fix: abac not using policy#918
Conversation
|
@tangyang9464 @closetool @sagilio please review |
|
@nodece plz review |
|
@silverspace plz review |
|
@sagilio Yep. I realized this error when I wrote the test. But if the matcher doesn't use policy, no policy should be matched for the request. So no matter what policy definitions look like, policy should have no effect on the request? |
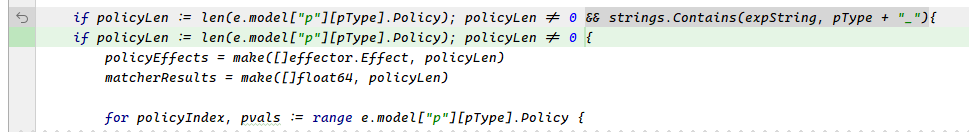
Yeah, you changes are right,we need not to scan all policies when matcher is not included rtype. But this just is a enhancment about performance. I do not know why the wrong result be returned in #917. |
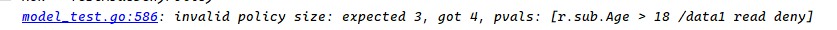
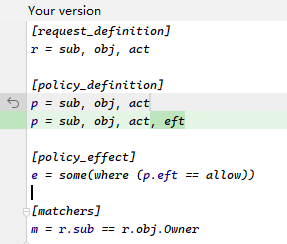
I think the root cause is that When the matcher doesn't use any policy and the request meets the judgment of the matcher, the request will match all policies because the matcher always returns true. Take #917 as an example, request: will match policy and the merged effect is |
|
@Abingcbc I see, you are right. We may need a more effective test case to descript the situation. |
Signed-off-by: abingcbc <abingcbc626@gmail.com>
|
@sagilio plz review |
|
🎉 This PR is included in version 2.39.1 🎉 The release is available on GitHub release Your semantic-release bot 📦🚀 |
|
Hi @Abingcbc , @hsluoyz , @sagilio model - I used request as and got the result as false. On replacing Is this the expected behaviour for the above case that the request depends on policy file instead of just relying on matcher |
|
@harshalmittal4 the online editor is pure frontend (https://github.com/casbin/casbin-editor), which uses Node-Casbin: https://github.com/casbin/node-casbin for Casbin enforcement. Usually we have latest features in Golang version Casbin and Node-Casbin maybe still doesn't have the feature of this PR: #918 yet. Issue proposed here: apache/casbin-node-casbin#433 |
|
Thanks @hsluoyz , got it. I'm currently getting more familiar with Casbin and would like to try contributing to some issues once I get comfortable |
Signed-off-by: abingcbc abingcbc626@gmail.com
Fix: #917
How it works
Ignore all policies when matcher doesn't contain any match related to policy.