util.GetHashedName(setName)) | ||
| if err := ipsMgr.DeleteSet(setName); err != nil { | ||
| log.Printf("Error deleting ipset %s", ipCidrSet) | ||
| } | ||
| } | ||
| } | ||
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| Original file line number | Diff line number | Diff line change |
|---|---|---|
|
|
@@ -29,6 +29,8 @@ spec: | |
| - to: | ||
| - ipBlock: | ||
| cidr: 10.0.0.0/24 | ||
| except: | ||
| - 10.0.0.1/32 | ||
| ports: | ||
| - protocol: TCP | ||
| port: 5978 | ||
Oops, something went wrong.
Add this suggestion to a batch that can be applied as a single commit.
This suggestion is invalid because no changes were made to the code.
Suggestions cannot be applied while the pull request is closed.
Suggestions cannot be applied while viewing a subset of changes.
Only one suggestion per line can be applied in a batch.
Add this suggestion to a batch that can be applied as a single commit.
Applying suggestions on deleted lines is not supported.
You must change the existing code in this line in order to create a valid suggestion.
Outdated suggestions cannot be applied.
This suggestion has been applied or marked resolved.
Suggestions cannot be applied from pending reviews.
Suggestions cannot be applied on multi-line comments.
Suggestions cannot be applied while the pull request is queued to merge.
Suggestion cannot be applied right now. Please check back later.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
translatepolicy should already remove empty sets
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
No, it didn't.
For the existing return object, including sets, namedPorts, lists, they are []string type and called UniqueStrSlice to remove empty set. However, for ipsetEntries, it's [][]string type and didn't do drop empty entries before returning. I intentionally didn't do that to keep index order for simplicity for deleting ipset when network policy rule updates.