[KYUUBI #3020] kyuubi ldap add new config property kyuubi.authentication.ldap.bindpw and kyuubi.authentication.ldap.attrs #3213
[KYUUBI #3020] kyuubi ldap add new config property kyuubi.authentication.ldap.bindpw and kyuubi.authentication.ldap.attrs #3213dev-lpq wants to merge 17 commits intoapache:masterfrom
Conversation
…w and kyuubi.authentication.ldap.attrs
|
btw, #3213 (comment) these UTs can be added to the codebase too? |
|
…w and kyuubi.authentication.ldap.attrs
@yaooqinn Please help check the PR, I have added the LDAP UTs. |
|
cc @turboFei can you check this, since LDAP is adopted in your environment |
could you help fix above UT failure? |
|
| val bindnPw = conf.get(AUTHENTICATION_LDAP_PASSWORD).get | ||
| val attrs = conf.get(AUTHENTICATION_LDAP_ATTRIBUTES).toArray | ||
|
|
||
| env.put(Context.SECURITY_PRINCIPAL, guidKey) |
There was a problem hiding this comment.
According to https://docs.cloudera.com/cdp-private-cloud-base/7.1.6/using-das/topics/das-user-authentication-ldap.html
LDAP GUID Key: Specify the LDAP attribute name whose values are unique on this LDAP server. For example: uid or CN.
GUID Key is not used for SECURITY_PRINCIPAL.
fixed |
|
The change LGTM, please rebase master and resolve conflicts |
| user | ||
| } | ||
|
|
||
| val guidKey = conf.get(AUTHENTICATION_LDAP_GUIDKEY) |
There was a problem hiding this comment.
seems AUTHENTICATION_LDAP_GUIDKEY is not used now.
Can we remove it? cc @pan3793
There was a problem hiding this comment.
it is a break change, we should keep backward compatibility.
could you deprecate AUTHENTICATION_LDAP_GUIDKEY?
If the AUTHENTICATION_LDAP_BINDDN is specified, using it first.
Otherwise, fallback to use original logical to get SECURITY_PRINCIPAL?
Codecov Report
@@ Coverage Diff @@
## master #3213 +/- ##
============================================
+ Coverage 51.06% 51.33% +0.26%
Complexity 13 13
============================================
Files 470 468 -2
Lines 26224 26205 -19
Branches 3626 3631 +5
============================================
+ Hits 13392 13452 +60
+ Misses 11556 11465 -91
- Partials 1276 1288 +12
📣 We’re building smart automated test selection to slash your CI/CD build times. Learn more |
|
Now the only remaining comments is #3213 (comment) how about fallback to get binddn according to guidKey & baseDn just like before if Otherwise, the customers that use the old kyuubi version will meet failure after upgrading kyuubi. |
|
thanks for your contribution @dev-lpq , will merge it after UT passed. |
|
thanks @dev-lpq , merged to master |
|
could you bind your email(pengqli@cisco.com) to your github account? |
@turboFei Added, thanks. |
|
merged to 1.6 as well |
…ion.ldap.bindpw and kyuubi.authentication.ldap.attrs ### _Why are the changes needed?_ Among the kyuubi ldap configuration parameters, there is currently "kyuubi.authentication.ldap.base.dn=", but there is no place corresponding to the CN password setting. similar to hive "hive.server2.authentication.ldap.binddn", "hive.server2.authentication.ldap.bindpw". ### _How was this patch tested?_ - [ ] Add some test cases that check the changes thoroughly including negative and positive cases if possible - [x] Add screenshots for manual tests if appropriate - [ ] [Run test](https://kyuubi.apache.org/docs/latest/develop_tools/testing.html#running-tests) locally before make a pull request Closes #3213 from dev-lpq/branch-ldap-1.6. Closes #3020 31817cc [pengqli] upgrade ldap to support ldap before 1.6.0 3109403 [pengqli] upgrade ldap to support ldap before 1.6.0 f62e4c9 [pengqli] upgrade ldap to support ldap before 1.6.0 e03e036 [pengqli] add AUTHENTICATION_LDAP_GUIDKEY deprecated 6f680df [pengqli] add ldap config AUTHENTICATION_LDAP_BINDDN 19f8e6c [pengqli] add ldap config AUTHENTICATION_LDAP_BINDDN 07df56b [pengqli] upgrade LdapAuthenticationProviderImpl 1a48f41 [pengqli] upgrade settings.md 8e9b572 [pengqli] upgrade ldap ldapBindpw 5793a81 [pengqli] upgrade ldap ldapBindpw 822d4c3 [pengqli] upgrade docs/deployment/settings.md c2b2041 [pengqli] upgrade ldap WithLdapServer UTs 5d7a301 [pengqli] add AUTHENTICATION_LDAP_PASSWORD into serverOnlyConfEntries 10b42b1 [pengqli] upgrade AuthenticationProviderFactorySuite UTs 490bfae [pengqli] kyuubi ldap add new config property kyuubi.authentication.ldap.bindnpw and kyuubi.authentication.ldap.attrs 5e07125 [pengqli] upgrafe config kyuubi.authentication.ldap.attrs 4e771ec [pengqli] kyuubi ldap add new config property kyuubi.authentication.ldap.bindnpw and kyuubi.authentication.ldap.attrs Authored-by: pengqli <pengqli@cisco.com> Signed-off-by: Fei Wang <fwang12@ebay.com>
|
The following logic is not correct I think I can not fully understand what's purpose of I don't have much experience w/ LDAP, and I would like to provide similar configurations w/ Hive unless we have strong reasons that we can give a better solution. |
|
Basically, the principle is to give users the same(or better) configuration keys w/ Hive. For implementation, |
|
Thank you for your answer, the current way to verify ldap: I will research unboundid-ldapsdk and hive LDAP , and provide a better solution. |
|
@dev-lpq, thanks for your passion and patience |
Why are the changes needed?
Among the kyuubi ldap configuration parameters, there is currently "kyuubi.authentication.ldap.base.dn=", but there is no place corresponding to the CN password setting. similar to hive
"hive.server2.authentication.ldap.binddn",
"hive.server2.authentication.ldap.bindpw".
How was this patch tested?
Add some test cases that check the changes thoroughly including negative and positive cases if possible
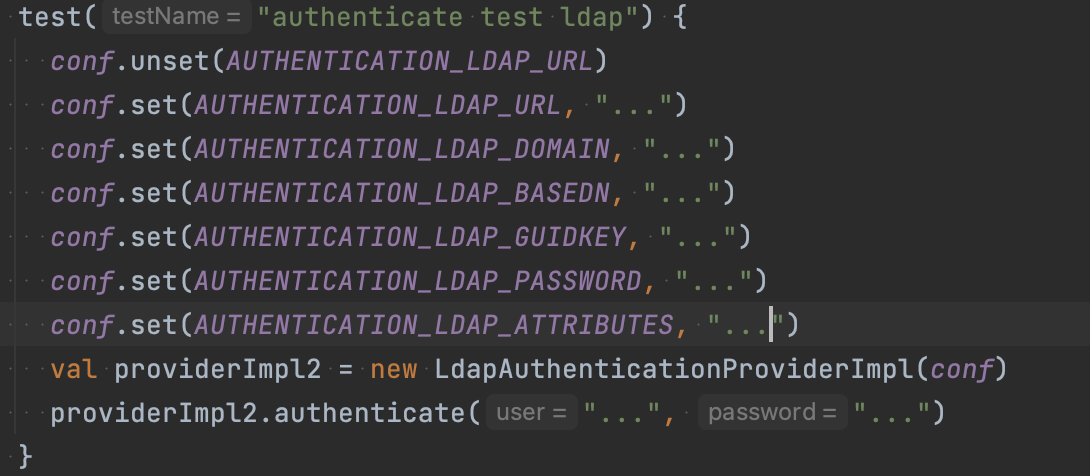
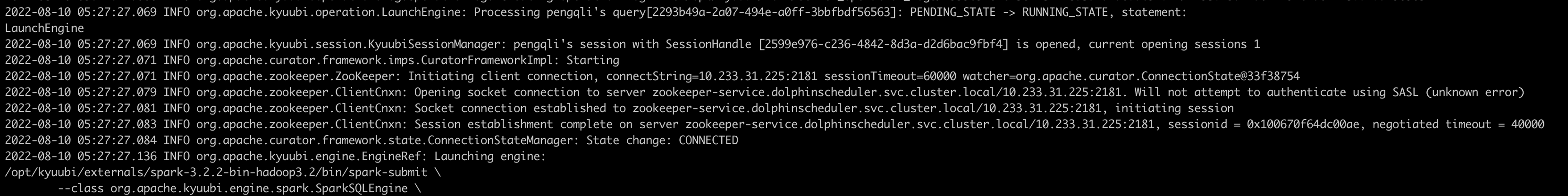
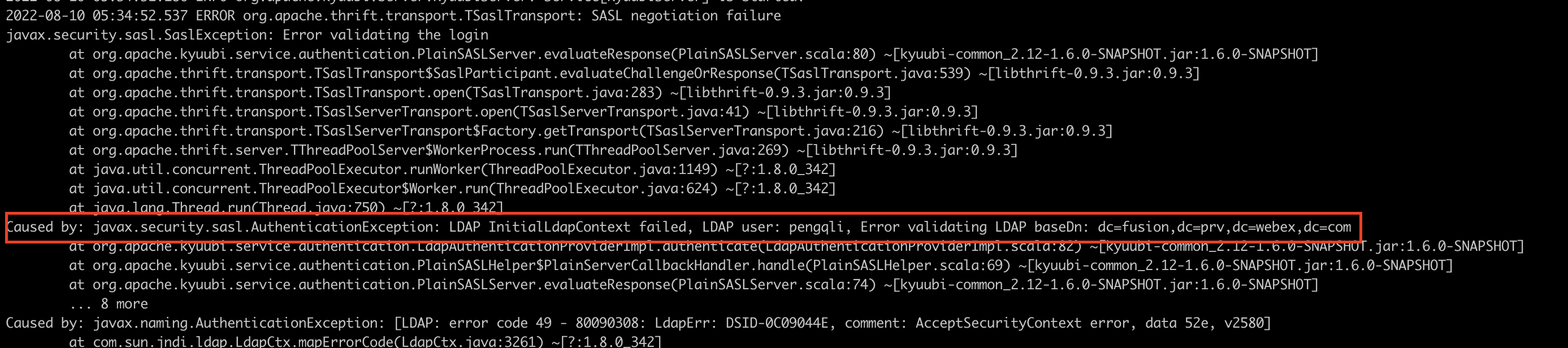
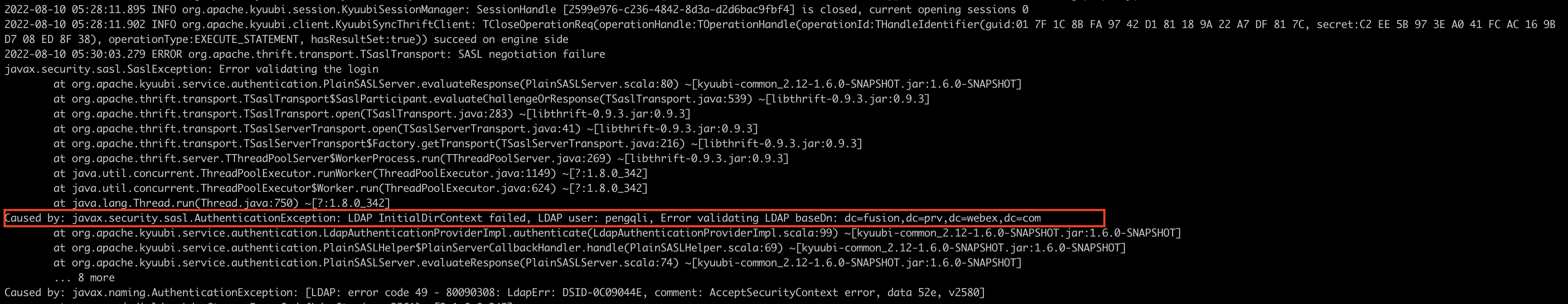
Add screenshots for manual tests if appropriate
Run test locally before make a pull request